In the dynamic landscape of modern business, where technology and finance intertwine, fintech startups have emerged as trailblazers of innovation. With their disruptive solutions and agile approaches, these startups are reshaping the way we interact with financial services. However, as they ascend on their growth trajectory, an imperative factor looms larger than ever before: fintech cybersecurity.
The fintech sector, by its very nature, deals with sensitive financial data, making it a prime target for malicious actors seeking to exploit vulnerabilities. As these startups transition from serving small businesses to catering to larger enterprises, a fundamental shift occurs in the expectations and demands placed upon them. Herein lies the significance of cultivating an enterprise-friendly information security (infosec) posture.
In this blog, we delve into the pivotal role that cybersecurity plays in the journey of fintech startups, especially as they set their sights on enterprise clients. We will explore the multifaceted benefits of adopting an enterprise-centric approach to infosec and how it becomes a linchpin in not only attracting but also retaining the trust of larger business clients. So, let’s embark on this journey to unravel the strategies and insights that empower fintech startups to fortify their infosec posture for the enterprise realm.
Understanding the landscape
As the fintech organization grows into a large business, it must recognize the challenges and plan solutions to those challenges. The problems faced by large enterprises are quite different from the challenges faced by small and medium enterprises.
A. Recognizing the shift: Startups transitioning to enterprise clients
1. The growth journey from small businesses to larger enterprises.
As fintech startups evolve, they often find themselves traversing a transformative journey from serving local businesses and individual consumers to catering to the intricate needs of larger enterprises. This transition represents more than just a change in client size; it’s a paradigm shift that necessitates a reevaluation of every operational facet, particularly in the realm of fintech cybersecurity.
2. Importance of aligning infosec practices with enterprise requirements.
As startups ascend the business ladder, the spotlight on fintech security concerns intensifies. Enterprises operate within a complex ecosystem where data breaches can have severe ramifications on not only financial stability but also reputation.
Fintech startups seeking to forge partnerships with enterprises must recognize that their clients demand a robust and adaptable infosec framework that aligns seamlessly with the multifaceted security requirements of larger businesses.
B. Enterprise infosec landscape
1. Overview of the heightened security expectations of larger enterprises.
Enterprises, driven by their size, global operations, and substantial digital footprints, harbor heightened fintech security expectations. They require a comprehensive fintech security posture that extends beyond conventional safeguards. This encompasses advanced threat detection, rapid incident response, and stringent access controls, all of which contribute to a fortified defense against modern cyber threats.
2. Highlighting the regulatory and compliance complexities for fintech startups serving enterprise clients.
Navigating the intricate labyrinth of regulations and compliance standards becomes paramount when catering to enterprises. Depending on the industry and geography, fintech startups may encounter a myriad of compliance frameworks such as GDPR, HIPAA, or industry-specific mandates. The ability to adhere to and demonstrate compliance with these standards is not only a legal requirement but also a testament to the startup’s dedication to data protection and security.
In the following sections, we will delve deeper into the strategies and best practices that fintech startups can adopt to create an enterprise-friendly infosec posture, thereby bolstering their credibility and fortifying their partnerships with larger business clients.
Key steps to creating an enterprise-friendly infosec posture for fintech security
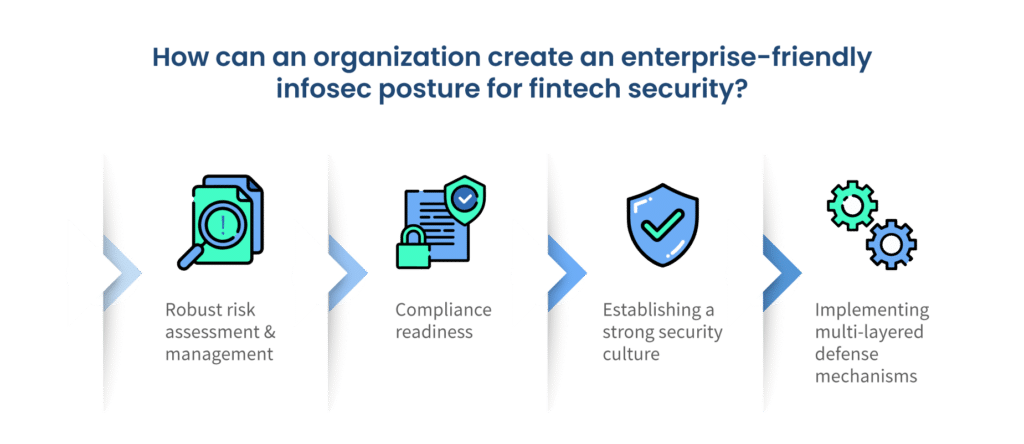
So what should a growing organization do to create a robust fintech cybersecurity posture?
A. Robust risk assessment and management
By aligning risk assessment with tailored risk management strategies, startups can proactively address fintech security vulnerabilities and provide the level of security assurance that enterprise clients expect.
1. Identifying and assessing potential security risks
In the realm of enterprise-friendly infosec, a thorough understanding of potential fintech security risks is paramount. Fintech startups must undertake a meticulous evaluation of their systems, processes, and data flows to uncover vulnerabilities that could be exploited by malicious actors. This involves:
- Asset inventory: Cataloging all digital and physical assets, including hardware, software, and sensitive data, to create a comprehensive overview of the company’s attack surface.
- Threat identification: Recognizing potential threats such as malware, phishing, insider threats, and more that could target your fintech startup.
- Vulnerability assessment: Utilizing scanning tools and penetration testing to pinpoint weaknesses in the infrastructure and applications.
- Impact analysis: Understanding the potential consequences of a security breach, such as data loss, financial losses, legal ramifications, and damage to reputation.
2. Developing a risk management strategy tailored to enterprise needs
Once potential security risks are identified, fintech startups should formulate a risk management strategy tailored to meet the unique security demands of enterprise clients. This strategy involves:
- Risk prioritization: Categorizing risks based on their potential impact and likelihood of occurrence to effectively prioritize mitigation efforts
- Risk mitigation: Implementing countermeasures and controls to reduce identified risks to an acceptable level. This might involve software patching, access controls, and security policies.
- Incident response plan: Creating a detailed plan outlining how the organization will respond to security incidents when they occur, minimizing their impact and facilitating swift recovery
- Continuous monitoring: Implementing real-time monitoring tools to track changes in the threat landscape and identify emerging risks.
B. Compliance readiness
In the intricate landscape of enterprise relationships, compliance readiness stands as a foundational pillar of fintech security posture. Fintech startups must demonstrate a profound grasp of industry-specific regulations and meticulously align their practices to meet the stringent compliance demands of enterprise clients.
1. Understanding industry-specific regulations
Enterprises operate within tightly regulated industries, and compliance with relevant regulations is non-negotiable. Fintech startups must invest time in understanding the intricate web of industry-specific regulations, such as the General Data Protection Regulation (GDPR) for data privacy or the Health Insurance Portability and Accountability Act (HIPAA) for healthcare data. This involves:
- In-depth research: Delving into the specifics of regulations that pertain to the industry or sectors your enterprise clients operate in.
- Legal expertise: Consulting legal professionals well-versed in compliance requirements to ensure accurate interpretation and implementation.
2. Implementing necessary compliance measures
Enterprises entrust their sensitive data to partners who adhere to the highest compliance standards. To forge successful partnerships with larger businesses, fintech startups must not only understand the regulations but also implement robust compliance measures. This includes:
- Data protection: Establishing stringent data protection protocols, including encryption, access controls, and regular data audits.
- Privacy by design: Infusing privacy considerations into product development processes to ensure that data protection is inherent in every stage.
- Documentation: Creating comprehensive documentation detailing compliance measures taken, ensuring transparency and accountability.
- Auditing and reporting: Conducting periodic internal audits to verify compliance and producing reports that demonstrate adherence to regulations.
By demonstrating a comprehensive understanding of industry-specific regulations and meticulously implementing compliance measures, fintech startups solidify their credibility in the eyes of enterprise clients. The subsequent sections will explore strategies to cultivate a fintech security-conscious culture within the organization, a critical aspect of an enterprise-friendly infosec posture.
C. Establishing a strong security culture
In the realm of enterprise-friendly infosec, the significance of fostering a fintech security-conscious culture cannot be overstated. It is the collective commitment of every employee that fortifies the defenses of fintech startups against evolving cyber threats. Here are two key steps to achieve this:
1. Fostering a fintech security-conscious mindset among all employees
The foundation of a strong fintech security culture lies in instilling a shared understanding of the critical role that every team member plays in maintaining information security. This involves:
- Leadership commitment: Leadership should set an example by prioritizing security in their actions and decisions, reinforcing its importance to the entire organization.
- Clear communication: Regularly communicate the significance of security practices and how they align with the organization’s mission and values.
- Ownership and accountability: Encourage employees to take ownership of security in their roles, emphasizing that fintech security is everyone’s responsibility.
- Recognition and rewards: Recognize and reward employees who exemplify exemplary security practices, reinforcing the desired behavior.
2. Conducting regular training sessions to educate the team
Empowering employees with knowledge about fintech security best practices is a cornerstone of an enterprise-friendly infosec posture. Regular training sessions ensure that every team member remains well-informed and equipped to make secure decisions. Consider the following:
- Phishing awareness training: Train employees to recognize phishing attempts and social engineering tactics, as these are common entry points for cyberattacks.
- Data handling and privacy: Educate employees about proper data handling, storage, and disposal procedures to prevent data leaks and breaches.
- Password hygiene: Emphasize the importance of strong, unique passwords and the use of multi-factor authentication.
- Incident reporting: Establish clear channels for reporting security incidents, encouraging a swift response to potential threats.
By fostering a culture where fintech security is ingrained in every aspect of the organization and regularly educating employees about fintech security best practices, fintech startups lay the groundwork for a robust enterprise-friendly infosec posture. The next section will delve into the implementation of multi-layered defense mechanisms, further enhancing the security fabric of the organization.
D. Implementing multi-layered defense mechanisms
In the intricate landscape of enterprise-friendly infosec, a multi-layered defense approach stands as a formidable bulwark against the multifaceted array of cyber threats. Fintech startups must harness advanced technologies and practices to fortify their security posture and safeguard sensitive information.
1. Utilizing advanced authentication methods
The cornerstone of securing access to critical systems and data lies in implementing advanced authentication methods, with multi-factor authentication at the forefront. Here’s how:
- Multi-Factor Authentication (MFA): Require users to provide multiple forms of verification, such as passwords, biometrics, or hardware tokens, before granting access. MFA dramatically reduces the risk of unauthorized access, even if credentials are compromised.
- Biometric authentication: Incorporate biometric identifiers like fingerprints, facial recognition, or iris scans for an additional layer of secure authentication.
2. Employing encryption and data protection techniques
Protecting sensitive data from unauthorized access requires robust encryption and data protection mechanisms. Here’s how to implement them effectively:
- End-to-end encryption: Implement end-to-end encryption for data both in transit and at rest. This ensures that only authorized parties can access and interpret the data, even if intercepted.
- Secure key management: Safeguard encryption keys using secure key management practices to prevent unauthorized access to encrypted data.
- Data masking: Implement data masking to display only limited data to those who don’t require full access, minimizing exposure of sensitive information.
- Tokenization: Replace sensitive data with tokens that retain the data’s format and length but have no exploitable value. This safeguards sensitive data while allowing processes to continue functioning.
By incorporating advanced authentication methods like MFA and employing encryption and data protection techniques, fintech startups create an intricate web of defense layers that substantially reduce the risk of unauthorized access and data breaches.
As we carry forward this blog, we’ll explore how fintech startups can collaborate with enterprise clients to ensure a secure and trust-driven partnership.
Infosec technologies fintech startups must leverage to support enterprise clients
Fintech startups targeting enterprise clients need to deploy a robust set of technologies to meet the complex needs and demands of large businesses. To succeed in the competitive fintech landscape, startups should carefully select and integrate the technologies given below into their business models while also staying attuned to emerging trends and regulatory changes in the financial industry. Collaboration with established technology providers and financial institutions can also be beneficial for fintech startups targeting enterprise clients.
A. Intrusion Detection and Prevention Systems (IDPS)
In the realm of enterprise-friendly infosec, the deployment of Intrusion Detection and Prevention Systems (IDPS) stands as a sentinel guarding the digital fortress. These systems play a pivotal role in proactively identifying and mitigating potential threats, thereby fortifying the fintech security posture of startups. Here’s how IDPS can be harnessed effectively:
1. Proactively identifying and mitigating potential threats
IDPS serve as vigilant guardians, continuously monitoring network traffic, system logs, and other digital footprints to identify anomalous and potentially malicious activities. Key strategies include:
- Signature-based detection: IDPS use known patterns or signatures of attacks to detect and thwart familiar threats, such as malware or common attack vectors.
- Behavioral analysis: By establishing a baseline of normal system behavior, IDPS can identify deviations that might indicate unauthorized access attempts or breaches.
- Anomaly detection: IDPS employ machine learning algorithms to identify patterns that deviate from the norm, signaling potential threats even if they lack a predefined signature.
2. Integrating IDPS into the tech stack for real-time fintech security monitoring
To maximize the efficacy of IDPS, fintech startups should seamlessly integrate these systems into their tech stack, enabling real-time security monitoring and rapid response. Here’s how to achieve this integration:
- Network traffic monitoring: IDPS monitor incoming and outgoing network traffic, scrutinizing data packets for signs of intrusion or unauthorized access attempts.
- Automated response: IDPS can be configured to trigger automated responses upon detection of suspicious activities. This might include blocking certain IP addresses or temporarily isolating compromised systems.
- Integration with SIEM: Integrate IDPS with Security Information and Event Management (SIEM) systems to centralize security event data, enabling comprehensive analysis and efficient incident response.
In the intricate landscape of modern cybersecurity, the integration of IDPS represents a proactive measure that bolsters the defense of fintech startups against a wide spectrum of threats.
B. Security Information and Event Management (SIEM)
In the dynamic realm of enterprise-friendly infosec, SIEM emerges as a central nervous system, orchestrating the collection, analysis, and response to security event data. The integration of SIEM not only elevates the fintech security posture of startups but also enhances their incident response capabilities. Here’s how SIEM can be harnessed effectively:
1. Role of SIEM in centralizing and analyzing fintech security event data
SIEM acts as a sentinel, aggregating data from disparate sources, such as network devices, applications, and logs, into a centralized platform. This centralization facilitates comprehensive analysis and detection of potential threats. Key functions include:
- Log collection and correlation: SIEM gathers logs from various systems and devices, correlating events across the infrastructure to unveil patterns and potential threats that might go unnoticed otherwise.
- Real-time monitoring: SIEM provides real-time insights into security events, enabling swift detection and response to incidents as they unfold.
- Data enrichment: SIEM enhances raw data with contextual information, helping security teams discern the significance of events and prioritize responses effectively.
2. Enhancing incident response capabilities through SIEM integration
The integration of SIEM into the tech stack empowers fintech startups with robust incident response capabilities, allowing them to thwart threats efficiently. Here’s how SIEM elevates incident response:
- Early detection: SIEM’s real-time monitoring enables the early detection of potential security breaches, reducing the dwell time of attackers within the system.
- Automated alerts: SIEM can trigger alerts for suspicious activities, notifying security personnel for swift investigation and mitigation.
- Incident analysis: SIEM aids in post-incident analysis, offering a comprehensive view of the attack timeline, entry points, and affected assets for a more effective response.
- Forensic analysis: SIEM retains historical data, facilitating forensic analysis to understand the full scope of an incident and prevent future occurrences.
By leveraging SIEM’s capabilities to centralize and analyze security event data, fintech startups can proactively detect and respond to threats, thus bolstering the fintech security posture.
C. Cloud security best practices
In the intricate landscape of enterprise-friendly infosec, cloud security emerges as a paramount concern, given the growing reliance on cloud environments for data storage and processing. Implementing robust cloud security practices is imperative for fintech startups aiming to safeguard sensitive information. Here are key strategies to secure data in cloud environments:
1. Strategies for securing data in cloud environments
Cloud environments offer scalability and convenience, but they also introduce new security challenges. Fintech startups must adopt comprehensive strategies to protect data in these dynamic ecosystems:
- Data encryption: Utilize encryption protocols to protect data both at rest and in transit. Encryption ensures that even if unauthorized access occurs, the data remains unreadable without proper decryption keys.
- Identity and Access Management (IAM): Implement stringent IAM practices to control who has access to your cloud resources. Enforce the principle of least privilege, granting only necessary permissions to users and applications.
- Multi-factor authentication: Employ MFA for accessing cloud accounts and services. This additional layer of verification deters unauthorized access, even if credentials are compromised.
- Regular audits and monitoring: Continuously monitor cloud activity and perform regular audits to identify any anomalies or suspicious activities. This proactive approach enables swift response to potential breaches.
2. Emphasizing the importance of choosing reputable cloud service providers
The selection of a cloud service provider profoundly impacts the security of your data. Opting for reputable providers with established security practices can significantly enhance your cloud security posture:
- Security certifications: Choose providers with recognized security certifications, such as ISO 27001 or SOC 2, which demonstrate their commitment to security best practices.
- Data residency: Ensure that the cloud provider’s data centers adhere to compliance requirements relevant to your industry and region.
- Transparent security practices: Look for providers that offer transparency in their security practices, allowing you to understand how they protect your data.
- Data backup and recovery: Evaluate the provider’s data backup and recovery mechanisms to ensure your data’s availability in case of disasters or outages.
By implementing these cloud security best practices and selecting reputable cloud service providers, fintech startups can navigate the complexities of cloud environments while safeguarding sensitive information.
Collaborating with enterprise clients on security
In the intricate realm of enterprise-friendly infosec, collaborative efforts with clients stand as a cornerstone of trust and mutual security. Fintech startups must embrace proactive security collaboration and transparent communication to foster enduring partnerships with larger business clients. Here’s how:
A. Tailored Security Assessments
1. Customizing security assessments to meet enterprise clients’ specific requirements:
Recognizing that each enterprise possesses unique fintech security needs, fintech startups should tailor their security assessments accordingly. This customization demonstrates a keen understanding of the client’s concerns and a commitment to addressing them:
- Risk alignment: Assess security risks in alignment with the client’s industry, regulatory requirements, and specific threats they may face.
- Bespoke solutions: Design security solutions that cater to the client’s infrastructure, operations, and sensitive data types.
- Threat intelligence sharing: Collaborate with the client to exchange threat intelligence and insights that aid in the identification and mitigation of potential risks.
2. Demonstrating a proactive approach to security collaboration:
The willingness to engage in tailored security assessments showcases a proactive approach to security collaboration. This proactive stance not only bolsters your credibility but also fosters a sense of partnership built on mutual security interests:
- Demonstrating due diligence: Highlight the efforts you’ve taken to thoroughly understand the client’s security landscape and adapt your measures accordingly.
- Transparency in process: Clearly communicate the steps you’ll take during the assessment, emphasizing your commitment to delivering a comprehensive evaluation.
B. Transparent Communication
1. Maintaining open channels for security-related discussions with clients
Clear and consistent communication forms the bedrock of a trust-driven partnership. Fintech startups should establish channels for ongoing security-related discussions with clients:
- Regular updates: Keep clients informed about security enhancements, threat trends, and incidents that could impact their operations.
- Timely incident reporting: In the unfortunate event of a security incident, promptly inform clients, detailing the nature of the incident, its impact, and the mitigation measures taken.
2. Sharing relevant security documentation to build trust and transparency
Transparency reinforces trust. Providing clients with relevant security documentation fosters a transparent relationship and demonstrates your commitment to upholding high standards:
- Security policies and procedures: Share your security policies, procedures, and practices to reassure clients about the steps you’re taking to protect their data.
- Compliance documentation: Furnish compliance-related documentation, including audit reports and certifications, to showcase adherence to industry standards.
By embracing tailored security assessments, proactive security collaboration, transparent communication, and information sharing, fintech startups not only elevate their security posture but also build strong, enduring partnerships with enterprise clients. As we conclude this journey through the landscape of an enterprise-friendly infosec posture, it’s evident that the path to success is paved with fintech security, transparency, and collaboration.
Summing up
In the dynamic world of fintech, as startups reshape finance with innovation, fintech cybersecurity emerges as their bedrock. Navigating into enterprise domains demands a robust infosec posture.
We’ve traversed this journey comprehensively: understanding transitions, aligning with enterprise needs, compliance readiness, fostering cultures, and embracing multi-layered defenses like IDPS and SIEM.
From tailored assessments to transparent collaboration, every strategy cements trust with enterprise partners. Security becomes both guardian and enabler, fostering innovation within a secure digital ecosystem.
In closing, fintech’s evolution is intertwined with security. This voyage doesn’t end; it transforms into a commitment to adapt, innovate, and secure. Together, we stride toward a future where fintech doesn’t just disrupt but fortifies, and where every digital transaction thrives on trust.
An enterprise-friendly infosec posture refers to the comprehensive approach that fintech startups adopt to enhance their cybersecurity measures as they transition from serving small businesses to larger enterprises. It encompasses strategies to align with enterprise security requirements, comply with industry regulations, foster a security-conscious culture, implement multi-layered defense mechanisms, collaborate transparently with enterprise clients, and leverage advanced technologies for proactive security.
Fintech startups dealing with sensitive financial data become prime targets for cyber threats. As they scale to serve larger enterprises, the stakes rise significantly. Cybersecurity is essential to protect not only the startups’ reputation and financial stability but also to reassure enterprise clients, who demand robust and adaptable security frameworks to safeguard their sensitive information.
Fostering a security-conscious culture involves instilling a collective understanding of the importance of information security among all employees. This includes leadership commitment, clear communication, employee training, and promoting ownership and accountability. A strong security culture enhances an organization’s defenses by encouraging employees to actively contribute to cybersecurity measures.

Megha Thakkar is a technical content writer with about a decade of experience in cybersecurity and compliance. She writes extensively on SOC 2, ISO 27001, GDPR, and security operations, helping organizations translate complex requirements into clear, audit-ready decisions. Her work, tailored for CISOs and executive leaders, is frequently cited in U.S. government and NIST publications.

Team Scrut is a collective of compliance, security, and risk practitioners sharing practical guidance on building audit-ready, scalable programs. We write about SOC 2, ISO 27001, continuous compliance, third-party risk, cloud security, and GRC automation, blending regulatory depth with operator experience to help fast-growing companies strengthen trust, streamline audits, and stay ahead of evolving security demands.

























