Traditional risk management is primarily focused on identifying, assessing, and mitigating risks associated with the financial, operational, and strategic aspects of an organization. It typically involves methods such as risk registers, qualitative assessments, and financial modeling to manage uncertainties in these areas.
While this approach has proven effective for many years, the emergence of the digital age and increasing reliance on technology have introduced a new dimension of risk: cyber risk.
Cyber threats have become a pervasive and highly dynamic risk that organizations must confront. Traditional risk management methods often fall short when it comes to addressing cyber risks due to their evolving nature and potentially catastrophic consequences.
As a result, there is a growing need for a shift towards cyber risk quantification, which involves the precise measurement and assessment of cyber risks in a quantifiable manner.
In this article, we will see how your organization can transition from traditional risk management methods to a more modern cyber risk quantification.
II. So, what does traditional risk management mean?
Traditional risk management is typically guided by the following principles:
- Risk identification: The process begins with the identification of potential risks, which can include financial risks, operational risks, strategic risks, and compliance risks. Organizations aim to create a comprehensive list of potential threats and vulnerabilities.
- Risk assessment: Once risks are identified, they are assessed in terms of their likelihood and potential impact on the organization. This assessment is often conducted using qualitative methods, such as risk matrices, and quantitative methods, such as financial modeling.
- Risk mitigation: Organizations develop strategies and action plans to mitigate identified risks. These strategies may involve risk avoidance, risk reduction, risk transfer (e.g., through insurance), or risk acceptance.
- Monitoring and review: Continuous monitoring and periodic review of risk management strategies are essential to adapt to changing circumstances and evolving risks.
Limitations and challenges in traditional risk management
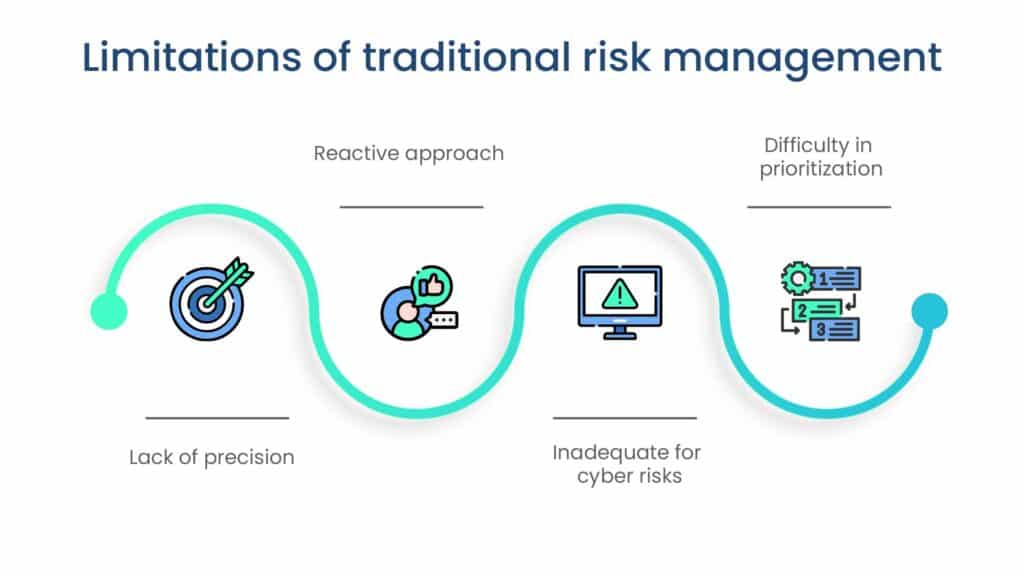
Traditional risk management, while effective for many types of risks, has several limitations and challenges:
- Lack of precision: Qualitative assessments used in traditional risk management are subjective and lack precision, making it challenging to quantify and compare risks accurately.
- Reactive approach: Traditional risk management is often reactive, addressing risks after they have materialized. This can lead to delayed responses and increased damage in case of unforeseen events.
- Inadequate for cyber risks: Traditional methods are ill-suited to the rapidly evolving and highly technical nature of cyber risks. They often fail to provide real-time or predictive insights into cybersecurity threats.
- Difficulty in prioritization: Traditional risk management may not effectively prioritize risks, leaving organizations uncertain about where to allocate resources most efficiently.
How traditional risk management falls short in addressing cyber risks

Traditional risk management faces significant challenges when it comes to addressing cyber risks.
- Lack of technical expertise: Traditional risk management practitioners often lack the technical expertise required to understand the complexities of cyber threats, vulnerabilities, and attack vectors. This knowledge gap can hinder accurate risk assessment and mitigation.
- Inadequate response time: Cyber threats can escalate rapidly, and traditional risk management’s reactive approach may not provide organizations with the agility needed to respond in real-time, leaving them vulnerable to cyberattacks.
- Insufficient data and metrics: Traditional risk management relies on historical data and may not have access to the real-time threat intelligence needed to assess cyber risks effectively. This can lead to underestimating the evolving cyber threat landscape.
- Complex regulatory environment: Cybersecurity regulations and compliance requirements are continuously evolving. Traditional risk management may struggle to keep up with the ever-changing legal and regulatory landscape, potentially leading to non-compliance and legal issues.
III. The concept of cyber risk quantification
Unlike traditional risk management, which relies on subjective assessments and qualitative methods, cyber risk quantification leverages quantitative models and metrics to provide a more accurate and objective understanding of an organization’s cyber risk exposure.
Benefits of adopting a quantified approach to cyber risk
Adopting a quantified approach to cyber risk offers several advantages for organizations:
- Improved decision-making: Cyber risk quantification provides decision-makers with objective data and metrics to prioritize cybersecurity efforts effectively. This enables informed decision-making regarding resource allocation and risk mitigation strategies.
- Resource efficiency: Organizations can allocate resources more efficiently by focusing on addressing high-impact, high-probability cyber risks, thereby optimizing cybersecurity investments.
- Strategic stakeholder communication: Quantified cyber risk data is easier to communicate to stakeholders, including executive leadership, boards of directors, insurers, and regulatory bodies. It enhances transparency and facilitates meaningful discussions about cybersecurity priorities.
- Enhanced cyber resilience: By identifying and quantifying cyber risks proactively, organizations can strengthen their cybersecurity posture and resilience against potential threats.
IV. Key steps in transitioning to cyber risk quantification
A. Assess current risk management practices
Transitioning to cyber risk quantification involves several key steps, starting with assessing current risk management practices. This includes evaluating traditional methods like qualitative risk assessments, identifying gaps such as lack of focus on cyber threats, and reviewing cybersecurity policies.
Organizations must engage stakeholders, benchmark against standards like ISO 27001 or NIST Cybersecurity Framework, and document findings. This lays the foundation for effective transition and enhancement of cyber risk management strategies.
B. Develop a cyber risk management strategy
Developing a strong cyber risk management strategy is vital for organizations moving towards cyber risk quantification. This involves defining clear objectives, prioritizing efforts based on organizational priorities, and creating a comprehensive strategy aligned with broader business continuity plans.
Emphasizing communication, ongoing monitoring, and fostering a culture of continuous improvement are also crucial. By doing so, organizations can effectively transition to cyber risk quantification while adapting to evolving threats and organizational changes.
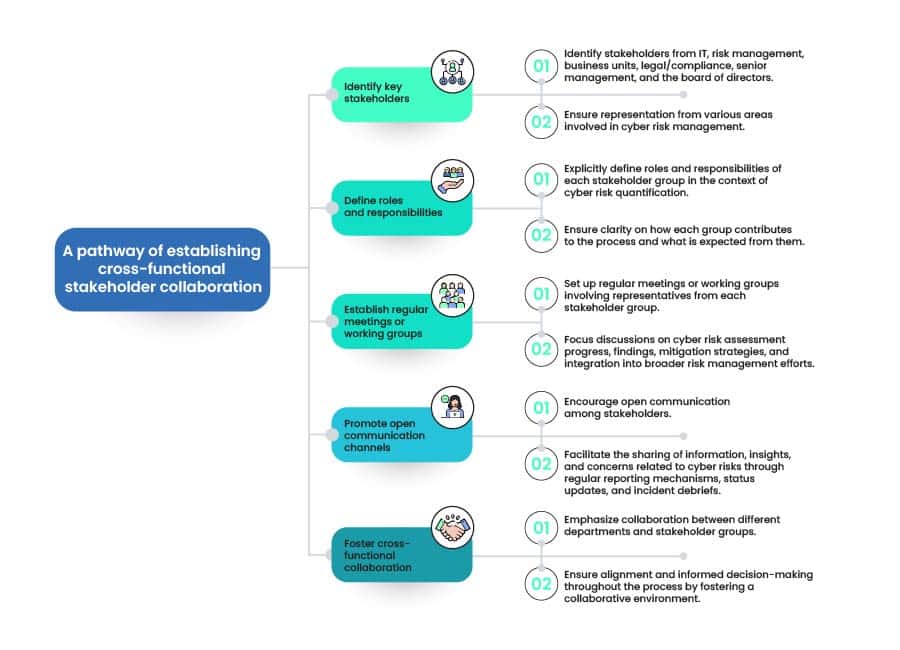
C. Establish cross-functional stakeholder collaboration
Establishing cross-functional stakeholder collaboration is crucial in transitioning from conventional risk management to cyber risk quantification because it facilitates communication, enables better risk mitigation strategies, and increases the likelihood of a sustainable transition.
D. Educate and train employees
Educating and training employees is a crucial aspect of effective cyber risk management. It helps create a cybersecurity-conscious culture and empowers individuals within the organization to contribute to the overall security efforts.
Here are the key steps to educate and train employees effectively:

E. Select appropriate cyber risk quantification framework
Selecting an appropriate cyber risk quantification framework is a critical step in enhancing your organization’s cybersecurity efforts. The process involves two key steps.
Firstly, you need to conduct thorough research and choose a framework that aligns with your organization’s goals and requirements. Options to consider include FAIR (Factor Analysis of Information Risk) or OCTAVE (Operationally Critical Threat, Asset, and Vulnerability Evaluation).
Secondly, after selecting a framework, it’s crucial to customize it to suit your organization’s specific needs and risk landscape. This customization should take into account factors such as industry-specific risks, the unique structure of your organization, and compliance requirements.
By tailoring the chosen framework, you can ensure that it effectively addresses your organization’s cybersecurity challenges and provides valuable insights for risk management.
F. Conduct a cyber risk assessment
Conducting a thorough cyber risk assessment is imperative for organizations to grasp and address cyber risks effectively. The process involves several key steps, beginning with the identification and prioritization of cyber risks.
After selecting an appropriate cyber risk quantification framework, such as FAIR or OCTAVE, and proceed with data collection, risk modeling, scenario analysis, sensitivity analysis, and factoring in mitigation costs. Generating comprehensive reports detailing quantified cyber risks, including monetary values, is crucial for informing key stakeholders and facilitating informed decision-making and resource allocation.
By systematically identifying, prioritizing, and quantifying cyber risks through a structured assessment process, organizations can better understand their cyber risk landscape and make informed decisions regarding risk mitigation strategies. Adhering to established frameworks and methodologies ensures consistency and reliability in risk quantification, enabling organizations to effectively allocate resources and prioritize risk management efforts to safeguard against potential cyber threats.
G. Integrate cyber risk quantification into the ERM framework
Integrating cyber risk quantification into Enterprise Risk Management (ERM) involves evaluating the current framework, identifying overlaps between cyber risks and other categories, and seamlessly integrating cyber risk management into the overarching strategy.
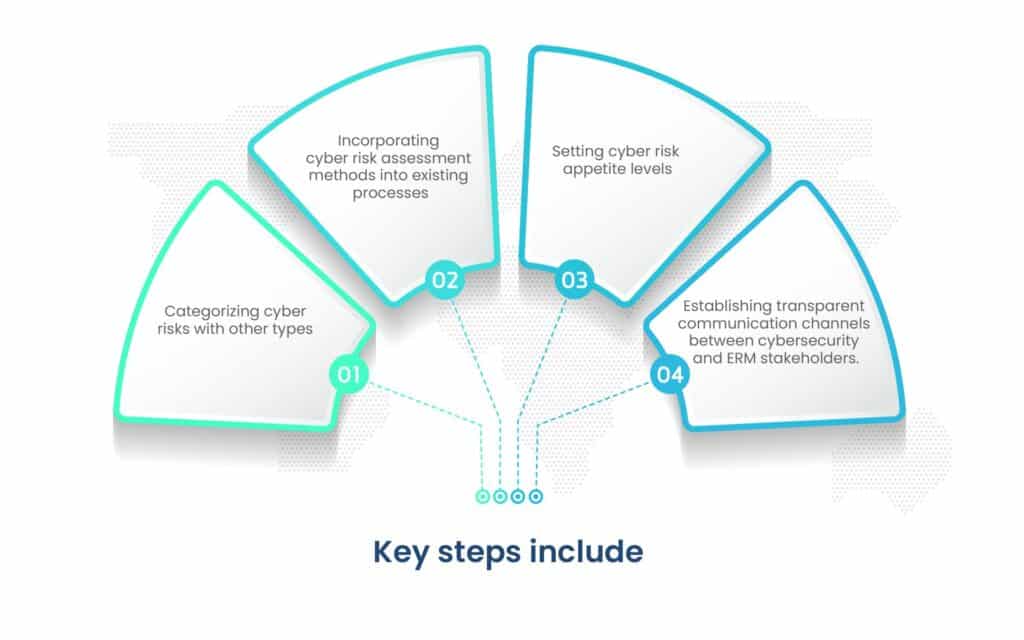
Efficient resource allocation ensures cybersecurity initiatives are well-funded and aligned with broader risk mitigation efforts. Continuous monitoring, scenario analysis, and regular updates maintain the integration’s effectiveness against evolving threats.
Ongoing assessment and collaboration between cybersecurity teams and ERM stakeholders are essential for accurate risk evaluations. This iterative approach ensures adaptability to emerging threats and changes in the risk landscape, ultimately strengthening overall risk management strategies.
H. Develop response and mitigation strategies
Developing robust response and mitigation strategies for cyber risks is imperative for organizations to minimize the potential impact of threats effectively.
Firstly, establishing response plans involves creating a comprehensive incident response plan with clearly defined roles, a communication plan for both internal and external stakeholders, and ensuring compliance with legal and regulatory requirements.
Moving on to mitigation strategies, prioritization based on cyber risk assessments is key, focusing on addressing high-impact risks first.

Additionally, testing and evaluation through penetration testing, tabletop exercises, and continuous improvement initiatives are crucial for refining response and mitigation strategies over time. Adequate resource allocation, including budget and skilled personnel, is essential to support the implementation and maintenance of these strategies effectively.
I. Monitor, review, and update
Continuous monitoring is a foundational aspect of effective cybersecurity management, involving real-time tracking of cybersecurity metrics, detection of threats, and adherence to security controls.
By promptly identifying anomalies and staying informed about emerging cyber threats through monitoring various intelligence sources, organizations can adapt their strategies effectively.
Additionally, maintaining detailed incident logs enables organizations to learn from past experiences, refine incident response plans, and continuously enhance their cybersecurity posture.
Furthermore, reviewing the performance of cybersecurity controls and response processes helps identify strengths and weaknesses, facilitating enhancements and adjustments to strengthen overall cybersecurity defenses.
Conclusion
In conclusion, the benefits of cyber risk quantification are significant and compelling. This approach offers organizations a more precise and data-driven means of understanding their cyber risk landscape, enabling them to make informed decisions and allocate resources effectively. By transitioning to cyber risk quantification, organizations can reap the benefits of cyber risk quantification.
In this era of escalating cyber threats, organizations must adapt and evolve their risk management practices. Cyber risk quantification provides the tools and insights needed to navigate the complex and ever-changing landscape of cyber threats effectively. By embracing this approach and leveraging the expertise of cybersecurity and compliance professionals, organizations can fortify their defenses and safeguard their future in an increasingly digital world.
Prioritize risks, implement security controls, conduct employee training, and regularly test and refine your strategies to minimize cyber threats.
Prepare clear and concise reports, translate technical details into business terms, and maintain open communication channels with stakeholders.
The goal is to enhance your organization’s cybersecurity posture by measuring, managing, and mitigating cyber risks effectively, ultimately reducing the financial impact of cyber incidents.

Megha Thakkar is a technical content writer with about a decade of experience in cybersecurity and compliance. She writes extensively on SOC 2, ISO 27001, GDPR, and security operations, helping organizations translate complex requirements into clear, audit-ready decisions. Her work, tailored for CISOs and executive leaders, is frequently cited in U.S. government and NIST publications.

Team Scrut is a collective of compliance, security, and risk practitioners sharing practical guidance on building audit-ready, scalable programs. We write about SOC 2, ISO 27001, continuous compliance, third-party risk, cloud security, and GRC automation, blending regulatory depth with operator experience to help fast-growing companies strengthen trust, streamline audits, and stay ahead of evolving security demands.

























