Think of your organization’s security posture as its health report: a summary of how well you protect your data, systems, and people. Across industries, threat actors are evolving faster than defenses, and many companies are under threat before they even take their first step.
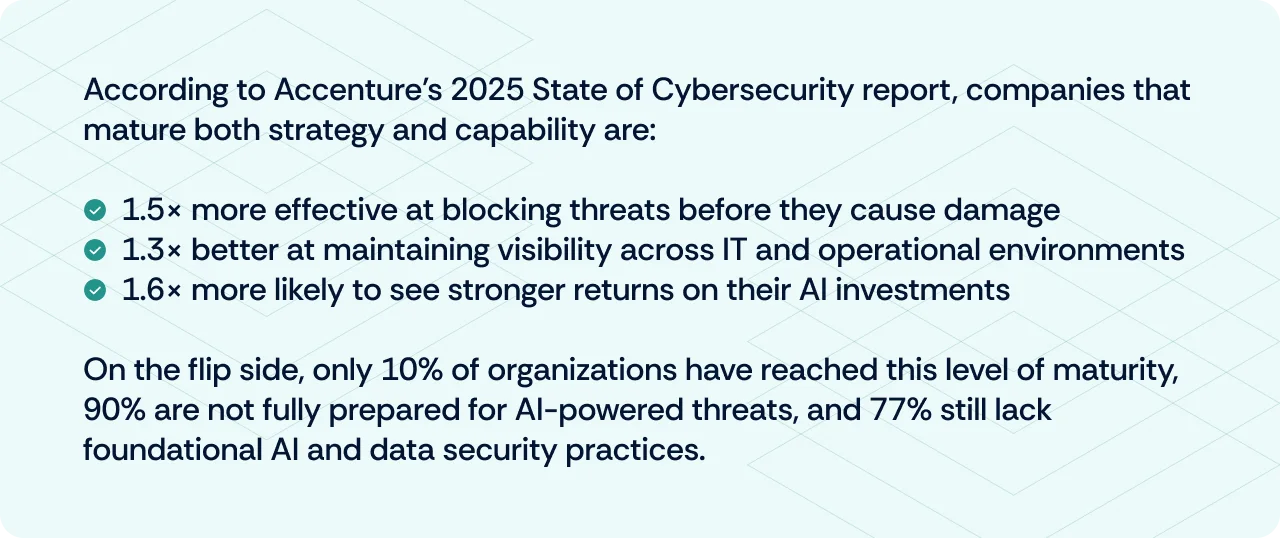
Startlingly, only 10% of companies have achieved what Accenture calls the reinvention‑ready zone, which means they combine strategic maturity with solid security capabilities. An alarming 63% still sit in the “exposed zone”, lacking both strategy and capability, making them prime targets for cyberattacks (Accenture, 2025).
On the AI front, things are even trickier: 36% of security executives admit that AI is outpacing their organization’s security readiness, and still, 90% lack the required standards to protect against AI‑driven attacks. That is one of the biggest disconnects businesses face in modern times.
So if your security posture were a health report, too many organizations are ignoring early symptoms until they’re in critical condition. This isn’t just a matter of optimization; it’s about survival.
What is security posture?
Security posture is your organization’s overall ability to predict, prevent, detect, and respond to cyber threats. It is not just about the tools you have in place. It is about how well your people, processes, and technologies work together to protect your business.
Think of it like your body’s immune system. Taking vitamins alone is not enough. What really matters is how strong, responsive, and coordinated your defenses are when a virus hits.
Your security posture reflects things like:
- How well you understand your risks
- How quickly you can detect and respond to incidents
- How often do you test your controls
- How resilient you are after a breach
According to the NIST glossary, security posture is defined as:
“The security status of an enterprise’s networks, information, and systems based on information security resources (e.g., people, hardware, software, policies) and capabilities in place to manage the defense of the enterprise and to react as the situation changes.”
A strong security posture helps your organization mitigate cyber threats before they escalate, while also preserving customer trust and business reputation. It improves your ability to adapt to evolving threats, ensuring that your defenses remain relevant as the threat landscape changes.
A well-defined posture also supports business continuity by reducing downtime and disruption during incidents. By preventing breaches and reducing recovery costs, it helps you avoid unnecessary financial loss. Most importantly, the stronger your posture, the lower your overall cybersecurity risk; the two are closely and inversely related.
What makes up your security posture?
Your security posture is not defined by a single tool or policy. It is the sum of everything you do to protect your organization, from visibility to response, from tools to training.
Here are the key components that shape it:
1. Attack surface visibility
This is your ability to identify and monitor all entry points into your systems, including endpoints, cloud assets, APIs, third-party connections, and shadow IT. You cannot defend what you cannot see.
2. Risk management
A strong posture relies on continuously identifying, prioritizing, and mitigating risks. A living risk register, business impact mapping, and periodic assessments ensure you are tackling the right vulnerabilities.
3. Incident response plan
When things go wrong, your posture is tested by how quickly and effectively you respond. Having a documented and rehearsed incident response plan helps reduce damage and accelerate recovery.
4. Compliance and governance
Security posture is closely tied to how well you align with standards and regulations like ISO 27001, SOC 2, or HIPAA. Governance policies, internal audits, and control testing play a significant role in building trust.
5. Security architecture and tooling
Your technical safeguards include firewalls, endpoint protection, SIEMs, and identity and access management systems. However, posture also depends on how well they’re configured and integrated.
6. Security processes and procedures
These include day-to-day practices like patch management, access reviews, backup protocols, and change control. Repeatable, documented processes reduce the risk of human error and improve operational discipline.
7. Employee and user training and awareness
Your people are part of your defense system. Regular training, phishing simulations, and awareness programs help build a security-first culture and reduce insider threats.
When all these elements work in sync, your organization moves from reactive firefighting to proactive resilience. As the CISO Series reminds us, security posture is not about having everything in place; it's about knowing what matters most and acting on it every day.
How to evaluate the security posture of an organization?
Evaluating your security posture is not about collecting artifacts for the sake of an audit. It is about peeling back the layers of your environment to see what is truly at stake, and how prepared you are to protect it.
Here is how you can evaluate your posture effectively:
1. Identify your IT assets
Start with an inventory of all systems, applications, data stores, and devices, including cloud environments and third-party tools. You cannot secure what you do not know exists.
2. Map your attack surface
Once your assets are identified, assess how they’re exposed. This includes internet-facing services, open ports, endpoints, APIs, and access points that could be exploited.
3. Assess cyber risk based on impact and likelihood
Not all risks are equal. Evaluate each risk by combining how likely it is to occur with the potential business impact if it does. This helps prioritize focus areas.
4. Identify security gaps and vulnerabilities
Use control testing, vulnerability scans, and audits to find what is missing, outdated, or misconfigured across your security layers.
5. Analyze the potential impact
Go beyond technical severity. Consider the operational, reputational, legal, and financial damage if a risk materializes.
6. Create an actionable improvement plan
Based on the gaps and impact, document specific, prioritized recommendations. Include timelines, owners, and metrics to track progress.
7. Repeat at the right frequency
Security posture evaluations are not one-time events. Depending on your threat profile and compliance needs, do this monthly, quarterly, or continuously using automation tools.
What are the different cybersecurity posture levels?
Cybersecurity posture typically falls into these levels:
- Reactive – Security is ad hoc and incident-driven. Issues are addressed only after they occur.
- Baseline – Basic controls are in place, often for compliance. Visibility and risk coverage are limited.
- Proactive – Regular risk assessments, employee training, and security monitoring are active. Security is planned, not improvised.
- Adaptive – Security is embedded into operations. Automation, continuous monitoring, and threat intelligence drive decisions.
- Resilient – The organization anticipates, withstands, and recovers from threats. Posture is continuously optimized and aligned with business outcomes.
How to improve and automate your security posture
Once you’ve assessed your posture, it's time to act strategically. Improvement isn’t about ticking boxes; it’s about targeting the gaps that matter and building durability over time. Automation helps you scale smarter, not harder.
Here’s how to strengthen and streamline your posture:
1. Prioritize high‑risk issues first
Focus remediation efforts on systems and data that pose the greatest business impact and likelihood of exploitation.
2. Automate asset inventory and attack surface monitoring
Deploy tools that continuously discover and track your IT assets, including cloud environments, endpoints, and shadow IT, so nothing slips through the cracks.
3. Establish robust policies, procedures, and controls
Document access control, data handling, incident response, vendor risk, and compliance protocols. Policy clarity creates consistent behavior.
4. Implement regular software updates and patching
Automate patch management to close known vulnerabilities before attackers exploit them.
5. Ensure compliance and regulatory alignment
Map remediation efforts to frameworks/standards/regulations like NIST CSF, ISO 27001, SOC 2, or HIPAA. Maintain audit trails and control maturity.
6. Utilize advanced security solutions
Leverage AI‑powered detection, unified platforms, and automated workflows to reduce manual gaps and accelerate response.
7. Maintain a living risk register with action plans
Let risk evolve with your business. Assign owners, set timelines, and update status as control failures are resolved.
8. Nurture threat intelligence programs
Feed real‑time contextual threat data into your detection engine to stay ahead of emerging attack vectors.
9. Enable continuous control testing and evidence collection
Replace periodic manual audits with always‑on posture monitoring. Tools like Scrut auto‑test controls and collect audit-ready evidence.
10. Invest in employee awareness and training
Use automated phishing campaigns, policy acknowledgment nudges, and role-based education to reinforce security habits.
11. Cultivate a strong security culture
Reward reporting, integrate security into hiring and offboarding, and make it part of daily work. Culture is posture in motion.
12. Backup data regularly and securely
Automate encrypted backups, test recoveries, and monitor failures to ensure reliable recovery.
Improving your posture is not just about surviving an audit. It’s about building real-world resilience that holds up when systems fail, when attackers get creative, and when teams are stretched thin.
Can we automate the improvement of security posture?
Yes, you can automate many aspects of improving your security posture, but not all of it.
Automation helps identify vulnerabilities, monitor controls, collect evidence, enforce policies, and respond to threats faster. Tools like posture management platforms can continuously scan your environment, detect drift, and alert you before issues become incidents.
However, strategic decisions, like risk prioritization, policy updates, and cultural change, still require human judgment. Automation accelerates the process, but posture improvement still needs leadership at the wheel.
Are there any tools to monitor for security posture management?
Yes, several tools are designed specifically for monitoring and managing security posture. Here are three widely used ones, each suited to different types of organizations:
1. Microsoft Defender for Cloud
- Use case: Monitors cloud infrastructure, detects misconfigurations, and provides security recommendations across Azure, AWS, and GCP. Also integrates with DevOps pipelines.
- Suitable for: Medium to large enterprises, especially those with multi-cloud or hybrid cloud environments.
2. Scrut
- Use case: Provides continuous security posture monitoring, automated control testing, and risk register management. Ideal for teams working across multiple compliance frameworks (e.g., SOC 2, ISO 27001, HIPAA).
- Suitable for: Startups and growth-stage companies looking to scale compliance and security together. A strong all-rounder for SaaS businesses.
3. Arctic Wolf
- Use case: Delivers managed detection and response (MDR) along with security operations support and posture management. Helps teams without in-house security expertise.
- Suitable for: Small to medium businesses and mid-market enterprises that want a SOC-as-a-service model.
Scrut is your all-in-one platform for security posture and compliance management. It helps you monitor controls, map risks, automate evidence collection, and stay audit-ready, all without drowning in spreadsheets or chasing screenshots. Whether you're a fast-moving startup or a scaling SaaS business, Scrut gives you the visibility, automation, and confidence to improve your security posture every day.
Ready to take control of your security posture?

No, cybersecurity posture and security posture are often used interchangeably, but there’s a slight nuance. Cybersecurity posture focuses specifically on your organization's ability to defend against digital threats like malware, phishing, data breaches, and ransomware. Security posture, on the other hand, is a broader term that may also include physical security, insider threats, and operational resilience. In most modern contexts, though, especially in cloud-first and digital environments, both terms usually refer to the same thing.
Yes, risk posture is an important part of your overall security posture. Risk posture refers to how much risk your organization is exposed to, and how much risk you’re willing to accept. It influences the decisions you make around controls, incident response, and investments in security tools. Security posture, meanwhile, reflects your actual ability to prevent, detect, and respond to threats. So while they’re not the same, risk posture directly shapes the priorities and maturity of your security posture.
Employees are a critical part of an organization’s security posture. They act as the first line of defense against threats like phishing and social engineering. Their actions, from following policies to reporting incidents, directly impact risk. With proper training and awareness, employees help turn security from a checklist into a culture.
Organizations use security frameworks as blueprints to build and strengthen their security posture. Frameworks like NIST CSF, ISO 27001, or CIS Controls provide a structured way to identify risks, implement controls, and measure progress. They help align security efforts with business goals, ensure regulatory compliance, and create consistency across teams. By mapping existing controls to these frameworks, organizations can spot gaps, prioritize improvements, and move from reactive to proactive security.
Yes, automation is essential for a modern security posture. It enables real-time monitoring, faster response, and reduces human error, all critical in today’s fast-changing threat landscape. Without it, staying secure at scale is nearly impossible.

Megha Thakkar is a technical content writer with about a decade of experience in cybersecurity and compliance. She writes extensively on SOC 2, ISO 27001, GDPR, and security operations, helping organizations translate complex requirements into clear, audit-ready decisions. Her work, tailored for CISOs and executive leaders, is frequently cited in U.S. government and NIST publications.

Team Scrut is a collective of compliance, security, and risk practitioners sharing practical guidance on building audit-ready, scalable programs. We write about SOC 2, ISO 27001, continuous compliance, third-party risk, cloud security, and GRC automation, blending regulatory depth with operator experience to help fast-growing companies strengthen trust, streamline audits, and stay ahead of evolving security demands.

























