Constant security threats, sensitive data, and never-ending compliance requirements—that’s a lot for an organization to handle! It can be overwhelming for companies to drive business outcomes while trying to fulfill security and compliance requirements.
Enforcing cybersecurity and data privacy while also obeying regulatory requirements can be made easier by following a structured security framework.

A security framework is like a handbook that guides an organization with a comprehensive approach to risk management and data protection. It consists of controls, policies, and procedures that help fortify an organization’s security posture.
There are several frameworks that help organizations design controls to prevent security risks and maintain compliance, one such framework being the Secure Controls Framework.
The Secure Controls Framework is one of the most comprehensive guidelines using which a company can conceptualize and enforce an in-depth security program. In this blog, we will cover what the secure controls framework is, how it works, and why it is a good idea to use a common control framework for your organization’s security.
What is the secure controls framework?
Simply put, the Secure Controls Framework (SCF) is an open-source guide that consists of a set of controls that help an organization design and implement effective security. It offers strategic and operational guidance to manage cybersecurity and data privacy without hindering operational growth.
This security controls framework takes a proactive approach to security, but it also results in compliance. Very often, companies that put compliance first, use controls that only concern compliance requirements.
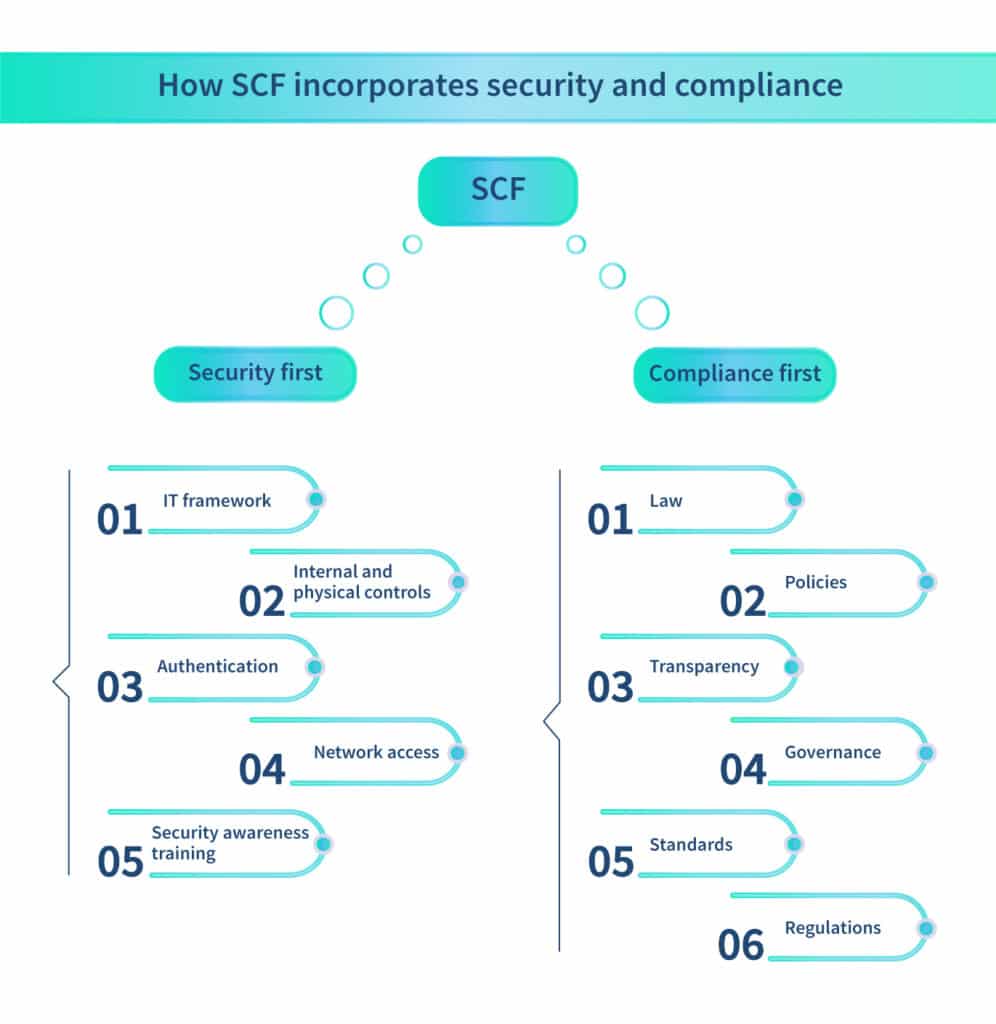
The SCF, on the other hand, takes into account principles of data and security that comply with both cybersecurity and data privacy law, making an organization both secure and compliant.
How does it work?
The SCF is a framework consisting of several applicable standards. It has over a thousand controls that adhere to over 150+ legislations and standards that are updated regularly by authorities.
It helps conceptualize, set up, and maintain a system that safeguards data, systems, applications, and operations of an organization.
The unique features of the secure controls framework are described below.
Distills requirements
Every organization has different needs to address based on the industry it belongs to or the region it operates in. For instance, fintech companies follow PCI DSS, while organizations handling the data of EU residents adhere to GDPR.
The SCF employs the process of “distilling expectations” to customize controls to address the unique requirements of an organization.
The SCF tackles security concerns by focusing on cybersecurity and data privacy controls for statutory, regulatory, and contractual obligations as well as industry-recognized best practices.
By adhering to these standards, it ensures that an organization is both compliant and secure while it focuses on its business processes.
Uses a data-centric approach
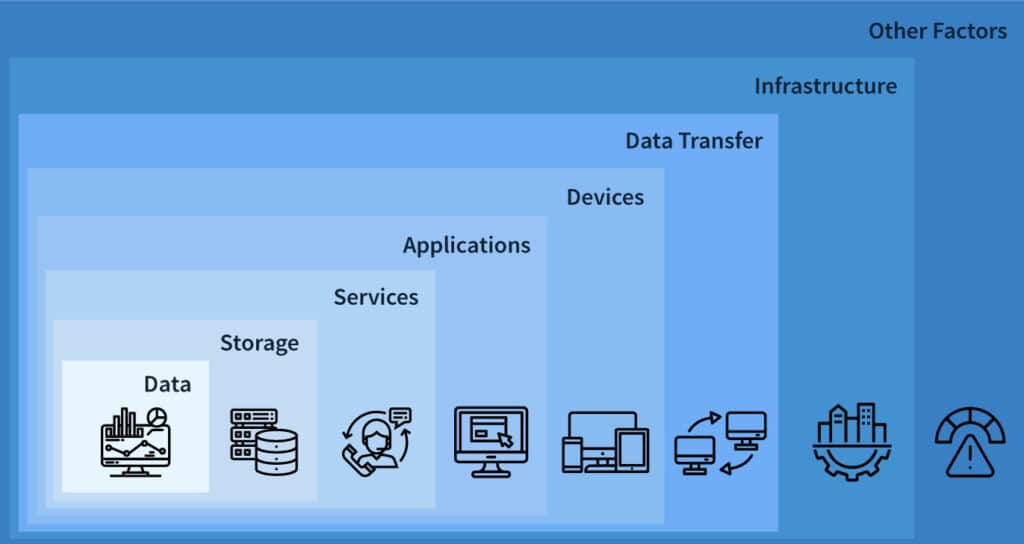
The SCF has in place technical and physical security controls that protect an organization’s data. The physical controls include things like biometrics, access cards, and surveillance cameras to keep unauthorized people out. The technical controls include authentication tools, antivirus software, and firewalls, among other tools, to keep hackers away from data.
The SCF regards data as the most precious commodity of an organization. All assets of an organization, such as hardware, servers, and applications, can be replaced. However, an organization’s data is irreplaceable.
This data-centric approach is kept at the center while setting up and maintaining a security program while following the SCF.
Follows the CIAS quadrant
The CIA (confidentiality, integrity, and availability) Triad does not cut it for the secure controls framework.
The SCF considers the CIA triad inadequate in its approach to cybersecurity and data privacy. This is because it lacks the significant component of safety. The SCF uses the confidentiality, integrity, availability, and safety quadrant to address the ever-evolving needs of organizations that use artificial intelligence (AI) and automated tools.
Since such organizations are prone to frequent security breaches, the SCF emphasizes safety to protect their data. These are the components of the CIAS Quadrant:
Confidentiality: It protects data and proprietary information by restricting its access to authorized users only.
Integrity: It protects data from being altered or destroyed by unauthorized users.
Availability: It ensures that data is made available without any hassle or delay to authorized users.
Safety: It works actively to prevent the risks associated with the use of technologies such as AI by obstructing security threats that could damage or destroy assets.
Safety focuses on preventing dangerous cyber crimes such as cyber stalking, cyber warfare, terrorism, and device tampering.
Uses cybersecurity for privacy by design (C4P)
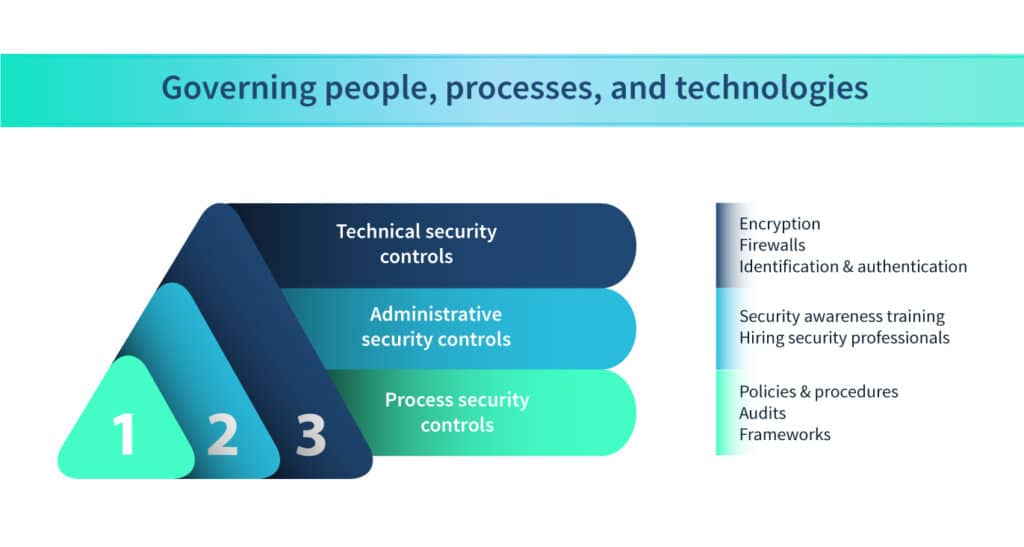
The SCF follows the concept of cybersecurity for privacy by design (C4P), which addresses privacy concerns by governing people, processes, and technologies.
The objectives of C4P are as follows:
- Enforce privacy using tools like virtual private networks and proxy servers
- Make security configuration settings secure by default
- Integrate security mechanisms into processes while implementing them
- Keep security practices simple and consistent for all users to avoid confusion
- Use methods such as zero trust to verify users
- Security awareness training for all users
What is Scrut’s Unified Control Framework and how can it help your organization?
Scrut launched its very own version of the secure controls framework called the Unified Control Framework (UCF). It is a great feature that simplifies the process of meeting compliance requirements across multiple frameworks.
The controls are mapped to frameworks and requirements in your Scrut account, and all artifacts are linked to the controls, including policies, evidence, and tests. This means you are not required to migrate your evidence, controls, or policies when adopting a new standard. We have retained your existing policies and evidence, eliminating any need for additional effort.
Our user-friendly interface makes it easy to navigate and manage your frameworks and controls. You can create custom frameworks and controls, making compliance management even more effortless.
Final thoughts
Using a secure controls framework helps an organization in the conception, implementation, and maintenance of an effective security posture.
It keeps cybersecurity and data privacy at the forefront and embeds security measures into every process, policy, and operation of an organization.
Using Scrut’s Unified Control Framework is a great way to balance both security and compliance needs. It is a game-changer for compliance automation. It lets you save time and effort by mapping controls to frameworks that are applicable to your organization and by satisfying similar requirements at the same time.
Schedule a demo today to learn more.