HIPAA compliance – Secure PHI in clicks!
- HIPAA Audit Centre for accelerated audits
- Single-window platform for all things HIPAA
- Onboarding with HIPAA compliance experts
- 75+ integrations for automated evidence collection
Book Your Free Consultation Call

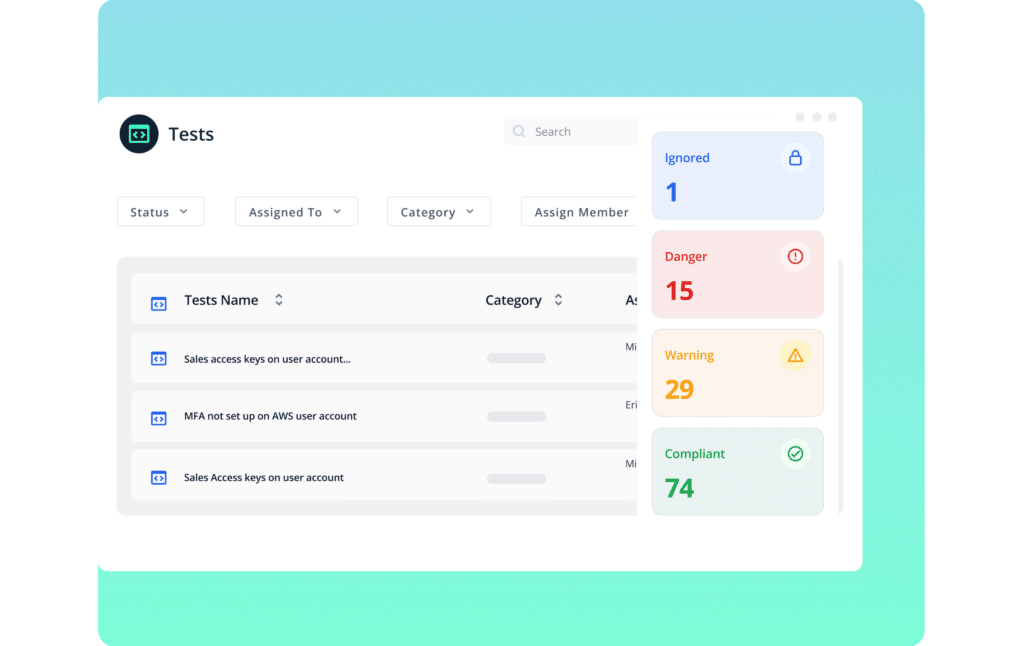
Strengthen your infosec program with defense systems
Focus on vulnerability alerts, leave audit overhead to us
Strengthen your infosec program
Identify compliance gaps so you can focus on what to fix.
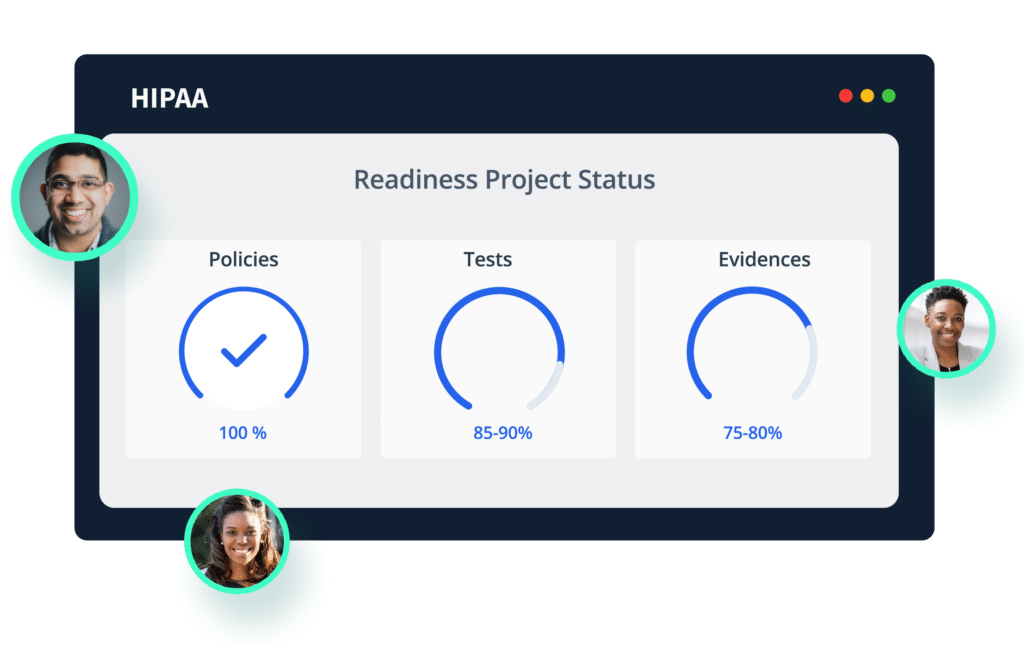
Get HIPAA audit-ready in weeks, not months
HIPAA compliant policies
50+ policy templates, customizable with an in-line editor
Automated gap assessment
In-built gap assessments to help you identify what needs to be fixed
HIPAA compliance experts
Onboarding with in-house infosec consultants, to get you ‘there’
Stay compliant, without manual effort
Continuous control monitoring
Alerts for any deviations, through continuous control monitoring
Seamless integrations
75+ pre-built integrations for automated control monitoring
Seamless workflows
Automated workflows to create, schedule, assign, and track tasks
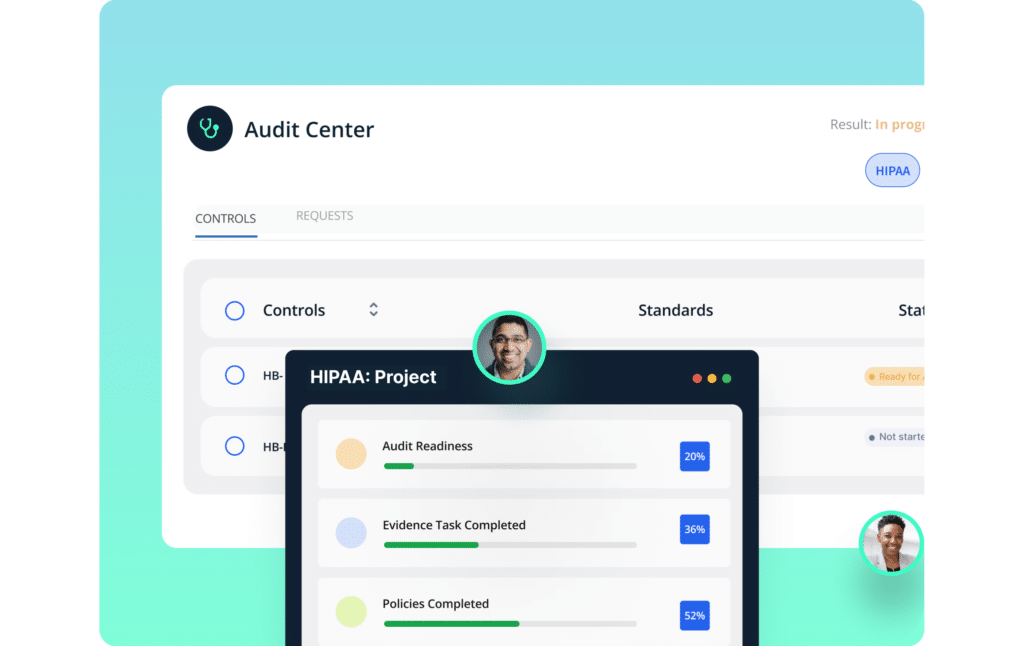
Accelerate audits, with seamless collaboration
Pre-mapped HIPAA controls
All policies, tasks, evidences pre-mapped to HIPAA controls
Automated evidence collection
70% less manual effort in collecting proof of compliance
HIPAA Audit Center
Auditors right on the platform for easy collaboration
Security with scale, without slippages
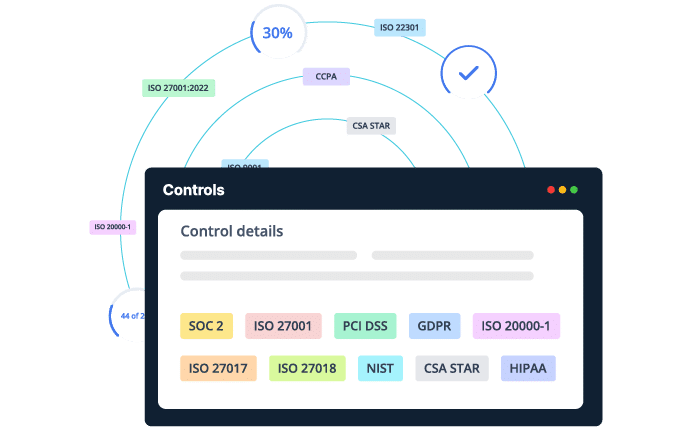
No hassle compliance with additional frameworks
21 frameworks, pre-mapped controls - right out of the box
Custom frameworks, and unifying frameworks
All your controls, mapped and monitored, in one place
GRC capabilities for all business units
Multiple product lines or multiple BUs: compliance for all
Save on costs as you scale
~50% efficient on cost of ownership
Recognized as a G2 Leader
On top of the leaderboard

With Scrut, compliance is:


Managing ISO 27001 and SOC 2 compliance was made indefinitely easier using Scrut’s platform. The dashboard helped us in maintaining all pieces of evidence and artifacts in one place.
Madhur Kaup
Director - Product Solutions,
Small-Business
Scrut’s smartGRC helped us make significant improvements in our security processes, enabling us to set up a stronger business model and get compliant with ISO 27001 and SOC 2.
Keshav Goud T
Compliance Manager,
Mid-Market
If you are looking to get SOC 2 and ISO 27001 compliant in a simplified way, Choose Scrut.
Lakshminarayana T.
Manager IT Operations,
Mid-Market
Scrut automation has been pivotal in helping us get compliant with ISO 27001, SOC 2, and GDPR.

Shubam Nigam
Business Strategy Specialist,
Mid-Market
Effortless integration with AWS and automated tasks using the SmartGRC platform powered by Scrut really proved to be beneficial for us in the compliance journey.

Srivatsan H.
Vice President - Technology,
Mid-Market
Scrut Automation has built a platform that not only integrates with our tools but also makes our lives easier through its simple and dynamic dashboards.

Chang Z.
Head of Engineering,
Mid-Market
Scrut automation streamlined all the compliance requirements for ISO 27001, SOC 2, and GDPR certifications.

Rakesh Nayak
Co-founder,
Small Business
Scrut centralized the entire compliance process for us, giving us a combined place for uploading evidence, network tests, and policies. Their automated tools made it easy to get SOC 2 and ISO certified within weeks.

Avinash Ramachandran
COO,
Small Business
The team delivered on its promise of being a one-stop shop for all our compliance requirements. They simplified the entire process by providing unwavering support. We definitely look forward to working with Scrut Automation for more certifications.

Wasim S
Chief of Staff,
Mid Market
From identification to setting standard policies in place, the team left no stone unturned in providing us with a seamless experience while respecting our time constraints.

Rejoy Cherian
Senior Manager,
Small Business
Scrut’s platform provides a complete compliance dashboard with tools for vendor management, ready-made employee training, and a network of reliable auditors.

Subham Goyal
Senior DevOps,
Mid Market
Scrut’s smartGRC simplified compliance for us, helping us build a robust security posture, compliant with ISO 27001 and SOC 2.

Tamishra Ray
Consultant,
Mid Market
Scrut is a user-friendly platform that allows you to eradicate any compliance-related friction with continuous cloud security and automated risk management.

Srinath P.
Lead Engineer, Co-Founder,
Small-Business
The SmartGRC platform has proved to be incredibly helpful for us in setting up our ISO and SOC compliance fast and hassle-free.

Anshu G
Corporate Success & Project Specialist,
Mid-Market
We were well guided throughout the process even though the platform was easy to navigate by itself. The integrations and centralized dashboard really simplified the process of SOC2 & ISO 27001 compliance.

Rajitha T.
HR Manager,
Mid-Market
Scrut helped us with SAR tokenization and ISO compliance management, which was difficult to achieve with most compliance tools out there. The cloud security tool integrated seamlessly with our cloud environment, making it easier for us to manage our cloud risks

Shyam Mishra
Manager
Mid-Market
Managing ISO 27001 and SOC 2 compliance was made indefinitely easier using Scrut’s platform. The dashboard helped us in maintaining all pieces of evidence and artifacts in one place.
Madhur Kaup
Director - Product Solutions,
Small-Business
Scrut’s smartGRC helped us make significant improvements in our security processes, enabling us to set up a stronger business model and get compliant with ISO 27001 and SOC 2.
Keshav Goud T
Compliance Manager,
Mid-Market
If you are looking to get SOC 2 and ISO 27001 compliant in a simplified way, Choose Scrut.
Lakshminarayana T.
Manager IT Operations,
Mid-Market
Scrut automation has been pivotal in helping us get compliant with ISO 27001, SOC 2, and GDPR.

Shubam Nigam
Business Strategy Specialist,
Mid-Market
Effortless integration with AWS and automated tasks using the SmartGRC platform powered by Scrut really proved to be beneficial for us in the compliance journey.

Srivatsan H.
Vice President - Technology,
Mid-Market
Scrut Automation has built a platform that not only integrates with our tools but also makes our lives easier through its simple and dynamic dashboards.

Chang Z.
Head of Engineering,
Mid-Market
Scrut automation streamlined all the compliance requirements for ISO 27001, SOC 2, and GDPR certifications.

Rakesh Nayak
Co-founder,
Small Business
Scrut centralized the entire compliance process for us, giving us a combined place for uploading evidence, network tests, and policies. Their automated tools made it easy to get SOC 2 and ISO certified within weeks.

Avinash Ramachandran
COO,
Small Business
The team delivered on its promise of being a one-stop shop for all our compliance requirements. They simplified the entire process by providing unwavering support. We definitely look forward to working with Scrut Automation for more certifications.

Wasim S
Chief of Staff,
Mid Market
From identification to setting standard policies in place, the team left no stone unturned in providing us with a seamless experience while respecting our time constraints.

Rejoy Cherian
Senior Manager,
Small Business
Scrut’s platform provides a complete compliance dashboard with tools for vendor management, ready-made employee training, and a network of reliable auditors.

Subham Goyal
Senior DevOps,
Mid Market
Scrut’s smartGRC simplified compliance for us, helping us build a robust security posture, compliant with ISO 27001 and SOC 2.

Tamishra Ray
Consultant,
Mid Market
Scrut is a user-friendly platform that allows you to eradicate any compliance-related friction with continuous cloud security and automated risk management.

Srinath P.
Lead Engineer, Co-Founder,
Small-Business
The SmartGRC platform has proved to be incredibly helpful for us in setting up our ISO and SOC compliance fast and hassle-free.

Anshu G
Corporate Success & Project Specialist,
Mid-Market
We were well guided throughout the process even though the platform was easy to navigate by itself. The integrations and centralized dashboard really simplified the process of SOC2 & ISO 27001 compliance.

Rajitha T.
HR Manager,
Mid-Market
Scrut helped us with SAR tokenization and ISO compliance management, which was difficult to achieve with most compliance tools out there. The cloud security tool integrated seamlessly with our cloud environment, making it easier for us to manage our cloud risks

Shyam Mishra
Manager
Mid-Market
Managing ISO 27001 and SOC 2 compliance was made indefinitely easier using Scrut’s platform. The dashboard helped us in maintaining all pieces of evidence and artifacts in one place.
Madhur Kaup
Director - Product Solutions,
Small-Business
Scrut’s smartGRC helped us make significant improvements in our security processes, enabling us to set up a stronger business model and get compliant with ISO 27001 and SOC 2.
Keshav Goud T
Compliance Manager,
Mid-Market
If you are looking to get SOC 2 and ISO 27001 compliant in a simplified way, Choose Scrut.
Lakshminarayana T.
Manager IT Operations,
Mid-Market
Scrut automation has been pivotal in helping us get compliant with ISO 27001, SOC 2, and GDPR.

Shubam Nigam
Business Strategy Specialist,
Mid-Market
Effortless integration with AWS and automated tasks using the SmartGRC platform powered by Scrut really proved to be beneficial for us in the compliance journey.

Srivatsan H.
Vice President - Technology,
Mid-Market
Scrut Automation has built a platform that not only integrates with our tools but also makes our lives easier through its simple and dynamic dashboards.

Chang Z.
Head of Engineering,
Mid-Market
Scrut automation streamlined all the compliance requirements for ISO 27001, SOC 2, and GDPR certifications.

Rakesh Nayak
Co-founder,
Small Business
Scrut centralized the entire compliance process for us, giving us a combined place for uploading evidence, network tests, and policies. Their automated tools made it easy to get SOC 2 and ISO certified within weeks.

Avinash Ramachandran
COO,
Small Business
The team delivered on its promise of being a one-stop shop for all our compliance requirements. They simplified the entire process by providing unwavering support. We definitely look forward to working with Scrut Automation for more certifications.

Wasim S
Chief of Staff,
Mid Market
From identification to setting standard policies in place, the team left no stone unturned in providing us with a seamless experience while respecting our time constraints.

Rejoy Cherian
Senior Manager,
Small Business
Scrut’s platform provides a complete compliance dashboard with tools for vendor management, ready-made employee training, and a network of reliable auditors.

Subham Goyal
Senior DevOps,
Mid Market
Scrut’s smartGRC simplified compliance for us, helping us build a robust security posture, compliant with ISO 27001 and SOC 2.

Tamishra Ray
Consultant,
Mid Market
Scrut is a user-friendly platform that allows you to eradicate any compliance-related friction with continuous cloud security and automated risk management.

Srinath P.
Lead Engineer, Co-Founder,
Small-Business
The SmartGRC platform has proved to be incredibly helpful for us in setting up our ISO and SOC compliance fast and hassle-free.

Anshu G
Corporate Success & Project Specialist,
Mid-Market
We were well guided throughout the process even though the platform was easy to navigate by itself. The integrations and centralized dashboard really simplified the process of SOC2 & ISO 27001 compliance.

Rajitha T.
HR Manager,
Mid-Market
Scrut helped us with SAR tokenization and ISO compliance management, which was difficult to achieve with most compliance tools out there. The cloud security tool integrated seamlessly with our cloud environment, making it easier for us to manage our cloud risks

Shyam Mishra
Manager
Mid-Market
Managing ISO 27001 and SOC 2 compliance was made indefinitely easier using Scrut’s platform. The dashboard helped us in maintaining all pieces of evidence and artifacts in one place.
Madhur Kaup
Director - Product Solutions,
Small-Business
Scrut’s smartGRC helped us make significant improvements in our security processes, enabling us to set up a stronger business model and get compliant with ISO 27001 and SOC 2.
Keshav Goud T
Compliance Manager,
Mid-Market
If you are looking to get SOC 2 and ISO 27001 compliant in a simplified way, Choose Scrut.
Lakshminarayana T.
Manager IT Operations,
Mid-Market
Scrut automation has been pivotal in helping us get compliant with ISO 27001, SOC 2, and GDPR.

Shubam Nigam
Business Strategy Specialist,
Mid-Market
Effortless integration with AWS and automated tasks using the SmartGRC platform powered by Scrut really proved to be beneficial for us in the compliance journey.

Srivatsan H.
Vice President - Technology,
Mid-Market
Scrut Automation has built a platform that not only integrates with our tools but also makes our lives easier through its simple and dynamic dashboards.

Chang Z.
Head of Engineering,
Mid-Market
Scrut automation streamlined all the compliance requirements for ISO 27001, SOC 2, and GDPR certifications.

Rakesh Nayak
Co-founder,
Small Business
Scrut centralized the entire compliance process for us, giving us a combined place for uploading evidence, network tests, and policies. Their automated tools made it easy to get SOC 2 and ISO certified within weeks.

Avinash Ramachandran
COO,
Small Business
The team delivered on its promise of being a one-stop shop for all our compliance requirements. They simplified the entire process by providing unwavering support. We definitely look forward to working with Scrut Automation for more certifications.

Wasim S
Chief of Staff,
Mid Market
From identification to setting standard policies in place, the team left no stone unturned in providing us with a seamless experience while respecting our time constraints.

Rejoy Cherian
Senior Manager, Cognicor
Scrut’s platform provides a complete compliance dashboard with tools for vendor management, ready-made employee training, and a network of reliable auditors.

Subham Goyal
Senior DevOps,
Mid Market
Scrut’s smartGRC simplified compliance for us, helping us build a robust security posture, compliant with ISO 27001 and SOC 2.

Tamishra Ray
Consultant,
Mid Market
Scrut is a user-friendly platform that allows you to eradicate any compliance-related friction with continuous cloud security and automated risk management.

Srinath P.
Lead Engineer, Co-Founder,
Small-Business
The SmartGRC platform has proved to be incredibly helpful for us in setting up our ISO and SOC compliance fast and hassle-free.

Anshu G
Corporate Success & Project Specialist,
Mid-Market
We were well guided throughout the process even though the platform was easy to navigate by itself. The integrations and centralized dashboard really simplified the process of SOC2 & ISO 27001 compliance.

Rajitha T.
HR Manager,
Mid-Market
Scrut helped us with SAR tokenization and ISO compliance management, which was difficult to achieve with most compliance tools out there. The cloud security tool integrated seamlessly with our cloud environment, making it easier for us to manage our cloud risks

Shyam Mishra
Manager
Mid-Market
Managing ISO 27001 and SOC 2 compliance was made indefinitely easier using Scrut’s platform. The dashboard helped us in maintaining all pieces of evidence and artifacts in one place.
Madhur Kaup
Director - Product Solutions,
Small-Business
Scrut’s smartGRC helped us make significant improvements in our security processes, enabling us to set up a stronger business model and get compliant with ISO 27001 and SOC 2.
Keshav Goud T
Compliance Manager,
Mid-Market
If you are looking to get SOC 2 and ISO 27001 compliant in a simplified way, Choose Scrut.
Lakshminarayana T.
Manager IT Operations,
Mid-Market
Scrut automation has been pivotal in helping us get compliant with ISO 27001, SOC 2, and GDPR.

Shubam Nigam
Business Strategy Specialist,
Mid-Market
Effortless integration with AWS and automated tasks using the SmartGRC platform powered by Scrut really proved to be beneficial for us in the compliance journey.

Srivatsan H.
Vice President - Technology,
Mid-Market
Scrut Automation has built a platform that not only integrates with our tools but also makes our lives easier through its simple and dynamic dashboards.

Chang Z.
Head of Engineering,
Mid-Market
Scrut automation streamlined all the compliance requirements for ISO 27001, SOC 2, and GDPR certifications.

Rakesh Nayak
Co-founder,
Small Business
Scrut centralized the entire compliance process for us, giving us a combined place for uploading evidence, network tests, and policies. Their automated tools made it easy to get SOC 2 and ISO certified within weeks.

Avinash Ramachandran
COO,
Small Business
The team delivered on its promise of being a one-stop shop for all our compliance requirements. They simplified the entire process by providing unwavering support. We definitely look forward to working with Scrut Automation for more certifications.

Wasim S
Chief of Staff,
Mid Market
From identification to setting standard policies in place, the team left no stone unturned in providing us with a seamless experience while respecting our time constraints.

Rejoy Cherian
Senior Manager,
Small Business
Scrut’s platform provides a complete compliance dashboard with tools for vendor management, ready-made employee training, and a network of reliable auditors.

Subham Goyal
Senior DevOps,
Mid Market
Scrut’s smartGRC simplified compliance for us, helping us build a robust security posture, compliant with ISO 27001 and SOC 2.

Tamishra Ray
Consultant,
Mid Market
Scrut is a user-friendly platform that allows you to eradicate any compliance-related friction with continuous cloud security and automated risk management.

Srinath P.
Lead Engineer, Co-Founder,
Small-Business
The SmartGRC platform has proved to be incredibly helpful for us in setting up our ISO and SOC compliance fast and hassle-free.

Anshu G
Corporate Success & Project Specialist,
Mid-Market
We were well guided throughout the process even though the platform was easy to navigate by itself. The integrations and centralized dashboard really simplified the process of SOC2 & ISO 27001 compliance.

Rajitha T.
HR Manager,
Mid-Market
Scrut helped us with SAR tokenization and ISO compliance management, which was difficult to achieve with most compliance tools out there. The cloud security tool integrated seamlessly with our cloud environment, making it easier for us to manage our cloud risks

Shyam Mishra
Manager
Mid-Market
How Scrut Automation Works
Frequently asked questions
What is HIPAA Compliance?
HIPAA was created to safeguard the confidentiality, integrity, and availability of protected health information (PHI). HIPAA compliance is the act of being on par with HIPAA regulations, standards, and implementation specifications, i.e., checking if entities are following HIPAA’s policies to meet its standards for data security and privacy.
What is covered under HIPAA compliance?
HIPAA requires “covered entities” to implement security and data privacy controls to protect patient’s health information from unauthorized access. HIPAA rules apply equally to all types of covered entities, including health plans, health care clearinghouses, and health care providers who are responsible for transmitting healthcare data in a HIPAA-compliant manner. HIPAA compliance is also required for Business Associates who create, access, process, or store PHI.
What is PHI (Protected Health Information)?
Information about a person’s past, present, or potential health condition that is gathered from them by a covered entity must be protected because it either identifies the person or there is a good reason to think that it can be used to find, identify, or get in touch with them.
Who needs to comply with HIPAA? Is it legally required?
HIPAA is a legal obligation under which all covered entities are mandated to establish security and data privacy controls to protect PHI from unauthorized access. Examples of covered entities required by law to abide by HIPAA regulations include healthcare providers, insurance providers, and clearinghouses. In this context, health care providers include physicians, hospitals, and medical, dental, and vision care facilities.
Is HIPAA applicable to wearables and medical devices?
It can be if the device collects, stores, or transmits PHI (for example, glucose levels associated with a specific person) to a Covered Entity or Business Associate organization. More medical devices, wearables, and IoT devices include built-in microprocessors and WiFi/Bluetooth, allowing them to store PHI data and transmit it to the cloud, where any healthcare entity can access it.
Are business associates and covered entities using the same HIPAA Compliance Software?
Any business adhering to HIPAA regulations can benefit largely from compliance software. It enables both covered entities and associates to audit their sensitive data and security measures to determine where they are already compliant, where they aren’t, and how to close remaining gaps.
What does a HIPAA violation include?
HIPAA violation includes actions such as failing to keep PHI private, inappropriately accessing PHI data, or sending PHI via insecure methods. Individual health information violations can result in fines of up to $250,000 or imprisonment for up to ten years.
How is HIPAA different from HITECH?
While the HIPAA Privacy Rule allows patients to access and manage their own PHI, the HITECH Act expands those rights by enabling patients to obtain electronic copies of their health records, provided that the covered entity keeps those records in that format. Additionally, HITECH forbids businesses from selling PHI unless very specific, limited circumstances apply. This successfully prevented service providers from making money off of treatment suggestions.
What does the HIPAA Security Rule mean?
The security standards meant for protecting the confidentiality, integrity, and availability of PHI are covered under the HIPAA security rule. It stipulates that covered entities must implement technical safeguards to prevent unauthorized access and related security incidents.
Why is HIPAA challenging?
Organizations that create, maintain, or transmit protected health information (PHI) are required by HIPAA to abide by its rules. HIPAA is mandatory, in contrast to SOC 2 and ISO 27001, and non-compliance with the framework can result in hefty fines.
Since HIPAA does not mandate a third-party audit, it is difficult to know your compliance status at any given time. With the help of Scrut Automation’s HIPAA compliance framework, you can maintain compliance easily.