If your company handles any type of customer data, obtaining a System and Organization Controls 2 (SOC 2) report will demonstrate that you value data security and protection. Companies with SOC 2 compliance are likely to close more deals.
But what is the best way to prepare for your SOC 2 audit? Is it a good idea to prepare internally for your SOC 2 audit? Or do you need an external consultant? This article will discuss the positives and negatives of SOC 2 audits in-house.
What is a SOC 2 audit?
A SOC 2 audit is a rigorous examination of a company’s systems and processes related to data security, privacy, availability, processing integrity, and confidentiality. This audit is based on the Trust Services Criteria (TSC) established by the American Institute of Certified Public Accountants (AICPA). SOC 2 compliance is crucial for organizations that handle sensitive customer data, as it demonstrates a commitment to protecting this information and meeting industry standards.
Also Read : Understanding SOC 2 reports: A comprehensive guide
Should your company get SOC 2 certification?
SOC 2 certification is more than just a checkbox—it’s a powerful statement of your company’s commitment to data security and privacy. For businesses looking to build trust with clients and stakeholders, SOC 2 compliance is increasingly becoming a necessity. This certification not only demonstrates that your organization adheres to stringent security standards but also reassures clients that their sensitive data is in safe hands.
Achieving SOC 2 compliance can open doors to new markets, especially in industries where data security is paramount, such as healthcare, finance, and technology. It can also increase customer confidence, giving you a competitive edge in a crowded marketplace. Companies that are SOC 2 certified often find it easier to establish partnerships, close deals, and retain customers.
However, it’s important to recognize that preparing for a SOC 2 audit is a complex and resource-intensive process. It requires a thorough review of your existing policies, the implementation of new controls, and meticulous documentation. Without the right tools and expertise, the process can be daunting, potentially diverting focus from your core business activities.
Pros of doing a SOC 2 audit in-house
SOC 2 reports generally have a one-year shelf life, after which they may become less valuable to potential customers. However, the frequency of SOC 2 certifications can vary depending on the size and complexity of a company’s internal controls. Some organizations may opt for more frequent assessments, such as every six months, to ensure their controls remain up-to-date and effective. While a SOC 2 Type 1 report assesses the effectiveness of controls at a specific point in time, a SOC 2 Type 2 report evaluates the effectiveness of those controls over a specific period, typically ranging from 6 to 12 months.
Also Read : How long does it take for SOC 2 compliance to be complete?
Conducting an internal audit at planned intervals, such as every 6-12 months, can help a company stay updated with the latest SOC 2 requirements and ensure that its controls are effective and current. Additionally, conducting an internal audit on a regular basis allows a company to identify any areas of weakness or non-compliance and address them on time, which can ultimately improve the chances of passing a SOC 2 review.
Here are some pros of doing a SOC 2 in-house audit.
1. Flexibility to operate as per your requirement
When preparing for a SOC 2 audit internally, all of your security rules, tests, and evidence tasks are created, which gives you complete control over your SOC 2 in-house project from start to finish. The organization has complete control and does not need to rely on a third-party provider.
Another benefit of an in-house audit is managing risks effectively and implementing internal controls. The strength of the internal audit function is critical for the successful implementation of internal controls and ultimately contributes to improved governance and achievement of organizational objectives.
2. Better collaboration and control
SOC 2 compliance can involve members from every department in an organization. Internal communication is always less difficult than external communication. You’ll be able to collaborate with everyone involved in your SOC 2 in-house project. With an in-house audit team, the organization should have access to the needed documents and information, which can help in quickly collecting evidence.
Cons of doing a SOC 2 audit in-house
Preparing for a SOC 2 audit is a resource-intensive endeavor that requires significant time, manpower, and expertise. For many organizations, especially those with limited compliance professionals, the process can quickly become overwhelming.
Here’s a look at some of the disadvantages of doing a SOC 2 audit in-house.
1. High cost
While it might seem like preparing in-house is a cost-effective option, the hidden costs can add up. The time spent by your team, the potential for errors, and the risk of a failed audit can lead to higher expenses in the long run. These hidden costs often outweigh the initial savings, making in-house preparation less cost-effective than it appears.
SOC 2 isn’t a one-size-fits-all solution. You’ll need someone with a well-developed knowledge of SOC 2 to assist you with your audit journey. Hiring people with the necessary skills, training, and experience can be time-consuming and costly. A full-time hire costs more than $100k.
According to Thomson Reuters’ 2023 Cost of Compliance Report, the cost of senior compliance staff is expected to rise, driven by increasing demand for subject matter expertise and specialized skills.
As threats evolve and become more complex, the technology required to defend against them must also evolve, which can be costly.
2. Time-consuming and involves a lot of hassle
Preparing for your in-house SOC 2 audit involves a lot of manual work. You must create and manage the project’s roadmap, assign task owners, and ensure task completion. Not just that, manual evidence collection also involves a lot of hassle. Every change to a policy or control needs to be built from scratch, which is time-consuming.
Finding and managing partners, such as VAPTs, CPAs, etc., takes a long time and could result in delays. Collecting and organizing evidence across multiple systems can quickly become a logistical nightmare. This manual approach not only slows down the process but also increases the risk of incomplete or inaccurate evidence submission.
3. High risk of errors
SOC 2 compliance is complex, with stringent requirements that must be met to pass an audit. Without the proper tools or expertise, there is a high risk of errors. These errors can lead to costly delays, failed audits, and potentially damaging compliance gaps. Relying solely on in-house resources increases the likelihood of missing crucial details, which could result in a negative audit outcome.
Human error is greatly increased when preparing for your SOC 2 audit in-house. You must ensure that no errors are made in all manual tasks. Your auditor will bill you for more hours for each error.
4. Lack of expertise
SOC 2 audits require specialized knowledge that many in-house teams may not possess. While your team may be familiar with general compliance practices, SOC 2’s specific requirements often necessitate a deeper understanding. Without access to SOC 2 compliance experts, your organization may struggle to navigate the complexities of the audit process, leading to inefficiencies and potential compliance issues.

5. Audit is very time-consuming
Collaboration with auditors over email is time-consuming. For your SOC 2, you must keep track of all policy and control changes. Sometimes, people make changes and then forget to record them. It’s difficult to go back and say who made the change, when it happened, and why.
Also Read: 7 ways to accelerate the SOC 2 audit process
Employee security training
When doing a SOC 2 project in-house, there will undoubtedly be bumps in the road. Your team must be trained on your SOC 2 goals and best practices for dealing with issues regularly. You should implement company-wide employee awareness training to reduce risk and strengthen internal security.
Requires a separate tool for cloud security monitoring
Another disadvantage of doing SOC 2 audit in-house is that you need a separate cloud security monitoring software. With the automation tool, users can keep track of cloud misconfigurations with centralized dashboards, including an automated classification for danger, warning, and secure configurations.
Stakeholder management
Task management is another problem when preparing the SOC 2 audit in-house. There is no centralized visibility into what is happening. When working on SOC 2 in-house, you will not have access to any automation. As a result, you’ll have to manually create and maintain all documentation, such as controls, policies, and evidence tasks. Without automation, it is not possible to hold team members accountable.
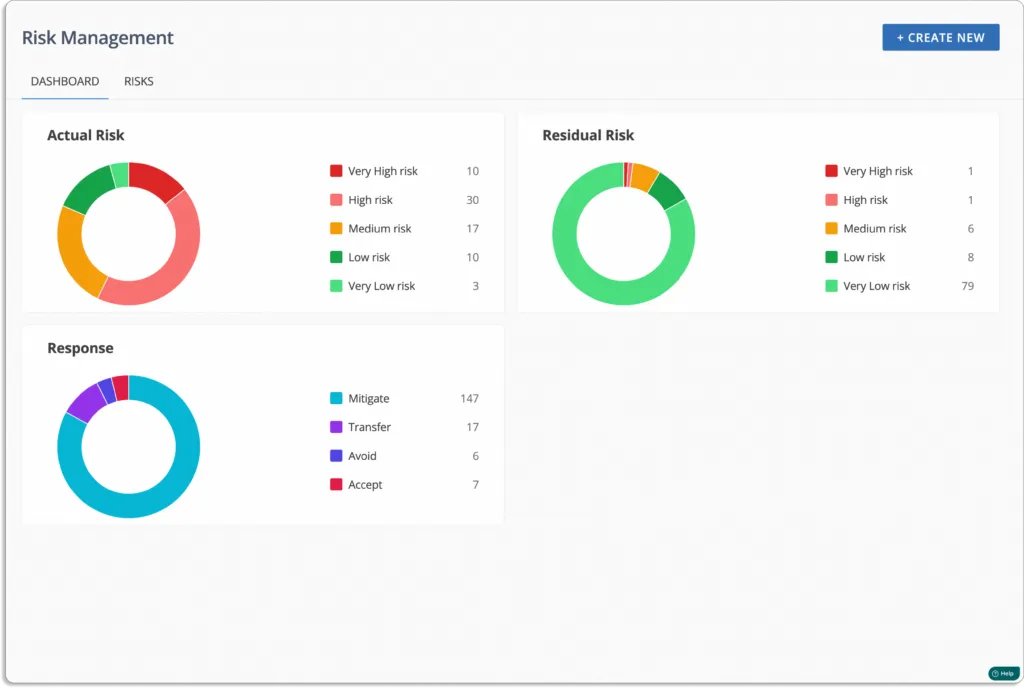
Risk Management
When working towards SOC 2 in-house, you will not have access to any automation. You’ll have to manage the risks from scratch manually. You will have to manually create and complete a risk management plan that includes all potential risks associated with your business and its remedies.
Vendor risk management
There is no automated vendor risk management during the in-house SOC 2 audit. You will have to manually send security questionnaires and analyze the answers. You will also have to perform all vendor risk assessments manually if you do not have automation software.
Read also: The ultimate guide for vendor risk management
Comes in the way of primary responsibilities
Conducting an in-house SOC 2 audit demands significant time and attention, pulling key team members away from their primary responsibilities. This diversion can lead to decreased productivity as employees juggle their regular duties with the demands of the audit.
The added workload often results in increased stress levels, which can further impact the overall efficiency and morale of your team. Instead of focusing on driving business growth and innovation, your staff may find themselves bogged down in compliance-related tasks, stretching resources thin and potentially affecting the quality of their core work.
Scrut makes SOC 2 compliance easier by automating much of the process with built-in features and integrations. Plus, with our expert team guiding you along the way, you can navigate SOC 2 with minimal hassle.
Orca reduced their audit time by 50% with Scrut. Learn more here.
How Scrut can help your SOC 2 audit?
Going through a SOC 2 audit in-house can be frustrating, time-consuming, and expensive. Your internal auditor cannot be everywhere at all times. That’s where Scrut automation software comes into the picture.
1. Simplify and automate the audit process
Scrut is designed to make the entire audit process smooth, easy, and error-free. By combining the most comprehensive automated compliance platform with a seamless audit experience, Scrut significantly reduces your SOC 2 compliance burden.
2. Key features of Scrut
Scrut manages a wide range of audit-related tasks, including:
- Cloud risk assessments
- Control reviews
- Risk management
- Employee policy attestations
- Vendor risk management
It automates tasks such as evidence collection, gap analysis, misconfiguration identification, and policy centralization, cutting manual work by 70%.
3. Access to compliance experts and auditors
Scrut provides access to its in-house compliance experts who guide you through the audit preparation process. In addition to internal experts, Scrut offers access to SOC 2 consultants, auditors, and other professionals. Collaborate with expert auditors from Scrut’s partner network at pre-negotiated rates, removing the need to search for external auditors.
4. Real-time risk and compliance monitoring
Scrut offers a unified, real-time view of risks and compliance. It continuously monitors automated controls to identify gaps and critical issues. Scrut’s Cloud Security feature gives you complete command of your cloud environment by connecting your cloud infrastructure (AWS, Azure, GCP, etc.) to the platform in minutes.

5. Pre-built policies for faster setup
Creating policies from scratch is time-consuming when you first begin your compliance journey. Scrut’s library of 50+ pre-built policies allows you to create a SOC 2-compliant infosec program in minutes, guiding you to collect what you need to pass the audit and get certified.

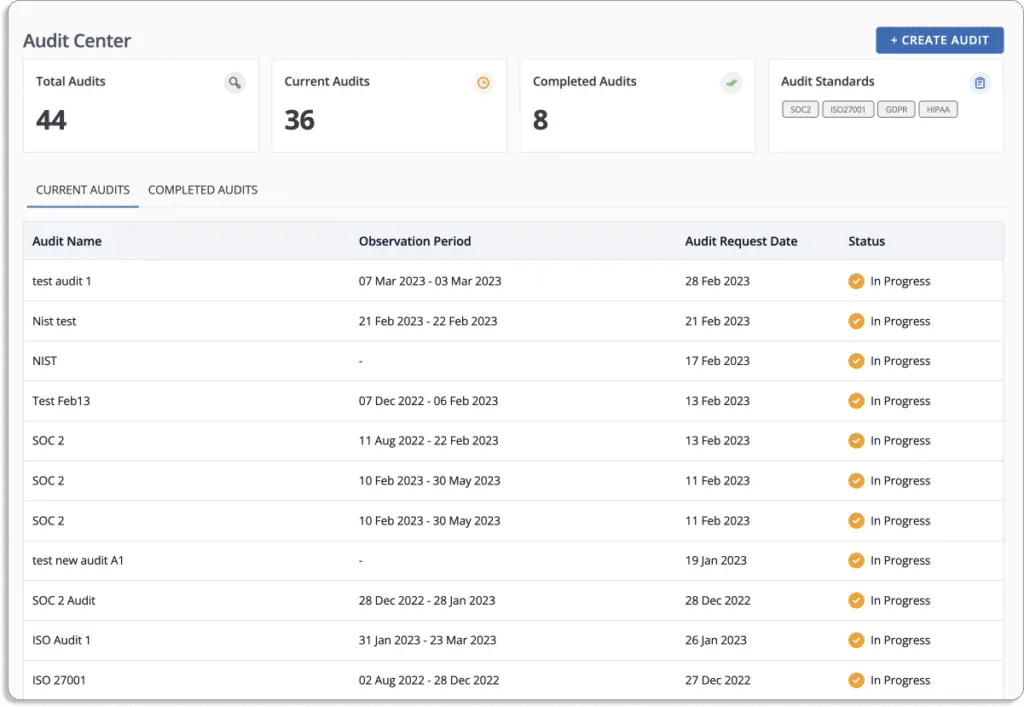
6. Comprehensive audit dashboard
Scrut’s Audit Center dashboard provides a complete overview of your audit. SOC 2 compliance involves an annual audit, and Scrut’s platform can scale to meet your company’s needs. When you click on each audit entry, you can view detailed information about the audit owner, data requested, task progress, and framework details, such as regulatory standards being tested.
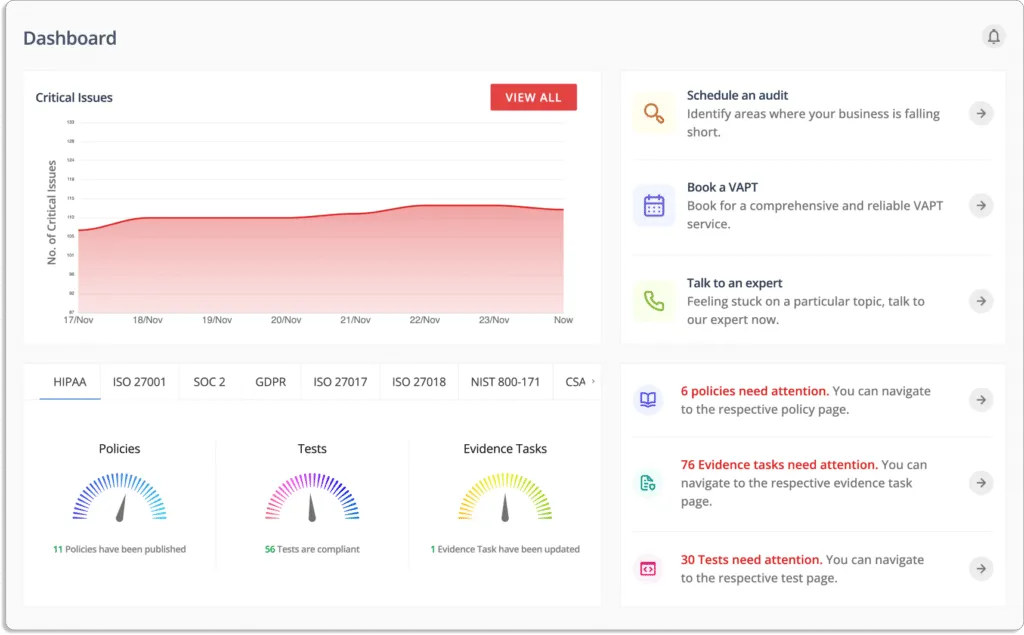
7. Detailed audit tracking
The dashboard also includes specific information about audit tasks and progress, allowing you to stay informed and ensure that auditors receive the necessary information on time. You can quickly identify any issues or nonconformities flagged during the audit process.
8. Streamlined risk management
Managing risks manually can be overwhelming. Scrut’s Risk Management feature streamlines the process by providing a centralized interface for identifying, assessing, and mitigating IT and cyber risks. This allows you to prevent threats and communicate the impact of risks on essential business operations.
9. Automated employee security training
Scrut automates employee information security training with a pre-built, 30-minute course designed by industry experts. This equips employees to recognize potential risks, avoid security lapses, and maintain a secure posture.

10. Vendor risk management
With Scrut, you can use pre-made templates or create custom security questionnaires to assess vendors. Scrut helps you compare vendors to find the least risky business partner.

Cogniquest cut down their manual workload by 70% during their SOC 2 audit with the help of Scrut.

It depends on your internal resources. If you have a skilled compliance team, preparing in-house can offer flexibility and control. However, if your team lacks expertise, hiring an external consultant may save time and reduce errors.
In-house audits provide flexibility, better collaboration, and complete control over the process. You can align the audit with your specific needs and have direct oversight of internal communications and documentation.
In-house audits can be costly, time-consuming, and prone to errors. Companies without specialized SOC 2 expertise may struggle to meet the requirements, increasing the risk of failed audits and compliance gaps.
An in-house audit requires significant time, manpower, and technical expertise. You’ll need skilled compliance professionals, IT resources, and tools to monitor and document security controls effectively.
Manual SOC 2 audits increase the likelihood of errors, delays, and missing crucial details. These risks can lead to higher costs, failed audits, and compliance issues

Susmita Joseph is a cybersecurity and compliance writer specializing in governance, risk, and regulatory content. She focuses on making complex subjects such as AI governance, cybersecurity compliance, and risk management accessible to growing and mature organizations. With a particular interest in the intersection of AI and GRC, her work explores how emerging technologies are reshaping compliance expectations and security operations.

Team Scrut is a collective of compliance, security, and risk practitioners sharing practical guidance on building audit-ready, scalable programs. We write about SOC 2, ISO 27001, continuous compliance, third-party risk, cloud security, and GRC automation, blending regulatory depth with operator experience to help fast-growing companies strengthen trust, streamline audits, and stay ahead of evolving security demands.