Tugboat Logic is a GRC tool that gives security assurance to enterprises. It’s not the only GRC tool, there are equally good GRC platforms in the market that can better suit your requirements.
You can choose among different GRC tools available in the market based on our detailed review of the tools in this article. We have discussed the 11 best alternatives to Tugboat Logic.
Tugboat Logic is an efficient enterprise compliance automation tool that ensures hassle-free audits for your organization.
It enables your organization to maintain privacy and stay compliant with security frameworks.
Tugboat Logic automates your InfoSec program and simplifies the compliance process of your organization with different frameworks, such as SOC 2, ISO 27001, GDPR, HIPAA, PCI DSS, and CMMC 2.0.
Now, let’s see the key features of Tugboat Logic.
Tugboat Logic – Key Features
The tool helps to build and manage an entire InfoSec program as per your requirements. It automatically defines security policies, responds to RFPs, and provides proof of compliance that you can use to gain the confidence of prospects and customers.
- Tugboat Logic eliminates the hassle of collecting manual evidence as it has over 75 native integrations. Further, it offers a custom evidence API builder to integrate with the vendors of your choice that are not in the integration library.
- The tool monitors, identifies, and evaluates risks present in your organization. Next, it gives recommendations to mitigate security and compliance risks.
- It has a pre-built library of over 40 security policies and recommends security controls associated with each policy. This helps you to start and get audit ready for most of the standards quickly.
- It automatically generates policies for your organization’s InfoSec requirements
- The platform provides audit-readiness module to prepare for privacy framework certifications such as SOC 2, ISO 27001, and others
- Tugboat Logic vendor risk management module helps you understand your partner’s security posture. Tugboat automatically sends security questionnaires to third-party vendors and collects their responses, and keeps it at a single place. Thus, you can compare and choose a vendor that meets your security and compliance requirements.
Now, before discussing the Tugboat Logic alternatives in detail, let’s dive deep into a few situations where Tugboat Logic is not the right choice for you.
Tugboat Logic – Drawbacks
The tool has some drawbacks, such as
- The tool does not send automatic reminders to your team members for pending tasks.
- Integration with Salesforce is missing. This is surprising since many enterprises use Salesforce for managing their customer relationships.
- Steep learning curve. It takes some time to get used to the UI.
- More inexpensive options are available in the market
- Sometimes, the search doesn’t work properly; searching questions in your own created question bank may show 0 results
Top 11 Tugboat Logic Alternatives
There are many GRC tools available in the market among which we have listed the top 11.
1. Scrut
Scrut smartGRC platform gives you single-window observability into your InfoSec risks. What differentiates Scrut from the other GRC platforms is that it is a “risk-first” GRC platform as opposed to “compliance-first”.
This is because risk observability is the foundation of all GRC programs.

If you cannot discover risks, you can neither establish governance in your organization nor stay compliant.
To uncover all the cyber risks in your organization,
- Scrut first discovers all your cyber assets
- Then it maps the relationships between all the assets
This gives you the context on the impact of risks associated with all your cyber assets. With this context, you can prioritize how to act on those risks.

Let’s now see how you can benefit from Scrut in various ways.
Scrut provides all compliance resources in one platform
With Scrut, you get everything required to get compliant in one place. But we just don’t leave you with the platform.
We provide access to all the complementary services required to manage your compliance programs.
Along with the GRC tool, you get access to the following:
- Help with gaps assessment
- Penetration testers, including red-team testers
We also assist you in locating the auditors that are the perfect match for you. We have a network of best-in-class auditors, like BSI, EY, and RiskPro.
Besides this, we even manage your SLAs with the above partners and represent you during the external audit. This means you don’t need to take the headache of answering the auditor’s questions.
In short, Scrut is your one-stop solution for all governance, risk, and compliance programs.
Don’t believe us? Have a look at some of our customers’ reviews on G2.
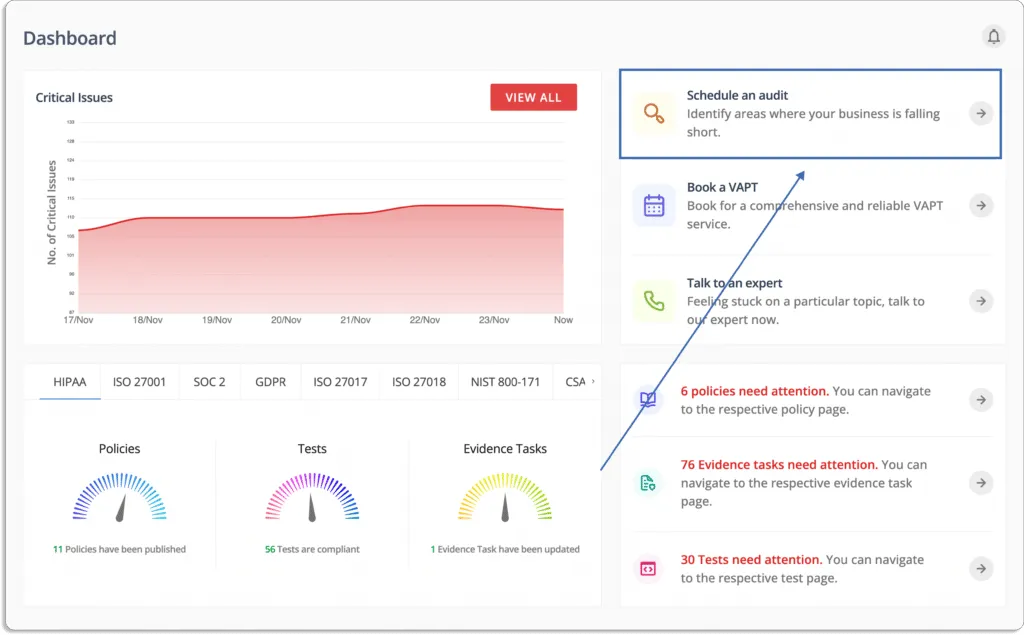
Eliminate dashboard fatigue with unified, real-time view of risks
With Scrut, you don’t have to switch between different tools to view all the risks.
Unlike other points solutions, you can directly manage your risks and compliance from a single platform, no matter how many cyber assets you have and where they are located.
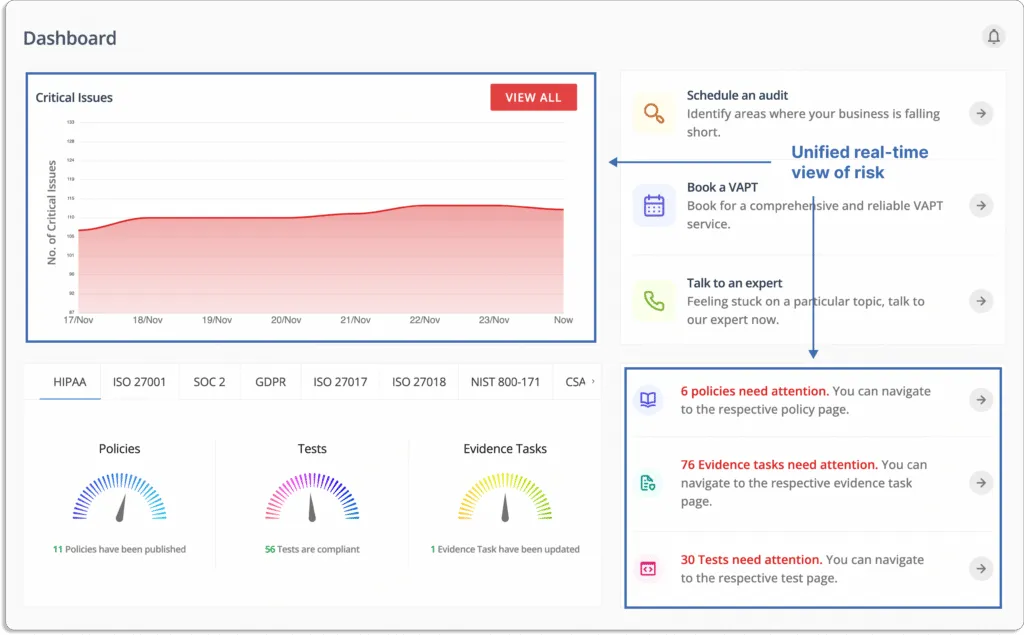
Going one step ahead, Scrut smartGRC helps you set up controls that can act on those risks, many of which are part of popular standards like ISO 27001, SOC 2, GDPR, PCI DSS, HIPAA, etc. Once the controls are set up, you can monitor them directly from the platform.
Get compliant 5x faster
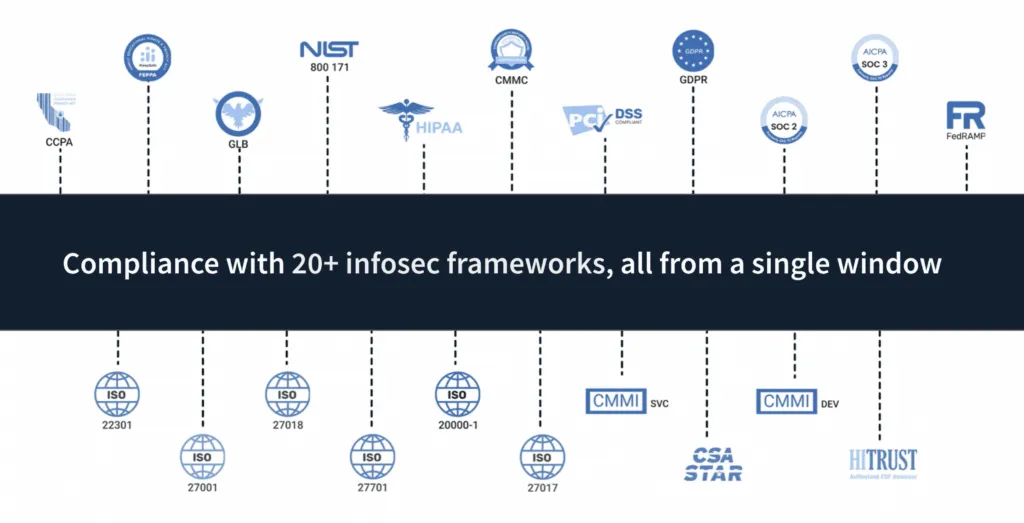
Get audit-ready faster for security and privacy standards such as SOC 2, ISO 27001, HIPAA, GDPR, FedRAMP, CCPA, PCI DSS, and others.
In all, Scrut currently supports over 20 security and privacy standards.
Scrut eliminates 70% of manual work by automating tasks, such as
- evidence collection,
- gap analysis,
- identifying misconfigurations, and
- centralizing policies.
Moreover, when going for multiple standards and regulations, you don’t worry about duplication of efforts. Scrut automatically maps artifacts to all the standards you want to comply with.
For example, if you create a critical policy through Scrut’s policy manager, say the Access Control Policy, it’ll automatically get mapped to relevant ISO 27001 controls and SOC 2 criteria. You need not create and map the policy twice for both the frameworks separately.
And we set this up very swiftly. For one of our customers that works with US federal agencies, it took us 3 business days to set up 11 frameworks.
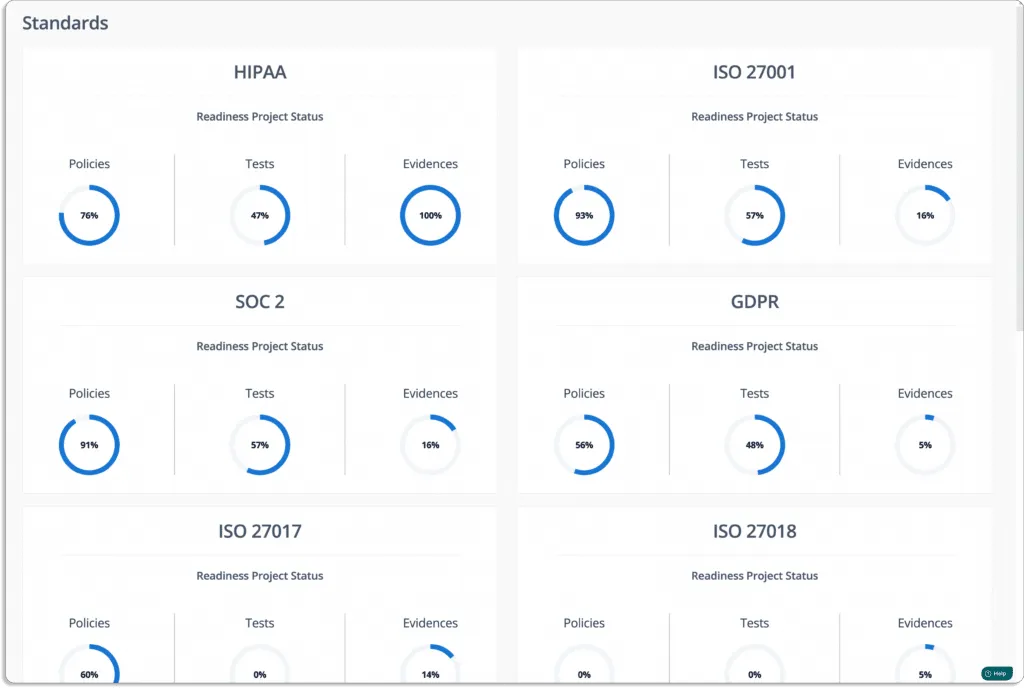
See the dashboard below from one of our customer.
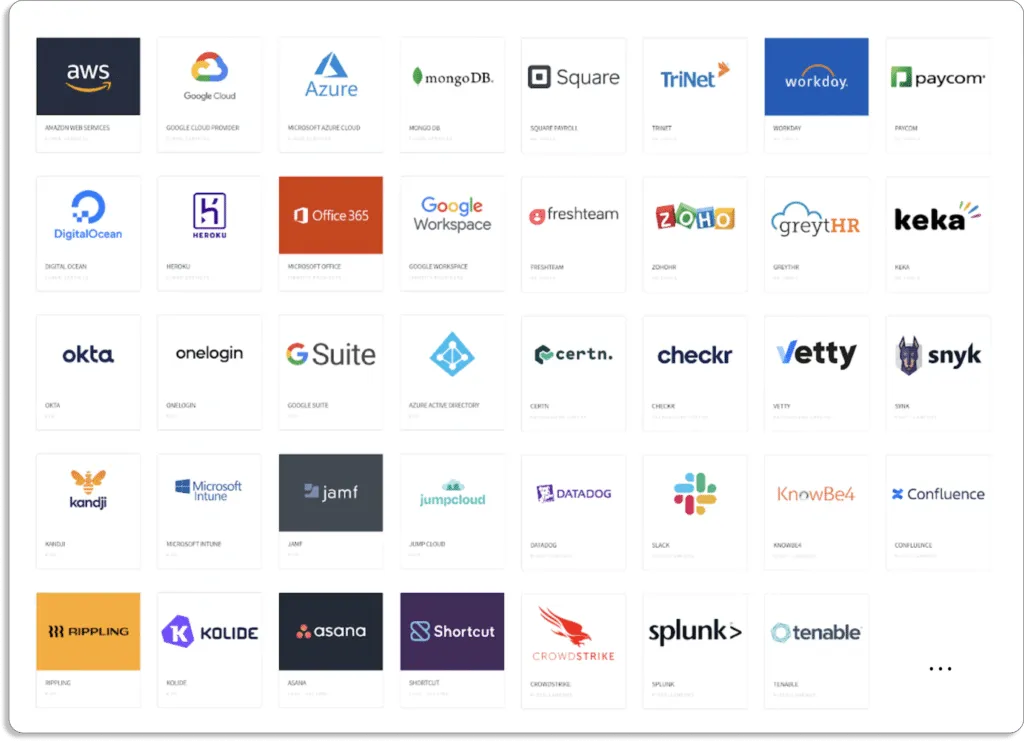
Automate evidence collection with 70+ integrations
Scrut connects with your existing tools, like cloud service providers, identity providers, MDM, task tracking tools, code version controls, HRMS, SSOs, and more, to automate your evidence collection.
Here are the integrations that we do off the shelf:
Once collected, Scrut keeps these evidence records in a central place.
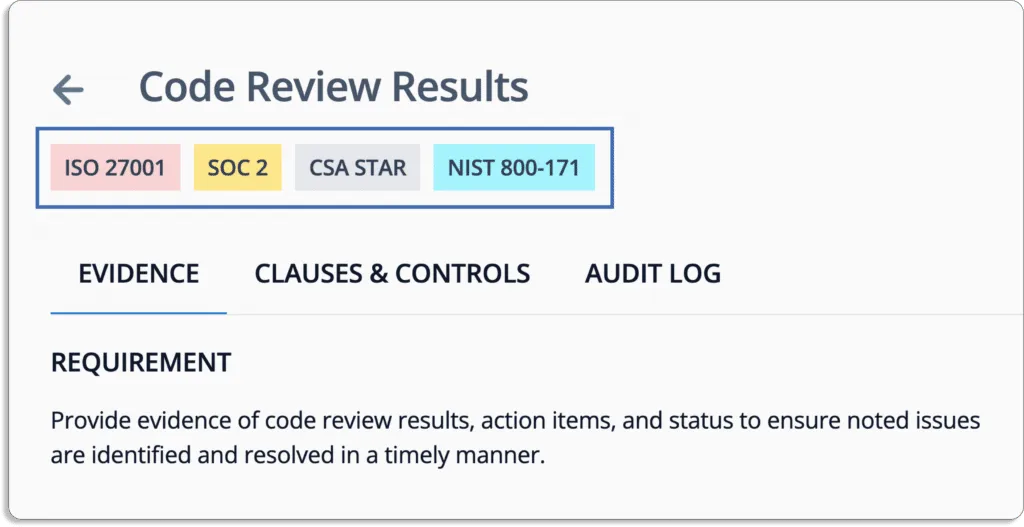
Let us understand this with the help of an example.
In a general scenario, when not using Scrut, your senior developers would be required to review the code from a security perspective. This task is required if you are going for any of these frameworks: ISO 27001, SOC 2, CSA STAR and NIST 800-171.
Here are the steps involved if this is done manually:
- Senior developers are required to review the code from security perspective.
- Then they need to prepare a report for every audit and upload it in their Google Drive, Box, or whichever place they are keeping record at.
- Repeat the above process every quarter.
- What agitates this pain is this needs to be done every quarter.
What could go wrong this this manual process? There are possibilities that:
- They miss to do the code review in time.
- Even if the review is done, there are chances that they fail to upload the review report.
- The report get misplaced and you are not able to find it later when required.
- Furthermore, there is no way to track if any backdated changes have been made or if it is deleted by anyone in the absence of logs. Thus, the integrity of the report is questionable.
On the other hand, Scrut, based on the frameworks you want to comply with, automatically populates the evidence tasks.
As you can see in the image below, the recurrence how frequently this report this reports need to be updated.
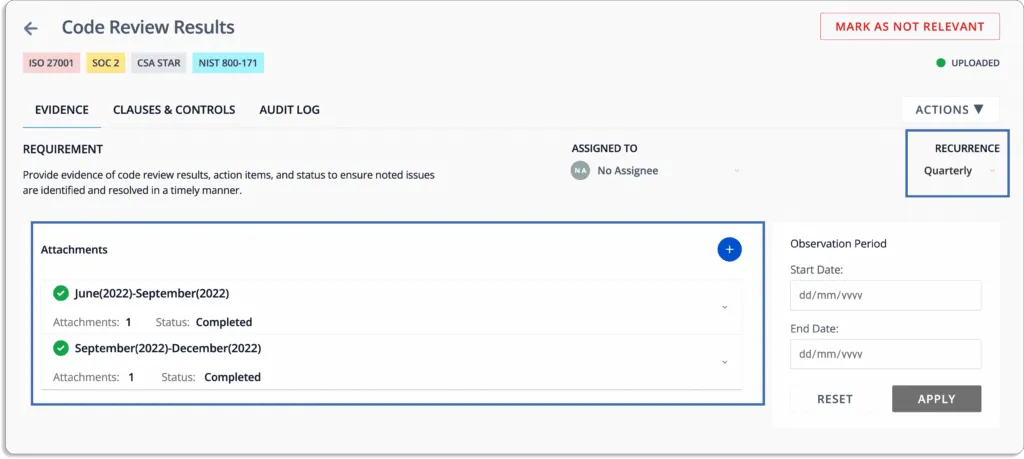
If for any reason the developer misses to upload the report, they get notified in their email or Slack, based on the settings. Thus, Scrut make sure that this task does not get left undone.
As all your evidence are attached at with relevant tasks, there is no chances of it getting misplaced or deleted.
Furthermore, Scrut logs all minute changes done by any user, whether in evidence changes made to policy documents, or API calls made through our integration.
The audit logs give the credibility the code review reports as every minute change is recorded.
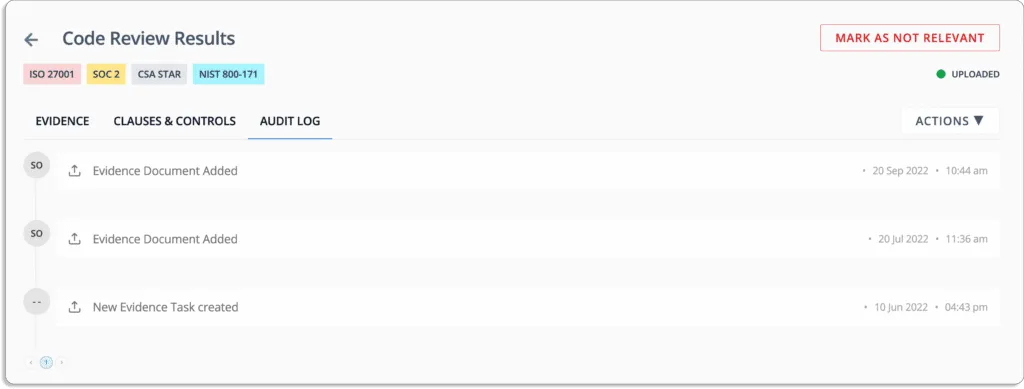
Earlier, one of our customers was keeping the evidence in Google Drive in various folders and was losing track of when the versions were updated. Scrut solved the problem immediately.
Streamline audit-related tasks
Scrut smartGRC streamlines every audit-related task from audit readiness to examination.
You can assign and keep track of tasks directly on the platform. This holds your team accountable to complete the assigned tasks within the deadlines.
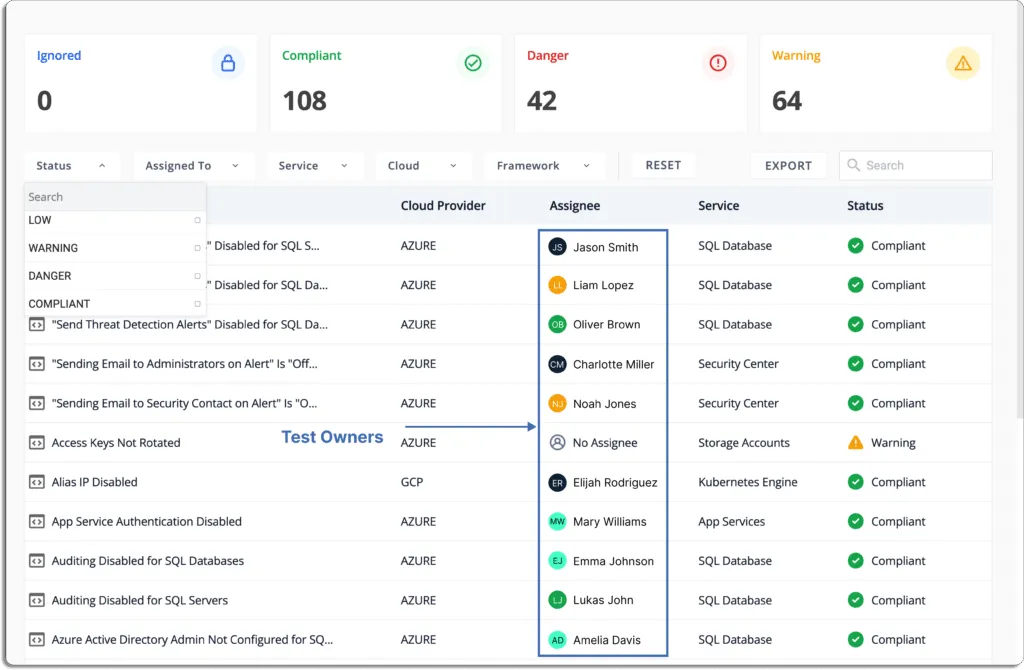
These owners can be a department or team heads who can further assign tasks to their team members.
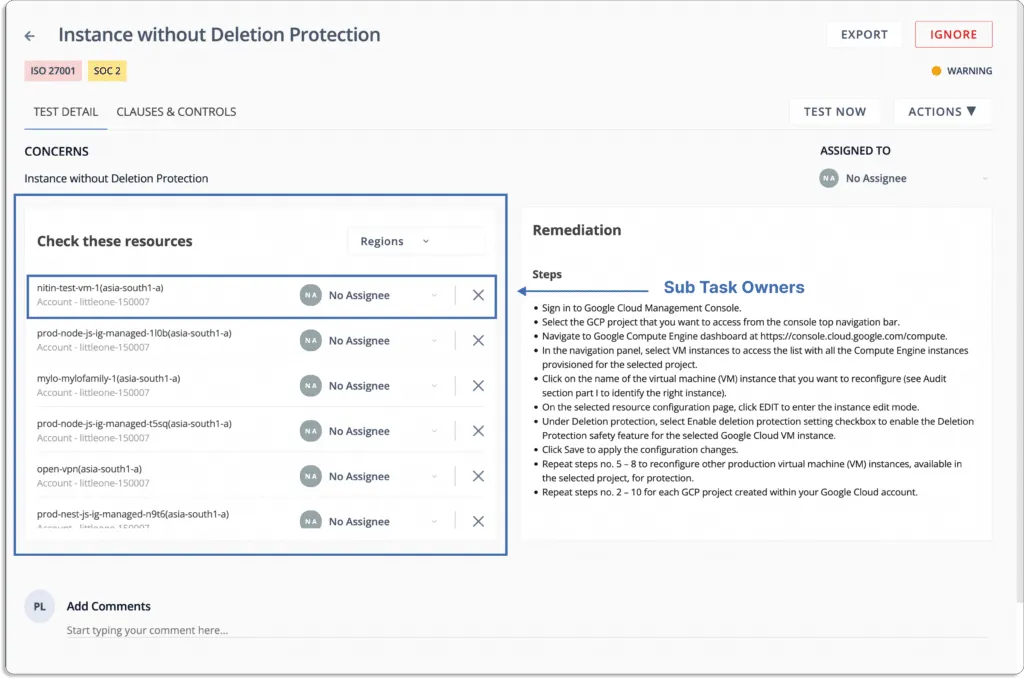
When you are ready for an audit, you can schedule an audit directly from the platform.
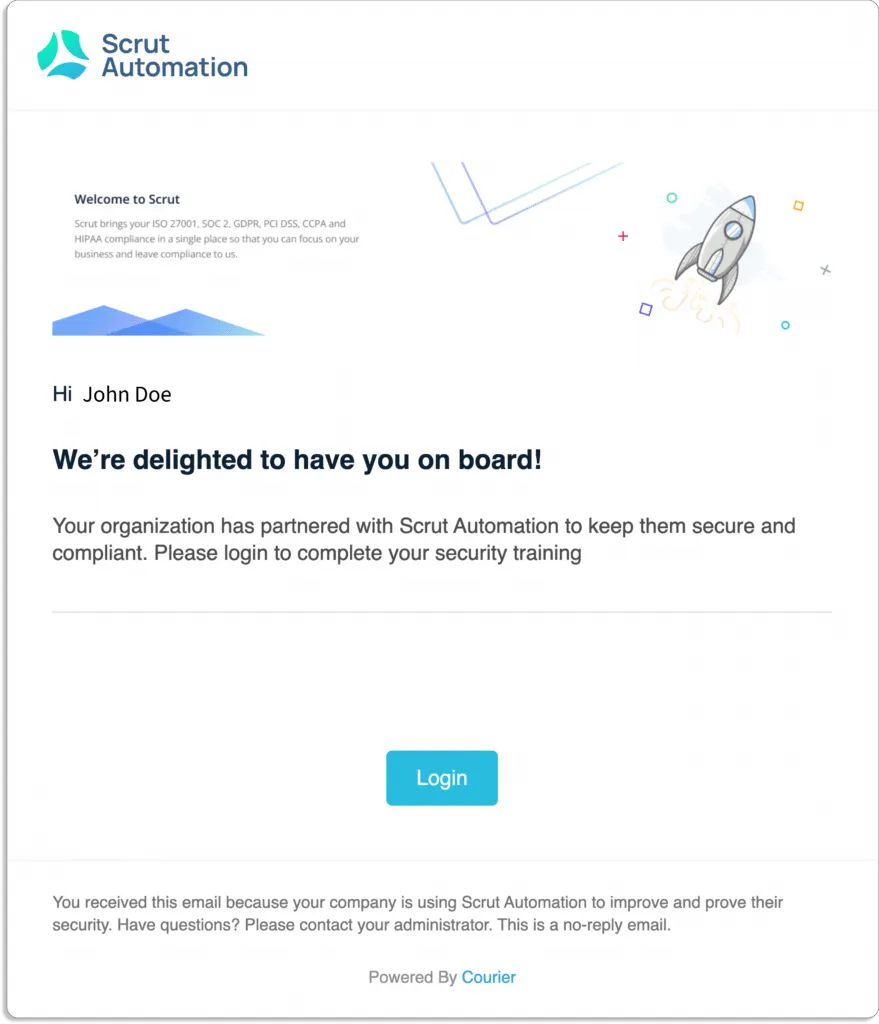
Automate security training awareness for employees
Scrut offers prebuilt 30 minutes course made by industry experts to automate employee InfoSec training. This enables employees to get well-equipped with everything they need to understand potential risk and avoid making mistakes (like clicking on phishing emails).
As you onboard an employee, they get an email asking them to sign on to their training platform.
After they log in, they see a dashboard like this with all the policies.
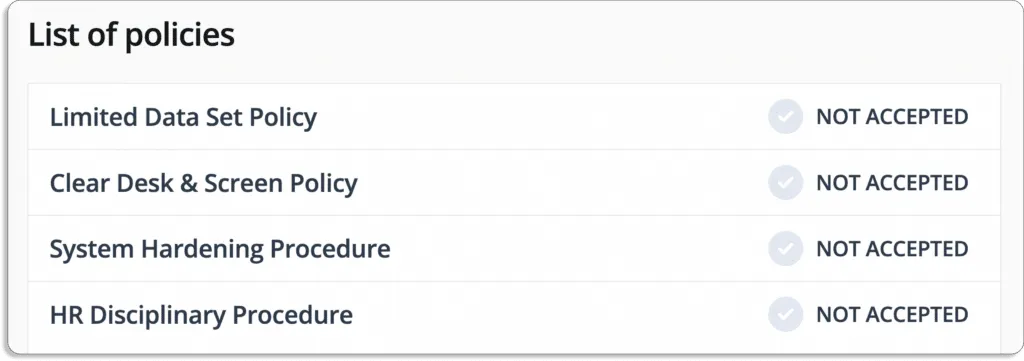
They can go thorough policy by policy and acknowledge the same and the overall status with change.
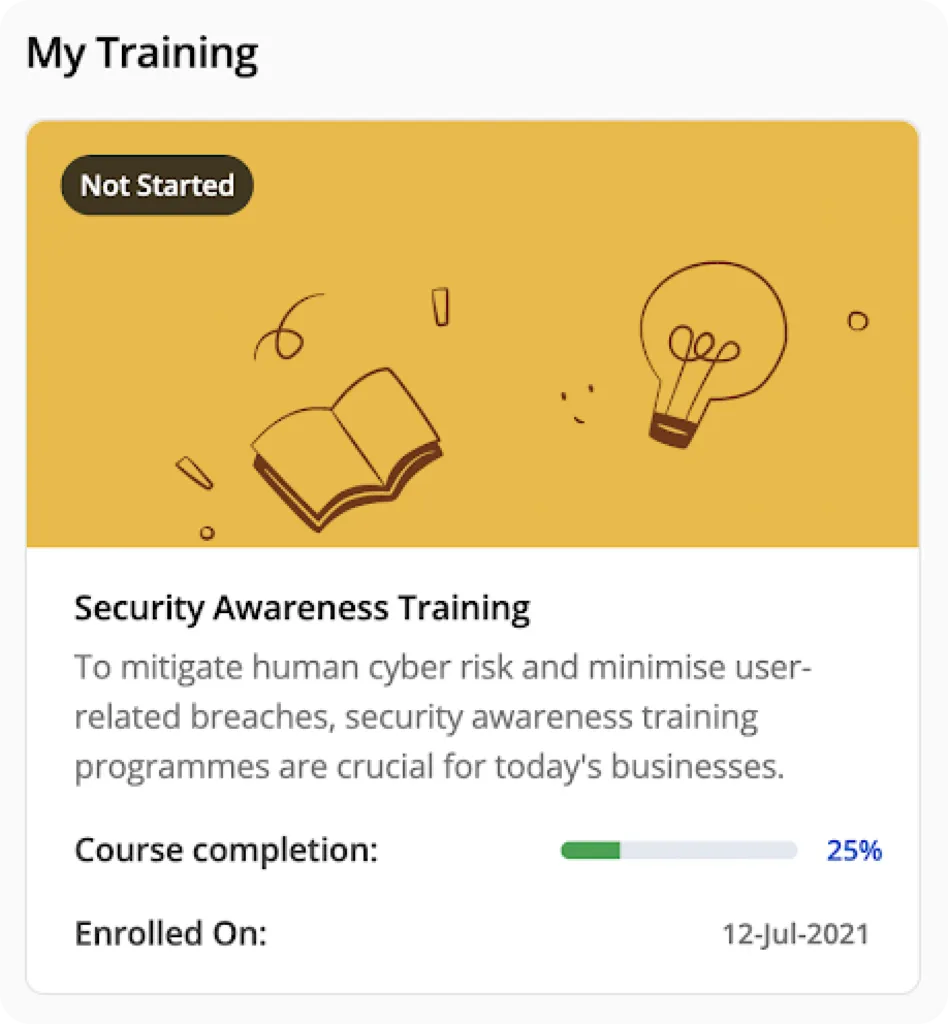
As an admin, you’re always aware of the overall aspects of employees training programs.
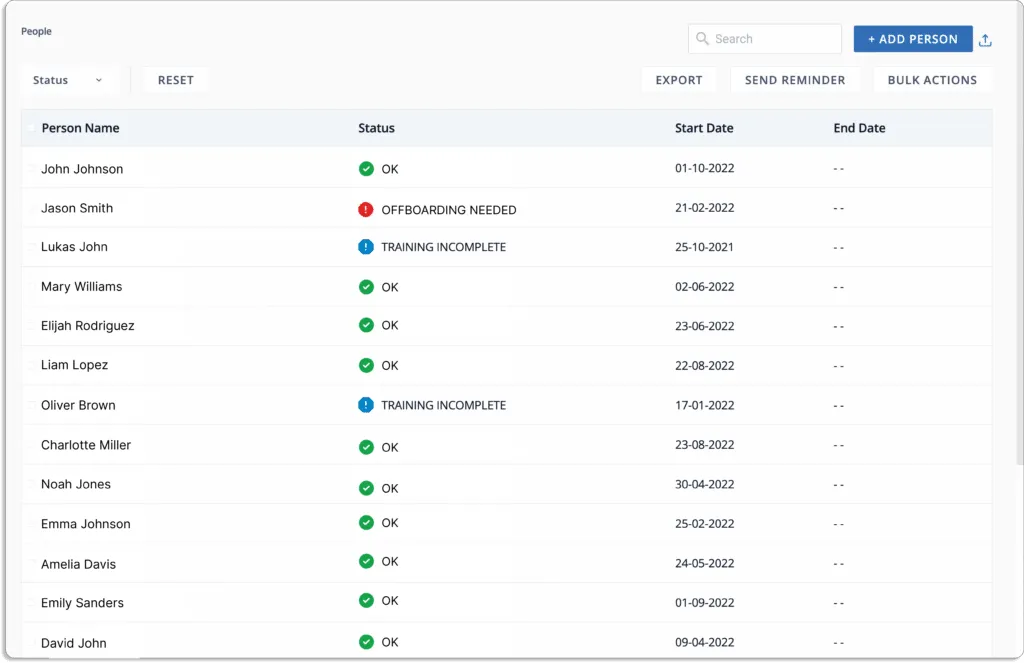
At last, you can be sure that they have not just gone through the policies but have actually understood them with quizzes.
Minimum thresholds score guarantees that your employees are informed and prepared to handle threats.
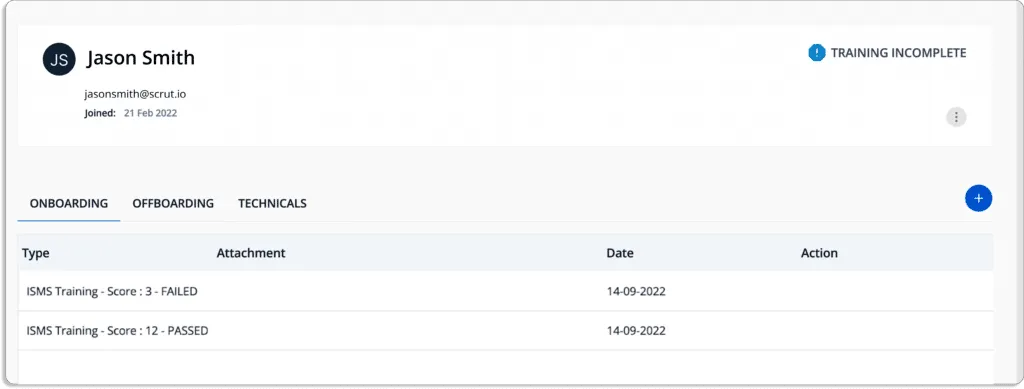
See the score of an employee who first failed, then went through the training, and finally passed.
We hold ourselves accountable till the end
Our customers have a 100% audit success rate. This is because before going for the external audit, we conduct very rigorous internal audits to ensure that our customers can pass the audit in one go.
Scrut’s founding team has experience doing 3000+ assessments across the globe over the last 15 years. Additionally, the InfoSec delivery team consists of folks from the Big Four.
With Scrut, you get hand-holding throughout your compliance journey. We don’t just leave you with a tool. We put our skin in the game!
Our payments are performance-based, and we get paid when the audits are successful and certificates issued. We’ll ride with you till the end of the line.
Customer Rating
- G2- 5/5
2. Vanta
Vanta helps in compliance automation for SOC 2, ISO 27001, HIPAA, GDPR, and other in-demand security and privacy frameworks to scale security practices for organizations.
Vanta’s risk management solution simplifies and provides risk assessment automation to eliminate an organization’s manual, complicated, and limited risk management capabilities.
To scale an organization’s security and privacy frameworks, Vanta has specialized compliance frameworks.
Vantas’ guided scoping, policies, controls, and automated evidence collection support each framework and ensure the audit readiness of your organization.
Pros
- The platform provides continuous compliance by ensuring an unparalleled view into complex environments.
- The platform detects vulnerabilities in cloud infrastructure by providing an automated test feature.
- With Vanta, users can examine different aspects that need to be monitored by generating automatic to do lists.
- The tool offers extensive monitoring capabilities, including monitoring for improper storage buckets and encrypting employee workstations.
- The platform provides a task-based methodology to find work that can be done right away.
Cons
- The platform has fewer specific integrations with US-based companies but needs more integrations with other software. For example, they don’t have integration for Microsoft Teams but have with Slack.
- The tool needs clear scopes and feedback loops between SOC 2 controls, available policy choices, and auditors’ opinions.
Customer Rating
- G2- 4.7/5
3. Drata
Drata helps you to gain visibility into your security posture and controls your compliance. It provides automated monitoring, evidence collection, and asset and personnel tracking. The tool streamlines the access controls completely with workflow automation.
You get the compliance status of all your people, devices, assets, and vendors into a single dashboard with 75+ SaaS integrations that provide complete visibility of controls across your security program.
It provides pre-vetted auditors to streamline the audit experience and support in your compliance journey.
Pros
- The platform allows users to focus on developing products by providing a control suite and monitoring that reduces the cognitive load required for compliance.
- Quick access to compliance experts from the platform.
- The tool provides estimation on how much work is still to be done by showing which activities you have finished and which are still unfinished through Drata’s dashboard.
Cons
- There is a 25MB file size limit for all evidence uploaded to Drata. Whenever you need to upload something larger, you must contact Drata’s assistance.
- Lacks integrations like sending Slack notifications when a test fails.
Customer Rating
- G2- 4.9/5
4. AuditBoard
AuditBoard provides a single platform to bring people, risks, and insights together to improve business resilience and keep pace with today’s demands.
It safeguards your organization from costly violations through effective adherence to compliance activities by managing all the evolving compliance requirements.
The tool helps to improve risk visibility in your organization and drive risk-aware decisions for mitigating all the risks.
The tool helps you stay compliant with all the required security and privacy frameworks. You can scale your compliance program faster and keep pace with changing regulations as AuditBoard automatically maps new framework requirements to your controls.
Pros
- Seamless and easy to adapt across the organization.
- Provides templates and best practices that can assist you in modifying your present procedures as you adopt.
- It doesn’t require much training for auditors and process owners to start utilizing the platform.
Cons
- The tool does not have all the auditing capabilities and need to add data analytics and automation processes to be more functional.
- Non-editable data in survey templates.
- Initial set up is complicated.
Customer Rating
- G2- 4.8/5
5. Hyperproof
Hyperproof platform organizes your risk management and compliance processes by automating workflows and unifying them so you can focus on what matters most.
It is an end-to-end system for understanding compliance requirements, maintaining internal controls, establishing appropriate compliance/audit processes and workflows, automating manual tasks, and monitoring/reporting compliance posture.
With Hyperproof’s risk management module, you can capture, analyze, and manage all risks by observing how risk decisions and remediation efforts affect your compliance posture.
The platform manages all compliance program requirements, internal controls, and evidence in one location. It provides prebuilt and customized templates for each framework for quick-start.
Control mapping, control implementation, evidence collection, testing, and monitoring are all made much more structured and efficient with Hyperproof’s workflow optimization and automation features.
Pros
- The platform manages your compliances ensuring controls, mitigation strategies, plans, tasks, and validation are easily available to you.
- The app reduces redundant work across programs, saving time and reducing errors.
- You can transfer the work of one compliance framework to another framework. For example, you can transfer the work for SOC 2 over the ISO framework for ISO 27001 compliance.
Cons
- Some functionality of the tool are not compatible with all browsers. For instance, downloading already uploaded artifacts through Firefox does not work properly.
- There is steep learning for understanding structure controls, particularly when you have many compliance requirements.
Customer Rating
- G2- 4.5/5
6. ZenGRC
ZenGRC simplifies audit and compliance management. With this tool, you can easily access necessary information for program evaluation and continuous compliance monitoring to address risk assessments to critical tasks with a complete view of the control environments.
ZenGRC effectively controls and assesses risks using risk management programs. ZenGRC pairs with Reciprocity Risk Intellect and unlocks risk insights for you to take proper risk-mitigating actions using existing compliance data from ZenGRC.
With ZenGRC, you can consolidate policies and procedures to automate routine compliance activities within your organization to maintain security and privacy frameworks compliance.
Pros
- ZenGRC provides a holistic view of how compliance status, program maturity, audit results, and vendor affect the overall risk scope of an organization.
- The tool provides easy mapping capabilities between frameworks, programs, risks, and vendors of an organization.
- The tool provides a system of record for all types of objects including business, compliance, audit, and risk objects.
- Its built-in dashboard, automated workflows and, data import and export capabilities save a lot of your time.
Cons
- It has limitations in customizable notifications and interfaces automatically open new tabs that quickly clutter your browser.
- Asset relationship mapping is very cumbersome and is not intuitive with what the system displays.
Customer Rating
- G2- 4.4/5
7. Secureframe
Secureframe helps you achieve and maintain continuous security and compliance such as ISO 27001, SOC 2, PCI DSS, HIPAA, CCPA, GDPR, and more. The tool streamlines your privacy frameworks and security standards to accelerate sales cycles and security posture.
The platform monitors all five SOC 2 trust services criteria and manages ISO 27001 certificates and surveillance audits. It also creates and monitors healthcare compliance programs and protects customer data.
Pros
- The platform provides regular meetings and Slack access while you get ready for your audit.
- Automated hundreds of manual procedures by assisting in fetching your vendor data.
- It provides easy to use reports tab to make your organization compliant with privacy frameworks.
Cons
- It needs advance refreshing capabilities as now their team manually refreshes the tasks after you fix any issues such as solving issues in AWS.
- Processes are a bit manual. It needs improvement in the automated processes to provide a seamless user experience.
Customer Rating
- G2- 4.6/5
8. Sprinto
Sprinto is powering cloud companies with security compliance programs through security audits worldwide. The platform launches compliance programs for tech companies efficiently and minimizes risks using its risk mitigation strategies.
Sprinto has 20+ built-in audit-ready security templates. provides built-in workflows around policies such as acknowledging joiners on getting hired and periodic leadership reviews.
It provides pre-approved, auditor-grade compliance programs to launch compliance, reducing your burden of manually figuring out the compliance.
Pros
- Sprinto handles most of the compliance-related tasks, including external audit firm interaction and protocols.
- The software automates your compliance process and helps you to get SOC 2 Type 1 and Type 2 hassle-free in no time.
- The tool integrates with major services such as AWS, GCP, and major HR management software.
Cons
- You need desktop installation of this software that is difficult and a cumbersome task for users.
- Your backend team needs to do a lot of manual work that can be replaced with automated workflows.
- They provide many features that are sometimes tough for users to grasp all at once and have a steep learning curve.
Customer Rating
- G2- 4.9/5
9. LogicGate Risk Cloud
LogicGate Risk Cloud is a cloud-based platform with a collection of pre-built applications that combines expert-level information and support with simple and no-code technology to transform the way you manage GRC operations.
You can start whenever you want with LogicGate Risk Cloud and add new frameworks and procedures as your GRC program develops. Since everything is on one platform, you can quickly link the components together so that your team has access to all the relevant data.
Pros
- You can automate evidence collection by creating forms to gather, and store details and answers required for events and locations.
- It takes your existing data formats and can easily import in the automated dashboard for better report generation capabilities for your organization.
- The platform provides workflows to create forms, manage reporting, and a customizable dashboard that you can use for easy exporting into different formats to generate value and give visibility to the privacy program.
Cons
- It needs more improvement in reporting customizations to provide better real-time reports for making informed decisions in the organization.
Customer Rating
- G2- 4.6/5
10. Logic Manager
LogicManager takes your business risk management to the next level using its flexible and intuitive GRC software. It provides a comprehensive matrix of GRC solutions that accelerates your risk assessment and compliance. Its robust risk management solution keeps your organization’s security ahead.
- The tools provide intuitive and accurate enterprise GRC dashboards and real-time reports to help you make an informed decision that increases your business performance.
- You can customize your most essential actions for quick access to profiles and data
- The tool provides you intelligent insights using its built-in controls and control suggestions to shrink your compliance burden.
- The tool provides customized workflows for tasks automation to plan and scope processes for decision makers and monitors responsibilities with an easily accessible to-do list.
- It helps to configure GRC from input fields to fit specific scenarios using custom profile and visibility rules.
- It allows seamless integrations to more than 50 popular third-party applications using its integration hub.
Pros
- The platform streamlines programs by providing customized workflows.
- The owner can create forms without the need of experts or consultants.
Cons
- The software doesn’t provide efficient risk assessments while maintaining historical data of previous risk assessments and due diligence requirements.
- It needs more improvements with the out-of-the-box reporting, and integrated workflows.
- The tool’s centralized configuration doesn’t enable individual thresholds for single entities of a big organization with different needs.
Customer Rating
- G2- 4.4/5
11. JupiterOne
JupiterOne provides a consolidated compliance solution to your cybersecurity and governance team. It supports all major compliance frameworks, including ISO, SOC 2, NIST, CIS, HIPPA and PCI, and HIPAA. The team provides custom frameworks and policies to meet your specific governance and compliance requirements.
Your team can discover security risks, prevent data breaches, and manage continuous compliance with total visibility across your cyber assets. JupiterOne enables you to automatically collect data to satisfy compliance requirements and handle your next audit proactively.
Furthermore, it assists you in developing and automating strong procedures, policies, and controls that connect security needs to specific cyber assets in your digital environment.
The platform keeps your team on the same page with out-of-the-box policies, procedures, controls, and automatic evidence gathering features. It assists enterprises in streamlining their compliance needs, regardless of security maturity level.
The platform provides built-in templates for security policies and procedures that are directly linked to your environment.
Pros
- User can visualize the relationships to understand what exactly going on in their digital environment.
- User can find assets matching filters with query syntax.
Cons
- When you get started with this tool, you may get intimidated by some extensive functions.
- SaaS integrations need to be improved as often some desirable data elements are missed into JupiterOne.
Customer Rating
- G2- 5/5

Susmita Joseph is a cybersecurity and compliance writer specializing in governance, risk, and regulatory content. She focuses on making complex subjects such as AI governance, cybersecurity compliance, and risk management accessible to growing and mature organizations. With a particular interest in the intersection of AI and GRC, her work explores how emerging technologies are reshaping compliance expectations and security operations.

Team Scrut is a collective of compliance, security, and risk practitioners sharing practical guidance on building audit-ready, scalable programs. We write about SOC 2, ISO 27001, continuous compliance, third-party risk, cloud security, and GRC automation, blending regulatory depth with operator experience to help fast-growing companies strengthen trust, streamline audits, and stay ahead of evolving security demands.

























