Choose risk-first compliance that’s always on, built for you.
Go back to blogs
SOC 2 Type 1 vs SOC 2 Type 2: What's the Difference?
Last updated on
April 14, 2025
min. read

Nowadays, businesses are under pressure to show their commitment to data security and privacy. However, understanding how to assess and verify security controls effectively can be confusing.
This is where SOC 2 reports come in, offering valuable insights into a company's data protection practices. There are two types of SOC 2 reports: Type 1 and Type 2. Many companies struggle to understand the key differences between them, and it can be unclear what each type means for their security posture.
In this blog, we'll explain the differences between SOC 2 Type 1 and Type 2 to help you determine which report best meets your organization's needs.
Overview: SOC 2 Type 1 vs SOC 2 Type 2
What is SOC 2 Type 1?
SOC 2 Type 1 is a framework designed for service organizations to manage and protect customer data. It focuses on five trust service criteria: security, availability, processing integrity, confidentiality, and privacy.
It evaluates whether controls are designed properly at a specific point in time. Licensed CPAs from an accredited firm of the American Institute of Certified Public Accountants (AICPA) issue the report.
The ideal time to get the report is when a company is ready to demonstrate its security and control commitment, typically in the early stages of establishing data security practices.
Although SOC 2 Type 1 reports are not legally required, they are often essential for gaining trust with clients or partners in regulated industries or those handling sensitive data, as they provide assurance regarding the organization's control environment.
How to get SOC 2 Type 1 report?
To get the SOC 2 Type 1 report, the organization must first implement the relevant security and operational controls as outlined by the framework. This often requires an internal audit and documentation to support compliance with the five trust service criteria.
The timeline to get the report typically ranges from 2 to 6 months. This depends on the organization's readiness and the complexity of the systems.
The cost for obtaining a SOC 2 Type 1 report can range from $10,000 to $30,000 or more, depending on the size and complexity of the organization and the scope of the audit.
Who needs the SOC 2 Type 1 report?
SOC 2 Type 1 report is primarily US-based and is increasingly gaining importance in regions outside of the US, especially in areas concerned with data privacy and security. While it is internationally recognized, the European Union prefers ISO 27001 for data security and privacy standards.
However, SOC 2 remains a key requirement for companies in the US and is becoming more significant in other parts of the world, especially within industries offering cloud services, SaaS, and other tech-related solutions.
The SOC 2 Type 1 report is applicable to organizations in industries such as:
- Technology
- Cloud services
- Financial services
- Healthcare
- Other sector that handles sensitive customer data or provides business-to-business services.
SOC 2 Type 1 report is particularly demanded in the following scenarios:
- Initial demonstration of controls: Provides a snapshot of an organization's security controls at a specific point in time, showcasing their practices.
- Building trust with new clients: Serves as a precursor to the SOC 2 Type 2 report, helping establish credibility and trust with potential clients.
- Identifying gaps before going for SOC 2 Type 2: Helps organizations assess their controls and processes to identify gaps before committing to the full Type 2 report.
- Vendor due diligence: Some clients are satisfied with SOC 2 Type 1 as it confirms that basic security and compliance controls are in place.
- Time constraints: When a full SOC 2 Type 2 report isn't feasible within a specific timeframe, SOC 2 Type 1 offers a quicker way to demonstrate compliance.
What are the requirements of the SOC 2 Type 1?
The SOC 2 Type 1 framework outlines 5 Trust Services Criteria (TSCs). Controls are designed based on these TSCs, and the auditor evaluates their effectiveness. Organizations must meet these controls to demonstrate their commitment to protecting customer data and ensuring operational security.
Each SOC 2 Type 1 requirement is designed to ensure comprehensive protection of customer data and operational security across various aspects of the organization.
- Establishment and documentation of security policies and procedures
- Risk assessments and management of information security risks
- System and infrastructure security, including network security
- Availability and reliability of systems and data
- Integrity of processing and controls
- Protection of customer data (confidentiality and privacy)
- Establishing processes for incident response and continuous monitoring
- Third-party vendor risk management
- Regular internal audits to assess control performance
To get the report, organizations must meet all of the requirements outlined in the SOC 2 Type 1 framework.
Advantages of the SOC 2 Type 1
The advantages of the SOC 2 Type 1 framework are:
- Builds trust: Enhances credibility with clients by demonstrating a strong commitment to data security.
- Competitive edge: Increases market advantage in industries requiring stringent data protection, especially when managing sensitive client information.
- Establishes security practices: Improves the organization's security posture by ensuring the effective design of robust policies and controls.
- Regulatory readiness: Enhances the ability to meet industry compliance requirements.
Disadvantages of the SOC 2 Type 1
The disadvantages of the SOC 2 Type 1 framework are as follows:
- Resource-intensive: Obtaining the report requires significant time, effort, and resources, which can be challenging for smaller organizations with limited resources.
- Limited scope: Decreases confidence in long-term control effectiveness, as SOC 2 Type 1 only evaluates control design at a specific point in time, without assessing their ongoing operational performance (which SOC 2 Type 2 covers).
- Short-term focus: Affects the ability to demonstrate sustained security practices, as it does not evaluate controls over an extended period.
What is the SOC 2 Type 2?
SOC 2 Type 2 is a security framework that evaluates the effectiveness of an organization's controls related to the five trust service principles (security, availability, processing integrity, confidentiality, and privacy) over a defined period, typically 6-12 months.
SOC 2 Type 2 assesses how well these controls operate in practice over time, rather than just their design at a specific point in time, as in SOC 2 Type 1. The TSCs in the SOC 2 Type 2 framework were last updated by the AICPA in 2023 to align with evolving industry best practices and technological changes.
The ideal time to obtain a SOC 2 Type 2 report is when an organization has been consistently applying its security practices and is ready to demonstrate that the controls are working effectively over time.
Although a SOC 2 Type 2 report is not a legal requirement, clients or business partners often require it, especially in industries handling sensitive data.
How to get SOC 2 Type 2 report?
To get a SOC 2 Type 2 report, an organization must implement and consistently follow security controls over a defined period. The process of getting the report involves an audit by a licensed CPA firm or agency accredited by the AICPA to assess the effectiveness of the controls across the five trust service principles.
Getting the report typically takes 6 to 12 months, depending on how long the organization has been applying the controls. Costs range from $10,000 to $50,000, depending on the organization's size and complexity.
Who needs the report?
SOC 2 Type 2 reports are widely recognized, particularly in North America, and are becoming increasingly important for businesses in industries that prioritize data security. Their relevance in other regions, such as Europe or Asia, largely depends on the specific requirements of clients.
SOC 2 Type 2 report is commonly required for:
- Companies offering cloud services, SaaS, data storage, or B2B services.
- Technology, finance, healthcare, and legal sectors
- Any company handling sensitive data or serving security-focused clients.
Companies have the flexibility to choose which Trust Services Criteria (Security, Availability, Processing Integrity, Confidentiality, Privacy) to include in their SOC 2 Type 2 audit. This customizable approach ensures that SOC 2 Type 2 is not a "one-size-fits-all" report, allowing businesses to focus on the areas most relevant to their operations and client needs.
What are the requirements of the SOC 2 Type 2?
The SOC 2 Type 2 framework requires you to:
- Implement security policies and procedures
- Perform regular risk assessments and address vulnerabilities
- Ensure the availability and reliability of systems
- Maintain data confidentiality and integrity
- Document incident response and remediation plans
- Perform periodic system monitoring and auditing
- Protect data from unauthorized access or disclosure
- Train employees regularly on security practices
- Establish third-party vendor management controls
- Maintain continuous improvement practices
Advantages of the SOC 2 Type 2
The advantages of the SOC 2 Type 2 framework include:
- Trust and credibility: SOC 2 Type 2 report provides clients with confidence that security controls are working effectively over time, which can help build trust and strengthen client relationships.
- Competitive edge: Having a SOC 2 Type 2 report demonstrates an organization's commitment to data security, making it a strong differentiator in competitive markets.
Disadvantages of the SOC 2 Type 2
The disadvantages of the SOC 2 Type 2 framework include:
- Cost and resource burden: Obtaining and maintaining a SOC 2 Type 2 report can be expensive and resource-intensive, particularly for small to medium-sized businesses.
- Time-consuming process: The audit process can take several months to complete, and continuous monitoring and assessment are necessary to ensure that controls remain effective over time.
Which framework to choose for your company?
SOC 2 Type 1
SOC 2 Type 1 is ideal for organizations looking to demonstrate their commitment to security and compliance at a specific point in time. It focuses on the design and implementation of controls based on the TSCs.
The implementation process involves defining and documenting security policies, setting up necessary controls, and ensuring they align with industry standards. The company then works with an auditor to evaluate the design of these controls and their adherence to the TSCs.
SOC 2 Type 2
SOC 2 Type 2 is suitable for organizations aiming to demonstrate not only the design but also the operational effectiveness of their controls over time. This framework requires continuous monitoring and assessment of controls over a 6-12 month period.
Implementing SOC 2 Type 2 involves establishing robust processes for regular testing, monitoring, and auditing of controls. Organizations will need to demonstrate ongoing compliance and the effectiveness of their controls, ensuring they consistently meet the TSCs. This typically requires significant resources to maintain operational effectiveness and periodic audits.
How can Scrut help to automate the process with SOC 2 Type 1 and SOC 2 Type 2?
Scrut can streamline and automate the entire process of achieving SOC 2 Type 1 and SOC 2 Type 2 reports by providing a set of tools and features specifically designed to help organizations meet the rigorous requirements of both frameworks.
For SOC 2 Type 1, Scrut automates the documentation and evidence-gathering process, making it easier to demonstrate that your controls are properly designed at a specific point in time. The platform helps manage policies, procedures, and security controls, ensuring that all documentation is up to date and ready for audit.
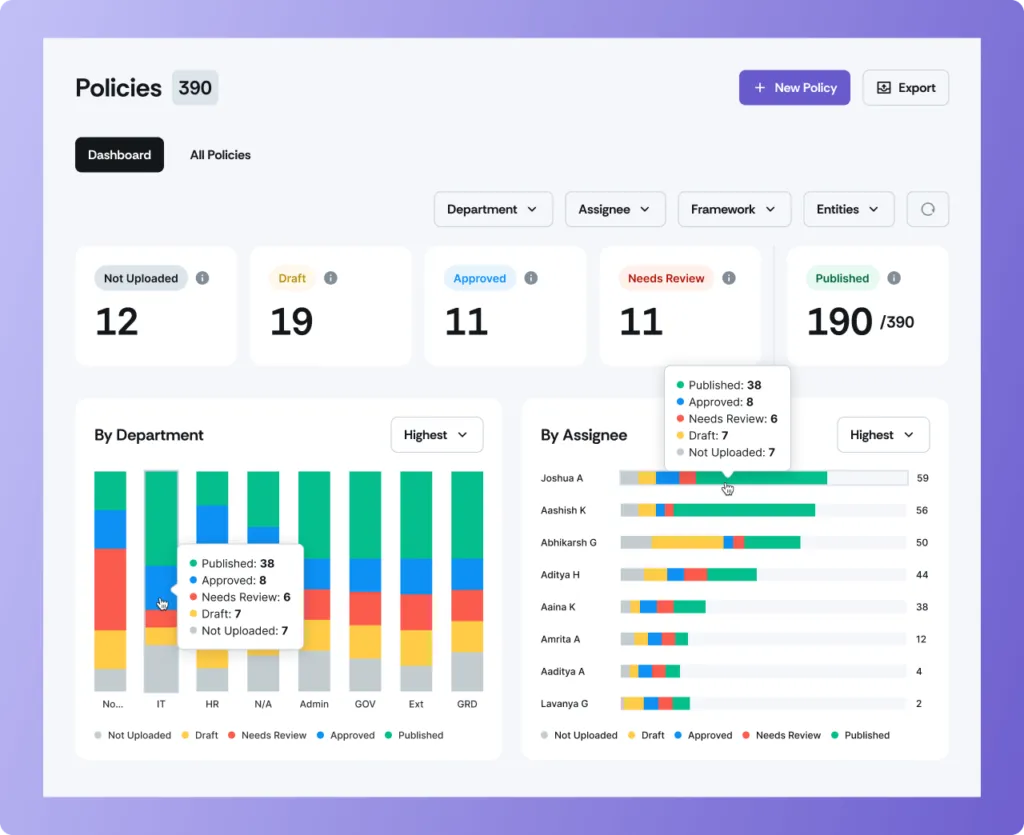
Scrut's policy management feature allows companies to create, track, and update required security policies, ensuring they align with SOC 2's Trust Service Criteria, while real-time monitoring tools ensure that security configurations are maintained.
Scrut's capabilities extend to automating the continuous monitoring and assessment of controls for SOC 2 Type 2, which requires proof of operational effectiveness over a defined period.
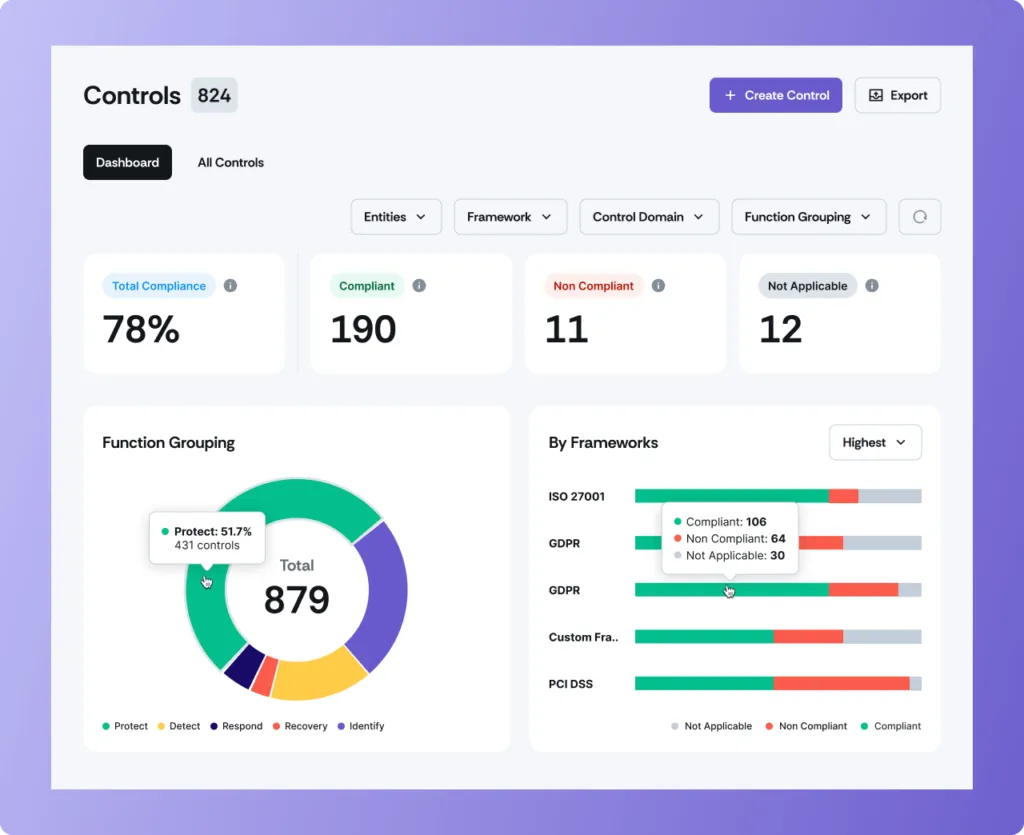
Scrut's platform provides automated compliance tracking and ongoing monitoring of your security posture, ensuring your controls consistently meet SOC 2 requirements over time.
Additionally, Scrut's audit-ready reports and automatic evidence collection ensure that you're always prepared for periodic audits without needing to scramble for documentation at the last minute.
Scrut's audit management tools simplify the entire audit process for both SOC 2 Type 1 and SOC 2 Type 2. They provide an easy-to-use dashboard for tracking progress, assigning tasks, and maintaining all relevant evidence in one place.
Whether you're aiming for a SOC 2 Type 1 report or preparing for a Type 2 audit, Scrut's platform offers the necessary features to automate, manage, and optimize every step, saving time and reducing the risk of non-compliance.
To learn more about how Scrut can assist you in your SOC 2 journey, feel free to get in touch!
FAQs
1. Can I replace SOC 2 Type 1 with SOC 2 Type 2?
SOC 2 Type 1 and SOC 2 Type 2 serve different purposes. SOC 2 Type 1 evaluates control design at a specific time, while SOC 2 Type 2 assesses operational effectiveness over 6-12 months. Typically, organizations first achieve SOC 2 Type 1 and then progress to SOC 2 Type 2.
2. What are the similarities between SOC 2 Type 1 and SOC 2 Type 2?
Both SOC 2 Type 1 and SOC 2 Type 2 are based on the same five Trust Service Criteria: security, availability, processing integrity, confidentiality, and privacy. Both aim to ensure data security and require internal controls, audits, and documentation. The main difference is that Type 1 evaluates controls at a point in time, while Type 2 assesses effectiveness over a period.
Table of contents


















