Audit documentation is often treated as a simple compliance task: collect evidence, organize it, and present it when the auditor asks. But, in reality, it is rarely that straightforward.
Security and compliance teams usually have the right controls in place, but the proof that those controls worked is usually scattered across tools, screenshots, spreadsheets, and approval threads. When the audit begins, teams scramble to reconstruct months of activity into something an auditor can review.
Most guidance on audit documentation explains definitions and standards, but offers little insight into how documentation actually works in modern security programs.
This guide focuses on the practical side: what auditors look for, what effective documentation looks like in SaaS environments, and how to structure it so audits run smoothly without creating unnecessary manual work.
Summary overview
- Audit documentation connects controls to evidence. It records the procedures performed, the evidence collected, and the conclusions reached, so auditors can verify that controls operated as expected during the audit period.
- Auditors focus on completeness, timestamps, responsible reviewers, and traceability to specific controls. Documentation that clearly shows these elements reduces follow-up requests and speeds up the audit review process.
- Continuous evidence collection and automation reduce audit workload. Mapping controls to evidence, assigning owners, and collecting documentation throughout the year help teams stay audit-ready and avoid last-minute evidence gathering.
What is audit documentation?
Audit documentation is the record of the procedures performed, the evidence collected, and the conclusions reached during an audit. It allows auditors to verify that controls operated as expected during the audit period and provides a traceable record of how those conclusions were reached.
In practice, audit documentation connects controls to the evidence that proves they worked. For many teams, this often includes records such as access review exports, change approvals, configuration checks, and policy approvals.
When these records are organized clearly and linked to the relevant controls, auditors can quickly validate that the required processes were performed.
Examples of audit documentation
Audit documentation can come from many sources across an organization’s systems and processes. In compliance audits, auditors typically review a combination of policy documents, system records, and operational evidence to verify that required controls are in place and functioning.
Common examples include:
Policies and procedures
Documented policies, standard operating procedures (SOPs), and security guidelines that define how the organization manages security, access, data protection, and compliance requirements.
Audit trails and system logs
Time-stamped records of user activity, access logs, and configuration change logs that show when actions occurred and who performed them.
Training records
Certificates, learning management system (LMS) reports, or attendance logs confirming employees completed required training, such as security awareness or regulatory compliance programs.
Risk assessments and security reviews
Risk assessment reports, vulnerability scan results, and remediation plans that document how risks are identified and addressed.
System configuration evidence
Screenshots or exported system reports demonstrating security settings such as encryption enabled, multi-factor authentication (MFA) active, or firewall rules configured.
Third-party and vendor documentation
Vendor contracts, service level agreements (SLAs), and vendor security reports, such as SOC 2 reports, are used to evaluate third-party risk.
Governance and oversight records
Meeting minutes, compliance committee reports, or management approvals showing oversight of security and compliance activities.
What auditors actually look for in audit documentation
During an audit, the issue is rarely the type of evidence collected. Most teams already have policies, logs, tickets, and reports available. The problem is that the documentation often lacks the context auditors need to evaluate whether a control actually operated as intended.
Auditors typically assess documentation across four practical criteria:
Completeness
The evidence must clearly demonstrate that the control activity occurred. For example, an access review report should list all users reviewed, not just a partial screenshot of the system.
Timestamped activity
Evidence needs to show when the activity happened. Auditors rely on dates and time stamps to confirm that controls were performed at the required frequency, such as quarterly access reviews or monthly vulnerability scans.
Responsible reviewer or approver
There must be a clear indication of who performed or approved the control. For example, a pull request approval in GitHub or a documented sign-off on a change request shows that a responsible individual reviewed the activity.
Traceability to the control
Documentation must map directly to a specific control requirement. A Jira ticket for a production change, for instance, should connect to the organization’s change management control and show the approval workflow associated with it.
When documentation includes these elements, auditors can quickly understand the control narrative and validate the evidence without having to make repeated follow-up requests.
What usually happens during an audit
Most compliance audits follow a predictable pattern. Understanding the flow helps security and compliance teams prepare the right evidence in advance.
Week 1: Audit kickoff and scope confirmation
The auditor confirms the audit scope, applicable controls, and documentation requirements. A formal request list is usually shared, outlining the evidence the team must provide.
Week 2–4: Evidence collection and testing
This is where most of the work happens. Auditors review policies, inspect system configurations, and validate that controls operated as expected during the audit period.
Week 4–6: Follow-ups and clarification requests
Auditors often ask for additional documentation or clarification if evidence is incomplete or unclear.
Final stage: Report drafting and review
Once testing is complete, the auditor prepares the audit report. Any findings or observations are shared with the organization before the report is finalized.
In theory, this process is straightforward. In practice, the difficulty comes from collecting and organizing the evidence needed to answer the auditor’s requests.
That’s where most of the operational workload appears.
A practical workflow for staying audit-ready year-round
One of the biggest mistakes organizations make is treating audits as a once-a-year project. As Todd Dekkinga, CISO at Cyber Way USA, explained in an episode of our podcast, Risk Grustlers, many startups only focus on compliance during certification and then scramble to reconstruct evidence before the next surveillance audit.
The result is a last-minute rush to assemble months of evidence across systems, which significantly increases audit preparation time.
The easiest audits happen when evidence is collected continuously throughout the year.
A simple operating model helps dramatically reduce the workload.
Step 1. Map controls to evidence once
Start by identifying what evidence proves each control is operating correctly.
For example:
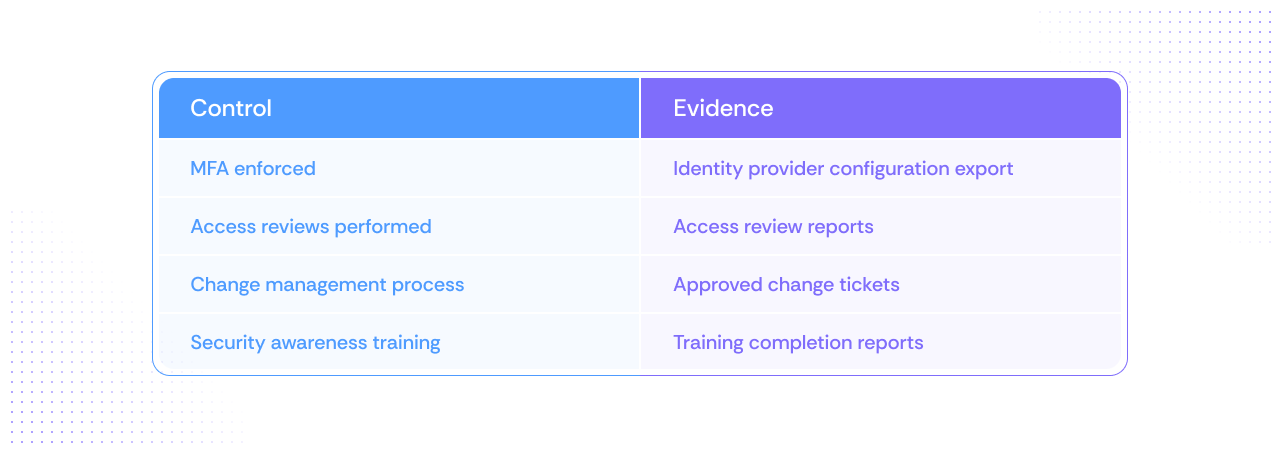
This mapping eliminates ambiguity when auditors request proof of control operation.
Without it, teams often spend time figuring out what evidence is acceptable during the audit itself.
Step 2. Assign clear evidence owners
Every piece of evidence should have a responsible owner.
For example:
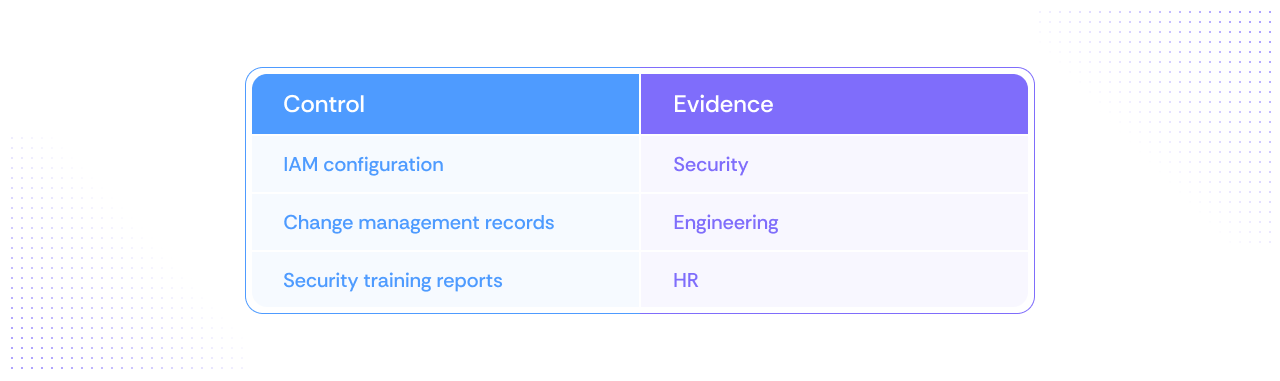
Ownership prevents last-minute scrambling when auditors request documentation. If evidence collection depends on chasing multiple teams during the audit window, the process quickly becomes slow and frustrating.
Step 3. Collect evidence continuously
Evidence collection should happen throughout the year, not just before an audit.
Teams typically do this by:
• exporting reports monthly or quarterly
• storing documentation in a central repository
• ensuring timestamps show when controls were verified
Spreading this work throughout the year avoids the common situation in which teams must assemble months of documentation in a few weeks.
Step 4. Run periodic internal checks
Internal checks help teams identify gaps before auditors do.
A simple quarterly review can confirm:
• Required evidence is being collected
• Control owners are still responsible for their controls
• Configurations still match policy requirements
These checks significantly reduce the risk of surprises during the audit.
What actually creates audit workload (and how to reduce it)
Most compliance teams do not struggle with understanding controls. They struggle to collect and manage the evidence needed to prove that those controls worked.
Three common factors create most of the audit workload.
- Manual evidence collection
Evidence often requires teams to manually:
• export logs
• generate reports
• capture screenshots
• compile documents
This process is repetitive and time-consuming, especially when auditors request historical evidence.
- Evidence scattered across systems
Compliance evidence typically lives across many different platforms:
• cloud infrastructure
• identity providers
• ticketing systems
• HR systems
• documentation tools
When auditors request proof of a control, teams often spend hours locating and exporting the relevant records.
- Repeated clarification requests
If evidence is incomplete or difficult to interpret, auditors may request additional documentation.
This leads to:
• repeated evidence collection
• additional screenshots or exports
• back-and-forth communication
The audit timeline can easily extend when these follow-ups accumulate.
The underlying issue is rarely the control itself. It is the manual effort required to gather proof of that control.
How automation reduces audit evidence work
Modern security environments change constantly. Configurations shift, access permissions evolve, and infrastructure scales rapidly.
Because of this, static evidence such as screenshots or one-time exports quickly becomes outdated.
Automation helps address this challenge by continuously collecting and validating compliance evidence.
Tools like Scrut Monitor help security and compliance teams automate evidence collection across systems and infrastructure. Instead of manually gathering proof before an audit via screenshots, spreadsheets, or one-time exports, evidence is fetched directly from connected tools, compiled into audit-ready formats such as PDF or CSV, and automatically stored as systems operate.
This approach provides several advantages:
• Evidence is collected continuously instead of during the audit window
• Control configurations are monitored in real time
• Compliance teams can quickly identify when a control drifts from policy
When auditors request documentation, teams can provide system-generated evidence showing how controls operated over time, rather than assembling proof retroactively.
This significantly reduces the operational workload associated with audit preparation.
This approach has delivered measurable results for companies such as Increff, an enterprise software company based in the United States, which reduced its compliance workload by more than 50 percent after implementing automated compliance workflows.
A simple checklist for staying audit-ready
Security and compliance teams can significantly reduce audit effort by implementing a few operational practices.
Before the next audit, confirm that you have:
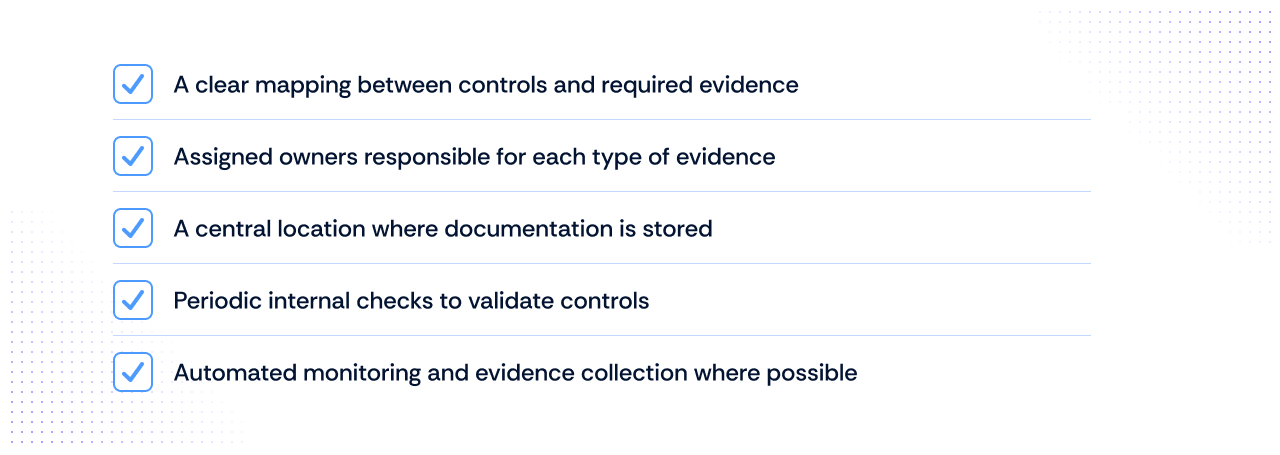
When these pieces are in place, audits become far more predictable.
Instead of scrambling to assemble documentation, teams can focus on demonstrating that their controls are operating as expected.
Conclusion
Audit documentation becomes difficult when it is treated as something to assemble right before the audit window. In reality, most of the evidence auditors request already exists inside the systems your teams use every day. The challenge is organizing that evidence so it is complete, traceable, and easy to review.
The goal is not to collect more documentation. It is to build a process that continuously captures evidence, maps it to controls, and makes it available when auditors request it. When documentation is managed this way, audits become far more predictable and far less disruptive to engineering and security teams.
Automation can play a major role here. Platforms that continuously collect evidence from cloud environments, ticketing systems, and security tools help reduce the manual work required to prepare for audits while ensuring documentation stays audit-ready throughout the year.
If you want to simplify audit documentation and reduce the time your team spends chasing evidence, schedule a demo with Scrut to see how continuous evidence collection and compliance automation can help streamline your next audit.
Not exactly. Audit evidence refers to the information auditors use to evaluate whether a control is operating effectively. Audit documentation is the structured record of that evidence, along with supporting details such as timestamps, approvals, and system reports. In practice, documentation organizes and contextualizes the evidence that auditors review.
Retention requirements vary depending on the framework and organizational policy. Many organizations retain audit documentation for at least three to seven years to support regulatory requirements, repeat audits, and internal reviews. Retention policies should align with your organization’s broader data governance and compliance requirement
Documentation is usually considered insufficient when it lacks traceability or context. Common issues include screenshots without timestamps, policy documents without approval records, or reports that do not clearly show who reviewed or authorized the activity. Auditors typically look for evidence that clearly demonstrates when the control occurred and who performed or approved it.
Auditors frequently request documentation related to access management, change management, security policies, training records, and risk assessments. This may include access review reports, change approval records, vulnerability scan results, policy approvals, and system configuration reports.
The most effective approach is to capture evidence continuously rather than collecting it during the audit window. Integrating compliance workflows with systems such as cloud infrastructure, ticketing platforms, and identity management tools helps generate evidence automatically. This reduces manual effort and ensures documentation is already available when auditors begin their review.

Susmita Joseph is a cybersecurity and compliance writer specializing in governance, risk, and regulatory content. She focuses on making complex subjects such as AI governance, cybersecurity compliance, and risk management accessible to growing and mature organizations. With a particular interest in the intersection of AI and GRC, her work explores how emerging technologies are reshaping compliance expectations and security operations.

Abinaya is an Associate PMM at Scrut, where she primarily leads analyst relations and works across product launches in product marketing. Her work focuses on shaping clear market narratives, strengthening category positioning, and translating complex topics in GRC, compliance, and cybersecurity into messaging that resonates with buyers. She is particularly driven by product marketing’s ability to connect product value with market impact, turning complex capabilities into stories that build credibility, create demand, and support growth

























