Cloud security posture management (CSPM) helps organizations detect misconfigurations, monitor compliance, and secure AWS, Azure, and GCP environments. As cloud adoption grows, CSPM has become critical for maintaining visibility and reducing cloud security risks across multi-cloud infrastructure.
Cloud platforms offer flexibility, scalability, and cost savings, but misconfigurations remain one of the leading causes of cloud security incidents. For CISOs, DevSecOps, SaaS, and compliance teams, CSPM solutions provide continuous monitoring, risk detection, and compliance visibility.
This blog covers what CSPM is, how it works, its key benefits and capabilities, how it compares to other cloud security tools, and what to look for in a CSPM solution.
What is CSPM?
CSPM is a cloud security solution that continuously monitors cloud environments for misconfigurations, security risks, and compliance gaps. It provides centralized visibility across AWS, Azure, and GCP, helping organizations enforce security policies, maintain compliance, and reduce cloud exposure. CSPM tools are widely used by security, DevSecOps, and compliance teams to strengthen cloud security posture.
So what is a CSPM in practice?
A CSPM platform automatically scans cloud infrastructure and services to detect issues such as publicly exposed storage, excessive permissions, disabled logging, or non-compliant configurations. It continuously monitors multi-cloud environments and helps teams prioritize and remediate risks before they lead to security incidents or compliance failures.
CSPM at a glance
| Category | Details |
|---|---|
| Full Form | Cloud Security Posture Management |
| Purpose | Detect and remediate cloud misconfigurations and compliance risks |
| Coverage | IaaS, PaaS, and limited SaaS visibility |
| Providers | AWS, Azure, Google Cloud |
| Deployment model | Primarily agentless SaaS deployment |
| Compliance frameworks | SOC 2, ISO 27001, GDPR, PCI DSS |
| Core capabilities | Continuous monitoring, risk prioritization, and compliance checks |
| Key value | Improved cloud visibility and infrastructure security |
How does CSPM work?
Cloud security posture management works by continuously monitoring cloud environments for security risks, misconfigurations, and compliance gaps across IaaS, PaaS, and SaaS services. CSPM tools provide centralized visibility into cloud assets, compare configurations against security best practices and compliance frameworks, and help teams remediate risks before they lead to incidents.
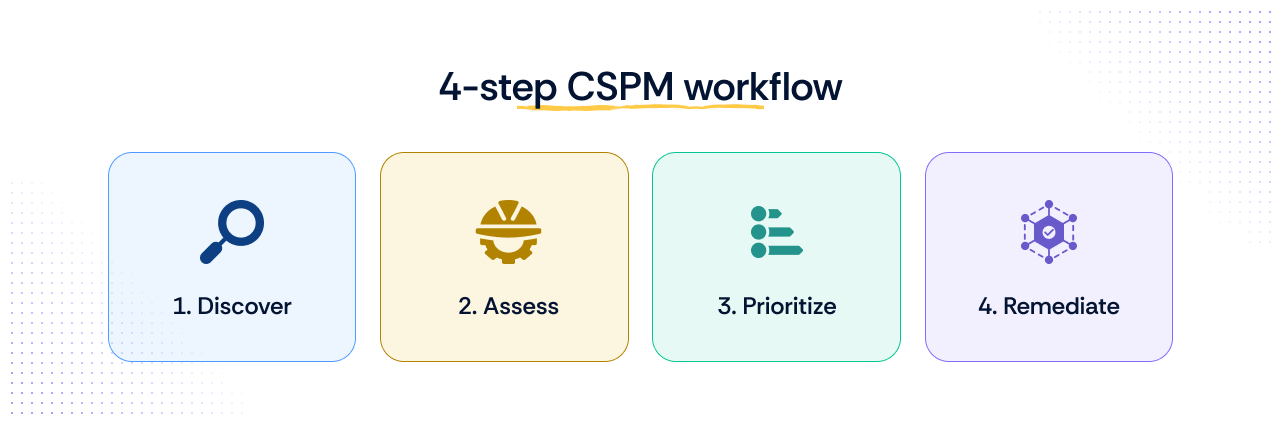
Most CSPM platforms follow a four-step workflow:
- Discover
Connect cloud environments such as AWS, Azure, and Google Cloud to identify assets, configurations, identities, and exposed services across the infrastructure. - Assess
Continuously scan cloud resources for misconfigurations, excessive permissions, exposed storage, disabled logging, and compliance violations. CSPM tools also map controls to frameworks such as GDPR, SOC 2, and ISO 27001. - Prioritize
Analyze risks based on severity, exposure, and business impact so security teams can focus on the most critical issues first. - Remediate
Create and track remediation tasks, automate fixes where possible, and continuously monitor environments to ensure issues remain resolved.
Platforms such as Scrut simplify this workflow through agentless integrations, continuous monitoring, compliance mapping, and remediation tracking. CSPM tools also integrate with DevSecOps and security platforms to support faster risk detection and stronger cloud governance.
Why is CSPM important?
Cloud environments are more dynamic and decentralized than traditional on-prem infrastructure, making security visibility much harder to maintain. Teams constantly deploy new services and configurations across AWS, Azure, and Google Cloud, increasing complexity and the risk of security gaps.
Misconfigurations are now one of the leading causes of cloud security incidents. Publicly exposed storage, excessive permissions, disabled logging, and unpatched systems can all leave sensitive data vulnerable.
According to a report by Snyk, cloud misconfigurations contribute to nearly 45% of cloud-related breaches. The Capital One data breach is one of the most well-known examples, where a cloud configuration weakness contributed to the exposure of sensitive customer data.
Since completely eliminating misconfigurations is difficult, organizations rely on CSPM solutions to continuously monitor cloud environments, detect risks, and improve cloud security posture before issues escalate.
The role of CSPM in preventing misconfigurations
Cloud security posture management helps organizations reduce cloud risk by continuously identifying and correcting security gaps across cloud environments.
Key ways CSPM helps prevent misconfigurations include:
- Detection of security gaps
Continuously scans cloud environments to identify issues such as exposed storage, weak access controls, open ports, and disabled logging. - Security policy enforcement
Ensures cloud resources follow approved security and compliance policies across AWS, Azure, and Google Cloud. - Automation of security tasks
Automates activities such as vulnerability scanning, configuration checks, and remediation workflows to reduce manual effort and human error. - Centralized visibility
Provides a unified view of cloud assets, risks, vulnerabilities, and compliance posture across multi-cloud environments. - Continuous monitoring
Tracks configuration changes in real time to help teams detect and remediate risks before they become security incidents.
By combining visibility, policy enforcement, and automation, CSPM solutions help organizations maintain a stronger and more consistent cloud security posture.
Cloud services covered by CSPM
CSPM solutions help organizations strengthen cloud security across IaaS, PaaS, and SaaS environments by continuously monitoring configurations, identities, access controls, and compliance risks across multi-cloud infrastructure.
| Category | Details |
|---|---|
| Full Form | Cloud Security Posture Management |
| Purpose | Detect and remediate cloud misconfigurations and compliance risks |
| Coverage | IaaS, PaaS, and limited SaaS visibility |
| Providers | AWS, Azure, Google Cloud |
| Deployment model | Primarily agentless SaaS deployment |
| Compliance frameworks | SOC 2, ISO 27001, GDPR, PCI DSS |
| Core capabilities | Continuous monitoring, risk prioritization, and compliance checks |
| Key value | Improved cloud visibility and infrastructure security |
An important limitation to note is that CSPM tools generally do not manage the underlying infrastructure of SaaS applications, since that responsibility remains with the SaaS provider. However, CSPM platforms can still monitor customer-controlled configurations such as access permissions, authentication settings, and data sharing policies.
Key benefits of CSPM

Cloud security posture management helps organizations reduce cloud risk, improve visibility, and maintain compliance across complex cloud environments. Gartner estimates that CSPM tools can reduce cloud security incidents caused by misconfigurations by up to 80%.
Here are some of the biggest benefits of CSPM:
- Centralized cloud visibility
Get a single view of cloud assets, permissions, misconfigurations, unencrypted databases, and MFA gaps across AWS, Azure, and GCP. - Faster compliance management
CSPM tools continuously monitor cloud environments against frameworks such as SOC 2, ISO 27001, and GDPR, helping teams identify and remediate compliance gaps faster. - Risk prioritization
CSPM solutions classify risks based on severity and exposure, helping security teams focus on the most critical issues first and reduce alert fatigue. - Continuous monitoring
Cloud environments change constantly. CSPM continuously scans configurations and security settings to detect risks in real time. - Improved DevOps collaboration
CSPM helps DevOps and security teams work from the same visibility layer, improving remediation workflows and reducing configuration errors. - Reduced manual effort through automation
Automated monitoring, policy enforcement, and remediation workflows help teams manage cloud security posture management at scale without relying on manual reviews.
Capabilities of CSPM solutions
Modern CSPM solutions help organizations continuously monitor, detect, and remediate cloud security risks across multi-cloud environments. Here are the core capabilities to look for in a CSPM platform:
- Multi-cloud and hybrid cloud support
Monitor cloud security across AWS, Azure, GCP, and hybrid environments from a centralized dashboard. - Continuous monitoring
Continuously scan cloud resources for misconfigurations, vulnerabilities, and compliance violations in real time. - Automated asset discovery
Automatically identify cloud assets, services, configurations, and exposed resources across dynamic environments. - Cloud misconfiguration detection
Detect insecure settings such as open storage buckets, excessive permissions, weak IAM policies, and exposed ports. - Compliance monitoring
Map cloud configurations against frameworks such as SOC 2, ISO 27001, GDPR, HIPAA, and PCI DSS to identify compliance gaps faster. - Threat detection and prevention
Monitor suspicious activity, unauthorized access attempts, and abnormal behavior across cloud environments. - AI-powered risk prioritization
Use contextual risk analysis and AI-driven prioritization to reduce alert fatigue and focus on the most critical cloud risks first. - Remediation automation
Automate remediation workflows, assign corrective actions, and enforce security policies at scale. - Incident response support
Provide alerts, investigation context, and response workflows to help teams contain and resolve cloud security incidents quickly. - SaaS security visibility
Monitor SaaS application configurations, user access, and security posture across tools such as Slack and Microsoft 365. - SIEM and CASB integrations
Integrate with SIEM, CASB, CWPP, and DevSecOps tools to centralize monitoring, threat detection, and response workflows. - DevOps and security collaboration
Help security and DevOps teams work together through shared visibility, automated workflows, and centralized cloud security posture management.
Who needs CSPM?
CSPM is valuable for any organization using cloud services, but it becomes especially important for businesses managing large-scale cloud infrastructure, sensitive data, or multiple compliance requirements.
Organizations that benefit the most from CSPM include:
1. Data-heavy organizations
Companies storing large volumes of customer, financial, or operational data in the cloud face higher security and compliance risks. CSPM helps continuously monitor sensitive cloud assets and identify misconfigurations before they lead to breaches.
2. Multi-cloud organizations
More than 80% of organizations now use multiple cloud providers, which increases complexity and visibility challenges. CSPM helps security teams monitor AWS, Azure, and GCP environments from a centralized platform and maintain consistent cloud security controls.
3. Compliance-driven organizations
Organizations working toward frameworks such as SOC 2, ISO 27001, HIPAA, PCI DSS, and GDPR use CSPM to continuously monitor cloud environments for compliance gaps and audit risks.
4. DevSecOps teams
DevSecOps teams use CSPM to detect insecure configurations early, automate remediation workflows, and improve collaboration between engineering and security teams.
5. SaaS and cloud-native companies
Fast-growing SaaS businesses often deploy cloud resources rapidly across multiple environments. CSPM helps maintain visibility, reduce configuration drift, and strengthen cloud security posture management as infrastructure scales.
CSPM vs other cloud security tools
CSPM is one part of the broader cloud security ecosystem. While other tools focus on workloads, identities, or SaaS access, CSPM primarily focuses on identifying misconfigurations, enforcing security policies, and improving cloud security posture.
| Tool | Primary focus | How it differs from CSPM |
|---|---|---|
| CSPM | Cloud infrastructure security posture | Detects misconfigurations, compliance gaps, and insecure cloud settings |
| CASB | SaaS access and data protection | Focuses on user access, shadow IT, and data movement across SaaS apps |
| CWPP | Workload and runtime protection | Protects workloads, containers, and applications running in the cloud |
| CIEM | Cloud identity permissions | Manages cloud entitlements and excessive user permissions |
| CNAPP | End-to-end cloud-native security | Combines CSPM, CWPP, CIEM, and other tools into a unified platform |
| CAASM | Cyber asset visibility | Provides visibility into assets and attack surfaces across environments |
CSPM vs CASB
CASB solutions help secure access to cloud applications and prevent data loss across SaaS platforms. However, they do not provide deep visibility into cloud infrastructure configurations like CSPM does.
CSPM vs CWPP
CWPP tools focus on protecting workloads, containers, and applications at runtime. CSPM focuses instead on securing the underlying cloud infrastructure, configurations, storage settings, and network policies.
CSPM vs CIEM
CIEM solutions manage identity permissions and cloud entitlements. While CIEM focuses on who can access cloud resources, CSPM focuses on whether those resources are configured securely.
CSPM vs CNAPP
CNAPP is a broader cloud-native security platform that combines multiple security capabilities into a single solution. CSPM is considered a subset of CNAPP.
In practice:
- CSPM focuses on posture management, compliance monitoring, and misconfiguration detection.
- CNAPP combines CSPM, CWPP, CIEM, vulnerability management, runtime protection, and workload security into one platform.
Organizations looking for broader cloud-native application security often adopt CNAPP platforms, while teams focused specifically on cloud configuration risks may start with CSPM.
CSPM vs CAASM
CAASM platforms provide visibility into all cyber assets across cloud and on-prem environments. CSPM is more narrowly focused on cloud infrastructure security and configuration management.
In many organizations, CSPM and CAASM work together to improve overall cloud security visibility and risk management.
How to choose a CSPM solution
Choosing the right CSPM solution is critical for improving cloud visibility, reducing misconfigurations, and scaling cloud security operations efficiently. The best platforms should support your current cloud environment while also adapting to future cloud security and compliance needs.
Here are the key factors to evaluate when selecting a CSPM solution:
1. Cloud integrations and multi-cloud support
Look for a CSPM platform that integrates seamlessly with AWS, Azure, GCP, and hybrid cloud environments. Strong API support and native integrations make deployment and monitoring easier.
2. Automation capabilities
Automation is essential for managing cloud security at scale. Evaluate whether the CSPM solution supports:
- Continuous monitoring
- Automated remediation
- Policy enforcement
- Real-time alerts
3. Customizable security policies
Every organization has different security and compliance requirements. Choose a CSPM solution that allows teams to customize policies, define risk thresholds, and map controls to frameworks such as SOC 2, ISO 27001, HIPAA, and GDPR.
4. Threat detection and risk prioritization
A strong CSPM platform should help teams identify high-risk cloud exposures quickly. Look for capabilities such as:
- Anomaly detection
- Threat intelligence
- Context-aware alerts
- AI-powered risk prioritization
5. Reporting and compliance visibility
The platform should provide dashboards, audit reports, compliance tracking, and risk analytics that help security and compliance teams monitor posture continuously.
6. Vendor roadmap and platform evolution
Cloud security platforms are evolving rapidly toward CNAPP and AI-driven security operations. Evaluate the vendor’s long-term roadmap, including:
- AI-assisted remediation
- CNAPP capabilities
- Identity security integrations
- Runtime protection support
A CSPM solution should not only solve today’s cloud security challenges but also support the future direction of cloud-native security.
How to implement CSPM
Implementing a CSPM framework requires more than connecting cloud accounts. Organizations need clear visibility, security policies, automation workflows, and continuous monitoring to improve cloud security posture effectively.
Here is a step-by-step approach to implementing CSPM:
1. Map cloud assets
Identify all cloud resources, workloads, storage buckets, identities, and SaaS applications across AWS, Azure, and GCP environments.
2. Define security policies
Establish cloud security policies based on internal requirements and frameworks such as SOC 2, ISO 27001, HIPAA, and GDPR.
3. Enable continuous monitoring
Configure the CSPM platform to continuously scan cloud environments for misconfigurations, vulnerabilities, compliance gaps, and risky activity.
4. Integrate DevOps workflows
Connect CSPM with DevOps and DevSecOps tools to identify security issues earlier in the development lifecycle and reduce configuration drift.
5. Automate remediation
Use automated workflows to fix common misconfigurations, enforce policies, and reduce manual security operations effort.
6. Align with compliance requirements
Map cloud controls to compliance frameworks and continuously monitor environments for audit readiness and policy violations.
7. Train security and engineering teams
Ensure cloud, DevOps, and security teams understand cloud security responsibilities, remediation workflows, and governance processes.
AI and the future of CSPM
AI is rapidly transforming how organizations manage cloud security posture management. Modern CSPM platforms are evolving beyond static rule-based monitoring toward intelligent, automated cloud security operations.
Key trends shaping the future of CSPM include:
- AI-powered threat correlation
AI can connect signals across cloud environments to identify high-risk attack paths and prioritize critical security issues faster. - Natural language security queries
Security teams are increasingly able to search cloud risks using natural language instead of complex filters or query languages. - Automated remediation
AI-driven workflows can automatically remediate common cloud misconfigurations and reduce manual response times. - CNAPP convergence
CSPM platforms are increasingly becoming part of broader CNAPP solutions that combine posture management, workload protection, identity security, and runtime protection into a single platform.
As cloud environments continue to grow more complex, AI-driven CSPM solutions will play a larger role in improving visibility, reducing alert fatigue, and accelerating cloud risk remediation.
How Scrut’s CSPM solution secures your cloud
Scrut’s CSPM solution helps organizations continuously monitor cloud environments, detect misconfigurations, prioritize risks, and maintain compliance across AWS, Azure, and GCP. With automated monitoring and centralized visibility, teams can strengthen cloud security without relying on manual reviews.
This visibility becomes especially important for fast-growing cloud-native companies. Typesense, for example, needed stronger visibility into cloud risks while preparing for SOC 2 Type 2 compliance. With thousands of EC2 instances spread across their environment, monitoring cloud security manually became difficult. Using Scrut’s CSPM solution, Typesense automated cloud monitoring, improved risk visibility, and completed its SOC 2 audit 5x faster.
Key capabilities of Scrut’s CSPM solution include:
- Unified cloud visibility
Monitor cloud assets, configurations, risks, and compliance posture from a centralized dashboard across multi-cloud and hybrid environments. - Continuous monitoring against 200+ CIS controls
Continuously assess cloud environments against CIS benchmarks and cloud security best practices to identify security gaps early. - Real-time misconfiguration alerts
Detect risky cloud configurations and receive actionable remediation recommendations before they become security incidents. - Faster remediation workflows
Assign, track, and automate remediation tasks directly within the platform to reduce response times and improve operational efficiency. - Reduced false positives through contextual risk prioritization
Scrut prioritizes risks based on severity and exposure, helping teams focus on the most critical cloud security issues first instead of sorting through noisy alerts. - Slack integrations for faster collaboration
Receive cloud security alerts directly in Slack and streamline remediation across security and DevSecOps teams. - Built-in compliance visibility
Map cloud controls to frameworks such as SOC 2, GDPR, and ISO 27001 to support continuous compliance monitoring and audit readiness.
Ready to strengthen your cloud security posture and reduce misconfigurations across your cloud environment? Book a free demo today.
CSPM is a cloud security solution that helps organizations detect misconfigurations, monitor compliance, and improve visibility across cloud environments such as AWS, Azure, and GCP. It continuously monitors cloud infrastructure to identify security risks before they lead to breaches.
CSPM stands for Cloud Security Posture Management.
Examples of CSPM platforms include Scrut, Prisma Cloud, Wiz, Lacework, and Orca Security. These platforms help organizations monitor cloud configurations, identify risks, and maintain compliance across multi-cloud environments.
CSPM provides: Continuous cloud security monitoring Misconfiguration detection Compliance visibility Risk prioritization Automated remediation workflows Centralized visibility across cloud environments
CSPM focuses on securing cloud infrastructure by identifying misconfigurations, compliance gaps, and insecure settings. CWPP focuses on protecting workloads, containers, virtual machines, and applications running inside cloud environments. Many modern CNAPP platforms combine both CSPM and CWPP capabilities.

Megha Thakkar is a technical content writer with about a decade of experience in cybersecurity and compliance. She writes extensively on SOC 2, ISO 27001, GDPR, and security operations, helping organizations translate complex requirements into clear, audit-ready decisions. Her work, tailored for CISOs and executive leaders, is frequently cited in U.S. government and NIST publications.

Team Scrut is a collective of compliance, security, and risk practitioners sharing practical guidance on building audit-ready, scalable programs. We write about SOC 2, ISO 27001, continuous compliance, third-party risk, cloud security, and GRC automation, blending regulatory depth with operator experience to help fast-growing companies strengthen trust, streamline audits, and stay ahead of evolving security demands.

























