Choose risk-first compliance that’s always on, built for you.
Go back to blogs
SOC 2 Common Criteria: Essential Guide & Overview
Last updated on
June 5, 2025
min. read

In today's digital age, safeguarding sensitive data isn't just an IT concern it's a business imperative. For CEOs, business leaders and security experts, maintaining customer trust and meeting compliance requirements are crucial too .
One key element in achieving this is understanding and implementing the Common Criteria in SOC 2. But what exactly are these criteria, and why should they matter to you and your business?
What is SOC 2 Common Criteria List?
The SOC 2 Common Criteria, also referred to as the CC-series, form the backbone of the Security Trust Services Criteria. These nine criteria focus on evaluating whether an organization has the right governance, risk management, access controls, and operational safeguards to protect systems and data from unauthorized access and threats.
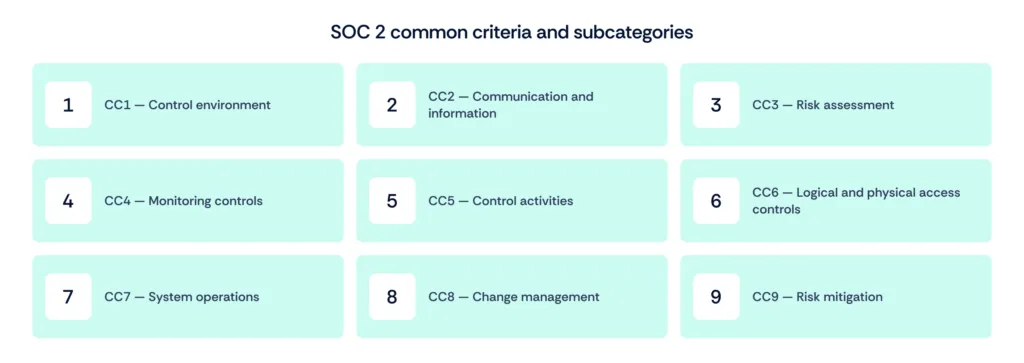
Here’s a deeper look at each criterion:
CC1 – Control environment
This criterion evaluates how seriously the organization treats security at the leadership and governance level. It includes oversight by the board of directors or senior leadership, clear assignment of roles and responsibilities, and accountability structures.
Key aspects:
- Tone at the top: Leaders prioritize integrity and ethical values.
- Clear reporting lines and responsibility assignments.
- Policies and procedures exist and are enforced.
- Employee onboarding and offboarding processes include security roles.
CC2 – Communication and information
This evaluates how effectively the organization communicates its policies, expectations, and responsibilities related to information security. It also covers how relevant information is identified, captured, and shared internally and externally.
Key aspects:
- Security policies and procedures are communicated across departments.
- Incident response plans are shared and understood.
- Reporting mechanisms exist for employees and third parties.
- Communication flows upward, downward, and across departments.
CC3 – Risk assessment
Organizations must regularly identify, assess, and manage risks that could impact the achievement of objectives. This includes understanding internal and external threats and analyzing how changes—technological, operational, or regulatory—could introduce new risks.
Key aspects:
- Periodic and event-driven risk assessments.
- Identification of relevant threats and vulnerabilities.
- Assessment of impact and likelihood of identified risks.
- Documentation of risk treatment plans.
CC4 – Monitoring controls
This criterion assesses how the organization monitors the effectiveness of its controls and addresses deficiencies. It includes both ongoing monitoring (e.g., automated alerts, dashboards) and periodic evaluations (e.g., audits, assessments).
Key aspects:
- Use of automated tools to track compliance and control performance.
- Internal audits or independent reviews.
- Corrective actions for identified control failures.
- Escalation procedures for critical issues.
CC5 – Control activities
Control activities are the specific actions and mechanisms implemented to mitigate risks. This includes both automated and manual processes that ensure policies are enforced, such as approval workflows, segregation of duties, and audit trails.
Key aspects:
- Documented and tested security controls.
- Preventive and detective controls (e.g., firewall rules, data validation).
- Defined escalation paths for exceptions or violations.
- Integration of control activities into business operations.
CC6 – Logical and physical access controls
This criterion focuses on how organizations manage access to systems, data, and infrastructure. It covers both logical (passwords, roles, encryption) and physical (badges, locks, CCTV) access.
Key aspects:
- User access provisioning and deprovisioning processes.
- Role-based access controls (RBAC) and least privilege principles.
- Multi-factor authentication (MFA) and encryption in transit and at rest.
- Physical access logs and facility security measures.
CC7 – System operations
This ensures that systems operate as intended and that any deviations, incidents, or failures are detected, reported, and resolved quickly. It includes system monitoring, vulnerability management, and response planning.
Key aspects:
- Monitoring of system health, logs, and performance.
- Defined procedures for incident detection and resolution.
- Disaster recovery and failover mechanisms.
- Patch and vulnerability management programs.
CC8 – Change management
This criterion evaluates how organizations manage changes to systems, infrastructure, and applications in a secure and controlled manner. The goal is to avoid introducing vulnerabilities through untested or unauthorized changes.
Key aspects:
- Formal change request and approval process.
- Impact analysis, testing, and rollback planning.
- Segregation of duties between development and deployment teams.
- Emergency change procedures.
CC9 – Risk mitigation
Organizations must implement controls and practices to mitigate identified risks. This includes vendor risk management, business continuity planning, and ongoing review of security programs.
Key aspects:
- Risk treatment plans with assigned ownership and deadlines.
- Vendor assessments and contracts with security clauses.
- Backup, recovery, and continuity planning.
- Continuous improvement of security controls based on evolving risks
SOC 2 common criteria mapping
Many organizations pursue compliance with multiple security standards. The AICPA provides mapping for the Common Criteria against other frameworks, including ISO 27001 and GDPR.
Mapping SOC 2 common criteria to ISO 27001
ISO 27001 outlines requirements for establishing, implementing, maintaining, and improving an information security management system (ISMS). The majority of its controls map directly to SOC 2's Trust Services Criteria.
Mapping SOC 2 common criteria to GDPR
The GDPR focuses on protecting EU citizens' personal data rights. Many of its requirements overlap with SOC 2's criteria, especially in the areas of privacy and data protection.
Scrut simplifies compliance by mapping multiple artifacts to common frameworks, streamlining workflows for organizations pursuing multiple certifications. Additionally, Scrut integrates with various tools to automate data collection and monitoring, further easing the compliance process.
Also read: 8 key differences between SOC 2 and ISO 27001
Benefits of SOC 2 common criteria mapping
Mapping SOC 2 common criteria to other standards, such as ISO 27001 and GDPR, provides several important benefits:
1. Streamlined implementation:
By aligning SOC 2 criteria with ISO 27001 and GDPR, organizations can leverage existing security controls and processes, potentially speeding up the implementation of these standards. This mapping reduces redundant efforts and enables a more efficient path to compliance.
2. Enhanced efficiency:
Common criteria mapping helps organizations avoid duplicative work by integrating multiple compliance frameworks. This can lead to more efficient resource utilization, as organizations can address overlapping requirements through a unified approach.
3. Cost savings:
Aligning SOC 2 with other standards can lead to significant cost savings. By streamlining processes and reducing the need for separate compliance initiatives, organizations can lower both direct compliance costs and indirect expenses associated with maintaining multiple systems.
4. Reputation boost:
Achieving compliance with multiple recognized standards through common criteria mapping can enhance an organization's reputation. It demonstrates a robust commitment to security and data protection, which can build trust with clients and partners.
5. Regulatory alignment:
Mapping SOC 2 criteria to GDPR ensures that privacy and data protection requirements are met, facilitating smoother interactions with regulatory bodies and helping avoid potential legal issues. This alignment also simplifies audits and reporting by providing a clear framework for meeting various regulatory demands.
Also read: SOC 2 audit keys to success
Why do SOC 2 common criteria matter to your business?
The Common Criteria aren't just about security; they also encourage businesses to adopt processes that enhance overall operational efficiency. By implementing these controls, your company can streamline processes, reduce redundancies, and improve the overall reliability of your systems.
From a CEO's perspective, this means better resource allocation, improved productivity, and a more agile organization that can quickly adapt to changing market conditions.
CC1: Security policy
Establishing a robust security policy ensures your organization has a clear, documented framework for protecting data and managing risks, enhancing overall security posture.
CC2: Organization of security
Proper organization of security responsibilities and resources streamlines your security management, ensuring that critical security functions are effectively assigned and managed.
CC3: Asset management
Effective asset management ensures that all information assets are identified, classified, and protected, reducing the risk of data breaches and loss.
CC4: Human resources security
Securing human resources through thorough background checks and training minimizes the risk of insider threats and ensures employees understand their security responsibilities.
CC5: Physical and environmental security
Implementing physical and environmental security controls protects your organization's infrastructure from physical threats and ensures the safety of data and hardware.
CC6: Communications and operations management
Managing communications and operations effectively helps in maintaining the integrity and availability of systems, preventing operational disruptions and data mishandling.
CC7: Access control
Enforcing strong access controls ensures that only authorized individuals can access sensitive data, reducing the risk of unauthorized access and data breaches.
CC8: Information systems acquisition, development, and maintenance
Integrating security into the acquisition, development, and maintenance processes ensures that systems are designed and maintained with security in mind, protecting against vulnerabilities.
CC9: Business continuity management
Having a solid business continuity plan ensures your organization can quickly recover from disruptions, maintaining operations and protecting data integrity in times of crisis.
Also read: SOC 2 Trust Services Criteria
Business use cases for common criteria
How Scrut can help automate SOC 2 compliance process?
Understanding and implementing the Common Criteria in SOC 2 is not just a technical requirement it's a business strategy that can protect your company from risks, enhance operational efficiency, and build customer trust. As a CEO, ensuring that your business meets these criteria is crucial for long-term success.
Navigating the complexities of SOC 2 compliance, including the implementation of the Common Criteria, can be challenging. This is where Scrut's platform comes in.
Learn how ActHQ landed deals with enterprise clients much quicker with Scrut. Find out how they saved 96 hours across compliances, increased customer retention, accelerated sales cycles, and enhanced employee security and compliance. Read the complete case study
Our platform provides automated monitoring, policy management, and evidence collection, ensuring that your business stays on top of its compliance obligations. With Scrut, you can easily track your progress, identify gaps, and ensure that your organization is always ready for audits.
Don't leave your compliance to chance. Contact Scrut today to learn how our platform can help you achieve and maintain SOC 2 compliance effortlessly. Let us help you safeguard your business and build a strong, secure foundation for future growth.
Frequently Asked Questions
1. What are the SOC 2 common criteria?
The SOC 2 Common Criteria are a set of nine subcategories within the Security Trust Services Criteria (TSC) that evaluate an organization's internal controls, including control environment, risk assessment, monitoring, and access controls.
2. Why is the security trust services criteria required for every SOC 2 audit?
The Security Trust Services Criteria is mandatory for every SOC 2 audit because it ensures that an organization's systems are protected against unauthorized access, vulnerabilities, and security risks.
3. How do the SOC 2 common criteria relate to other compliance frameworks like ISO 27001 or GDPR?
The SOC 2 Common Criteria can be mapped to other frameworks like ISO 27001 and GDPR, helping organizations streamline compliance efforts by aligning controls across multiple standards.
4. What are the business benefits of adhering to the SOC 2 common criteria?
Adhering to the SOC 2 Common Criteria helps businesses strengthen their security posture, enhance customer trust, ensure compliance with industry standards, and reduce the risk of data breaches and other security incidents.
5. How can organizations prepare for a SOC 2 audit using the common criteria?
Organizations can prepare for a SOC 2 audit by reviewing and strengthening their internal controls, ensuring proper communication of security policies, regularly assessing risks, and monitoring the effectiveness of their controls as outlined in the SOC 2 Common Criteria.
Table of contents



















