The vendor risk management maturity model (VRMMM) evaluates how organizations manage vendor risks through a set of metrics. It offers a roadmap for organizations to enhance their vendor risk management capabilities and improve their ability to mitigate risks associated with vendors. This model assesses a company’s capabilities, sets goals, and tracks progress.
This article will discuss the vendor risk management maturity model in detail.
What is Vendor Risk Management?
Vendor risk management (VRM) is the process of identifying, evaluating, and managing risks associated with an organization’s relationships with vendors. Throughout the entire vendor lifecycle, from initial engagement to termination, VRM aims to ensure that the organization understands the risks involved and takes appropriate measures to mitigate them.
VRM gives enterprises visibility into the vendors they work with, how they work, and which vendors have adequate security procedures. The VRM process requires implementing policies, procedures, and protocols to ensure compliance with all contractual requirements. It includes frequent evaluations and audits of the vendor’s performance to ensure they meet the organization’s standards.
Given that, organizations heavily rely on vendors to deliver goods, services, and technology solutions that are essential for their operations. Any disruption or failure on the part of a vendor can significantly impact the business’s continuity. VRM helps proactively identify and address vulnerabilities within the vendor’s operations, enabling the business to effectively prepare for and mitigate potential disruptions.
One approach to conducting a vendor risk assessment is by using questionnaires. A questionnaire can be used to conduct vendor risk assessments. The vendor assessment aims to evaluate and research both the current and potential vendors. By examining a vendor’s security controls, objectives, policies, practices, and other critical factors, organizations can make informed decisions about vendor selection and determine the level of risk associated with each vendor.
Some of the questions you should ask your vendors are given below:
- Do you utilize tools to monitor your network and your organization’s software?
- Can you list the software and tools used in your organization?
- Do you have a team to manage vendor risk?
- Are employees allowed to download free or open-source software, or is permission required beforehand?
Some of the types of vendor risks are explained below:
- Compliance risk – This risk arises from the potential violations of laws, regulations, and internal processes that your organization must adhere to in order to conduct business. The laws that apply to each firm will vary with different industries. However, some common requirements, such as GDPR and PCI DSS, apply to all industries.
- Operational risk – Operational risk occurs when vendor procedures are disrupted. Vendor operations are closely linked to organizational processes, so when vendors fail to fulfil their obligations, it can impede the smooth execution of daily operations within the organization.
- Strategic risk – Strategic risk is the likelihood that an organization does not make decisions that support its long-term aims. This can occur when risks are not correctly assessed, there is insufficient due diligence into new goods, business lines, or activities, or when the company takes actions inconsistent with its objectives or fails to generate the expected return on investment.
- Reputational risk – Reputational risk arises when a third-party vendor’s actions or behaviour negatively impacts your brand or reputation, directly or indirectly. You must maintain a positive relationship with your vendor so that any personal issues can not cause business interruption and resource loss.
Vendor Management Lifecycle
Vendor management refers to the process of managing vendors and coordinating with vendors throughout their entire lifecycle, from initial identification and selection to ongoing monitoring and performance evaluation. It enables your organization to recognize the value of its vendors and integrate them into your procurement plans.
The vendor management lifecycle includes multiple stages – vendor identification, vendor selection, contract negotiation, onboarding of vendors, vendor performance management, and vendor offboarding.
- Vendor Identification: This is the stage where you list down possible providers who meet your organization’s specific requirements at a certain level. This includes investigating and evaluating vendors based on their expertise, capabilities, reputation, and adherence to industry standards.
- Vendor Selection: After identifying possible vendors, you will assess them further to determine the suitable fit for your needs. It includes sending requests for proposals or conducting interviews to analyze suppliers’ credentials, pricing, and alignment with the organization’s goals.
- Contract Negotiation: Once you select the vendor who qualifies for the above stage, you will engage with them to find out and set the terms and circumstances of the agreement. This includes developing service level agreements, pricing structures, delivery timelines, and other related contractual parameters.
- Vendor Onboarding: The vendor onboarding process begins once both parties sign the contract. This stage includes exchanging pertinent information, establishing communication channels, and providing training to ensure the vendor understands your organization’s operations.
- Vendor Performance Management: This includes monitoring key performance metrics to verify whether the vendor meets contractual responsibilities. You will conduct performance review sessions and meetings with the vendor to address any difficulties, provide feedback, and explore areas for development.
- Vendor Offboarding: Vendor offboarding is the last stage when your organization cancels their contract or migrates to a new vendor. This entails handing over duties, knowledge, and applicable data or assets to the new vendor or internal teams for a smooth transition.
Vendor Risk Management Maturity Model
A vendor risk management maturity model (VRMMM) measures the maturity of a company’s third-party risk management program.
The two vital components that every VRMMM must have for determining and evaluating requirements and hazards are:
- A technique to determine how each department manages risks and where resources should be shifted or backed up.
- A technique to evaluate the development of maturity in components of your current risk management framework.
The model can help organizations better understand their present risk landscape and suggest opportunities for improvement.
The six levels of vendor risk management maturity are listed below:
- Startup: It includes newly formed firms or organizations with no established vendor risk management operations. An organization at this maturity level does not have a vendor risk assessment in place.
- Initial Vision And Ad Hoc Activity: Vendor risk management processes are ad hoc or informal during this stage with no standard process. Hence, each case is handled independently.
- Route Approval And Ad Hoc Activity: During this stage, the management has authorized a standard plan for organizing activities as part of a comprehensive implementation effort.
- Clearly Defined And Established Plans: This is the stage where policies, procedures, and guidelines are developed and documented. Vendor management roles and responsibilities are clearly defined, and there is some level of training and awareness.
- Implementation And Functioning: At this stage, the vendor risk management program within the organization is well-managed and integrated. There is a centralized repository or system for storing vendor-related information and risk assessments. It includes ongoing monitoring and reporting of vendor risks and regular collaboration with vendors to address and mitigate risks.
- Continuous Revision And Improvement: Organizations regularly assess vendor risk to optimize strategy and management after establishing the vendor risk management program. They actively look for opportunities to enhance their vendor risk management processes and stay abreast of emerging risks.
How Can Scrut Help You Manage Your Vendor Risks?
Scrut provides an efficient way of assessing, monitoring and controlling vendor risks. The tool shows insight into how your vendors perform and whether their security posture suits your organization.
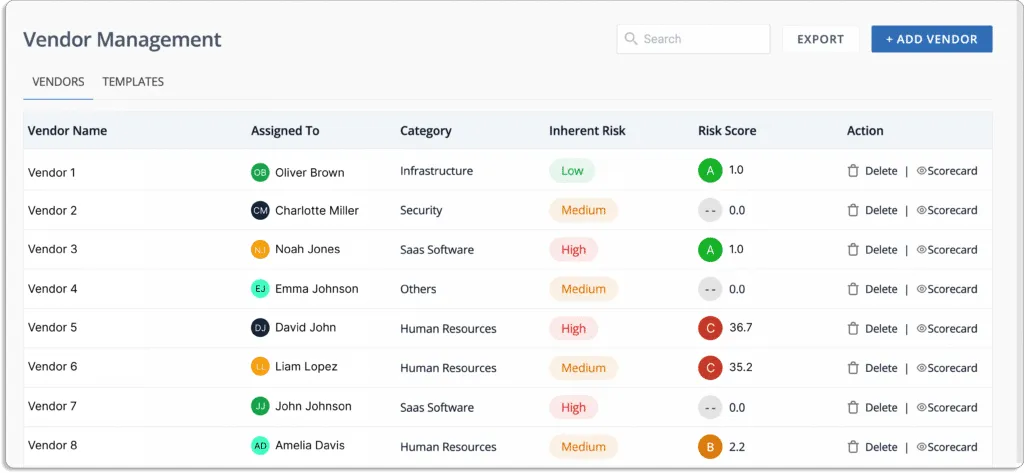
You can quickly assess how your vendors are performing in terms of compliance and information security, as shown in the screenshot below:
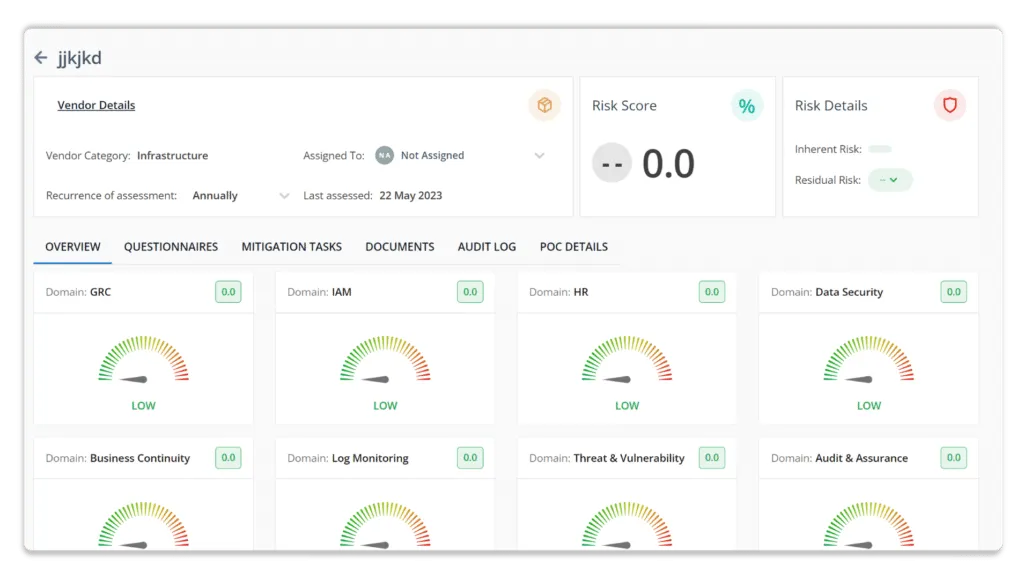
You can verify your vendor’s adherence to information security standards. You can also send security surveys and detect deviations from a single dashboard with detailed monitoring and feedback.
Scrut allows you to identify, evaluate, and track vendor risks in a single window. It speeds up reviewing your vendors’ security posture by 70% and determines whether they meet your compliance guidelines.
The tool supports you in streamlining your vendor compliance check with security questions. You can create your questionnaire or use one of our pre-made forms, as illustrated in the screenshot below.
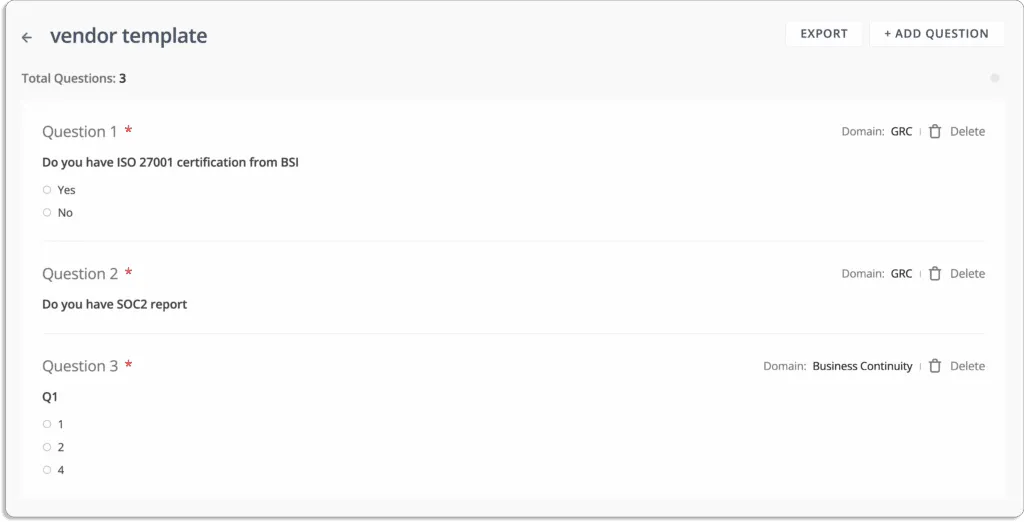
Upload A Security Questionnaire – The Scrut vendor risk management tool allows users to upload a security questionnaire or use a pre-built template. It puts an end to traditional vendor security evaluation methodologies. Users can invite suppliers to respond via an easy-to-use web-based portal.
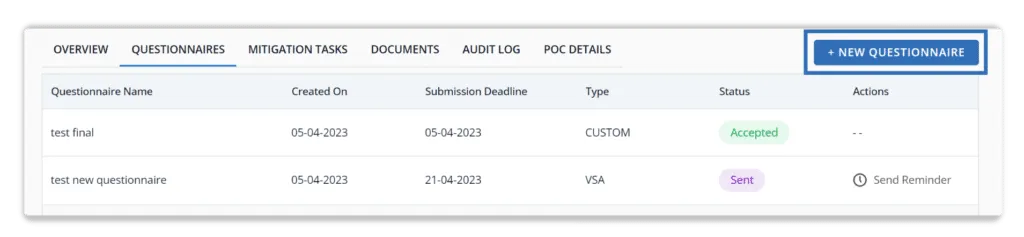
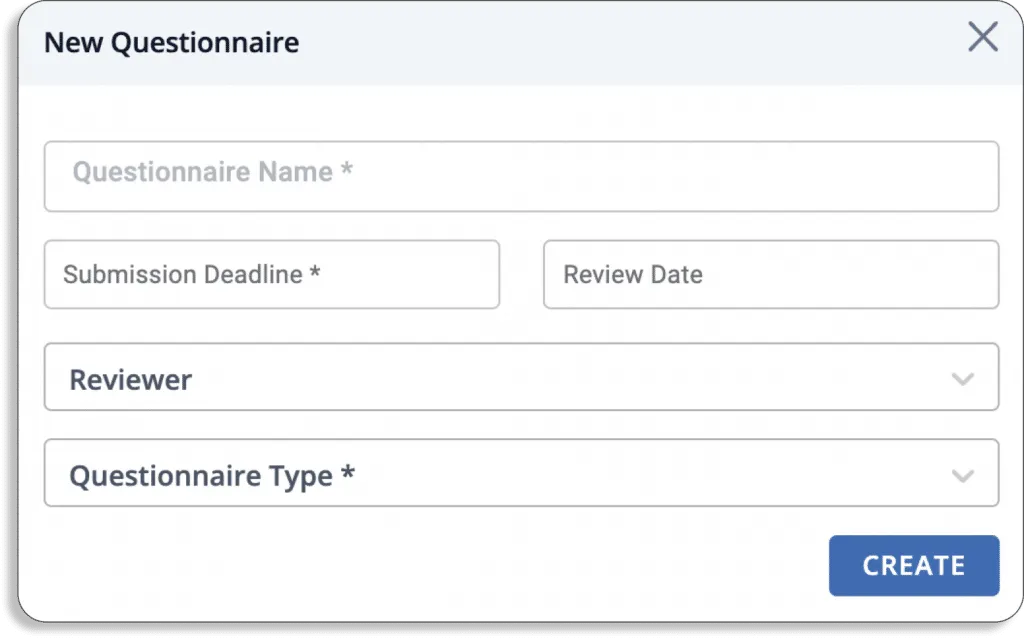
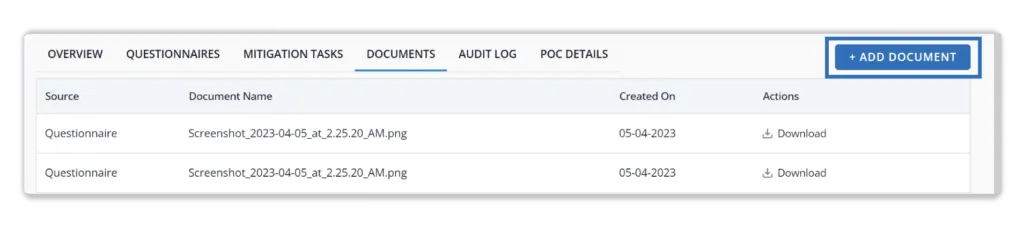
Share Review Data – Users can instantly share vendor review data for compliance and audit needs. The tool keeps all vendor security certifications, software vendor audits, and documents in one place. It allows users to share vendor responses with customers and auditors.
Invite Vendors – Users can invite vendors to complete the security audit questionnaires on the platform. It assists users in comparing suppliers to select the lowest-risk business partner or develop a risk security strategy suited to vendor risk categories.
Scrut provides a single window for identifying, assessing, and tracking vendor risks. It facilitates the evaluation of your vendors’ security posture by 70% and evaluates whether they are in compliance with your compliance standards. To learn more about Scrut Automation, schedule a demo.

Megha Thakkar is a technical content writer with about a decade of experience in cybersecurity and compliance. She writes extensively on SOC 2, ISO 27001, GDPR, and security operations, helping organizations translate complex requirements into clear, audit-ready decisions. Her work, tailored for CISOs and executive leaders, is frequently cited in U.S. government and NIST publications.

Team Scrut is a collective of compliance, security, and risk practitioners sharing practical guidance on building audit-ready, scalable programs. We write about SOC 2, ISO 27001, continuous compliance, third-party risk, cloud security, and GRC automation, blending regulatory depth with operator experience to help fast-growing companies strengthen trust, streamline audits, and stay ahead of evolving security demands.

























