
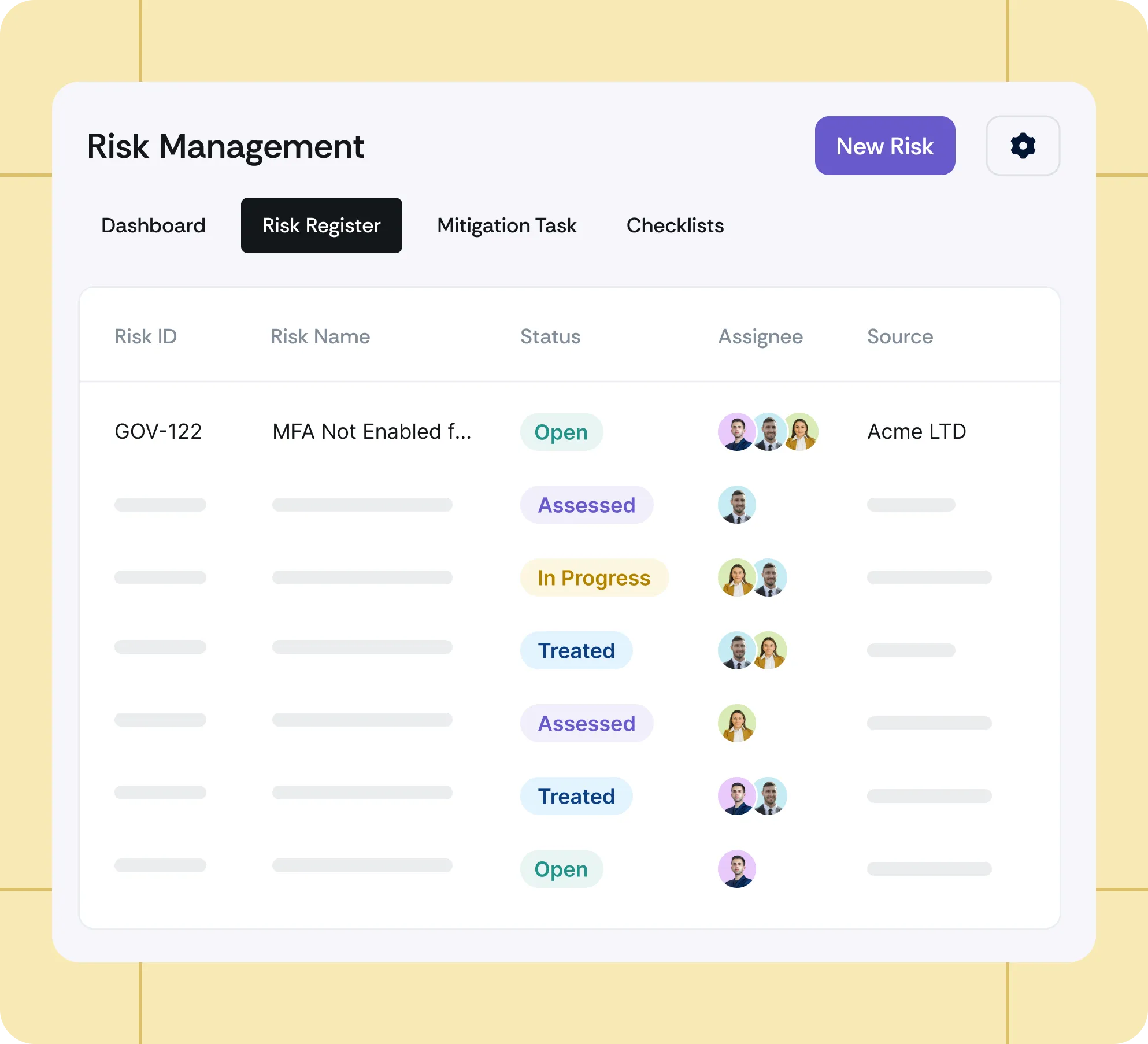
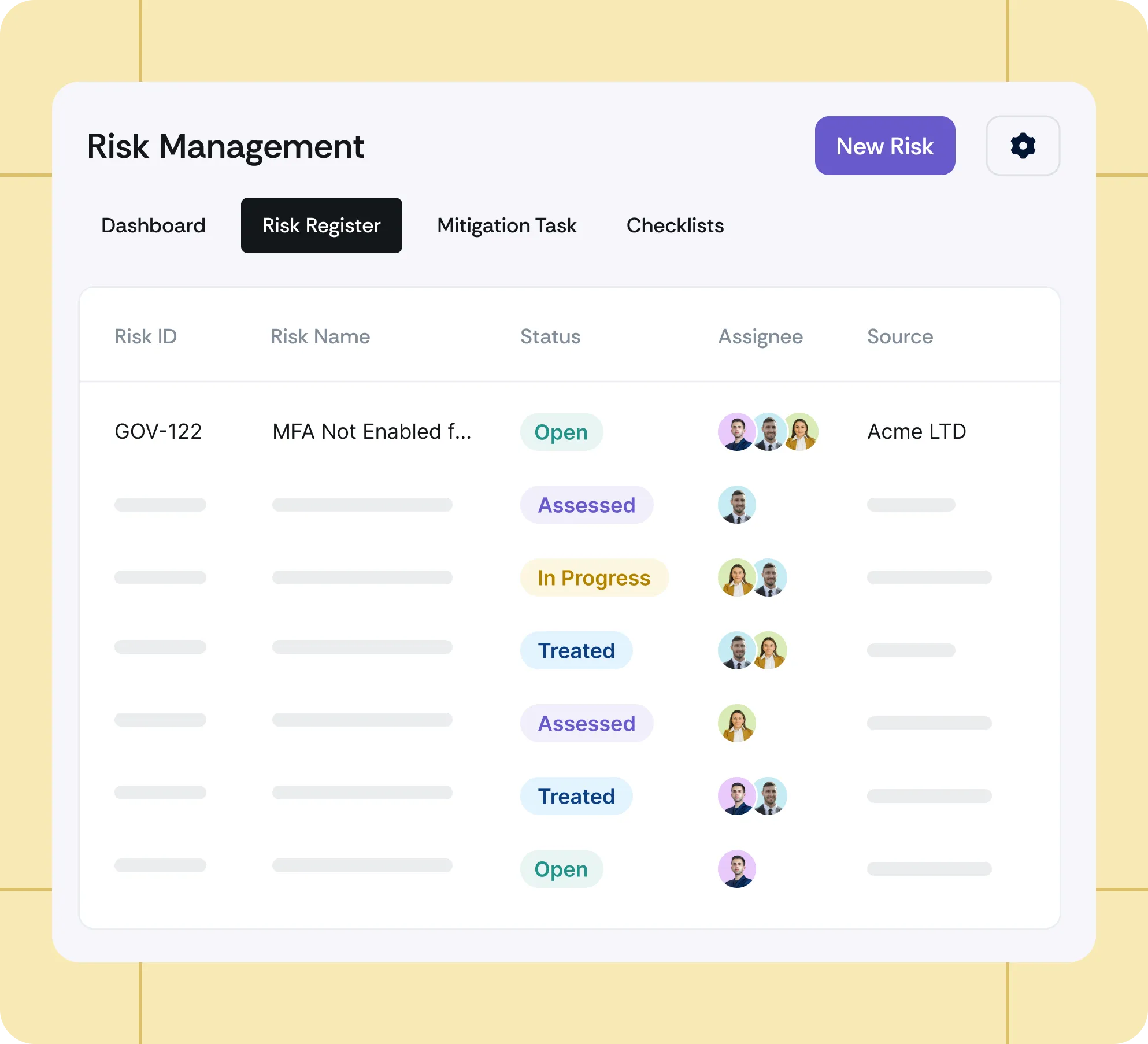
Scrut makes it easier to manage both risk and vendors, helping us identify, assess, prioritize, and mitigate risks with ease.
A 30-minute call to confirm timing, scope, and whether this is worth pursuing.

Accelerate vendor onboarding, automate risk assessments, and manage third-party risk seamlessly with Scrut Teammates.
Centrally manage frameworks, automate evidence collection, and simplify audits with prebuilt controls, while AI surfaces gaps and guides what to fix next so you stay audit-ready with less manual effort.












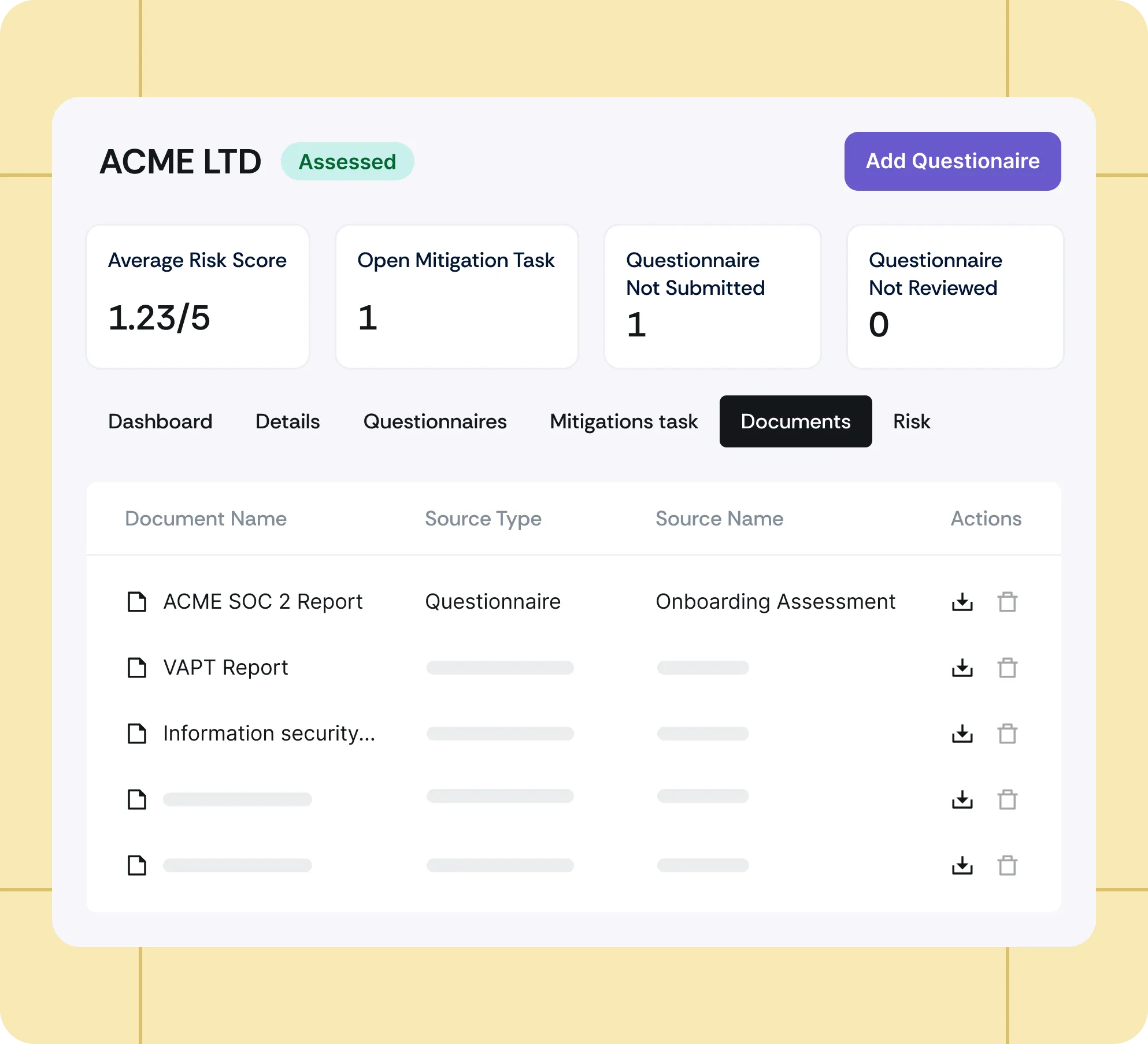
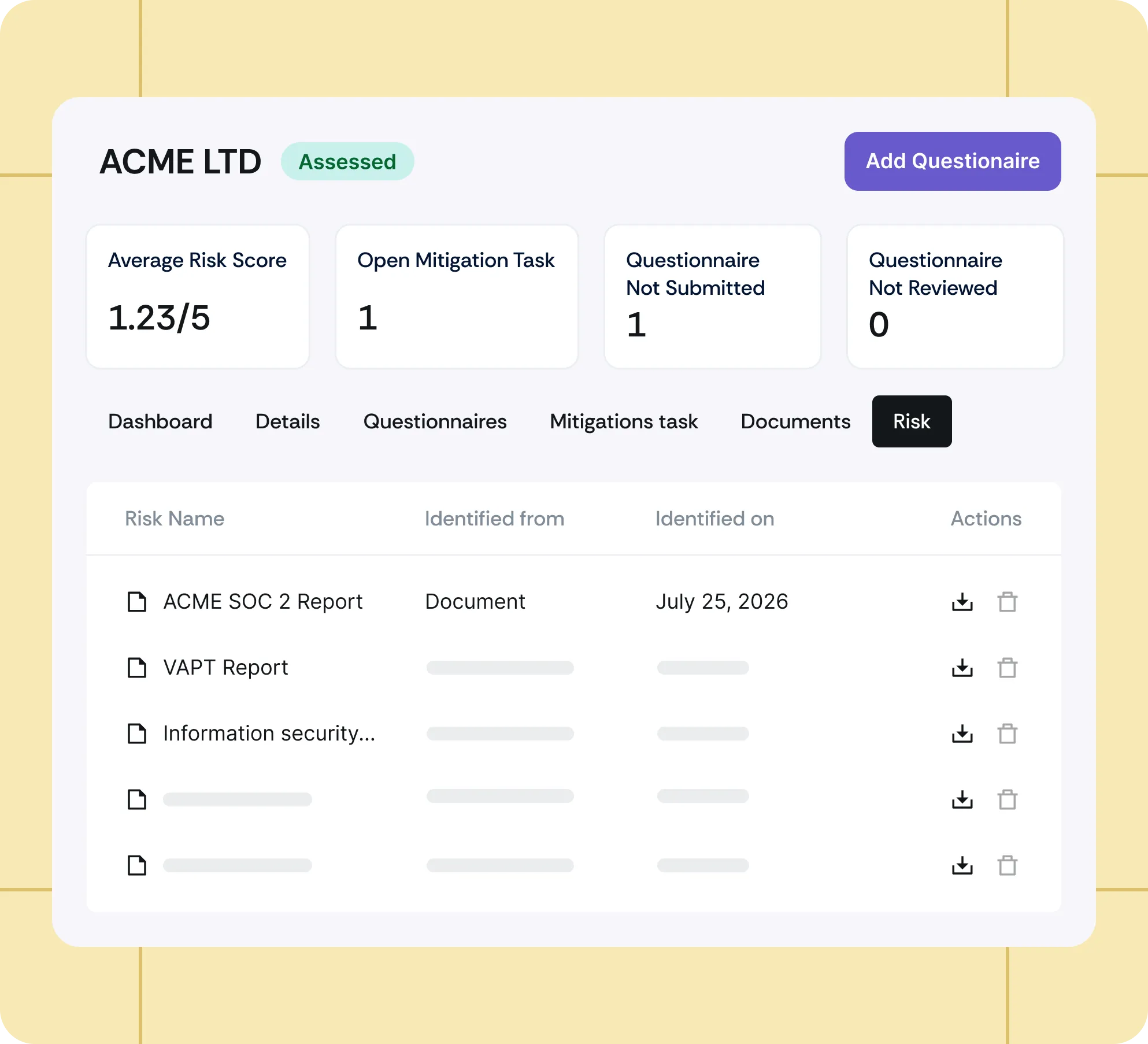
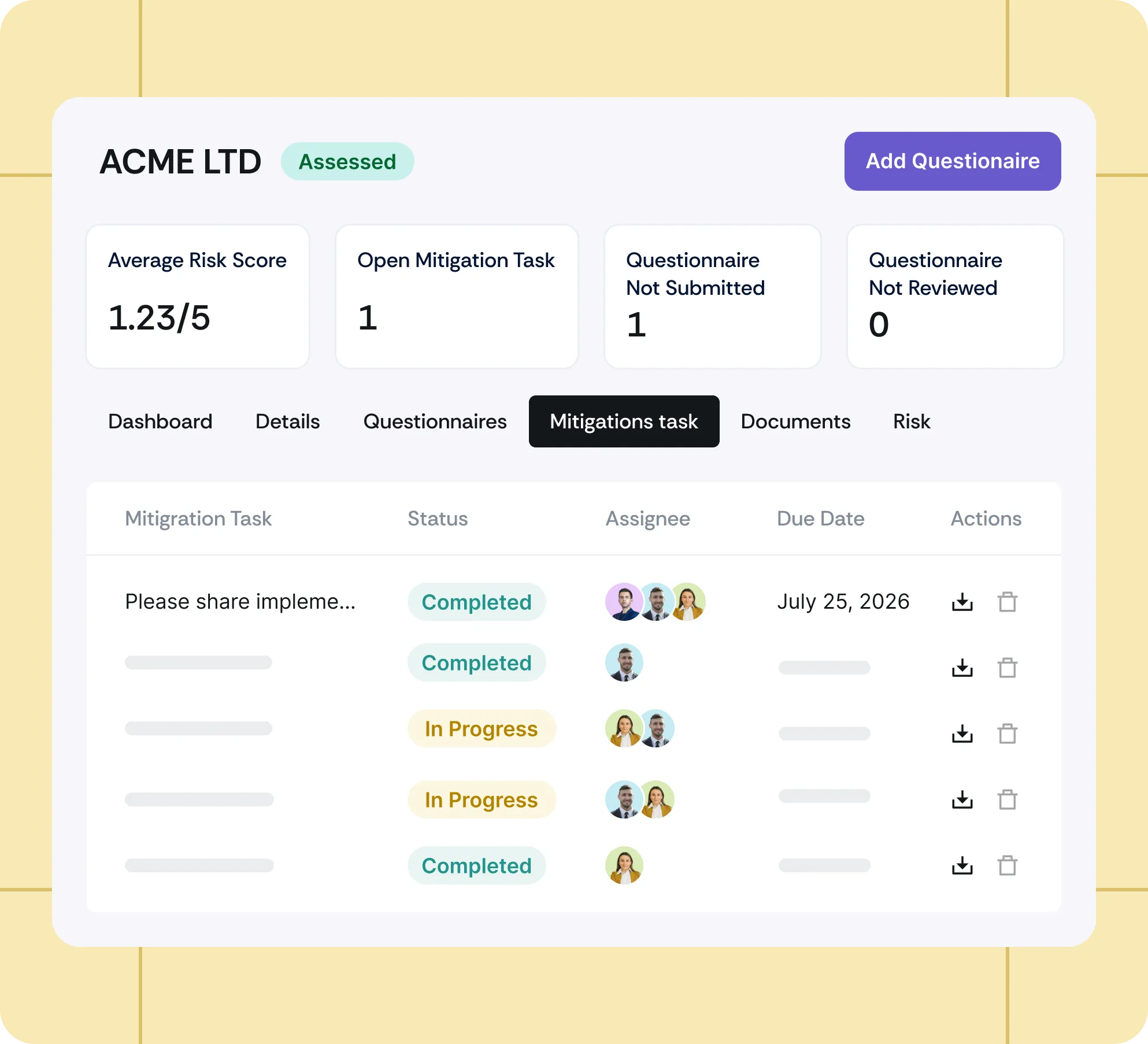








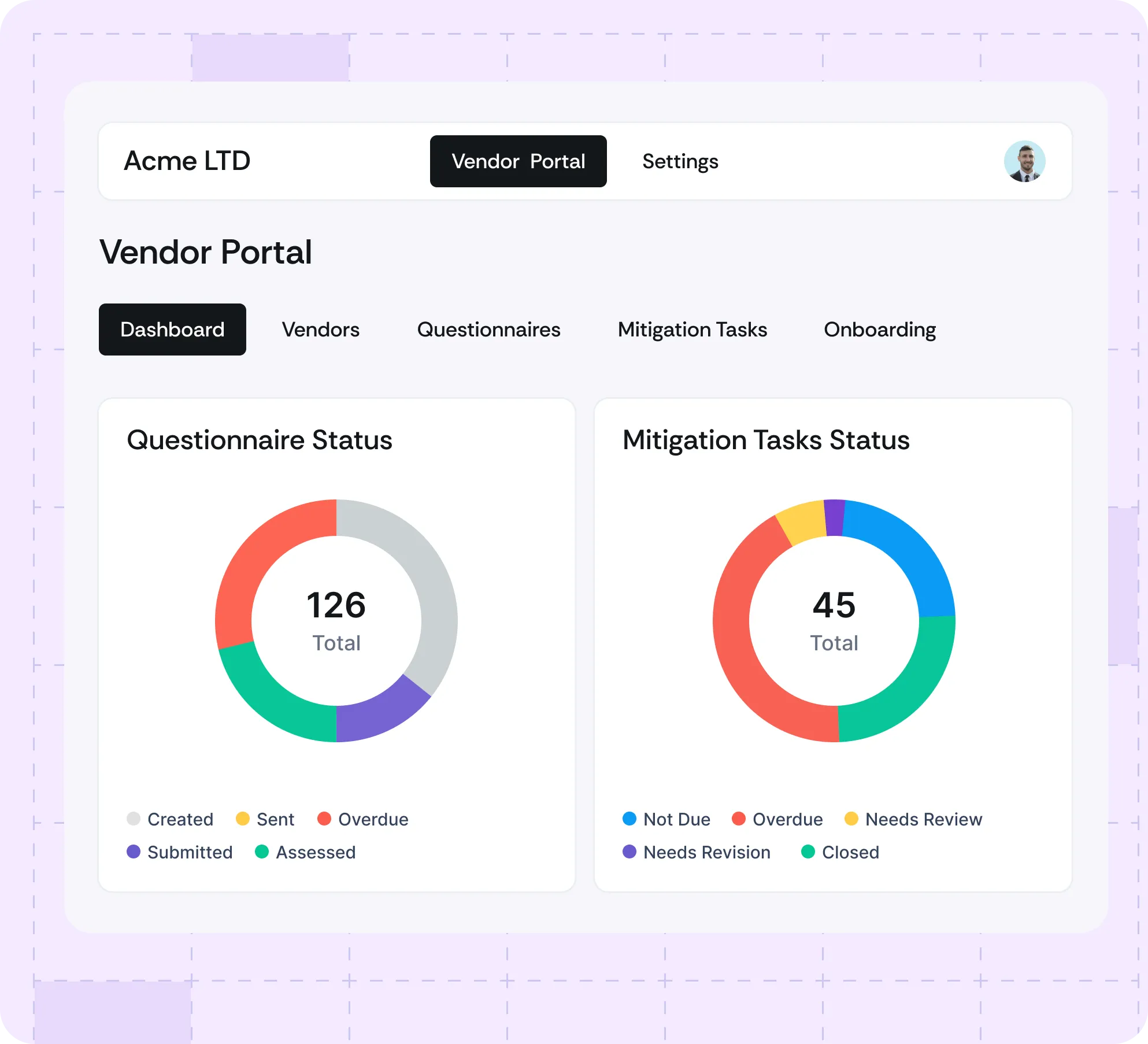

Security teams shouldn’t have to chase vendors for updates. Scrut keeps everything in one place, automates follow-ups, and ensures risks never slip through the cracks.
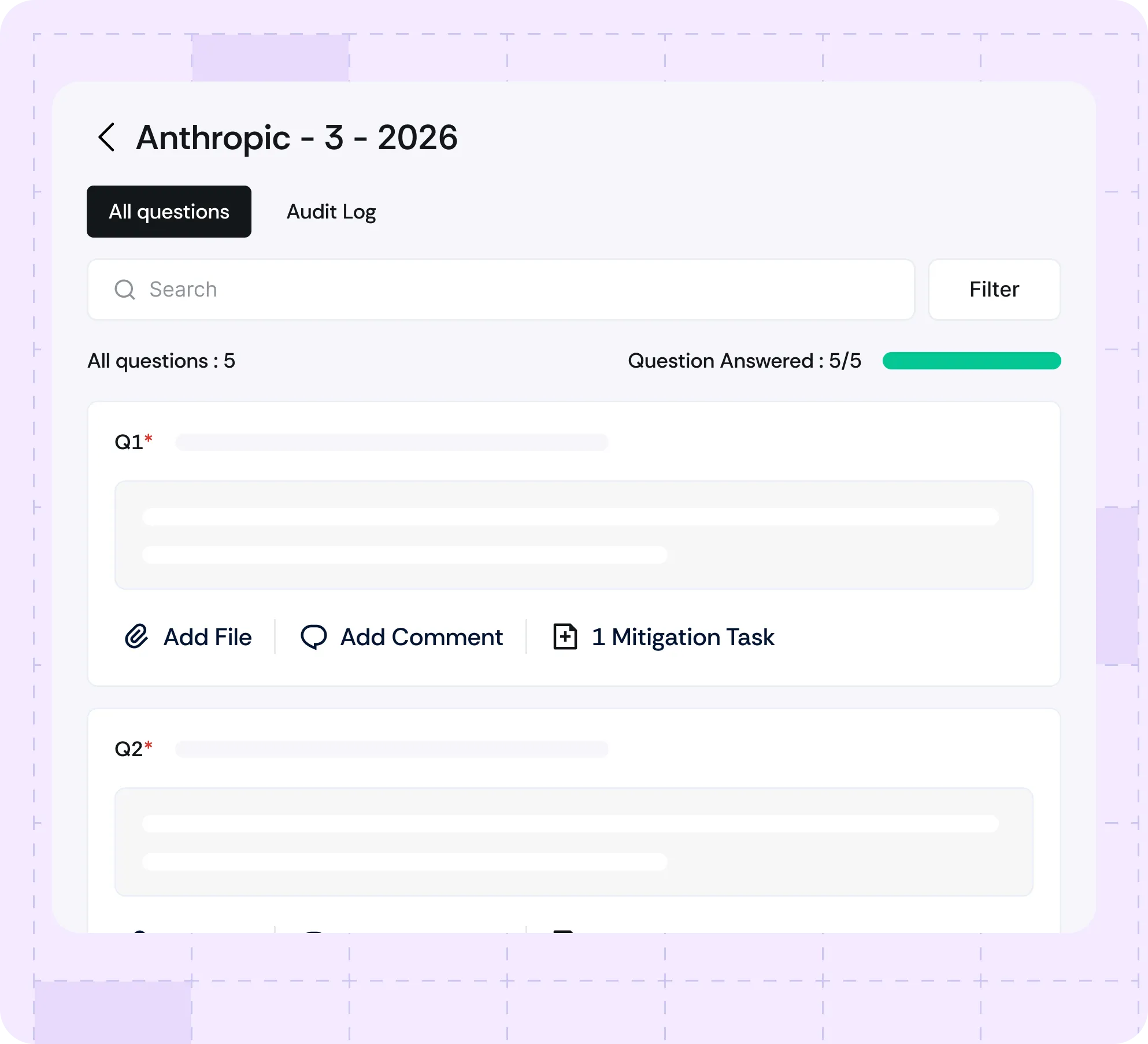
Automatically generate risk assessment questionnaires tailored to each vendor’s inherent risk level using Scrut Teammates.
Automatically generate risk assessment questionnaires tailored to each vendor’s inherent risk level using Scrut Teammates.
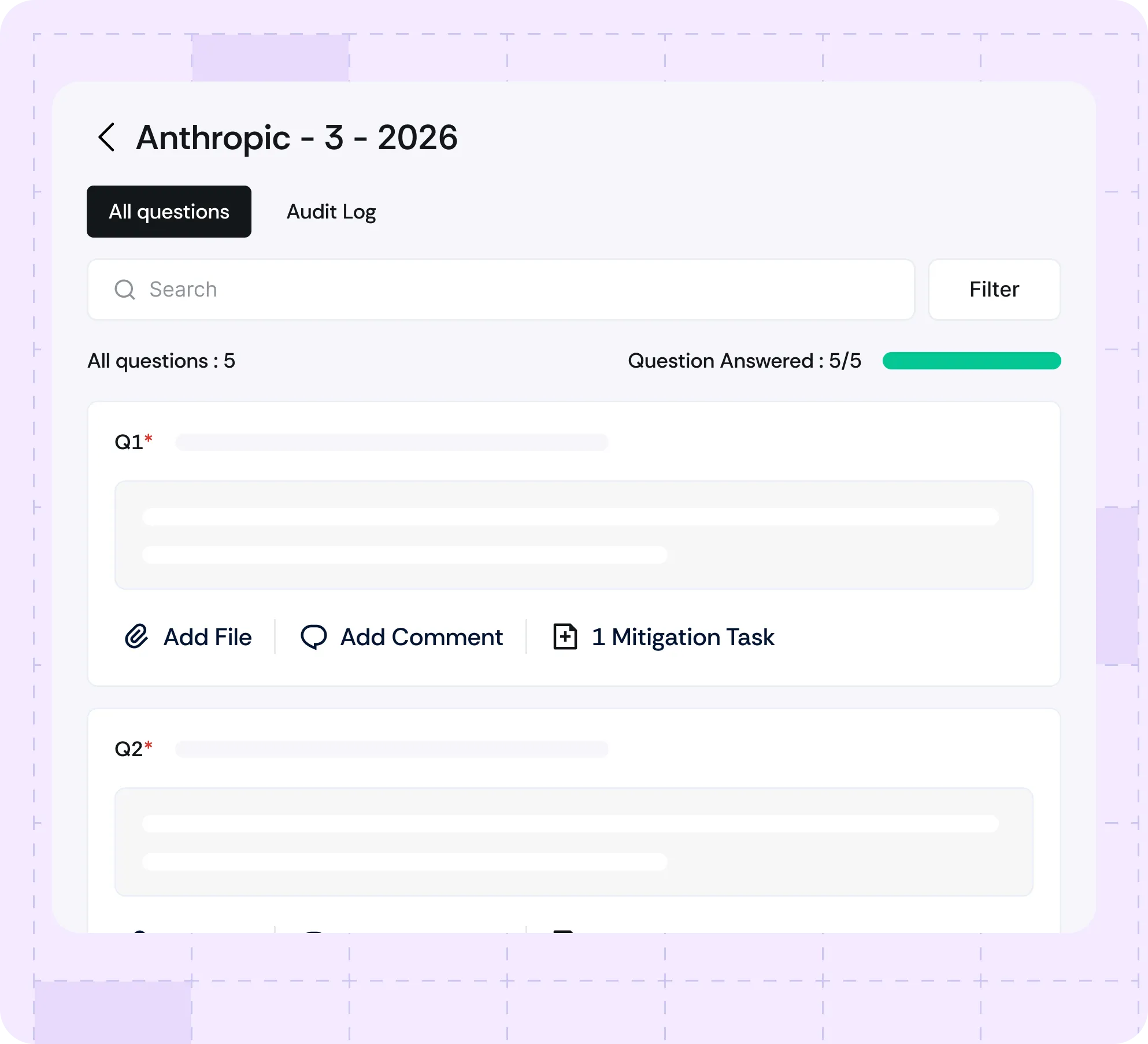
Ensure complete, high-quality vendor responses with AI-powered validation, and reduce manual follow-ups.
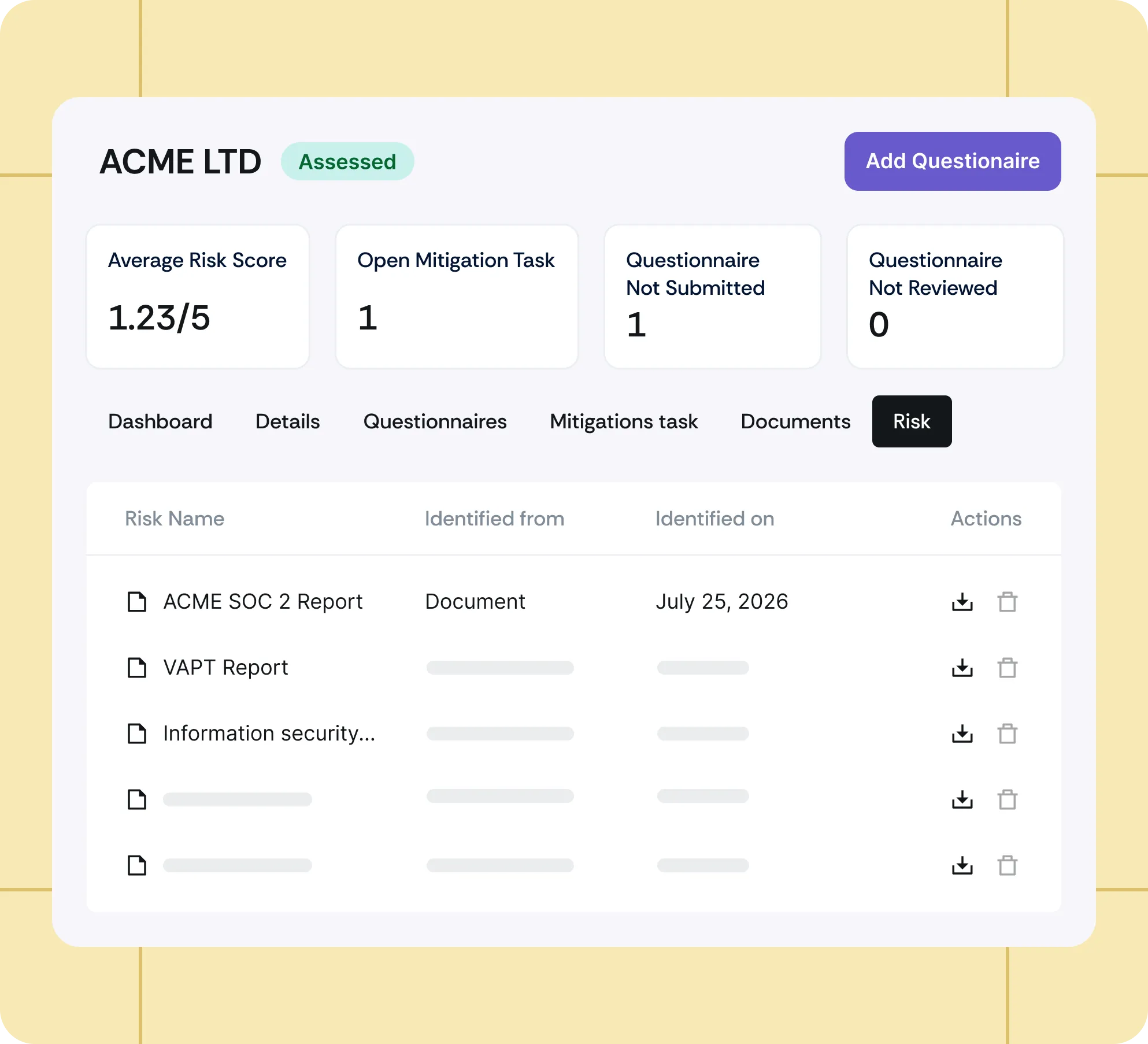
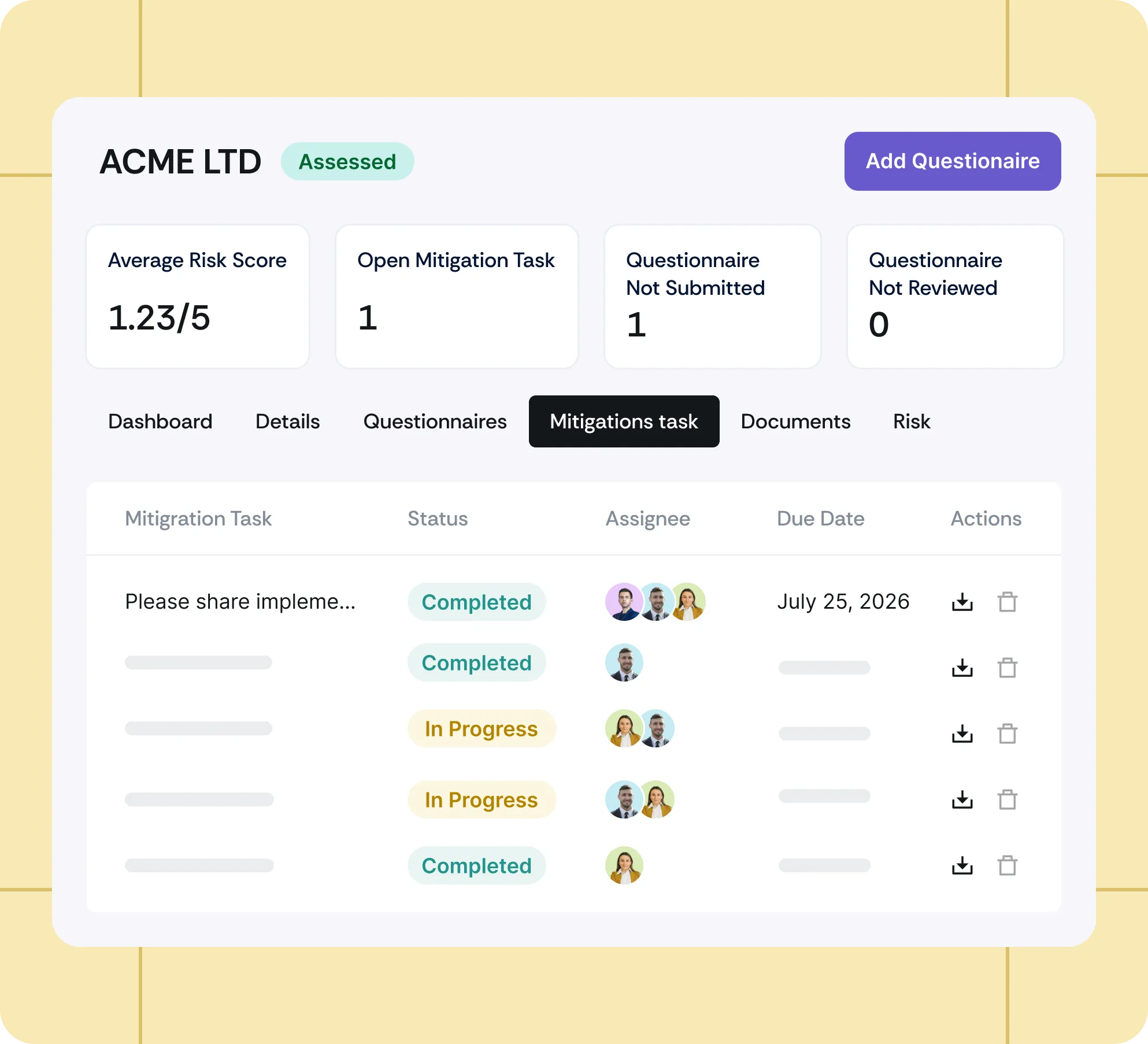
Generate AI-suggested mitigation tasks for identified risks automatically and track their progress to resolution.
Ensure complete, high-quality vendor responses with AI-powered validation, and reduce manual follow-ups.
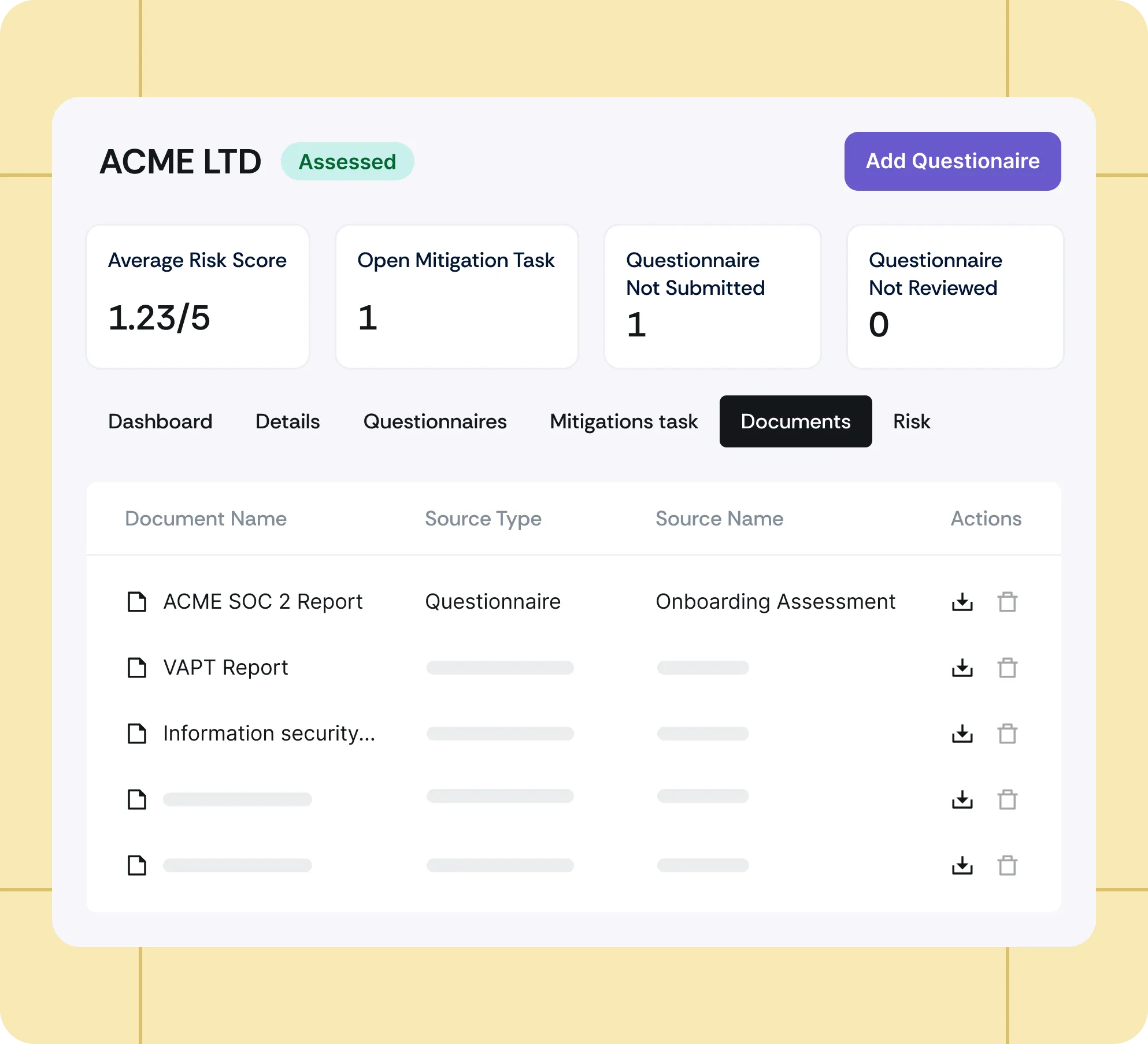
Automatically monitor online sources and surface active breach data and security threats about the vendor.
Automatically monitor online sources and surface active breach data and security threats about the vendor.
Use custom fields to capture additional vendor details and adapt profiles to your security needs.
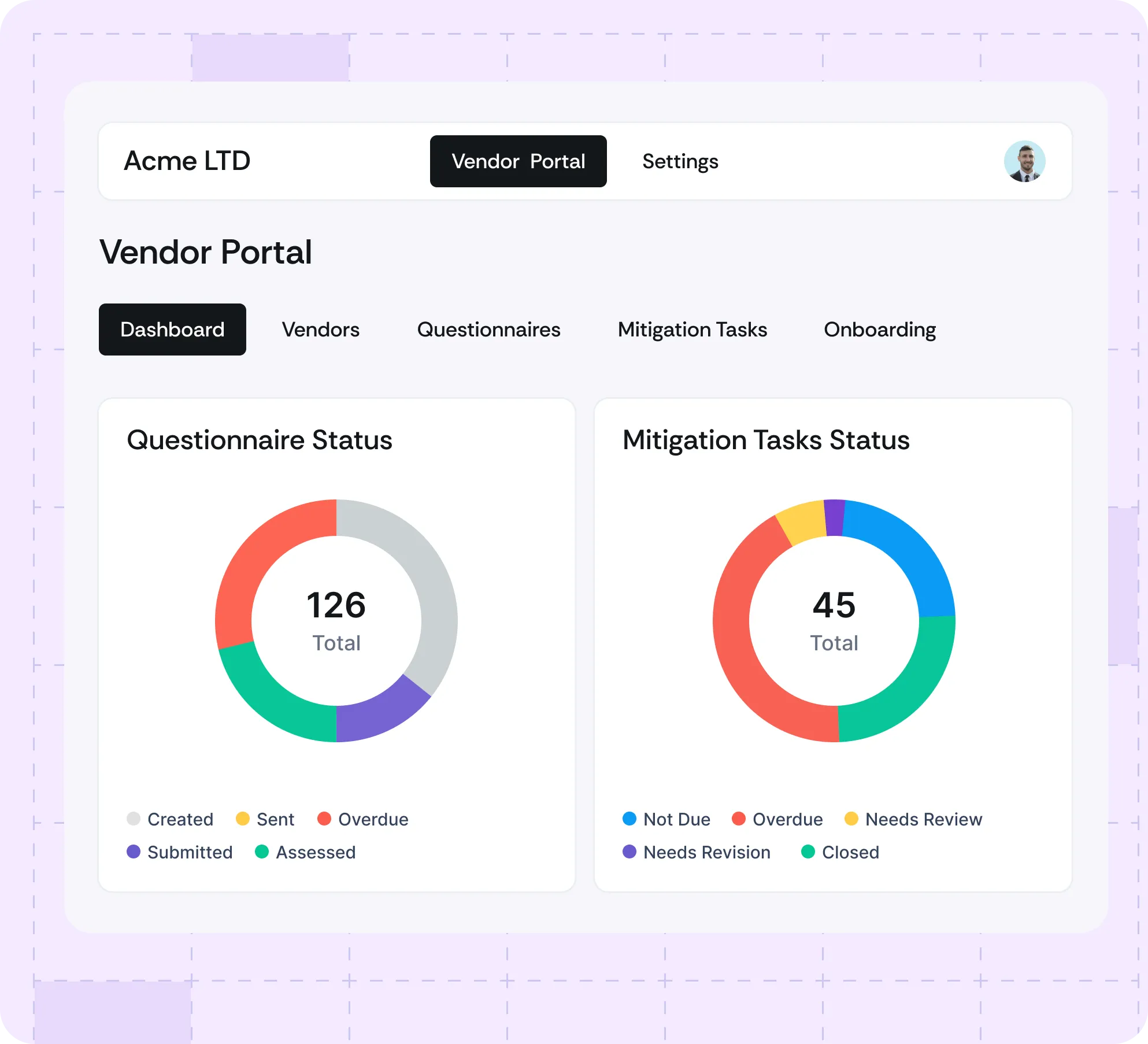
Gain real-time visibility into vendor risks and prioritize high-risk vendors. Generate reports to communicate progress to stakeholders.

Scrut makes it easier to manage both risk and vendors, helping us identify, assess, prioritize, and mitigate risks with ease.



Scrut’s vendor tracker makes it easy to see who’s submitted responses and who hasn’t.



Before Scrut, we managed vendor assessments in spreadsheets. Now it’s streamlined, with real-time tracking and reminders that make the process way more efficient.

