In an increasingly interconnected world, where digital interactions have become the norm, ensuring secure access to information and services is paramount.
Authentication protocols serve as the gatekeepers of digital access, verifying the identity of users and granting them appropriate permissions. Traditionally, password-based authentication has been the cornerstone of online security, requiring users to prove their identity through a combination of usernames and passwords.
However, the rise of cyber threats and the vulnerabilities inherent in password-based systems have highlighted the need for more robust authentication methods. Enter multi-factor authentication (MFA), which adds additional layers of security by requiring users to provide multiple forms of identification, such as passwords, biometric data, or security tokens.
In this blog, we will delve into the significance of multi-factor authentication in bolstering security measures.
Commonly used authentication methods
The traditional methods of authentication, such as simple passwords, mobile apps, and two-step verification (SMS OTP), fall short in providing robust security.
However, relying solely on these methods is no longer sufficient.
| Authentication Method | Limitations |
|---|---|
| Simple Passwords |
Easily guessable or simplistic passwords are vulnerable to brute-force attacks. Reusing passwords across multiple accounts heightens the impact of security breaches. Phishing scams deceive users who might unknowingly disclose their login credentials, facilitating unauthorized access. Passwords stored in plaintext or poorly encrypted databases are prime targets for cybercriminals. These lead to data breaches, resulting in financial implications and erosion of trust in an organization. |
| Mobile App Authentication | Requires users to possess and maintain specific mobile devices. May not be feasible for all users or scenarios. Relies on device security, which can be compromised. |
| Two-Step Verification (SMS) | Vulnerable to interception or SIM swapping attacks. Relies on the integrity of mobile networks and may fail during network outages or in areas with poor connectivity. SMS OTPs are vulnerable to network outages, social engineering, and SS7 and man-in-the-middle attacks. |
While these methods offer some level of security, they pale in comparison to the comprehensive protection provided by Multi-Factor Authentication (MFA).
What is MFA?
Multi-factor authentication (MFA) is a security method that requires users to provide two or more forms of verification before granting access to a system or application. These verification factors typically include:
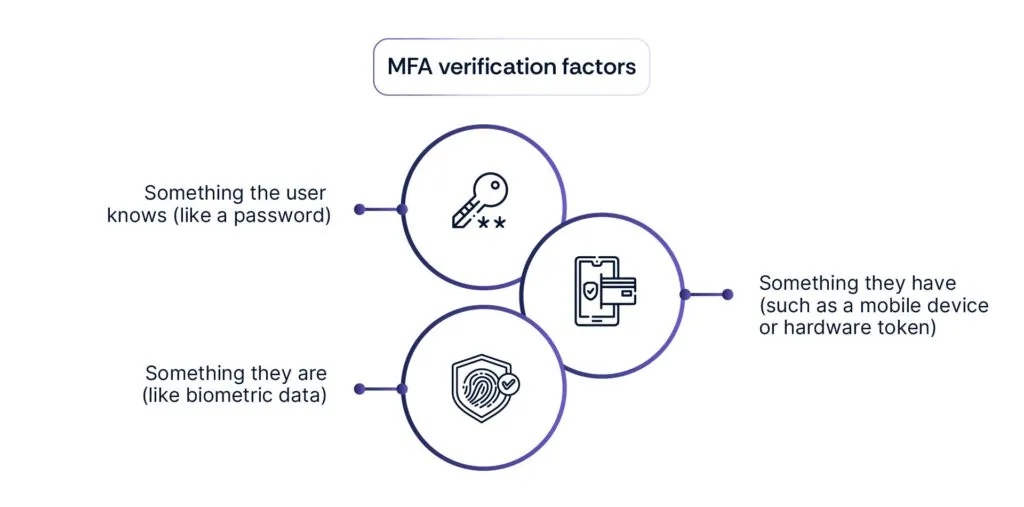
MFA adds an extra layer of security beyond traditional password-based authentication, making it significantly more difficult for unauthorized users to gain access to sensitive information or accounts. It’s an essential tool in combating cyber threats and protecting digital assets.
Indeed, MFA emerges as the superior choice for organizations striving to fortify their defenses against evolving cyber threats.
In one of the largest data breaches in history, Yahoo disclosed that hackers stole account information for over 3 billion users in 2013. Weak encryption methods and poor password security practices contributed to the breach, underscoring the need for stronger authentication measures.
Benefits of Multi-Factor Authentication (MFA) in mitigating security risks
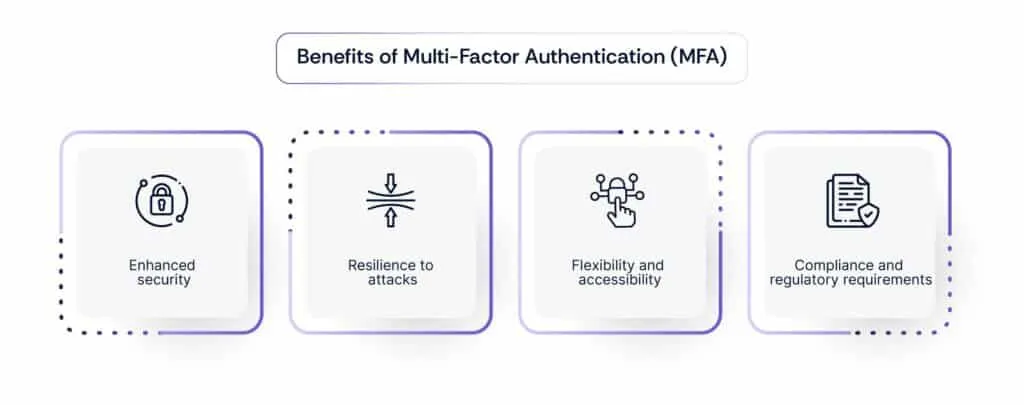
- Enhanced security: MFA adds an extra layer of protection beyond simple passwords, mitigating the risks associated with password breaches and unauthorized access.
- Resilience to attacks: Unlike single-factor authentication methods like SMS OTP, MFA reduces the likelihood of successful phishing attacks or credential theft, as attackers would need to compromise multiple authentication factors.
- Flexibility and accessibility: MFA accommodates a diverse range of authentication factors, allowing organizations to tailor security measures to suit their users’ preferences and operational needs.
- Compliance and regulatory requirements: Many regulatory standards, such as GDPR and PCI DSS, mandate the implementation of MFA as part of robust cybersecurity practices, ensuring compliance with legal and industry requirements.
Leveraging mobile devices for MFA
Leveraging mobile devices for MFA presents a pragmatic compromise that addresses the security, cost, and convenience concerns. Most users already own smartphones or tablets, making them readily available for authentication purposes.
Mobile devices offer built-in biometric authentication features such as fingerprint scanners and facial recognition, enhancing security without the need for additional hardware tokens.
Utilizing existing mobile devices for authentication can significantly reduce the implementation costs associated with deploying specialized hardware tokens or biometric scanners.
Mobile-based MFA solutions provide users with a seamless and convenient authentication experience, leveraging familiar devices and interfaces.
In conclusion
Deploying multiple authentication protocols is vital for robust cybersecurity. Biometrics, tokens, and multi-factor authentication (MFA) offer layers of protection against unauthorized access and data breaches.
Organizations must prioritize comprehensive security measures while maintaining flexibility and independence in decision-making.
Scrut provides the tools to evaluate security solutions objectively, ensuring that choices align with risk profiles, resources, and goals. Schedule a demo today to learn more.
Authentication protocols are sets of rules and procedures used to verify the identity of users accessing systems or networks. They are critical for organizational security because they ensure that only authorized individuals can access sensitive information or resources, thus preventing unauthorized access and potential security breaches.
Diverse authentication methods add layers of security by requiring multiple forms of verification beyond just passwords. Biometrics, such as fingerprints or facial recognition, provide unique physical identifiers, while tokens generate one-time passcodes, making it harder for attackers to gain unauthorized access.
Organizations relying solely on traditional password-based authentication methods face significant security risks. Passwords can be easily compromised through techniques like phishing, brute force attacks, or password reuse. Additionally, users often choose weak or easily guessable passwords, further increasing the risk of unauthorized access.
Implementing multiple authentication protocols creates a more robust security posture by adding layers of defense. Even if one authentication method is compromised, attackers would still need to bypass additional authentication factors, such as biometrics or tokens, to gain access. This multi-factor approach significantly reduces the likelihood of successful unauthorized access.
When determining which authentication protocols to deploy, organizations should consider factors such as the sensitivity of the data or resources being protected, the usability and convenience for end-users, regulatory compliance requirements, and the organization’s risk tolerance. It’s essential to strike a balance between security and usability to ensure that authentication measures are effective without overly burdening users.

Megha Thakkar is a technical content writer with about a decade of experience in cybersecurity and compliance. She writes extensively on SOC 2, ISO 27001, GDPR, and security operations, helping organizations translate complex requirements into clear, audit-ready decisions. Her work, tailored for CISOs and executive leaders, is frequently cited in U.S. government and NIST publications.

Team Scrut is a collective of compliance, security, and risk practitioners sharing practical guidance on building audit-ready, scalable programs. We write about SOC 2, ISO 27001, continuous compliance, third-party risk, cloud security, and GRC automation, blending regulatory depth with operator experience to help fast-growing companies strengthen trust, streamline audits, and stay ahead of evolving security demands.

























