Scrut is a powerful tool for managing risk within your organization. It provides a comprehensive view of your risk posture, allowing you to easily identify, assess, and mitigate potential information security threats.
With Scrut, you can make informed decisions about the risks you face and take proactive steps to protect your business from potential harm. Let’s understand how.
Risk assessment is a crucial aspect of any business, allowing companies to identify and address potential threats. However, many organizations struggle with risk assessments due to a lack of understanding or limited resources. This can lead to incomplete risk analysis.
To address this issue, enterprises often turn to enterprise risk management systems, which can be cumbersome and complex for mid-market SaaS and fintech startups. That’s where Scrut Risk Management comes in.
Scrut is a solution that aims to provide a simple and effective way for clients to gain greater visibility into their risks, prioritize and manage them effectively, and focus on what truly matters.
Scrut Risk Management Dashboard
Scrut risk management enables organizations to identify, assess and remediate risks, and make their security and compliance posture strong.
Scrut risk management dashboard gives you a glance of the overall risk posture of your organization.

To simplify, Scrut gives you the ability to visualize, quantify, and take strategic decisions based on your risk posture.
There are three steps in creating a risk management plan:
- Risk identification
- Risk assessment
- Risk treatment
Scrut helps you with all of these. Let’s see how.
Risk Identification
Risk refers to any unpredictable event that could disrupt operations or cause loss to the finances or company’s reputation.
The first step in the risk identification process is understanding the scope and nature of your organization’s risks. Based on that, you can work on that risk to reduce its impact. Failing to do so can put your organization in a lot of trouble.
Thus, while implementing a risk plan for the first time, ensure to involve all the stakeholders and then proceed with the risk identification step.
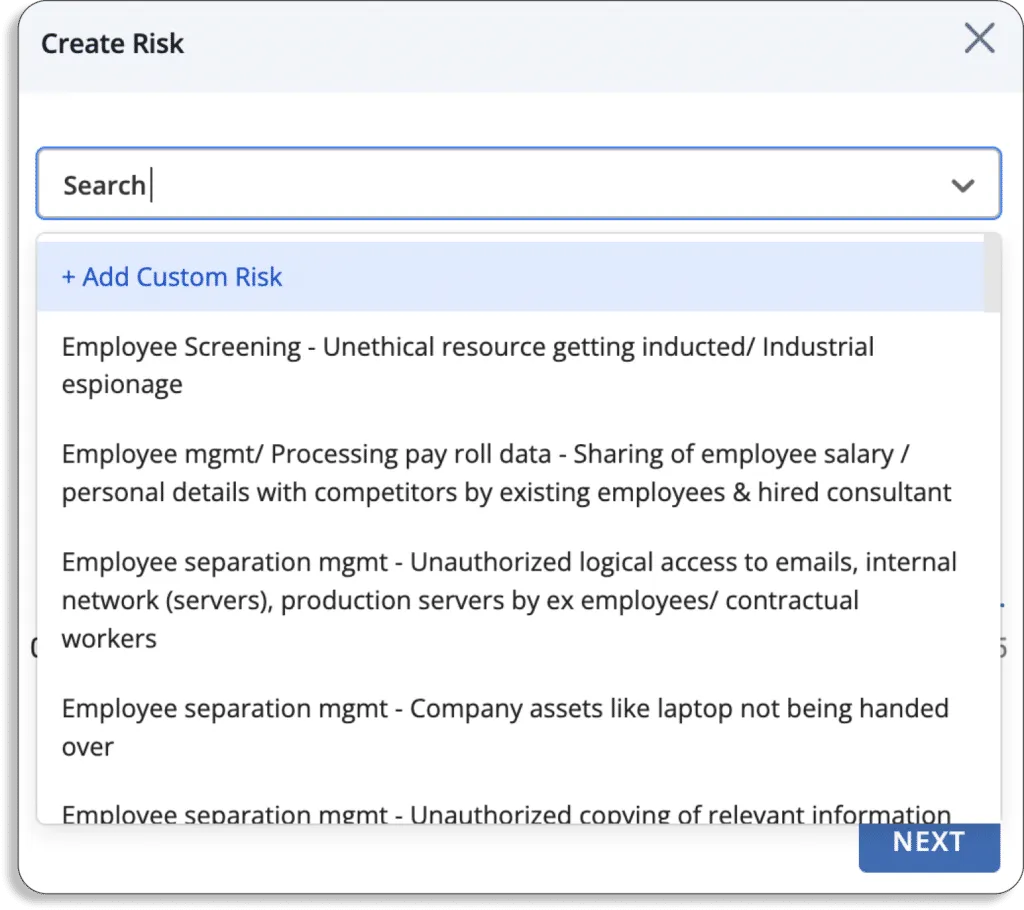
Scrut solves this problem by pre-polulating the most common risks that all business face. This eliminates the blind spot for CISOs.
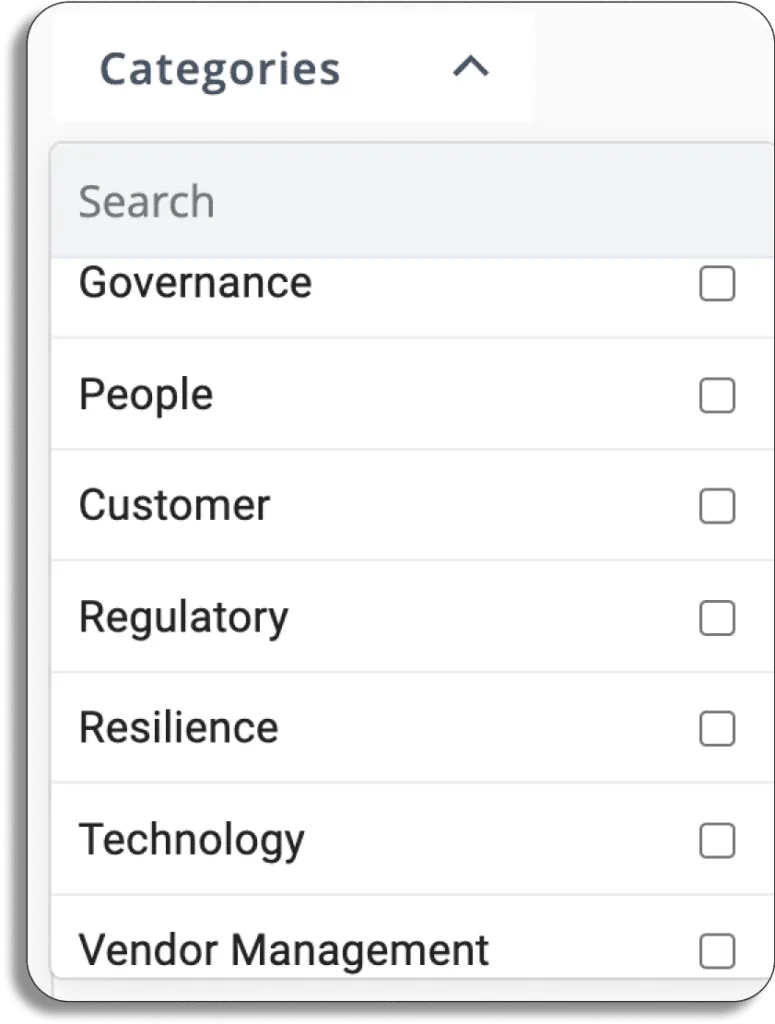
Scrut classifies risks into 7 categories, as shown in the screenshot below.
- Governance
- People
- Customer
- Regulatory
- Resilience
- Technology
- Vendor Management
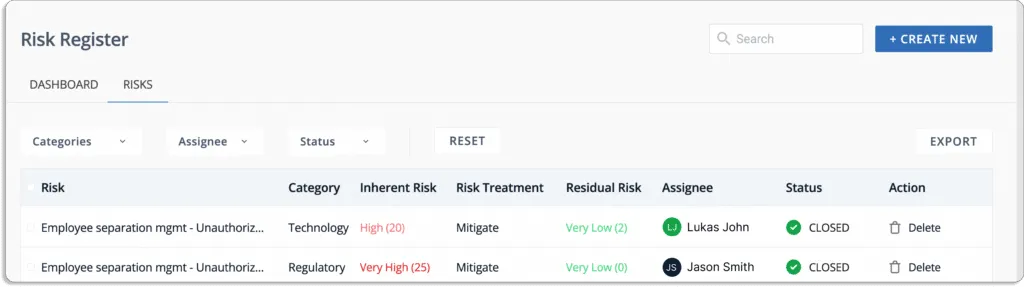
To make your risk register, you first need to list all the risks. You can do it by following the below steps in Scrut:
To start with,
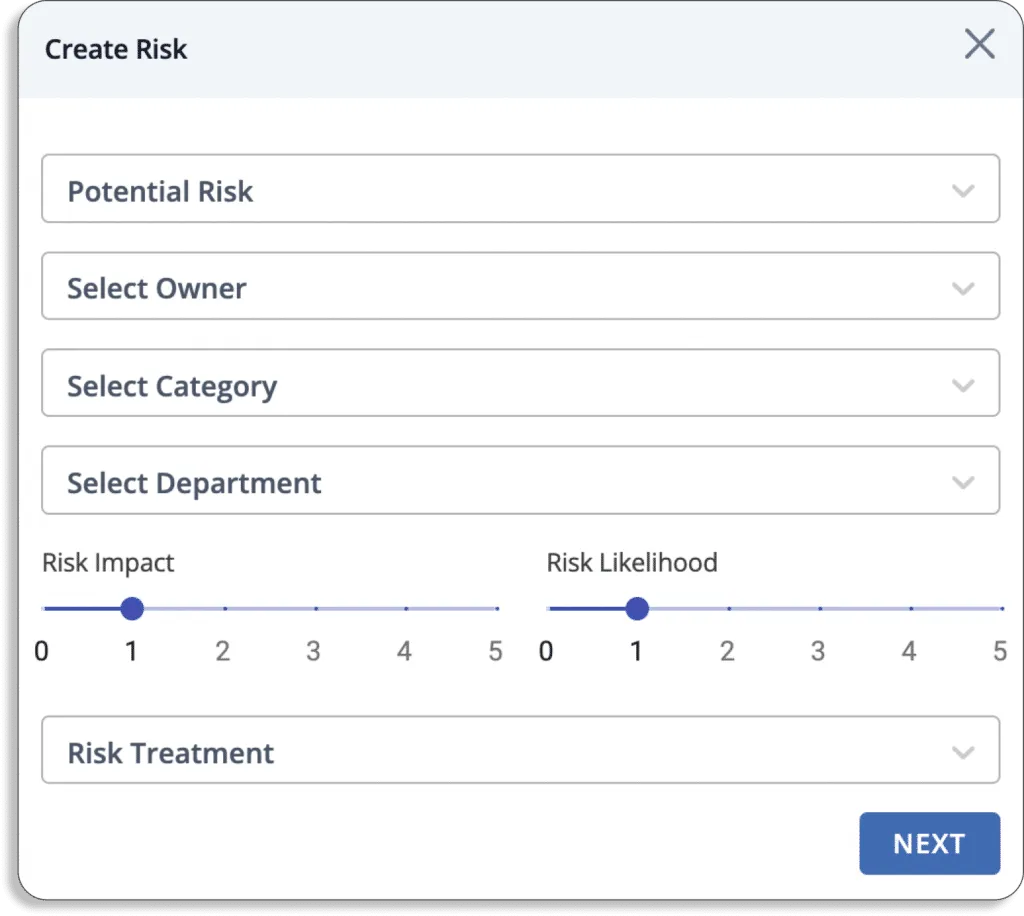
- Click on create new
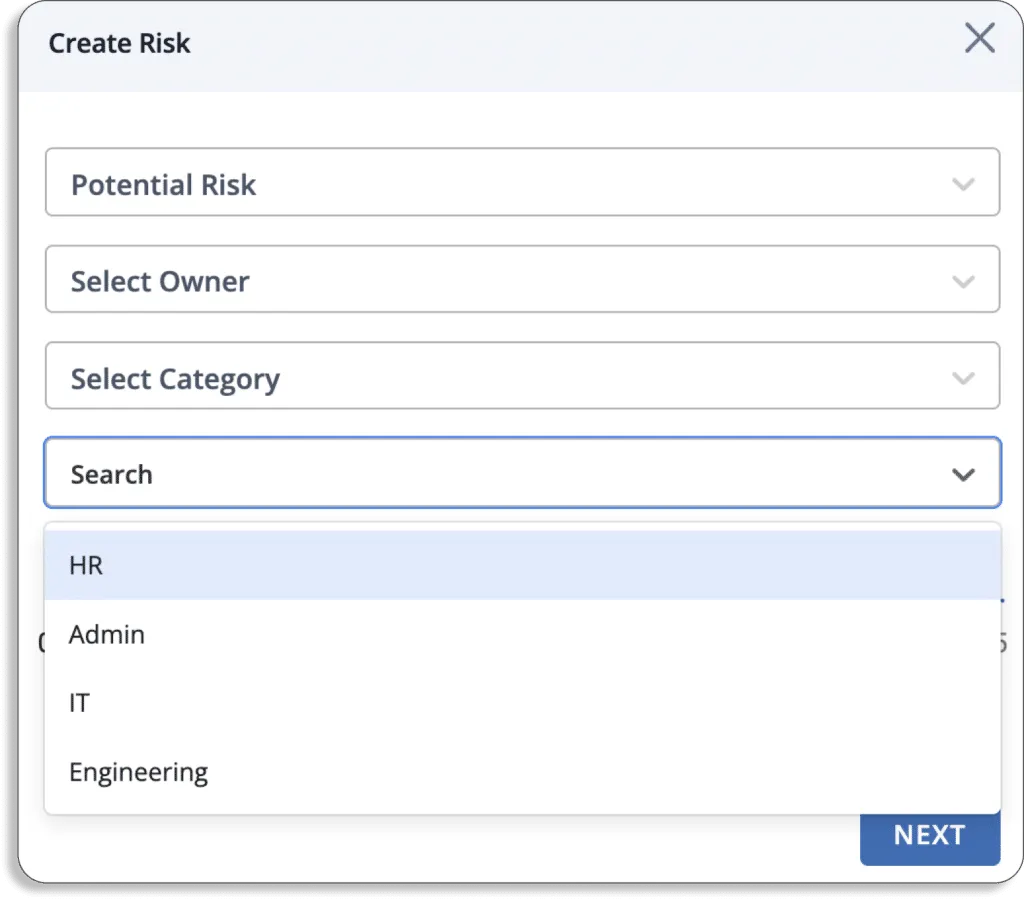
- A pop up like this will appear on your screen:
- You can choose any risks either from our risk library or create your own custom risks.
- For every risk, select the person responsible for keeping track and managing it, select the category from the list we discussed above.
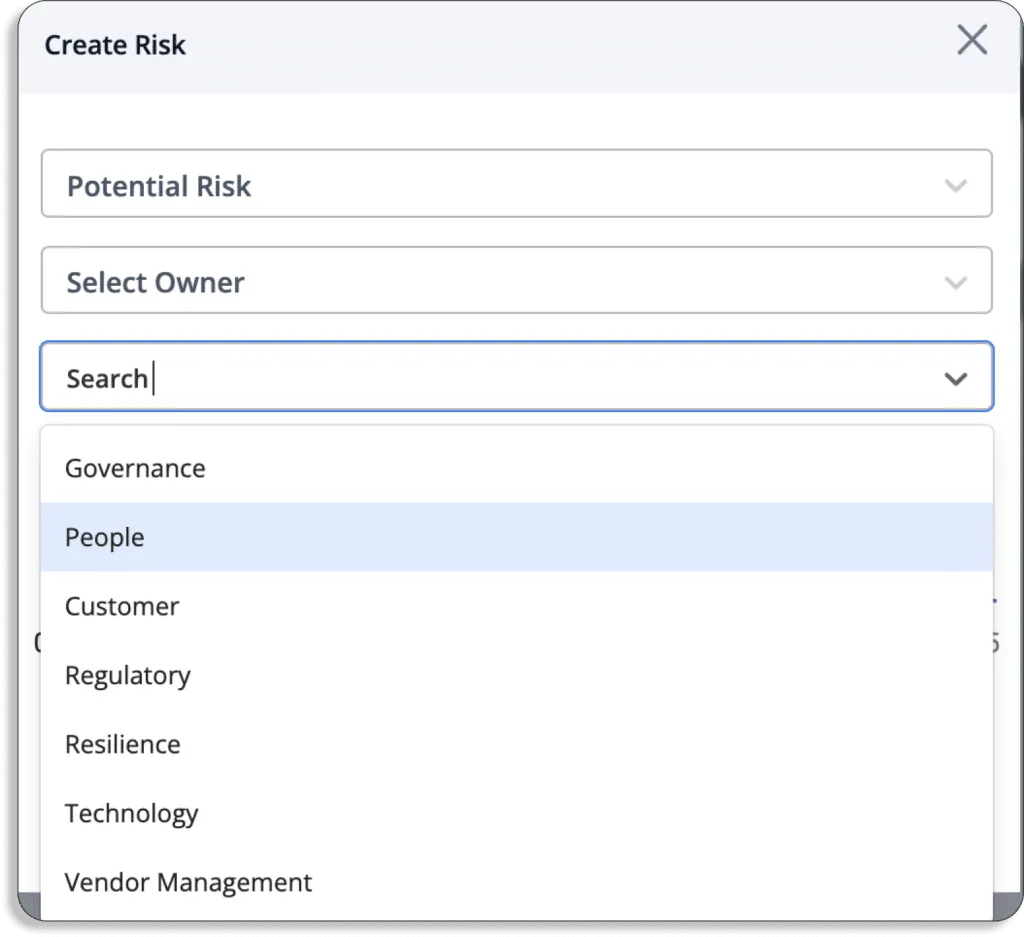
- Afterward, select the department from HR, Admin, IT and Engineering.
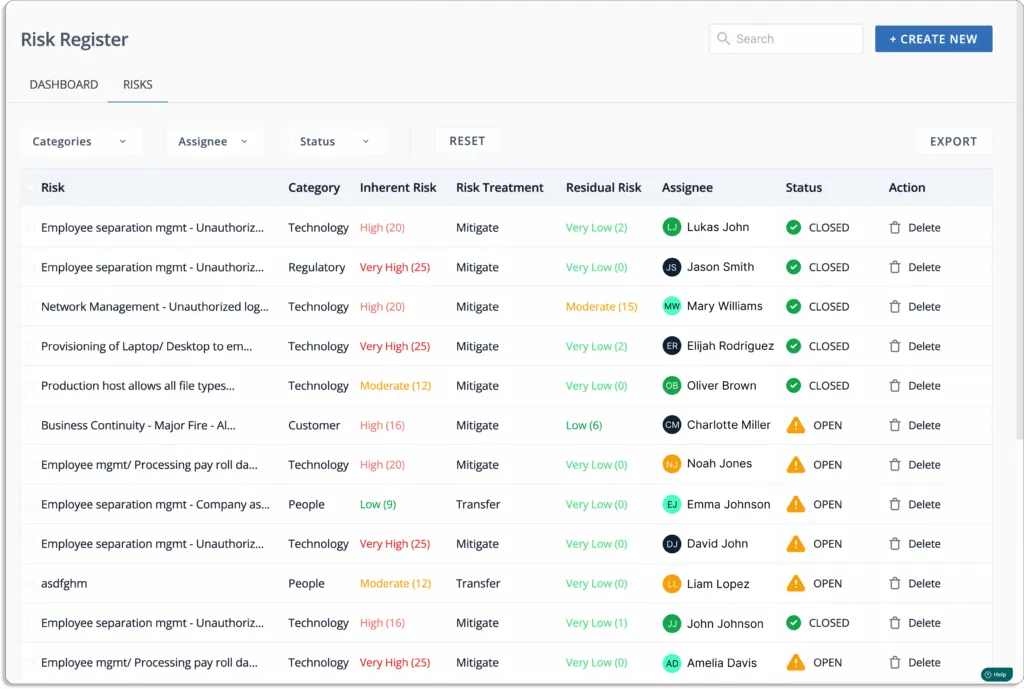
- Lastly, a list of all the associated risks called as Risk register would be displayed.
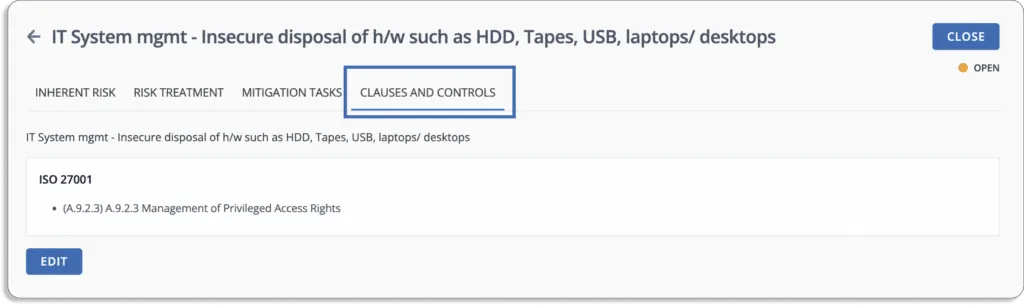
One unique benefit of Scrut is that it automatically maps these risks against different compliance frameworks and their controls, as shown in the screenshot below.
Risk Assessment
Once you have identified the risks associated with your business, the next step is to understand how it affects your organization.
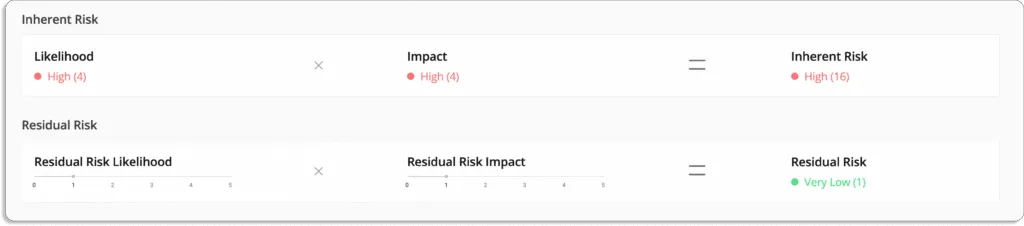
Regular risk assessments are performed to determine which risks should be prioritized. Scrut helps you measure your risk, reliably. The platform creates your risk scoring based on the likelihood and impact of events.
Risk is associated with two events: likelihood that event will take place and its impact in case the risk takes place.
Risk = Likelihood * Impact
- Likelihood: Likelihood is the probability of the event.
- Impact: The amount of damage an event can cause is known as impact.
Let’s take an example of IT system management risk.
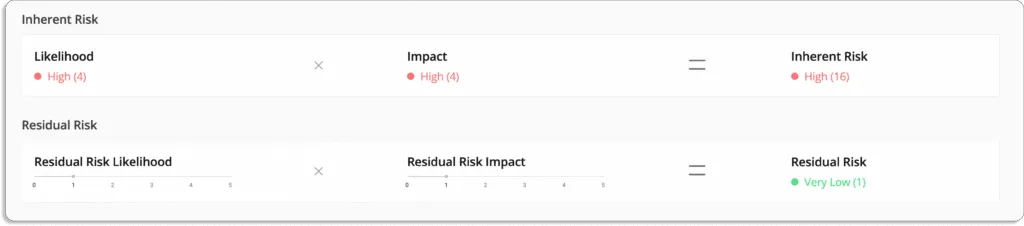
The likelihood of this event is 4 (high)
The impact in case the event occurs is also 4 (high)
Thus, Risk = Likelihood (4) * Impact (4) = 16 (high)
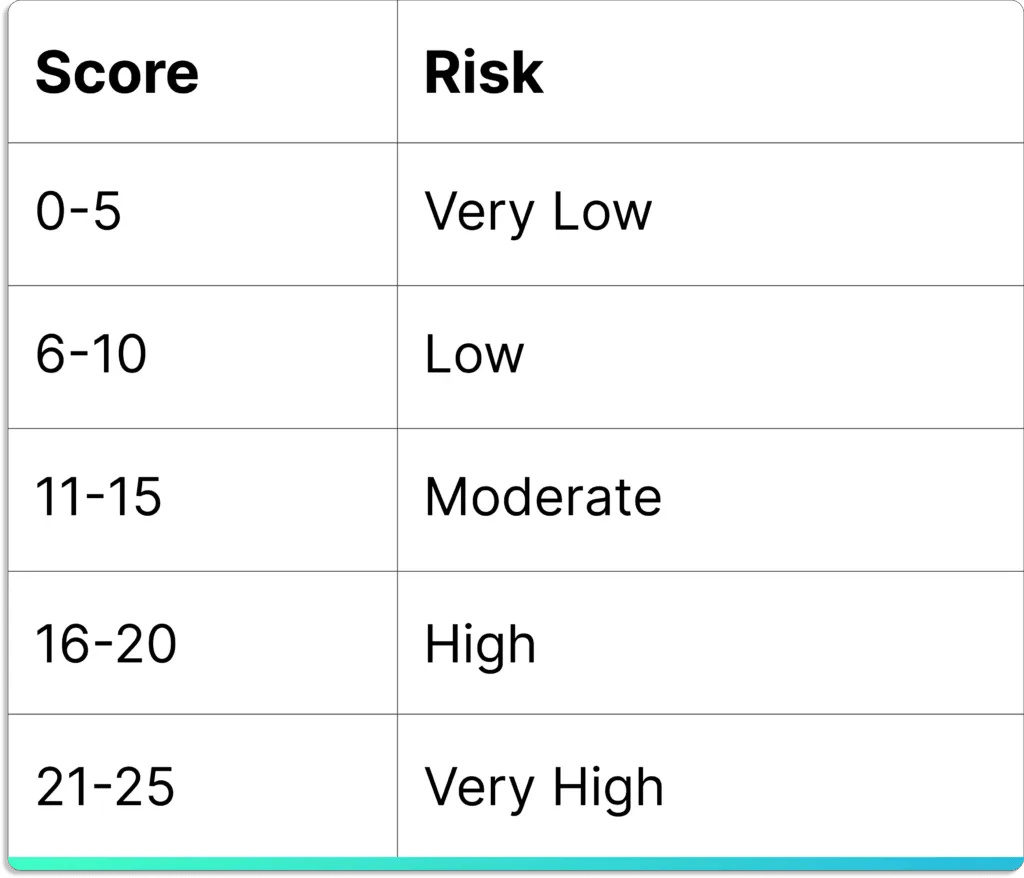
The final risk score always lies between 0 – 25, and you can interpret it as shown in the below table.
Then, you can visualize the output of risk assessment in a heatmap.
A heatmap is a risk matrix in risk management in which risks are ranked based on their potential impact and the likelihood of occurrence.
Scrut’s risk heatmap is the visual overview of your risk profile, as shown in the screenshot below.

With built-in expert-vetted scoring methodologies, you can quantify your risk profile and assess the impact of your treatment plans using inherent and residual scores.
Risk Treatment
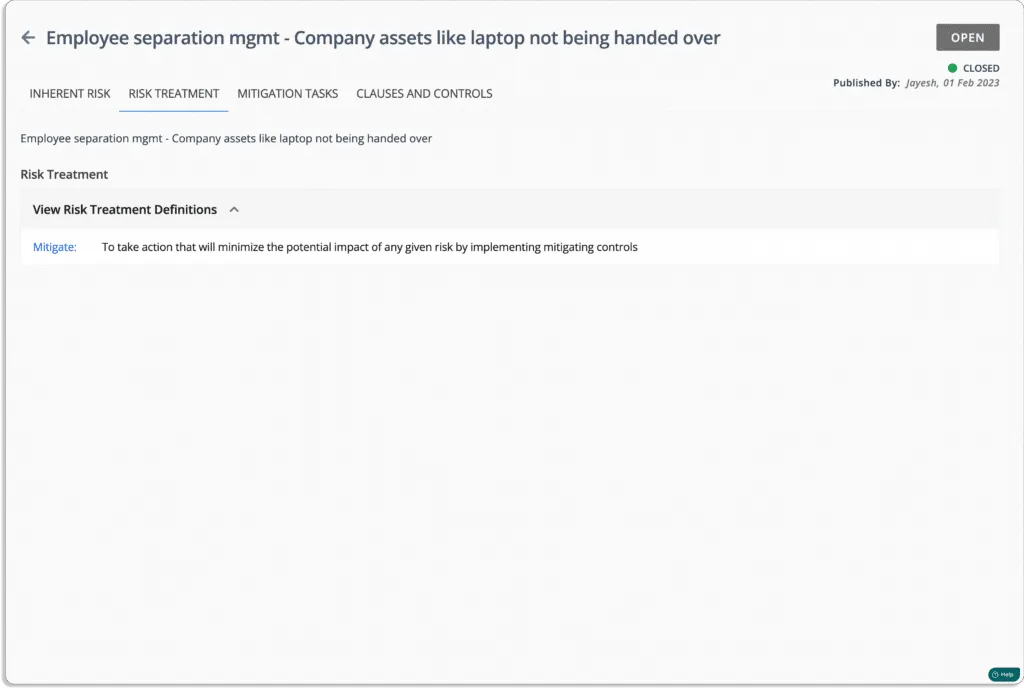
After you’ve completed the risk assessment, the final step is to create a risk treatment plan. A risk treatment recommendation is a set of safeguards or processes that can be implemented to decrease the likelihood, impact, or both of the inherent risks.
Risk treatment entails creating a variety of risk-mitigation options. Then you’ll evaluate those options, devise a plan of attack using your risk management strategy, and begin putting controls in place.
Of course, not all risks are equal; you must concentrate on the most significant ones.
Using the Scrut Risk Management tool, you can free your team from time-consuming manual work.
With Scrut Risk Management platform, you have the following treatment options for every risk —
- Accept – To acknowledge the risk, but decide that any actions to avoid or mitigate the risk can be too costly or time-consuming
- Transfer – To take action by transferring the risk to another entity
- Mitigate – To take action that will minimize the potential impact of any given risk by implementing mitigating controls
- Avoid – To take action that will eliminate the risk in its entirety
Transferring Risk
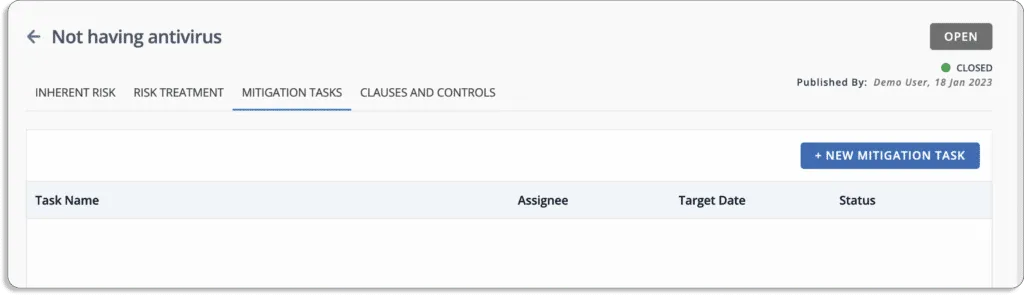
In the example shown above, the risk of not having an antivirus, which could result in the exposure of personal information and the violation of privacy, can be transferred to another entity.
We can transfer ownership of that item to a third party who is better equipped to handle the situation, such as an antivirus product company that will install the antivirus software for us.
Mitigating Risk
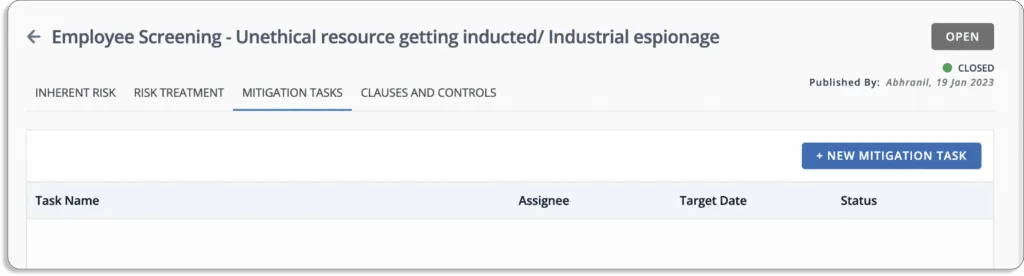
Mitigation measures aim to reduce a threat’s potential damage to manageable levels for the organization. In this case, we implement a background screening program for new employees hired to avoid espionage or employees with an inconsistent profile.
You can now create a task and assign it to the respective security official to implement the background screening program.

Accepting Risk
Accepting the risk is the best strategy if it is financially beneficial than any other option. In the above example, the cost of shipping assets back to the parent location and refurbishing them is high, and storing them in the warehouse is costly. In that case, renting out the used assets could be a good way to manage the risk.
Residual Risk: Risks that Remains Post Treatment
Once the risk has been treated, the residual risk score reflects the effects of risk treatment measures on the risk.
At the most basic level, it is the value obtained from inherent risks after adjusting the impact of risk treatment.
In the example below, the inherent risk score of 20 was reduced to a residual risk score of 4, indicating that this risk has become less impactful.
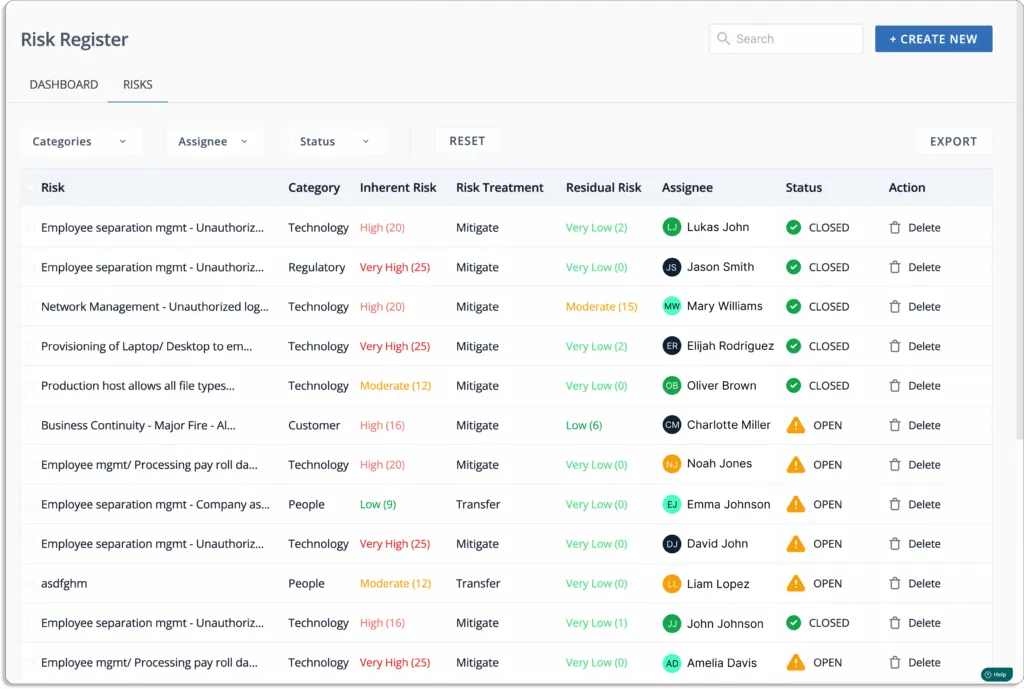
Track Risk in Real Time with Risk Register
Scrut risk management eliminates the need to manage and constantly update your risk register across multiple spreadsheets. It compiles all risks related information and mitigating tasks in a central repository that can be easily shared with auditors for faster compliance audits.

Susmita Joseph is a cybersecurity and compliance writer specializing in governance, risk, and regulatory content. She focuses on making complex subjects such as AI governance, cybersecurity compliance, and risk management accessible to growing and mature organizations. With a particular interest in the intersection of AI and GRC, her work explores how emerging technologies are reshaping compliance expectations and security operations.

Team Scrut is a collective of compliance, security, and risk practitioners sharing practical guidance on building audit-ready, scalable programs. We write about SOC 2, ISO 27001, continuous compliance, third-party risk, cloud security, and GRC automation, blending regulatory depth with operator experience to help fast-growing companies strengthen trust, streamline audits, and stay ahead of evolving security demands.

























