With an unrelenting wave of cyberattacks impacting companies of all sizes, customers and regulators are understandably focused on ensuring organizations maintaining sensitive data have effective security programs.
Unfortunately, these efforts have not evolved in a fully coordinated or standardized manner, leading to compliance frameworks sprawl. While enterprises generally have large governance, risk, and compliance (GRC) teams that can address these demands, mid-market businesses can struggle to ensure adherence to a web of overlapping demands.
In this post, we’ll take a look at the challenges associated with meeting multiple compliance standards and identify some key steps organizations can take to address them.
The challenge of compliance overload
Industries face multiple requirements
Organizations that work in a variety of different spaces unfortunately need to meet overlapping compliance requirements. The most extreme example is probably Palantir, which operates in healthcare, financial services, and in both U.S. and international government networks. As a result, it must comply with a vast array of standards.
While most organizations don’t have such comprehensive compliance requirements, it is quite common to see situations requiring adherence to at least two. For all but the largest companies, this can be a heavy administrative burden.
Challenges of compliance framework sprawl
As a result of this web of requirements, companies need to meet many requirements at the same time simply to do business and avoid regulatory penalties.
Body image: can we create clouds of these frameworks around a vector (similar to the first screen in UCF video)
Below are some common examples.
- General purpose and business-focused:
- Government-sponsored but non-prescriptive frameworks like the U.S. National Institute of Standards and Technology (NIST):
- Mandatory laws and regulations like the:
Documentation and control requirements vary across standards
Because of the varying motivations and histories of each framework, each has its own precise requirements that don’t necessarily have a direct equivalent in other standards.
- Whereas SOC 2 allows organizations to largely define their own control sets, ISO 27001 has more detailed requirements in the form of mandatory information security management system (ISMS) components.
- While GDPR applies to “personal data,” the CCPA applies to “personal information,” which have slightly different definitions.
- NIST 800-53 includes baselines of “low,” “moderate” and “high” that are not by themselves required by any standard, but which other standards will incorporate (such as the U.S. Federal Risk and Authorization Management Program (FedRAMP).
Managing complexity
Given the complexity that businesses face when it comes to compliance, having an effective program in place to manage it is critical. Important steps you can take include:
Designing controls comprehensively and flexibly
Whenever possible and appropriate, developing policies, procedures, and other controls usable across multiple frameworks is a best practice.
For example, SOC 2 does not specifically mandate vulnerability scanning or penetration testing on certain cadences. With that said, it makes sense from a cybersecurity perspective to establish such a program that meets or exceeds ISO 27001 standards. The latter framework requires timely identification of vulnerabilities, an assessment of the organization’s exposure to it, and the application of appropriate controls considering the risk.
Properly documenting a procedure meeting these criteria will both improve your organization’s security posture while making future ISO 27001 certification much easier.
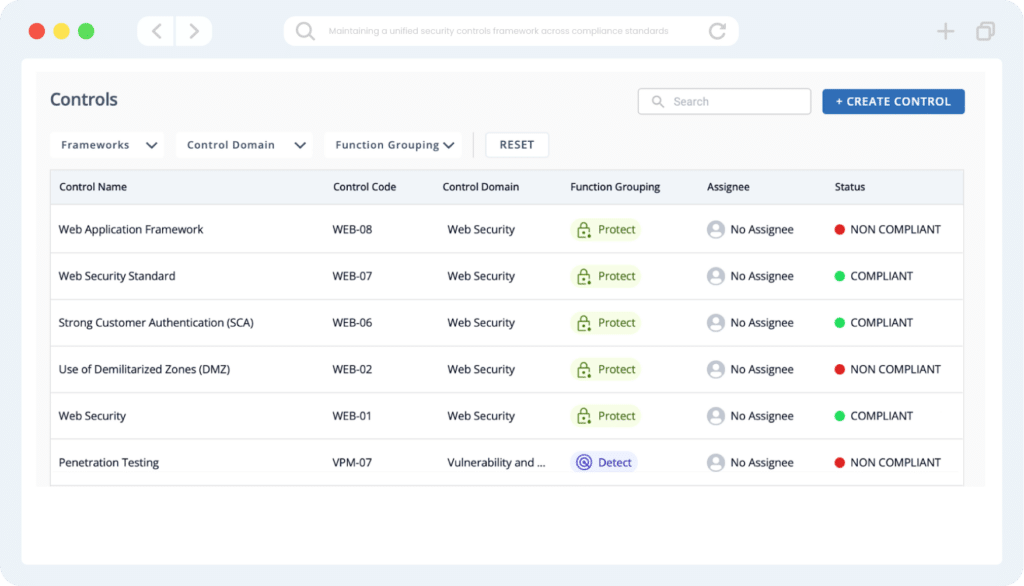
Maintaining a centralized risk register
Tracking all of the risks across your organization in a single place is essential to staying secure and meeting compliance requirements. While using spreadsheets or other generic tools might work for a while, a purpose-built risk register will eventually become necessary.
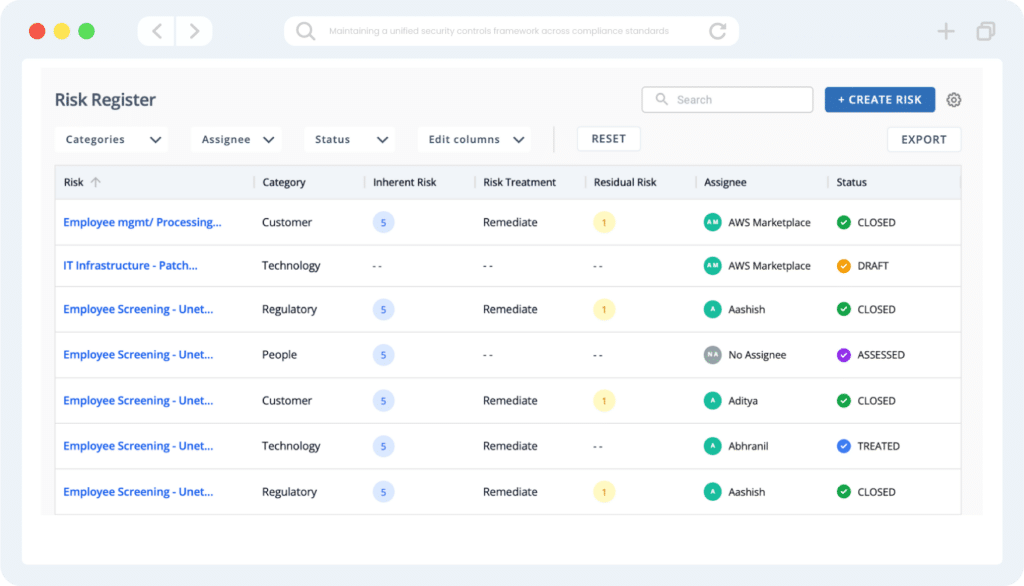
What is especially helpful when tangling with regulatory sprawl is a tool that can map risks and controls to specific frameworks. This can help you to stay on top of overlapping and duplicative requirements without pulling your hair out.
Track security and compliance-related tasks to completion
While having policies and other documentation in place is necessary for regulatory compliance, it is almost never sufficient. Actually implementing these requirements on a daily practice is what will protect your company and ensure you can pass audits.
Especially when dealing with a variety of different requirements across frameworks, ensuring that nothing slips through the cracks becomes critical. That’s why having a compliance-focused workflow management system can help you stay on top of a diverse set of rules and regulations. By reminding action owners and guiding them toward completion, you can rest more easily before the auditors come knocking.
Automating evidence collection
If you are going to face multiple types of audits, having an effective and automated process for collecting evidence is critical to avoiding business disruption while providing reviewers the documentation they need to give your business a stamp of approval.
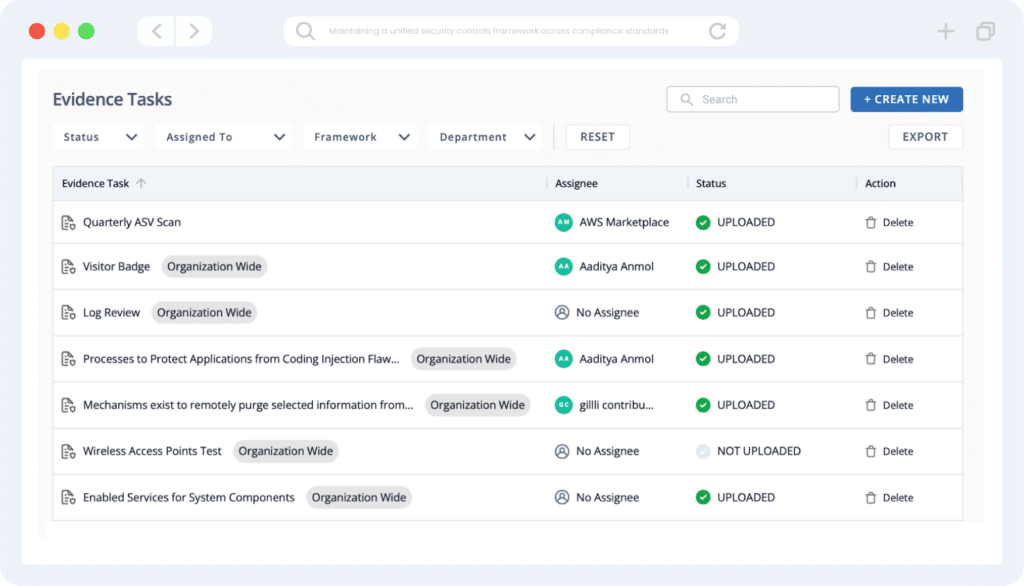
Since modern businesses run a wide array of different tools and software in their networks, manually pulling data from each one will quickly become unscalable. Thus, having a centralized platform that can continuously and monitor your cloud providers, code repositories, human resources systems, and similar applications will be incredibly helpful.
Conclusion
If you find yourself in the unenviable position of needing to meet multiple regulatory and compliance requirements, there are things you can do to streamline your GRC program and avoid some of the associated pain.
Developing a flexible set of controls, tracking risks in a centralized register, automating compliance tasks, and setting evidence collection on autopilot can go a long way. Having a well-developed and structured system for accomplishing all of these things, though, will be a prerequisite.
So if you are interested in seeing how Scrut can help you stay on top of an array of compliance frameworks, set up a call with one of our experts.