In the rapidly evolving landscape of business, where digital connections and partnerships are the bedrock of growth, the concept of vendor risk management has taken on unprecedented importance.
As organizations increasingly rely on third-party vendors to achieve their goals, they also expose themselves to potential risks that could jeopardize their security, reputation, and compliance standing. In this intricate dance between innovation and vulnerability, the need for a robust and efficient vendor risk management strategy has never been more critical.
Vendor risk management goes beyond mere due diligence; it involves a comprehensive assessment of the potential risks associated with your vendor relationships. From cybersecurity breaches to regulatory non-compliance, the spectrum of risks is vast and intricate.
However, manual processes for managing these risks are no longer sufficient to address the complexities and pace of modern business operations. This is where the power of automation steps in to revolutionize the way we safeguard our enterprises.
In this blog, we will learn all about the automation of vendor risk management, the challenges faced, the benefits of automation, and the steps to be taken for the automation of vendor risk management.
What is vendor risk management?
Vendor risk management (VRM) is a structured approach that organizations employ to assess, manage, and mitigate the risks that emerge from their interactions with vendors and other third-party entities. These risks encompass a wide spectrum, ranging from data breaches and cybersecurity vulnerabilities to regulatory non-compliance and financial instability. The primary goal of VRM is to identify potential risks, implement strategies to minimize their impact and maintain a robust line of defense against any adverse consequences that might arise from these risks.
What is the need for automation in vendor risk management?
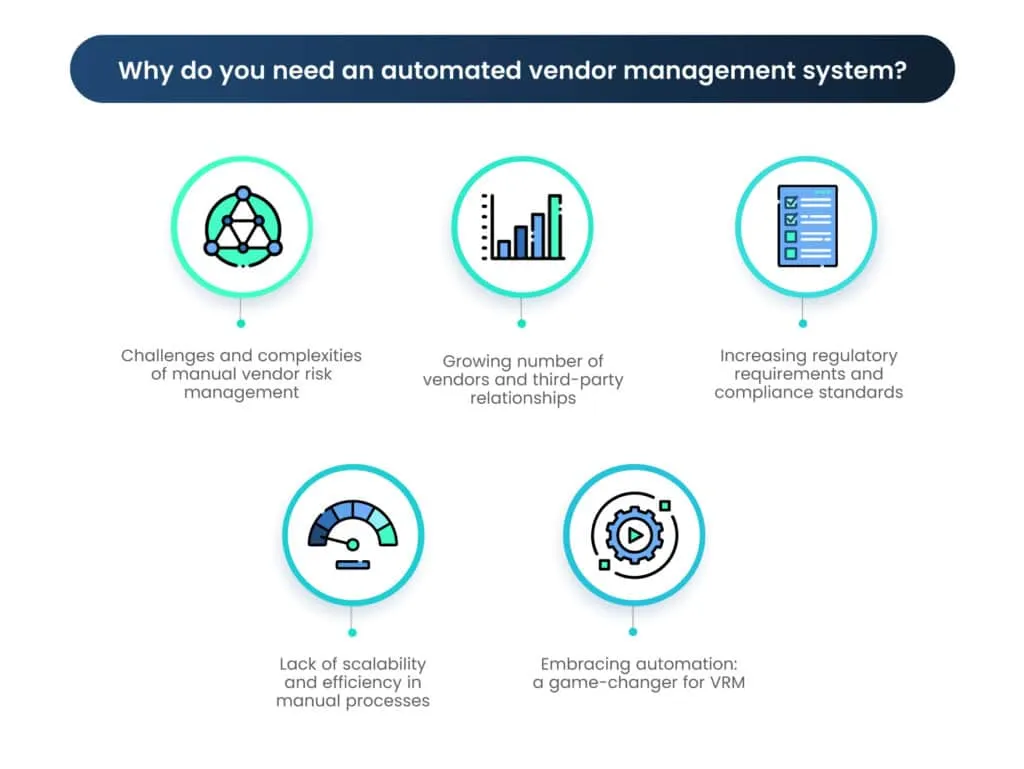
As organizations continue to forge partnerships with an increasing number of vendors and regulatory landscapes evolve, the necessity for automation in VRM has become undeniable. Let’s delve into the challenges that manual VRM encounters and explore how automation can revolutionize this critical domain.
A. Challenges and complexities of manual vendor risk management
Following are the challenges faced by organizations when they manually manage vendor risk.
1. Resource-intensive processes
Manual VRM often involves copious amounts of paperwork, manual data entry, and repetitive tasks. This not only consumes valuable human resources but also increases the likelihood of errors due to fatigue and oversight.
2. Inconsistent assessment criteria
Manual processes can result in inconsistencies in how vendor risks are assessed and categorized. Without standardized assessment criteria, decision-making becomes arbitrary and lacks reliability.
3. Limited scalability
As organizations expand and onboard more vendors, the manual approach struggles to scale efficiently. Managing an ever-growing vendor portfolio with manual methods becomes increasingly time-consuming and prone to errors.
4. Delayed risk identification
Manually monitoring vendors for risks on an ongoing basis is challenging. Risks may go unnoticed until they escalate, leading to reactionary measures rather than proactive risk management.
B. Growing number of vendors and third-party relationships
The modern business landscape is characterized by extensive networks of vendors, suppliers, contractors, and partners. As organizations seek to innovate and specialize, their reliance on external entities grows. This proliferation of third-party relationships exponentially increases the complexity of managing associated risks. Manual VRM struggles to keep up with the sheer volume of vendors, often resulting in gaps, oversights, and a lack of holistic risk visibility.
C. Increasing regulatory requirements and compliance standards
Regulatory bodies worldwide are continuously updating and strengthening their requirements for data privacy, cybersecurity, financial transparency, and more. Organizations are expected to ensure not only their own compliance but also the compliance of their vendors. Manual processes can lead to missed deadlines, incomplete documentation, and misinterpretations of regulatory changes. The result? An elevated risk of non-compliance, which could lead to severe penalties and reputational damage.
D. Lack of scalability and efficiency in manual processes
Manual VRM processes might work adequately for a limited number of vendors, but as the vendor ecosystem expands, inefficiencies become evident. Tracking vendor profiles, conducting third party risk assessments, updating documentation, and coordinating communications with vendors can become overwhelming. This lack of scalability often results in delayed assessments, increased vulnerability to risks, and a compromised ability to react promptly to emerging threats.
E. Embracing automation: a game-changer for VRM
Automation in VRM offers a dynamic solution to these challenges. By leveraging technology to streamline processes, automate data collection and analysis, and provide real-time monitoring, organizations can mitigate risks more effectively, ensure compliance, and enhance operational efficiency. The subsequent segments of this blog series will delve into the various components of an automated VRM system, the benefits it offers, and the practical steps to successfully implement automation. Stay tuned as we explore how automation can transform vendor risk management into a strategic advantage in the quest for security, compliance, and organizational resilience.
What are the benefits of automating vendor risk management?
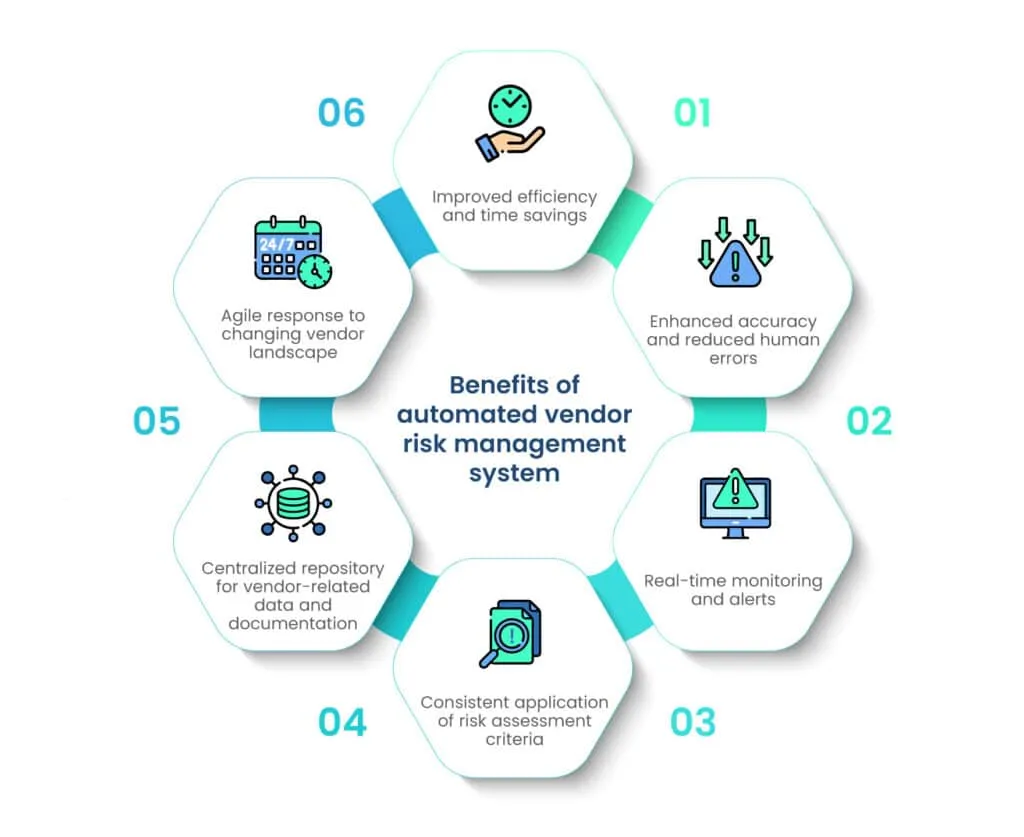
As organizations grapple with an expanding vendor network, evolving regulatory demands, and the need for real-time risk monitoring, automation offers a suite of benefits that can reshape the way we manage vendor risks. Let’s delve into the advantages of automating VRM and understand how it revolutionizes the landscape.
1. Improved efficiency and time savings
Automation transforms the labor-intensive, manual processes of VRM into swift, streamlined workflows. Tasks that once consumed significant time, such as data collection, verification, and third party risk assessments, can now be executed in a fraction of the time. The result? Faster response times, accelerated decision-making, and a liberated workforce that can focus on strategic activities rather than administrative tasks.
2. Enhanced accuracy and reduced human errors
Manual processes are susceptible to human errors, which can have far-reaching consequences in VRM. From misinterpreting data to overlooking critical risk indicators, these errors compromise the integrity of risk assessments. Automating vendor risk assessment eliminates these risks by executing tasks consistently and following predefined algorithms, ensuring accurate risk evaluations and more informed decisions.
3. Real-time monitoring and alerts
In a dynamic business environment, risks can emerge or escalate rapidly. Automation empowers VRM to be vigilant at all times, providing real-time monitoring of vendor activities and flagging any deviations from expected behaviors. This proactive approach enables organizations to address emerging risks promptly, preventing potential threats from materializing into larger issues.
4. Consistent application of risk assessment criteria
Standardization is the cornerstone of effective VRM. Automation ensures that predefined risk assessment criteria are consistently applied to all vendors, eliminating bias and subjective judgments. This results in uniformity in risk categorization and decision-making across the vendor landscape.
5. Centralized repository for vendor-related data and documentation
Vendor relationships involve a plethora of documents, contracts, assessments, and communication records. Automation centralizes these records into a digital repository, facilitating easy access, storage, and retrieval. This centralized hub not only enhances collaboration among teams but also simplifies compliance reporting and audits.
6. Agile response to changing vendor landscape
As the vendor ecosystem evolves, organizations need agility to adapt their risk management strategies. Automation allows for swift adjustments to risk assessment criteria, thresholds, and monitoring parameters. This flexibility ensures that VRM remains aligned with the changing risk landscape and evolving business priorities.
What are the key components of an automated vendor risk management system?
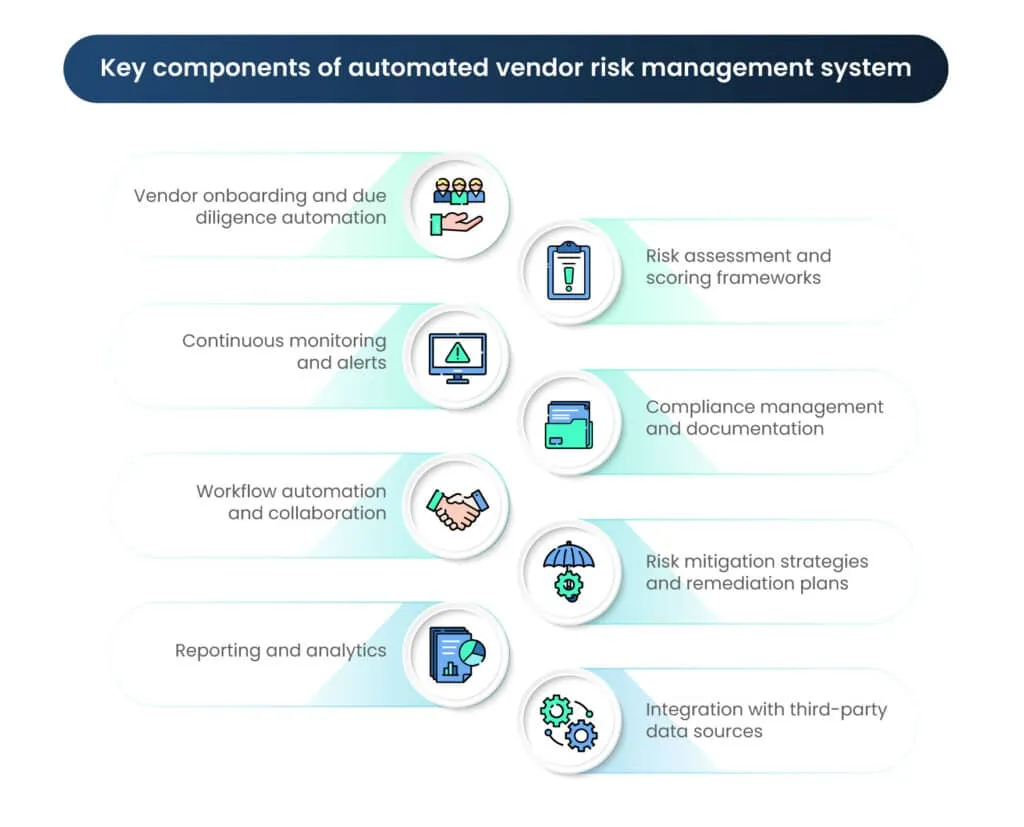
An automated vendor risk management system is a multidimensional solution that integrates technology, processes, and data to enhance the efficiency, accuracy, and efficacy of managing vendor-related risks. To create a holistic approach to VRM, several key components come into play. Let’s explore these components in detail:
1. Vendor onboarding and due diligence automation
This component involves automating the process of onboarding new vendors. It includes the collection, verification, and assessment of vendor information, which can range from financial statements to security practices. Integration with external data sources can expedite due diligence, ensuring that only reputable and compliant vendors are brought into the fold.
2. Risk assessment and scoring frameworks
Automated vendor risk management systems incorporate predefined risk assessment criteria and scoring methodologies. These criteria can encompass factors such as financial stability, data security practices, regulatory compliance, and business continuity planning. The system calculates risk scores based on these factors, allowing organizations to categorize vendors by risk level and prioritize mitigation efforts. This, in turn, is one of the major benefits of automating vendor risk assessment.
3. Continuous monitoring and alerts
An integral feature of automation is the ability to monitor vendors in real time. Automated systems can track vendor activities, detect changes, and promptly send alerts for any anomalies or potential risks. This real-time monitoring ensures that organizations stay informed about developments that might impact the risk profile of their vendors.
4. Compliance management and documentation
Automated VRM systems maintain a centralized repository for all vendor-related documentation, including contracts, agreements, audit reports, and compliance assessments. This feature streamlines the documentation process, making it easier to access information for internal use, audits, and regulatory reporting.
5. Workflow automation and collaboration
Efficient VRM relies on seamless collaboration among different teams, including procurement, legal, IT, and compliance. Automation facilitates this collaboration by routing tasks, notifications, and approvals through predefined workflows. This ensures that the right stakeholders are involved in assessing and mitigating risks at various stages of the vendor relationship lifecycle.
6. Risk mitigation strategies and remediation plans
Automated VRM systems can suggest risk mitigation strategies based on the identified risks and the organization’s risk tolerance. This might involve recommending additional security assessments, updating contractual terms, or establishing contingency plans. The system can also track the progress of mitigation efforts and ensure that remediation plans are executed effectively.
7. Reporting and analytics
Automation enhances reporting capabilities by generating standardized third party risk assessment reports, compliance status summaries, and dashboards. These reports offer insights into the overall vendor risk landscape, enabling data-driven decisions and providing a comprehensive view for senior management and regulatory authorities.
8. Integration with third-party data sources
To enhance due diligence and automate vendor risk assessment accuracy, automated VRM systems can integrate with external data sources. These sources might include regulatory databases, financial services providers, and threat intelligence feeds. Such integrations enrich the system’s ability to assess risks from multiple angles.
What are the steps to implement automated vendor risk management system?
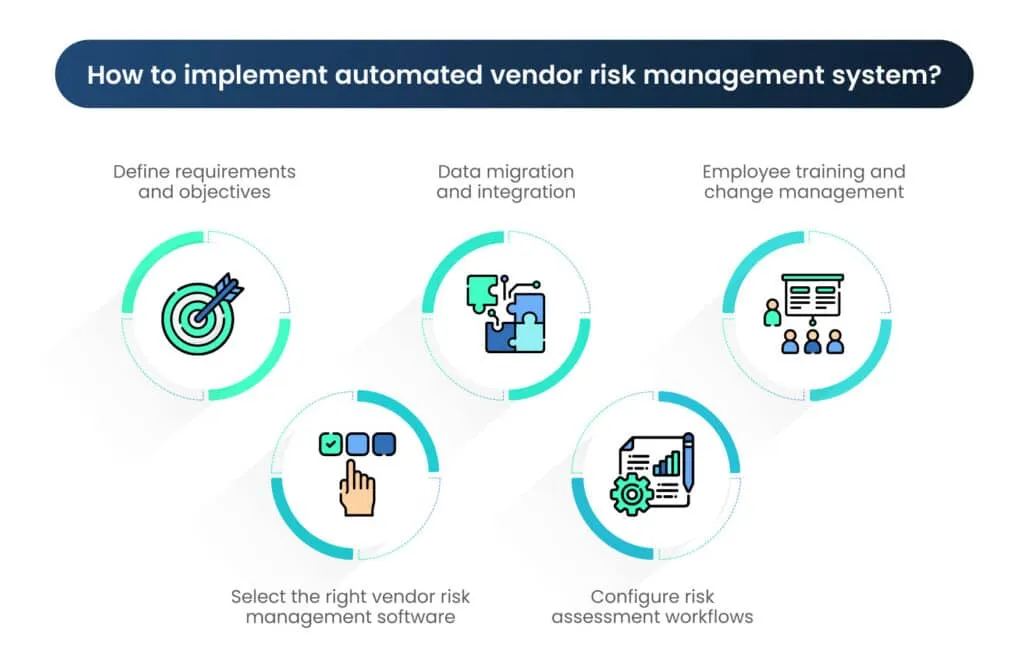
The transition to an automated vendor risk management system holds the promise of heightened efficiency, accuracy, and agility in managing vendor-related risks. As you embark on this transformative journey, a structured approach to implementation ensures a seamless transition. Let’s explore the steps involved in bringing an automated VRM system to life:
A. Define requirements and objectives
- Identify specific needs and goals for the system: Start by understanding your organization’s unique requirements. Identify pain points in your current VRM process, and envision how automation can address these challenges.
- Determine the risk assessment criteria and scoring methodology: Define the parameters that will be used to assess vendor risks. Specify the risk scoring methodology that aligns with your organization’s risk appetite.
- Clarify integration requirements with existing systems (if any): Consider the systems already in place, such as procurement software or compliance databases. Determine how the automated VRM system will integrate with these existing tools.
B. Select the right vendor risk management software
- Research and compare automation tools available in the market: Explore different vendor risk management software solutions. Consider factors like features, reputation, customer reviews, and vendor track record. Software like Scrut comes with loads of different features and integration benefits.
- Consider factors like scalability, customization options, and user-friendliness: Ensure that the chosen vendor risk managment software can accommodate your organization’s growth and is customizable to match your specific needs. A user-friendly interface will facilitate adoption.
- Check for integration capabilities with other relevant systems: Verify that the chosen software can seamlessly integrate with other systems you currently use or plan to implement in the future.
C. Data migration and integration
- Plan for data migration from existing systems to the new platform: Develop a migration strategy that ensures a smooth transfer of existing vendor data and risk assessment records to the new automated system.
- Ensure seamless integration with internal databases and external data sources: Integrate the automated VRM system with internal databases for consistent data flow. Consider external data sources like regulatory databases for enriched third party risk assessment.
- Test data accuracy and integrity after migration: Thoroughly test the migrated data to ensure that it retains its accuracy and integrity throughout the transition.
D. Configure risk assessment workflows
- Set up automated workflows for vendor onboarding, risk assessment, and monitoring: Define the sequence of automated tasks and approvals involved in vendor onboarding, risk assessment, and ongoing monitoring.
The following image shows the vendor onboarding process on the Scrut platform.
- Define roles and permissions for different users involved in the process: Specify user roles and access levels to ensure that the right individuals have the appropriate permissions within the system.
- Customize risk assessment templates according to your organization’s needs: Tailor risk assessment templates to align with your organization’s specific risk factors, industry requirements, and risk appetite.
E. Employee training and change management
- Provide training to employees on using the new automated system: Equip your staff with the skills and knowledge needed to effectively navigate and utilize the automating vendor risk management system.
- Emphasize the benefits of automation for their daily tasks: Highlight how the automated system simplifies their tasks, enhances accuracy, and contributes to better risk management outcomes.
- Address any concerns or resistance to change: Anticipate and address employee concerns about the transition. Communicate the advantages and provide support to ease the transition process.
How can an organization overcome the challenges of automated vendor risk management system?
As organizations transition to an automated vendor risk management system, they step into a realm of enhanced efficiency and accuracy. However, the journey is not without its challenges. To ensure the sustained success of your automated VRM system, it’s crucial to address potential hurdles and adopt strategies that fortify your risk management efforts. Here’s how you can overcome challenges and set the stage for a prosperous automated VRM implementation:
1. Addressing data privacy and security concerns
Automated VRM involves the collection and storage of sensitive vendor information. To maintain trust and compliance, prioritize data privacy and security. Implement robust encryption protocols, access controls, and secure authentication mechanisms. Regularly audit your system’s security measures and ensure that they align with industry best practices and relevant regulations, such as GDPR or HIPAA.
2. Regular system updates and maintenance
The dynamic landscape of technology demands constant vigilance. Regularly update your automated VRM system to incorporate security patches, feature enhancements, and performance optimizations. Develop a comprehensive maintenance schedule and ensure that your system remains up-to-date to counter emerging vulnerabilities and to ensure the system’s long-term effectiveness.
3. Continuous monitoring of system performance
While automation enhances efficiency, it doesn’t eliminate the need for ongoing oversight. Implement mechanisms for continuous monitoring of your automated VRM system’s performance. Set up alerts to notify you of any anomalies, downtime, or unusual activities. Regularly review system logs to identify any potential issues that might impact its functionality.
4. Adapting to evolving regulatory requirements
Regulations governing data privacy, cybersecurity, and vendor relationships are in a constant state of flux. Stay informed about industry-specific regulations and international standards. Your automated VRM system should be flexible enough to adapt to these changes. Regularly review and update your risk assessment criteria to reflect the evolving regulatory landscape.
Final words
In today’s dynamic business landscape, where digital connections drive growth and partnerships, vendor risk management has become pivotal. As organizations rely more on vendors, they also expose themselves to potential risks. This necessitates a robust vendor risk management strategy that goes beyond due diligence.
Automation is the answer to the challenges faced by manual processes. It offers efficiency, accuracy, and real-time monitoring, revolutionizing risk management. From onboarding to continuous monitoring, automation streamlines workflows, reduces errors, and enhances collaboration.
As we wrap up this exploration, we’re on the cusp of a new era in vendor risk management. Automation holds the promise of not only mitigating risks but also responding proactively to emerging threats, ensuring compliance, and fostering comprehensive risk assessment.
The journey doesn’t stop here—it’s a shift towards implementation, adaptation, and evolution. By embracing automated vendor risk management, organizations embrace transformative change that can redefine their path and drive sustained growth in an ever-evolving business world.
Manual vendor risk management involves resource-intensive processes, inconsistent risk assessment criteria, limited scalability, delayed risk identification, and struggles to keep up with the growing number of vendors and complex regulatory requirements.
Automation streamlines workflows, reduces errors, and provides real-time monitoring. It ensures efficient vendor onboarding, consistent risk assessment, prompt alerts for anomalies, and centralized documentation. Automation enhances accuracy, agility, and compliance efforts.
Common challenges include addressing data privacy and security concerns, ensuring regular system updates and maintenance, continuous monitoring of system performance, and adapting to evolving regulatory requirements.

Megha Thakkar is a technical content writer with about a decade of experience in cybersecurity and compliance. She writes extensively on SOC 2, ISO 27001, GDPR, and security operations, helping organizations translate complex requirements into clear, audit-ready decisions. Her work, tailored for CISOs and executive leaders, is frequently cited in U.S. government and NIST publications.

Team Scrut is a collective of compliance, security, and risk practitioners sharing practical guidance on building audit-ready, scalable programs. We write about SOC 2, ISO 27001, continuous compliance, third-party risk, cloud security, and GRC automation, blending regulatory depth with operator experience to help fast-growing companies strengthen trust, streamline audits, and stay ahead of evolving security demands.

























