Choose risk-first compliance that’s always on, built for you.
Go back to blogs
ISO 27001 compliance: Complete guide (2026)
Last updated on
May 11, 2026
8
min. read
.png)
If your organization handles sensitive data, ISO 27001 compliance is likely already on your radar. Adopted by companies across IT, healthcare, finance, and manufacturing in over 150 countries, ISO 27001 has become the global benchmark for information security management.
At its core, the standard helps organizations build a structured Information Security Management System (ISMS), a framework designed to protect intellectual property, customer data, and business-critical information while ensuring alignment with relevant legal and regulatory requirements.
This ISO 27001 guide walks you through everything you need to know: the framework's structure, its controls and policies, the certification process, and how to maintain compliance over time. Originally published in 2005 and most recently updated in 2022, the standard continues to evolve alongside the threat landscape, making it as relevant today as ever.
Read on for a full breakdown of ISO 27001 and what it takes to comply.
What is ISO 27001 compliance?
ISO 27001 compliance means implementing and maintaining an Information Security Management System (ISMS) that meets the requirements of ISO/IEC 27001, developed by ISO and IEC. It demonstrates that an organization systematically manages sensitive information, mitigates security risks, and meets relevant legal and regulatory obligations.
ISO 27001 at a glance
What does the ISO 27001 standard mean?
ISO 27001 is an internationally recognized standard for managing information security. It provides organizations with a structured framework to establish, implement, and continuously improve an ISMS, ensuring sensitive information stays protected against evolving threats.
A few things worth clarifying upfront:
- ISO 27001 is not a product or tool. It is a management standard that defines how an organization should approach information security systematically.
- Certification is voluntary. Organizations choose to pursue it to demonstrate compliance, build customer trust, or meet contractual and regulatory requirements.
- The 2022 update matters. ISO/IEC 27001:2022 replaced the 2013 version, introducing streamlined controls better suited to modern cybersecurity challenges.
What are the ISO 27001 requirements?
ISO 27001 requirements define the criteria an organization must meet to establish, implement, maintain, and continually improve an ISMS. They cover everything from leadership commitment and risk assessment to control implementation and performance evaluation, providing a structured path to managing information security effectively.
Key requirement areas include:
- Context of the organization: Understanding internal and external factors that affect information security
- Leadership: Securing management commitment and defining security roles and responsibilities
- Planning: Conducting risk assessments and setting objectives for the ISMS
- Support: Ensuring adequate resources, staff competence, and internal communication
- Operations: Implementing and controlling security processes and risk treatment plans
- Performance evaluation: Monitoring, measuring, and auditing ISMS effectiveness
- Improvement: Addressing non-conformities and driving continuous improvement
ISO 27001 framework: Clauses and controls
The ISO 27001 framework is organized into two main components: clauses and Annex A.
Clauses (0 to 10) establish the foundation for building and managing an ISMS. Clauses 0 to 3 set the context, scope, and terminology. Clauses 4 to 10 cover the operational requirements, from leadership and planning through to performance evaluation and continuous improvement.
Annex A provides a reference set of 93 security controls grouped into four categories: organizational, people, physical, and technological. Organizations select and apply controls based on their individual risk assessments and security needs.
Together, the clauses and Annex A give organizations a complete, adaptable structure for managing information security, one that scales to any industry or organizational size.
What are ISO 27001 controls?
ISO 27001 controls are the security measures and safeguards organizations implement to manage information security risks. The current version, ISO/IEC 27001:2022, includes 93 controls drawn from Annex A, each selected based on an organization's specific risk assessment and security requirements.
The 93 controls are organized into four categories:
- Organizational controls (37): Policies, roles, responsibilities, and governance measures that define how security is managed at an institutional level.
- People controls (8): Measures addressing employee behavior, awareness, training, and responsibilities across the employment lifecycle.
- Physical controls (14): Safeguards protecting physical assets, facilities, and equipment from unauthorized access or damage.
- Technological controls (34): Technical measures covering access control, encryption, logging, vulnerability management, and secure development.
Organizations are not required to implement all 93 controls. Selection is driven by the risk treatment process, with any exclusions documented and justified in the Statement of Applicability (SoA).

How to achieve ISO 27001 compliance
Achieving ISO 27001 compliance involves a structured sequence of steps that take an organization from initial assessment through to certified ISMS operation.
- Define the ISMS scope: Identify which parts of the organization, information assets, and processes fall within the ISMS boundary.
- Conduct a gap analysis: Assess current security practices against ISO 27001 requirements to identify areas of non-compliance.
- Perform a risk assessment: Identify, analyze, and evaluate information security risks across the defined ISMS scope.
- Select and implement controls: Choose applicable controls from Annex A based on risk assessment outcomes and document exclusions in the Statement of Applicability.
- Develop policies and procedures: Create and formalize the documentation required by ISO 27001, including the information security policy and supporting procedures.
- Train staff and build awareness: Ensure employees understand their roles and responsibilities within the ISMS.
- Run an internal audit: Evaluate ISMS effectiveness and address any non-conformities before the external audit.
- Complete the external audit: Engage an accredited certification body to conduct the Stage 1 documentation review and Stage 2 certification audit.
- Obtain certification and maintain it: Once certified, sustain compliance through annual surveillance audits and a recertification audit every three years.
What is ISO 27001 compliance monitoring?
ISO 27001 compliance monitoring is the ongoing process of tracking, measuring, and verifying that an organization's ISMS continues to meet the standard's requirements after certification. It ensures controls remain effective, risks are managed proactively, and the organization stays ready for annual surveillance audits.
Why it matters
Compliance does not end at certification. Continuous monitoring is what keeps it intact.
- Audit readiness: Maintains a consistent state of preparedness for annual surveillance audits and the three-year recertification cycle, eliminating last-minute scrambles.
- Risk visibility: Surfaces emerging threats and control gaps before they escalate into non-conformities or security incidents.
- Continuous compliance: Ensures the ISMS reflects the current state of the organization as it scales, adopts new tools, or enters new markets.
Key activities
- Risk assessment: Regularly reviewing and updating the risk register to account for changes in the threat landscape, business operations, or asset inventory.
- Control monitoring: Tracking whether implemented controls are functioning as intended and flagging deviations for remediation.
- Internal audits: Conducting periodic evaluations of the ISMS to identify non-conformities and drive corrective action before external audits.
- Evidence collection: Continuously gathering and organizing documented proof that controls are operating effectively across the ISMS scope.
Automation
Manual monitoring at scale is resource-intensive and error-prone. Automation addresses this directly.
- Evidence automation: Integrates with cloud environments, identity providers, and infrastructure tools to collect compliance evidence without manual effort.
- Alerts: Triggers real-time notifications when control failures, policy violations, or high-risk events are detected.
- Integrations: Connects with existing tools across the security and IT stack to centralize monitoring and reduce context-switching.
Frequency
ISO 27001 compliance monitoring operates on two tracks. Continuous monitoring runs in the background at all times, tracking controls, collecting evidence, and flagging anomalies as they occur. Periodic monitoring runs on a defined schedule, covering formal risk assessments, internal audits, and management reviews at intervals appropriate to the organization's risk profile.
ISO 27001 audit
An ISO 27001 audit is a formal evaluation of an organization's ISMS to verify that it meets the requirements of the standard and continues to operate effectively.
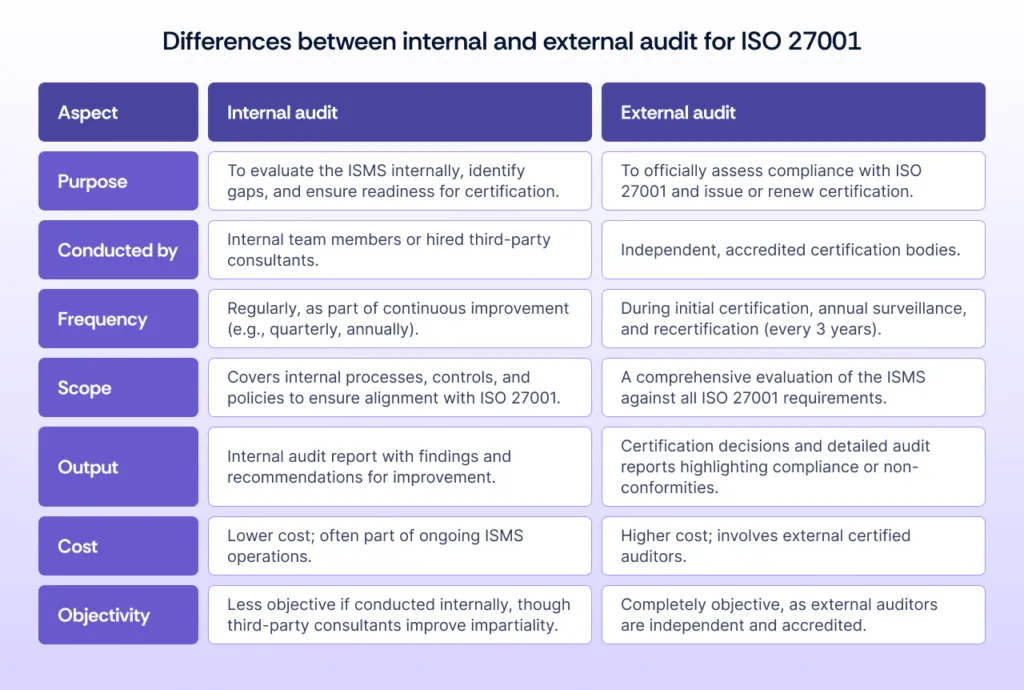
There are two types:
Internal audit: It is conducted by trained staff or third-party consultants. It identifies gaps, non-conformities, and areas for improvement within the ISMS, and is typically performed in preparation for an external audit.
External audit: It is carried out by an accredited certification body. It is independent, formal, and determines whether an organization qualifies for certification or renewal. The external audit follows a two-stage process:
- Stage 1 (Documentation review): The auditor evaluates ISMS policies, procedures, and documentation to confirm readiness for the certification audit.
- Stage 2 (Certification audit): A thorough on-site assessment of how the ISMS is implemented and operating in practice.
Following certification, accredited bodies conduct annual surveillance audits to confirm continued compliance. A full recertification audit is required every three years.
ISO 27001 certification cost
ISO 27001 certification typically costs between $15,000 and $90,000 in total, depending on the size, complexity, and existing security maturity of the organization.
The total cost breaks down across three areas:
Audit preparation: It covers gap analysis, penetration testing, and readiness activities. Estimated cost: $3,000 to $40,000.
Implementation: This covers security training, new tools, and productivity impact during rollout. Estimated cost: from $1,000 annually.
Certification audit: This covers internal audits, the Stage 1 and Stage 2 external audit, and surveillance audits. Estimated cost: $10,000 to $50,000.
These figures are estimates. Actual costs vary based on organizational needs, the chosen certification body, and whether external consultants are engaged.
For smaller organizations, automation platforms can significantly reduce implementation and audit preparation costs by streamlining evidence collection and compliance management.
How long does ISO 27001 certification take?
ISO 27001 certification typically takes between three and twelve months, depending on the organization's size, complexity, and existing security maturity.
Smaller organizations with established security practices may certify faster, while larger enterprises implementing an ISMS from scratch should expect a longer timeline.
Tools for ISO 27001 compliance
Implementing and maintaining ISO 27001 manually is resource-intensive. Purpose-built ISO 27001 software reduces that burden by centralizing compliance activities, automating evidence collection, and keeping the ISMS audit-ready year-round.
Scrut is an AI-powered compliance platform that brings ISO 27001 automation to every stage of the certification journey, from initial gap analysis through to recertification. Instead of managing policies, controls, and audit evidence across disconnected tools, teams get a single platform that handles the operational load continuously.
Key capabilities include:
- Compliance management: Centralized control over policies, controls, and documentation across the ISMS scope.
- Audit readiness: Real-time compliance tracking and organized evidence storage, structured for Stage 1 and Stage 2 audits.
- Policy and control templates: Pre-built templates for core ISO 27001 policies, reducing setup time and ensuring alignment with standard requirements.
- Continuous monitoring: Automated tracking of control effectiveness with alerts for gaps or failures.
- Integrations: Native connections to cloud providers, identity platforms, and ticketing tools for seamless evidence collection.
- Expert guidance: Access to ISO 27001 consultants who support ISMS design, gap remediation, and audit preparation.
For organizations pursuing certification for the first time or managing the three-year recertification cycle, ISO 27001 automation significantly reduces both the time and cost involved.
ISO 27001 vs other standards
ISO 27001 is often implemented alongside other frameworks. Understanding how it compares helps organizations identify overlap, avoid duplication, and build a more efficient compliance program.
ISO 27001 maps well to most major security and risk frameworks, making it a strong foundation for organizations managing multiple compliance requirements simultaneously.
How Scrut helps with ISO 27001 compliance
Scrut is an AI-powered compliance platform that operationalizes continuous compliance and security, replacing audit chaos with scalable execution. For organizations pursuing or maintaining ISO 27001 certification, it reduces the time, cost, and manual effort involved at every stage.
- Get audit-ready faster: Centralized evidence collection and real-time compliance tracking mean you are never caught unprepared for a Stage 1, Stage 2, or surveillance audit.
- Eliminate manual effort: Automated evidence gathering across cloud environments, identity providers, and infrastructure tools replaces hours of manual work per audit cycle.
- Implement faster with templates: Pre-built policies and controls aligned to ISO 27001 requirements cut setup time significantly, particularly for first-time certifications.
- Stay compliant between audits: Continuous control monitoring surfaces gaps and failures as they occur, not weeks later during an internal review.
- Reduce certification costs: Automation and centralized compliance management lower the resource burden associated with audit preparation and ongoing ISMS maintenance.
- Scale without added complexity: As the organization grows, Scrut scales with it, keeping the ISMS current without proportional increases in compliance overhead.
FAQs
What is ISO 27001 compliance?
ISO 27001 compliance means implementing and maintaining an ISMS that meets the requirements of ISO/IEC 27001. It demonstrates that an organization systematically manages information security risks, protects sensitive data, and meets relevant legal and regulatory obligations across its operations.
Who can be ISO 27001 certified?
Any organization, regardless of size, industry, or location, can pursue ISO 27001 certification. This includes businesses, non-profits, and government entities that handle sensitive information and want to demonstrate a structured approach to information security management.
What are the benefits of ISO 27001 certification?
Key benefits include:
- Enhanced security posture: A structured ISMS reduces exposure to data breaches, unauthorized access, and operational security failures.
- Regulatory compliance: Certification supports alignment with legal and industry requirements, including GDPR and sector-specific regulations.
- Customer trust: ISO 27001 certification signals to clients and partners that information security is managed to an internationally recognized standard.
- Competitive advantage: Certification is increasingly a procurement requirement, particularly in enterprise and public sector sales cycles.
- Continuous improvement: The standard's ongoing audit and review cycle embeds a culture of proactive risk management across the organization.
How to automate ISO 27001 compliance?
ISO 27001 automation platforms like Scrut connect to your existing cloud, identity, and infrastructure tools to automatically collect compliance evidence, monitor controls in real time, and keep documentation audit-ready without manual effort.
Automation is particularly valuable for managing annual surveillance audits and the three-year recertification cycle without scaling headcount proportionally.
How long does ISO 27001 certification take?
ISO 27001 certification typically takes between three and twelve months. Smaller organizations with existing security controls in place can move faster, while larger enterprises building an ISMS from scratch should plan for a longer implementation timeline before engaging a certification body.
Table of contents



















