Choose risk-first compliance that’s always on, built for you.
Go back to blogs
SOC 2 Compliance Timeline: How Long Does It Take to Achieve Compliance?
Last updated on
June 24, 2025
min. read

How long does it really take to get SOC 2 compliant? The short answer: most organisations can expect a timeline of 6 to 12 months for their first audit. For a SOC 2 Type I, which examines your controls at a single point in time, it’s often closer to 3 to 6 months. But if you’re going for a Type II, the journey typically extends to 6 to 12 months, since auditors observe your controls over a set period to ensure they’re operating effectively.
Once you’ve crossed the finish line the first time, renewals are faster. SOC 2 reports are valid for 12 months, meaning you’ll need to schedule a renewal audit within that window. Most organisations complete the renewal process in 6 to 8 months, thanks to established systems and lessons learned during their initial run.
Of course, these are just averages. The truth is, no two SOC 2 journeys are alike. Your timeline depends on how ready your organisation is, the complexity of your environment, the type of audit you’re aiming for, and how quickly you can get the right processes and policies in place.
In this blog, we’ll unpack all the factors that influence the clock, break down each stage of the SOC 2 timeline, and share how you can get to compliance faster, without cutting corners.
Why there’s no single answer to the SOC 2 timeline
There’s no universal timeline for SOC 2 because every organisation starts from a different place. A startup with a simple tech stack and good security hygiene might be ready in a few months. But a larger company with complex systems and gaps to close could take closer to a year.
Think of it like building a fortress: you can’t throw up walls on quicksand and hope they hold. Rushing without solid foundations often leads to delays later when auditors uncover weak spots. Taking the time to set up the right controls from the start not only keeps your timeline realistic but also ensures your compliance posture will stand the test of time.
However, let’s make an educated guess about how long it might take to be SOC 2 compliant.
SOC 2 Type I audit process and timeline
A SOC 2 Type I audit assesses whether your controls are designed effectively at a single point in time. It’s like a snapshot of your security posture. It is useful for showing early commitment to compliance, but not enough to prove ongoing effectiveness. Most organisations complete the entire process in 3 to 6 months, covering preparation, implementation, and the auditor’s review.
The process typically unfolds in two phases:
1. Pre-audit phase (2–3 months)
This is where most of the work happens. You’ll define your audit scope, draft and implement required policies, and remediate any gaps identified during a readiness assessment. For many organisations, this phase takes 8 to 12 weeks, depending on how mature their security practices are.
2. Audit phase (2–5 weeks)
Once your auditor steps in, they’ll review your controls, interview key team members, and test documentation. Because Type I doesn’t involve observing controls over time, the fieldwork is relatively short. After this, the auditor will draft your SOC 2 report, typically within a few additional weeks.
SOC 2 Type II audit process and timeline
A SOC 2 Type II audit builds on Type I. It doesn’t just ask whether your controls exist. It tests if they operate effectively over a set period (the observation period). The entire process usually takes 6 to 12 months, depending on the length of your observation period and how prepared your organization is.
1. Pre-audit phase (2–3 months)
Just like Type I, you’ll begin by defining the scope and preparing policies. If you’ve recently completed a Type I, much of this groundwork will already be in place, potentially shortening the timeline.
2. Observation period (3–12 months)
This is unique to Type II. Auditors review evidence from a 3, 6, or 12-month period, depending on your chosen audit window. The longer the period, the stronger the assurance in your SOC 2 report, but also the longer it takes to reach the finish line.
3. Audit phase (4–8 weeks)
After the observation period, the auditor conducts fieldwork similar to Type I but with a focus on evidence that your controls were consistently applied throughout. The final report follows shortly after.
4. Renewal audits (6–8 months)
Technically, SOC 2 reports don’t ‘expire’. However, they are considered outdated after a period of 12 months and you’ll need to undergo a renewal audit within that timeframe to maintain compliance. The renewal process is typically faster because your controls and processes are already in place. It involves a fresh observation period and a shorter audit phase, focusing on demonstrating that your security posture has remained effective over time.
Which SOC 2 audit type should I start with?
If you’re new to SOC 2, starting with Type I is often the smarter choice. It’s faster to achieve and helps you demonstrate that the right controls are in place at a specific point in time. Many organizations use it as a stepping stone to prepare for Type II, which requires proving that those controls operate effectively over a longer period.
However, if your customers or contracts explicitly ask for a SOC 2 Type II report, or if you already have strong processes in place, you can go straight for Type II. Just be ready for the longer timeline and observation period it involves.
Do you need Type II right after Type I?
Yes, it’s strongly recommended if you want to demonstrate operational maturity. Type I is often a stepping stone, ideal for startups and organizations starting from scratch. But most customers and partners expect a SOC 2 Type II report because it verifies how well your controls work in practice.
That said, you may not need to pursue Type II immediately if your business doesn’t handle sensitive customer data yet or if no contractual obligations demand it.
If you’re using Type I as a springboard, plan to start your Type II observation period immediately after receiving your Type I report. This avoids losing momentum and keeps your compliance efforts continuous.
What is the validity of the SOC 2 audit report?
A SOC 2 report is valid for 12 months from the date it’s issued. After that, you’ll need to undergo a renewal audit to maintain continuous compliance and assure customers that your controls are still effective.
Is the SOC 2 audit a continuous process?
Yes. While the formal audit happens annually, maintaining SOC 2 compliance is a continuous process because security and privacy risks evolve constantly. Controls must operate effectively year-round, not just at audit time, to protect customer data and meet contractual or regulatory expectations.
Auditors for a Type II report also review evidence from the entire observation period, making it crucial to monitor and address compliance gaps as they arise. This approach not only avoids surprises during audits but also demonstrates to customers that security is built into your operations, not treated as a checkbox exercise.
How often should SOC 2 audits be done?
SOC 2 audits should be done annually. Since SOC 2 reports are valid for 12 months, scheduling a renewal audit every year helps maintain continuous compliance and keeps your attestation current.
Factors affecting the SOC 2 audit timeline
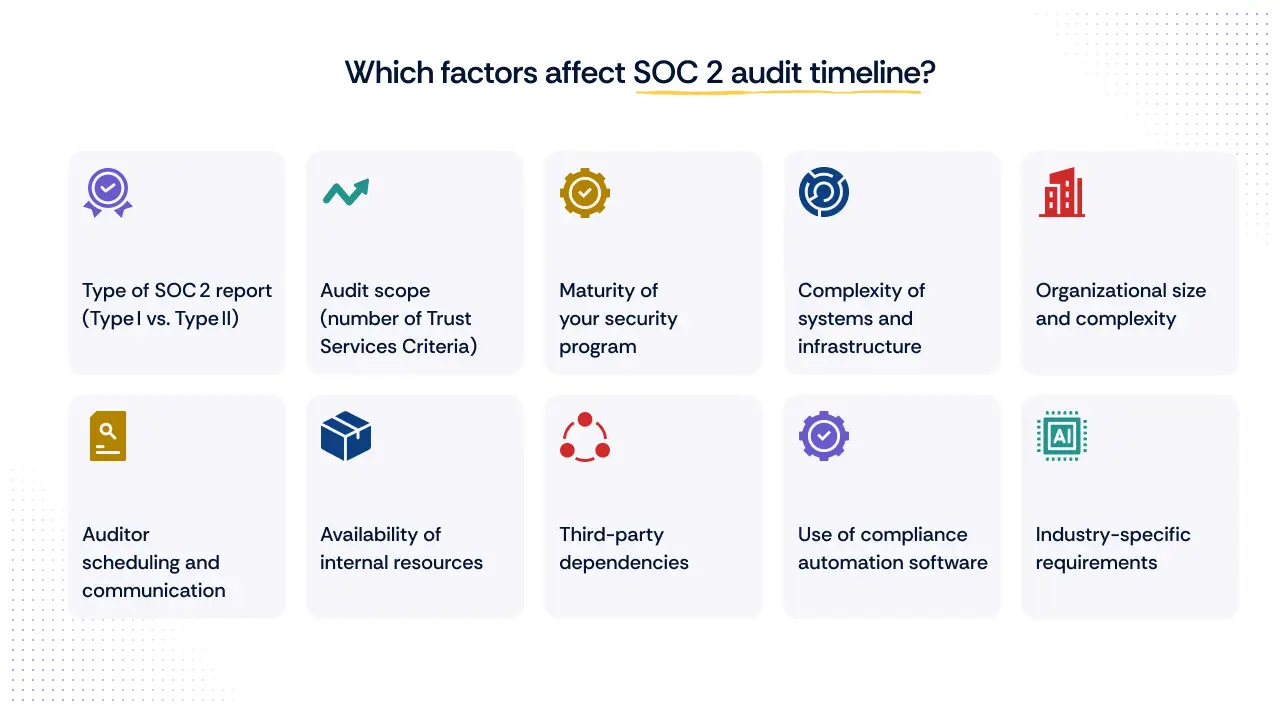
There’s no fixed timeline for achieving SOC 2 compliance. Some organizations breeze through it in a few months, while others take closer to a year, or more. The difference often lies in the details: the type of report you’re aiming for, how broad your audit scope is, and how mature your security practices are.
It’s also shaped by your organization’s size and complexity, how much internal bandwidth you can dedicate, and even external factors like auditor availability or vendor dependencies. On top of that, the tools you choose, manual processes versus automation, can either slow you down or help you move faster.
Here’s a closer look at the key factors that can influence your SOC 2 timeline:
1. Type of SOC 2 report (Type I vs. Type II)
The report type you choose has a direct impact on timelines. Type I audits are faster since they assess your controls at a single point in time, often taking a few months. Type II audits, however, require a 3–12 month observation period to evaluate whether your controls operate effectively over time, making the process longer.
2. Audit scope (number of Trust Services Criteria)
While the Security criterion is mandatory, expanding your audit to include other Trust Services Criteria like Availability, Confidentiality, Processing Integrity, or Privacy increases the breadth of the assessment. A broader scope means more systems, processes, and controls to prepare and test, which can extend the timeline.
3. Maturity of your security program
Organizations with mature security practices, where policies are documented, controls are implemented, and teams are trained, tend to move through the audit process more quickly. In contrast, companies starting from scratch may need additional time for gap assessments, remediation, and policy implementation before they’re audit-ready.
4. Complexity of systems and infrastructure
The complexity of your technical environment also plays a role. A small SaaS setup with a single cloud provider is easier to evaluate than a large enterprise managing multi-cloud environments, legacy systems, and numerous integrations. The more complex your systems, the longer it takes to prepare and gather evidence.
5. Organizational size and complexity
Larger organizations often face additional challenges due to multiple departments, locations, and distributed teams. Coordinating evidence collection and aligning all stakeholders can take more time than it would for a smaller, centralized team.
6. Auditor scheduling and communication
External factors like auditor availability can influence how quickly you get through the process. During peak seasons, auditor schedules fill up quickly, potentially delaying your start date. Clear and proactive communication with your auditor is also key to avoiding unnecessary bottlenecks.
7. Availability of internal resources
Limited team bandwidth can be a major roadblock. When internal teams are juggling compliance with day-to-day responsibilities, it can slow down evidence collection and remediation efforts. Having dedicated compliance resources often helps accelerate progress.
8. Third-party dependencies
If your systems rely on third-party vendors or service providers, their readiness and responsiveness can impact your timeline. Waiting on them for evidence or updates can introduce delays beyond your direct control.
9. Use of compliance automation software
Manual processes often lead to bottlenecks and inefficiencies. Leveraging compliance automation platforms streamlines evidence collection, maintains continuous monitoring, and helps your team stay audit-ready, significantly shortening the time needed to prepare for and complete your audit.
10. Industry-specific requirements
Certain industries, such as healthcare or financial services, may face additional scrutiny or regulatory expectations that extend preparation and testing timelines. Industry-specific controls can also add to the scope of work for your teams and auditors.
SOC 2 compliance challenges and how to overcome them

Achieving SOC 2 compliance often feels like navigating a maze, with twists that catch even the best-prepared teams. According to the SANS 2024 SOC Survey, 71% of security operations professionals identified a lack of automation and orchestration as the biggest obstacle in their workflows. When your audit prep still depends on manual evidence collection and spreadsheets, delays and errors are almost inevitable. So, how do you clear those roadblocks?
1. Manual evidence collection
Relying on manual processes slows down audits and invites inconsistencies. The good news: platforms like Scrut automate evidence gathering, pulling in audit-ready data from your tech stack and ensuring your logs, configurations, and documentation are always up to date, often cutting prep time dramatically.
2. Overstretched internal teams
When audit prep becomes an afterthought, progress stalls.
3. Complex audit scope
Audits covering multiple Trust Services Criteria (beyond Security) increase the breadth of evidence required. Scrut simplifies this by dynamically mapping evidence to each relevant control across all selected TSCs, reducing manual overhead as your scope grows.
4. Coordination with auditors
Manual hand-offs and miscommunication can lead to frustrating delays. With Scrut, auditors get access to a live dashboard where they can view evidence, leave comments, and resolve queries in real time, streamlining fieldwork and cutting down back-and-forth.
5. Third-party vendor delays
Waiting on vendors for reports or certifications can bring your audit timeline to a halt. Scrut automates third-party evidence collection where possible and notifies teams about pending manual inputs, keeping the process moving smoothly.
6. Budget constraints
Building a compliance program manually is expensive, both in time and resources. Scrut’s automation helped e6data reduce audit prep effort across six frameworks, saving costs and effort by consolidating risk assessments, vendor reviews, and policy attestations in one place.
7. Maintaining year-round compliance
SOC 2 Type II requires uninterrupted control operation. Scrut’s continuous monitoring and real-time alerts keep you informed about compliance issues the moment they arise, so you’re always audit-ready, not scrambling at the last minute.
8. Industry or regulatory overlays
For fintech, healthcare, or other highly regulated sectors, additional frameworks like ISO 27001 or HIPAA often overlap with SOC 2 requirements. Scrut simplifies cross-framework audits by reusing evidence and control mappings, accelerating multi-framework compliance.
For example, Insightly Analytics, operating in the highly regulated financial services sector, used Scrut to manage SOC 2 and ISO 27001 simultaneously. By leveraging Scrut’s cross-framework capabilities, they avoided duplicating efforts across overlapping controls and completed both audits in record time, reducing compliance fatigue for their lean team.
9. Complexity in large environments
Big, distributed infrastructures increase audit workload exponentially. Scrut scales effortlessly, aggregating evidence across thousands of cloud resources and user accounts in minutes, not weeks.
10. Knowledge gaps
Many teams simply don’t know where to start. Scrut’s readiness assessment guides organizations through scoping, gap analysis, and remediation tracking, reducing dependency on deep in-house compliance expertise.
How Scrut makes SOC 2 audits faster and simpler
Scrut cuts months off your SOC 2 journey by automating the heavy lifting. It connects with your systems to pull evidence in real time, maps it to SOC 2 controls, and keeps everything audit-ready.
With live dashboards for auditors, you avoid endless back-and-forth emails and speed up fieldwork. Continuous monitoring means no last-minute scrambles, renewals become a routine, not a restart.
The result? Scrut customers have cut SOC 2 readiness timelines significantly, with some completing renewals in under two months.

FAQs
How can you avoid SOC 2 audit delays?
Avoid delays by starting with a readiness assessment, automating evidence collection, aligning teams and vendors, and maintaining continuous monitoring to stay audit-ready year-round.
How much does an SOC 2 audit cost?
SOC 2 audit expenses vary depending on your report type, organizational complexity, and scope:
- SOC 2 Type I: Typically costs $15,000–$40,000, covering auditor fees, readiness assessments, and related tools.
- SOC 2 Type II: More comprehensive and costlier, ranging from $30,000 to $80,000, influenced by factors like observation period length, audit breadth, and organizational size.
Globally, costs may differ; smaller organizations in regions like India could see lower ranges, while enterprises or those engaging top-tier audit firms may face significantly higher fees
Can the SOC 2 reporting window be changed?
Yes, the SOC 2 reporting window can be adjusted, but only with your auditor’s approval. It’s often done when transitioning between audits or modifying the observation period for a Type II report. However, you must ensure there are no gaps between reporting periods to maintain continuous compliance and avoid affecting customer trust.
What happens if I miss the last SOC 2 audit window?
If you miss your SOC 2 audit window, there will be a gap in your compliance coverage, which could raise concerns for customers and partners relying on your report. To address this, you can issue a bridge letter, a formal statement explaining that your controls remain in place and effective until the next audit is completed. However, a bridge letter is only a temporary solution and doesn’t replace a valid SOC 2 report.
How many auditors are required to complete the SOC 2 audit?
Typically, a SOC 2 audit is conducted by a single CPA firm with one or more auditors assigned to your engagement. The exact number of auditors depends on your organization’s size, complexity, and the scope of the audit, but most small to mid-sized companies work with a dedicated audit team of 2–4 professionals from the firm.
What is the best time to start the SOC 2 audit?
The best time to start a SOC 2 audit is after completing a readiness assessment to identify and fix any gaps in your controls. For Type II audits, align your start date with the desired observation period. Many organizations begin at the start of their fiscal year to simplify reporting. Starting early also gives you time to engage auditors, especially since their schedules fill quickly during peak seasons.
Table of contents



















