Wiz is one of the most widely adopted cloud-native application protection platforms (CNAPPs) on the market, but it is not the only option. Depending on your cloud environment, compliance requirements, or budget, it may not be the best fit.
Organizations commonly seek Wiz alternatives because of gaps in on-premises support, limitations in runtime protection, or the need for tighter compliance automation tied to GRC workflows.
This guide compares eight Wiz competitors across cloud security posture management (CSPM), compliance capabilities, deployment models, and overall fit. We also include dedicated comparison sections for the most commonly searched matchups: Wiz vs CrowdStrike, Wiz vs Orca, Wiz vs Lacework, and Wiz vs Prisma Cloud.
How we evaluated these Wiz competitors
To ensure this comparison is useful regardless of which direction you lean, we assessed each platform across five dimensions:
- Cloud coverage and deployment model: Which cloud providers are supported (AWS, Azure, GCP, others)? Is the tool agentless, agent-based, or hybrid?
- CSPM and CNAPP capabilities: Does it cover misconfiguration detection, vulnerability management, identity and entitlement management, and workload protection?
- Compliance framework support: Can it map findings to frameworks like CIS Benchmarks, SOC 2, ISO 27001, HIPAA, PCI DSS, and GDPR?
- Ease of deployment and operational overhead: How quickly can teams deploy, and what ongoing maintenance is required?
- Verified customer ratings: We referenced G2, Gartner Peer Insights, and PeerSpot scores as of early 2026.
We drew on direct experience from Scrut customers who use our cloud security module alongside compliance automation, as well as publicly available review data.

What is Wiz? A quick review
Wiz is a CNAPP built for cloud-native environments. It connects to cloud environments via APIs (supporting AWS, Azure, GCP, VMware vSphere, OCI, Alibaba Cloud, Red Hat OpenShift, and Kubernetes) and provides agentless scanning across virtual machines, containers, serverless functions, and data stores.
According to Gartner Peer Insights, Wiz holds a 4.7/5 rating with 300+ reviews and is ranked among the top CSPM tools for multi-cloud visibility.
Key features of Wiz
Wiz offers a broad set of cloud security capabilities under one platform:
- Continuously prioritizes critical risks based on analysis of misconfigurations, secrets, vulnerabilities, malware, sensitive data, and identities.
- The Wiz Security Graph provides contextual insights into toxic risk combinations and attack paths.
- Graph-based network and identity engine prioritizes misconfigurations by focusing on verified exposed resources.
- Evaluates over 1,400 configuration rules across runtime and infrastructure as code (IaC).
- Covers CSPM, CIEM, CWPP, DSPM, and AI-SPM.
Drawbacks of Wiz
Based on verified reviews on G2 and PeerSpot, these are the most commonly cited limitations:
- The re-assessment functionality is limited to a few daily runs and does not always work reliably.
- No support for custom report templates.
- Container discovery statuses do not automatically resolve.
- Kubernetes integration is difficult to implement within CI/CD pipelines.
- Lack of support for on-premises platforms and services, a significant gap for hybrid environments.
- Alert fatigue: even with prioritization, teams can get overwhelmed by findings, some of which are false positives.
8 Best alternatives to Wiz
Below is a breakdown of eight cloud security platforms worth evaluating, starting with tools that address Wiz's most common gaps: compliance automation integration, on-prem support, and runtime protection.
1. Scrut Automation
Scrut Cloud Security goes beyond traditional CSPM by combining cloud misconfiguration scanning with a full GRC platform that automates compliance across frameworks like SOC 2, ISO 27001, HIPAA, GDPR, and PCI DSS. This makes Scrut particularly strong for organizations that need cloud security tied directly to compliance evidence and audit readiness, something standalone CSPM tools like Wiz do not provide.
The platform scans and monitors misconfigurations across AWS, Azure, and GCP, comparing configurations against 200+ cloud controls across CIS benchmarks. It provides status information for all cloud resources with four severity levels: Danger, Warning, Low, and Ignored (compliant).
Why teams choose Scrut over standalone CSPM: One enterprise SaaS client was using Wiz for cloud security but running a separate GRC tool for SOC 2 compliance. The result was duplicate effort, where cloud findings had to be manually mapped to compliance controls. After consolidating onto Scrut, cloud security findings mapped automatically to the relevant SOC 2 and ISO 27001 controls, and evidence collection from their AWS and GCP environments was fully automated.
Key features:
- Actionable remediation: Sends alerts with specific recommendations for correcting misconfigurations, and lets you assign tasks directly to team members.
- Multi-cloud and multi-account support: Connect your entire cloud infrastructure (AWS, Azure, GCP, Oracle Cloud, IBM Cloud) to Scrut in under 10 minutes.
- Full-stack cloud security: Covers virtual machines, containers, and serverless across hybrid and multi-cloud infrastructure. Learn more in our cloud security strategy guide.
- Compliance-integrated CSPM: Cloud security findings feed directly into the compliance workflow, closing compliance gaps in real time.
- Centralized repository: All information security tasks and artifacts are in one place, eliminating the need to manage multiple tools.
Thanks to these features, Scrut is one of the top-rated CSPM solutions, earning a 4.9/5 customer rating on G2 for its ability to simplify cloud security, strengthen compliance, and help teams remediate risks faster.

2. JupiterOne
JupiterOne unifies and standardizes asset data across complex multi-cloud environments, collecting identity, code, security, endpoint, infrastructure, and ephemeral asset data and mapping their relationships. According to the NIST Cybersecurity Framework, asset management and visibility are foundational to effective security programs.
Key features:
- Easily incorporates evidence for SOC, HIPAA, GDPR, and other compliance assessments.
- Provides inventory assets and configurations using GraphQL, enabling flexible querying.
- Strong at connecting the dots between assets, users, endpoints, and code repositories.
Customer Rating: G2 - 4.9/5
3. Lacework
Lacework uses a single platform across AWS, Azure, Google Cloud, and Kubernetes to provide consolidated compliance visibility. Its Polygraph Data Platform leverages machine learning to baseline cloud behavior and detect anomalies without requiring manual rule configuration.
Key features:
- Alerts security teams in real time using machine learning through behavioral anomaly detection.
- Multiple security capabilities on a single platform: threat detection, vulnerability management, compliance monitoring, and incident response.
- Automated multi-cloud security covers configurations, logs, and workload data with relationship mapping.
Customer Rating: G2 - 4.5/5
4. Aqua Security
Aqua CSPM detects and resolves configuration issues across AWS, Azure, Google Cloud, and Oracle accounts using 100% agentless technology. According to OWASP's cloud security guidance, runtime protection for containerized workloads is a critical capability gap in many CSPM tools. Aqua addresses this with both agentless scanning and runtime controls.
Key features:
- Detailed results with the ability to filter by specific criteria.
- User-configurable dashboards for cloud security and image scanning.
- Strong container and Kubernetes security capabilities with shift-left scanning.
Customer Rating: G2 - 4.5/5
5. CloudGuard (Check Point)
CloudGuard enables seamless onboarding of new cloud accounts while managing compliance and security across AWS, Azure, Google Cloud, Alibaba Cloud, and Kubernetes. The platform manages compliance posture across 50+ frameworks and assesses over 2,400 security rulesets.
Key features:
- Comprehensive tracking of cloud activity across all devices and workloads.
- Good compliance mapping with pre-built policies for HIPAA, PCI DSS, SOC 2, and CIS benchmarks.
Customer Rating: G2 - 4.5/5
[IMAGE] Logo: Prisma Cloud logo, or screenshot of multi-cloud dashboard.
6. Prisma Cloud (Palo Alto Networks)

Prisma Cloud is a comprehensive CNAPP that covers CSPM, CIEM, CWPP, and more, offering visibility across public cloud infrastructure with continuous automated monitoring. The platform uses machine learning and threat intelligence for detection.
Key features:
- Strong CI/CD, IaC, container, and serverless integration capabilities.
- Comprehensive visibility across multi-cloud environments.
- Backed by Palo Alto Networks' broader security ecosystem and threat intelligence.
Customer Rating: G2 - 4.3/5
7. Orca Security
Orca is an agentless CNAPP that monitors cloud environments for misconfigurations, policy violations, compliance risks, and threats. Its SideScanning technology provides full-stack visibility without deploying agents.
Key features:
- Simple to manage with straightforward deployment.
- Comprehensive information on vulnerable cloud resources through agentless workload scanning.
- Combines workload protection, configuration security, identity management, data discovery, and detection in a single platform.
Customer Rating: G2 - 4.7/5
8. Datadog Cloud Security
Datadog CSPM checks the configuration of cloud accounts, hosts, and containers, with continuous scanning that tracks all resources. The platform leverages Datadog's broader observability platform for security posture context.
Key features:
- Gather and correlate security data with observability data from the same platform, a significant advantage for existing Datadog users.
- Customizable monitoring of deployed service health alongside security posture.
Customer Rating: G2 - 4.3/5
Wiz vs CrowdStrike: How do they compare?
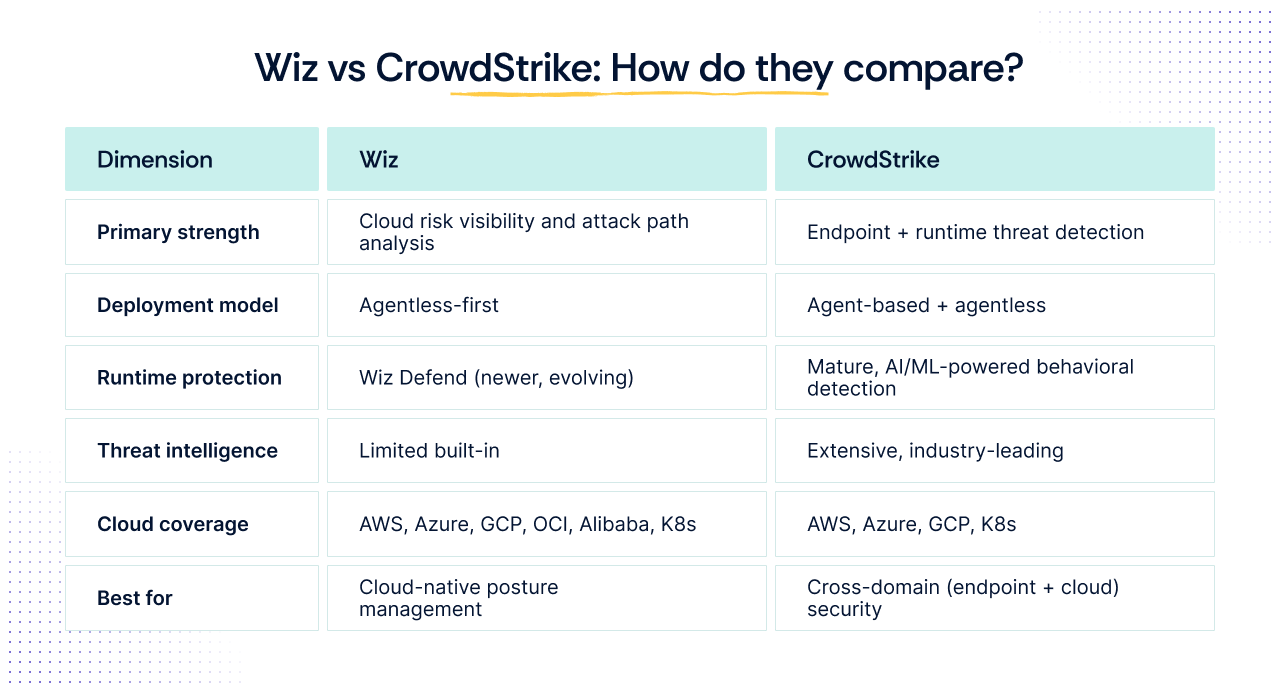
This is one of the most commonly searched cloud security comparisons, and the answer depends on where your security priorities lie.
Wiz was built from the ground up for cloud environments with an agentless-first model. Its core strength is the Security Graph, which correlates signals across misconfigurations, vulnerabilities, identities, and network exposure.
CrowdStrike Falcon Cloud Security evolved from CrowdStrike's deep endpoint security expertise. Its key advantage is runtime threat detection and response, where its agent delivers deep visibility into processes, files, and workload activity.
Bottom line: If your security challenges are primarily cloud posture and attack path visibility, Wiz has the edge. If you need unified endpoint and cloud security with mature threat intelligence, CrowdStrike is stronger. Many enterprise teams run both.
Wiz vs Orca Security: Which agentless CNAPP is better?
Both Wiz and Orca are agentless CNAPPs, making this a direct comparison for teams that want cloud security without deploying agents. Wiz uses API-based scanning and its Security Graph; Orca uses its proprietary SideScanning technology.
| Dimension | Wiz | Orca |
|---|---|---|
| Scanning approach | API-based agentless | SideScanning technology |
| Risk prioritization | Security Graph with attack path analysis | Context-aware risk scoring |
| DSPM | Yes | Yes |
| Container security | Yes | Yes |
| G2 rating | 4.7/5 | 4.7/5 |
Bottom line: Both are strong agentless options. Wiz has broader market adoption and a more mature security graph. Orca offers competitive full-stack coverage in a simpler package.
Wiz vs Lacework: Behavioral detection vs risk graph
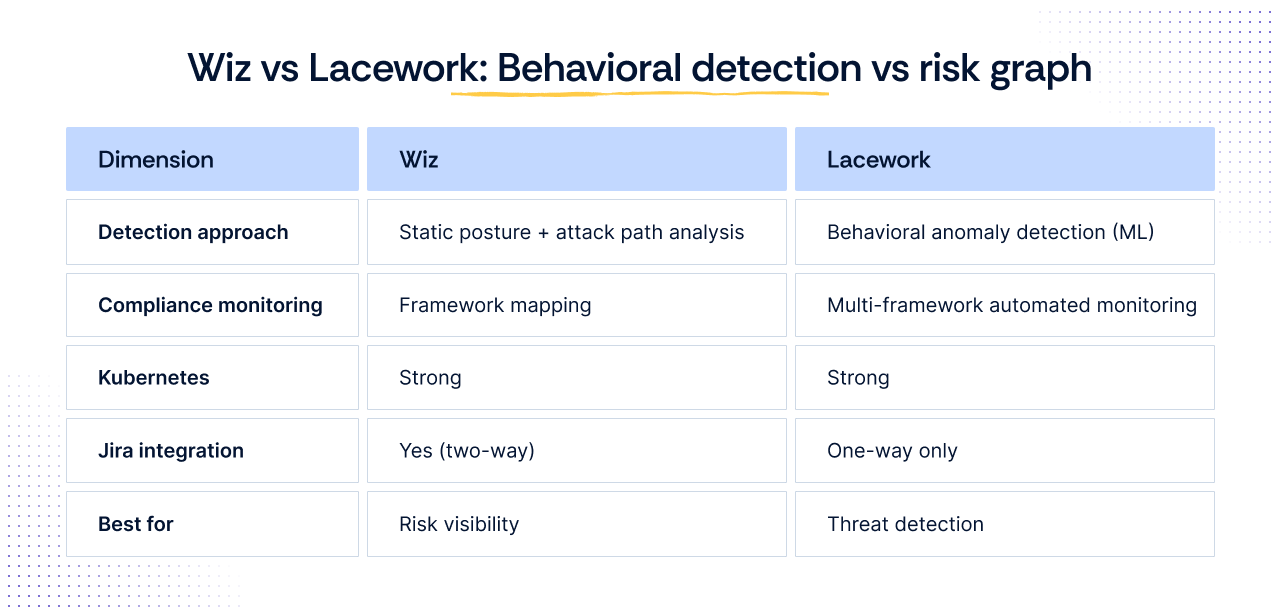
Wiz and Lacework take fundamentally different approaches to cloud threat detection. Wiz focuses on posture management and attack path analysis. Lacework emphasizes behavioral anomaly detection through its Polygraph Data Platform, using machine learning to baseline normal cloud activity and flag deviations.
Bottom line: Wiz is stronger for risk posture and remediation. Lacework is stronger at detecting active threats. Some organizations run both.
Wiz vs Prisma Cloud: CNAPP feature depth
Prisma Cloud (Palo Alto Networks) and Wiz both offer comprehensive CNAPP coverage, but they come from different starting points. Wiz was purpose-built for cloud security with an agentless architecture. Prisma Cloud grew from Palo Alto's acquisition strategy, combining RedLock, Twistlock, PureSec, and Bridgecrew into one platform.
| Dimension | Wiz | Prisma Cloud |
|---|---|---|
| Architecture | Purpose-built, agentless-first | Integrated from multiple acquisitions |
| Coverage | CSPM, CIEM, CWPP, DSPM, AI-SPM | CSPM, CWPP, code security, IaC, containers |
| Code security | Wiz Code (newer) | Bridgecrew (mature) |
| UI complexity | Streamlined | More complex |
| G2 rating | 4.7/5 | 4.3/5 |
Bottom line: Wiz is more unified and intuitive. Prisma Cloud has deeper shift-left capabilities. Choose Prisma if you need deep DevSecOps integration and are already in the Palo Alto ecosystem.
Wiz alternatives: Feature comparison matrix
This matrix summarizes how Scrut and the seven other Wiz alternatives stack up across the capabilities that matter most when evaluating cloud security platforms:
| Capability | Scrut | Wiz | CrowdStrike | Orca | Prisma Cloud | Lacework | Aqua |
|---|---|---|---|---|---|---|---|
| Agentless scanning | Yes | Yes | Partial | Yes | Partial | Partial | Yes |
| Runtime protection | N/A | Wiz Defend | Yes (mature) | Limited | Yes | Yes | Yes |
| CSPM | 200+ controls | 1,400+ rules | Yes | Yes | Yes | Yes | Yes |
| GRC/compliance | 60+ frameworks | Limited | No | No | Limited | Limited | Limited |
| Evidence collection | 100+ integrations | No | No | No | No | No | No |
| Auditor collaboration | Yes | No | No | No | No | No | No |
| Risk management | Full register | Risk prioritization | Limited | Limited | Limited | Limited | Limited |
| Vendor risk management | Yes | No | No | No | No | No | No |
How to choose the right Wiz alternative
The right cloud security tool depends on your specific gaps and priorities. Here are practical guidelines based on common buyer profiles:

- Cloud security integrated with compliance automation: If you need cloud findings that automatically map to SOC 2, ISO 27001, HIPAA, and other frameworks with automated evidence collection and auditor collaboration, Scrut is designed for this use case.
- Runtime threat detection as top priority: CrowdStrike Falcon Cloud Security has the most mature runtime capabilities for unified endpoint and cloud security.
- Direct Wiz replacement with agentless scanning: Orca Security is the closest architectural match.
- Behavioral anomaly detection: Lacework offers the strongest ML-driven approach.
- Deep DevSecOps and code security integration: Prisma Cloud offers the most comprehensive shift-left capabilities.
- Already in the Check Point or Palo Alto ecosystem: CloudGuard or Prisma Cloud will integrate most seamlessly.
The best Wiz alternative depends on what you are trying to solve. For cloud posture management combined with compliance automation, Scrut provides the most integrated approach. For pure cloud security with runtime threat detection, CrowdStrike and Prisma Cloud are leading options. For agentless-only deployments, Orca Security offers the most direct comparison.
CSPM (Cloud Security Posture Management) focuses specifically on detecting misconfigurations and compliance violations in cloud infrastructure. CNAPP (Cloud-Native Application Protection Platform) is a broader category that combines CSPM with workload protection (CWPP), identity and entitlement management (CIEM), data security (DSPM), and sometimes code security and runtime threat detection.
Yes. Many enterprise security teams use Wiz for posture management and attack path analysis while running CrowdStrike or another agent-based tool for runtime protection. The key consideration is ensuring the tools do not create duplicate alerts or operational overhead.
Wiz is primarily designed for cloud environments and has limited support for on-premises platforms. Organizations with significant hybrid infrastructure may need alternatives like CrowdStrike or Prisma Cloud that support hybrid deployment models.
Migration complexity depends on workload size, integrations, and how deeply Wiz is embedded in your security workflows. For organizations using Wiz primarily for compliance evidence, migrating to an integrated platform like Scrut can consolidate your tool stack and reduce operational overhead.

Over the past 14+ years, Ishani has worked across products, solutions, and services, helping teams turn complex technology into clear, compelling stories that actually land with customers. Her focus has always been on product messaging, thought leadership, and go-to-market strategies that drive real impact, not just awareness. Her background spans B2B SaaS across cybersecurity, governance, risk, compliance, and IT management, working with teams across industries and growth stages.

Shraddha Chaturvedi is a GRC and Data Privacy professional with over 8+ years of experience in information security consulting and auditing. At Scrut Automation, she leads Infosec Delivery, helping organizations navigate frameworks like ISO 27001, SOC 1, SOC 2, GDPR, HIPAA, and more. Shraddha has previously worked with firms such as EY and PwC, and also contributes as a guest faculty, mentoring students in cybersecurity and risk management.

























