CSPM solutions provide cloud asset and configuration visibility. A CSPM tool maps interdependencies between cloud infrastructure, services, and abstraction layers to analyze the scope of the risk. It enforces data protection controls and identifies workload issues and potential attack surfaces.
The growing adoption of cloud services brings with it challenges, such as difficulty in tracking cloud workloads and limited security coverage, with increased complexity due to the multi-cloud environment.
Settings in the cloud are prone to manual errors leading to misconfigurations. A large number of cloud data breaches happen because of misconfigurations.
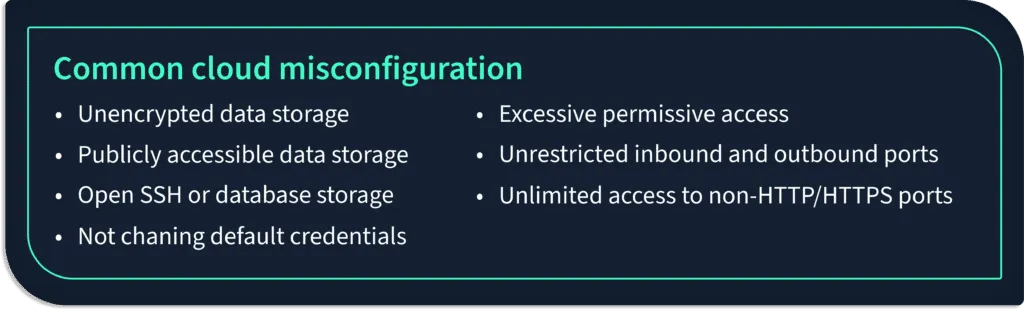
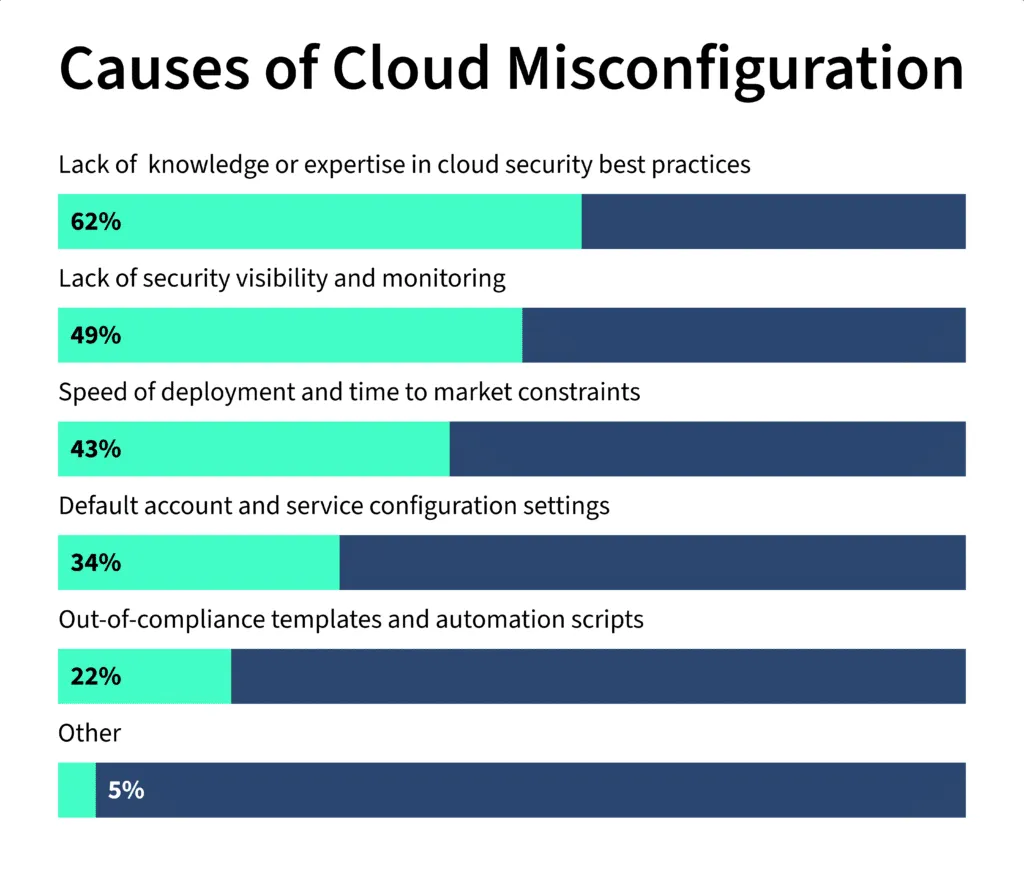
These misconfigurations occur due to various reasons:
- Lack of awareness of cloud security.
- Not having complete visibility in the cloud environment.
Recently, a simple misconfiguration in the access control caused a ransom attack on the Australian telecommunications company Optus.
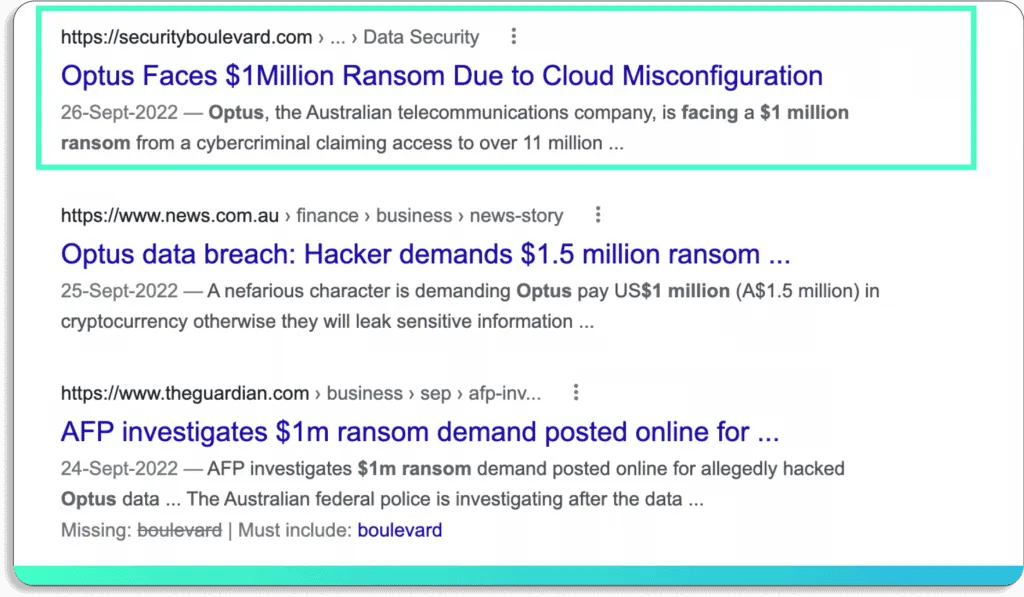
Consequently, over 11 million records of the company were exposed.
Incidents like this are not rare. According to a report by VMware, misconfigurations are the cause of 1 in 6 cloud data breaches.
Furthermore, this number will only increase as more organizations shift their data to the cloud. According to a Gartner report, 99% of cloud security issues will be due to misconfigurations by the year 2025.

Moreover, traditional security tools fail to detect vulnerabilities in the cloud. Hence, organizations are turning towards cloud monitoring tools, like cloud security posture management (CSPM), to solve these issues.
CSPM tools help you secure your cloud across IaaS , PaaS, and SaaS with continuous real-time monitoring. They detect your cloud misconfigurations and help you proactively prevent cyber incidents, such as data breaches, data exfiltration, data theft, email spoofing, and DDOS attacks.
16 Cloud Security Posture Management (CSPM) Tools: A Quick Overview
| # | Tool | Core Strengths / Description | Pros | Cons | G2 Rating |
|---|---|---|---|---|---|
| 1 | Scrut Automation | - Customizable cloud controls - Preemptive remediation - Contextual alerts via Slack - Full-stack security across multi-cloud |
- Contextual, actionable alerts - Unified dashboard - Slack integration - Easy delegation and setup |
- No explicit cons mentioned | 5.0 |
| 2 | JupiterOne | - Asset inventory & relationship mapping - Supports compliance (SOC, PCI, HIPAA) - GraphQL API |
- Graph-based visualizations - Powerful integrations - Easy SOC/PCI evidence collection |
- Initial learning curve | 5.0 |
| 3 | Orca Security | - Agentless scanning - End-to-end cloud visibility - Fast implementation |
- Detailed insights - Simple to administer - Covers multiple layers |
- Less visibility into memory-level system activity | 4.7 |
| 4 | Lacework | - Threat detection across multi-cloud - Kubernetes & hybrid support - Automated compliance tracking |
- Quick deployment - Great alert system - Good compliance visibility |
- No two-way sync with Jira | 4.5 |
| 5 | Aquasec | - CSPM for cloud-native deployments - Visual scan results - Protects VMs, containers, serverless |
- Rich dashboards - Auto threat visualization - Easy policy enforcement |
- Lacks some integrations (Datadog, Webhooks) | 4.5 |
| 6 | CloudGuard | - Multi-cloud security & governance - Kubernetes and IAM support - Strong compliance management |
- Broad service coverage - Deep workload visibility |
- Complex setup - Limited 3rd-party integrations |
4.5 |
| 7 | Threat Stack | - Host-based intrusion detection - Layered visibility & remediation |
- Predefined SOC 2 rules - Clear dashboard - Easy agent deployment |
- Alert tuning required - Noisy false positives |
4.4 |
| 8 | Trend Micro Cloud One Conformity | - Real-time multi-cloud compliance - Single dashboard visibility - Strong governance & policy monitoring |
- Instant alerts - Infra-wide vulnerability view - Compliance-first |
- Complex configuration - Policy update delays |
4.6 |
| 9 | BMC Helix Cloud Security | - Custom & prebuilt policy support - ITSM integration for automation |
- One-click remediation - Full user control - Friendly interface |
- Tedious install (50+ steps) - Incident closing issues |
4.4 |
| 10 | Ermetic | - Entitlement & risk prioritization - Multi-cloud visibility - SSO integration |
- Enforces least-privilege access - Powerful IAM risk analysis - Easy SSO setup |
- No Kubernetes misconfig detection - Needs cloud vuln improvement |
4.9 |
| 11 | Prisma Cloud | - CI/CD, IaC, container integration - Unified risk view - Broad cloud provider support |
- Real-time container scanning - Strong compliance - IaC integration |
- Expensive - UI complexity |
4.3 |
| 12 | CrowdStrike Falcon Horizon | - Unified host-to-cloud coverage - Misconfig detection and remediation |
- Multi-cloud threat alerts - Easy control panel monitoring |
- Sometimes misclassifies non-relevant vulnerabilities | 4.4 |
| 13 | Datadog CSPM | - Unified logging and security monitoring - Benchmarked config scans - Reporting dashboards |
- Centralized logging - Real-time scans - Compliance tracking |
- High cost - Heavy resource usage |
4.3 |
| 14 | Zscaler CSPM | - Fast secure connectivity - Remediation across public clouds |
- Fast MFA-based access - Reliable mobile auth flow |
- Custom app config complexity - Crashes after device suspend |
4.2 (Capterra) |
| 15 | Rapid7 InsightCloudSec | - Real-time risk assessment - CI/CD rule enforcement - Automated remediation |
- Scalable - Easy to deploy - Secure build pipeline |
- Scan failures - Manual cleanup needed |
3.9 |
| 16 | Sophos Cloud Optix | - Risk-based alerting - Agent-based identity tracking - Strong compliance focus |
- Prioritized risk remediation - Manages identity & policy - Maintains compliance |
- Expensive - Agent-based - Complex setup |
4.3 |
16 Cloud Security Posture Management (CSPM) Tools
If you go into the market looking for CSPM solutions, it is easy to get confused with hundreds of CSPM tools, each claiming to be the best.
So, we have picked the top 16 CSPM tools to reduce your research time.
1. Scrut Automation
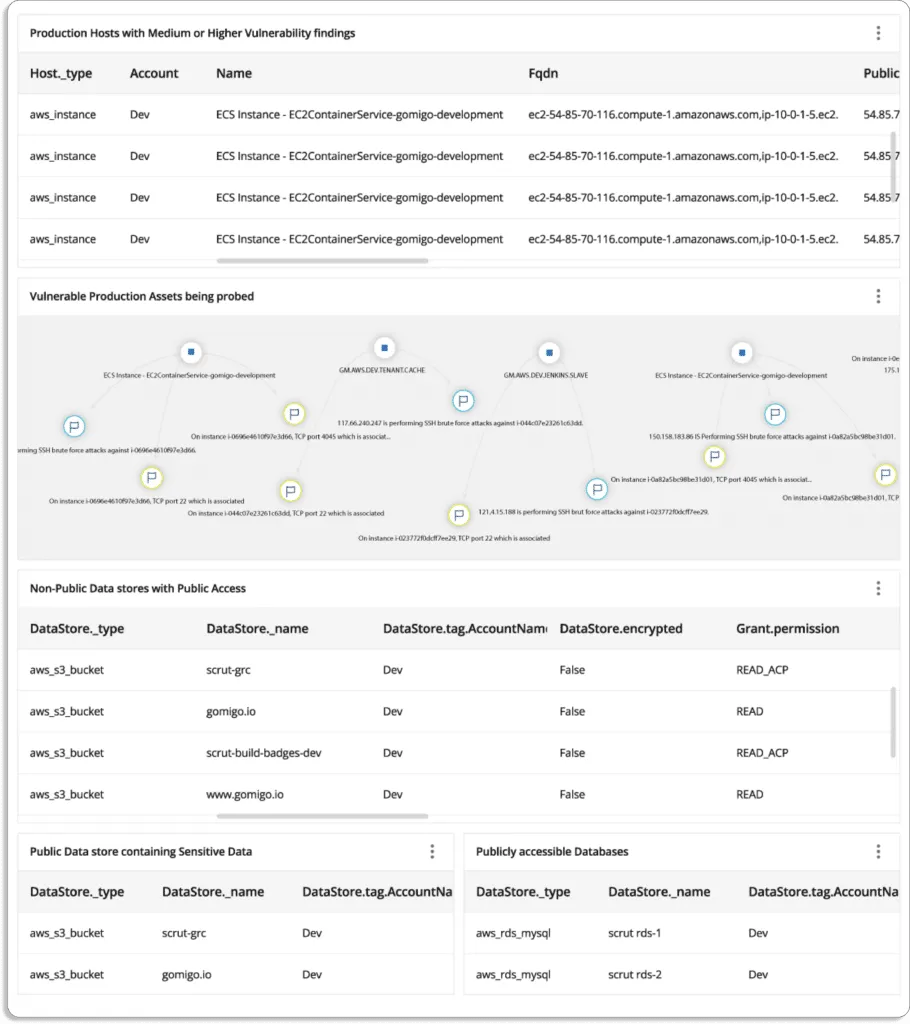
Scrut Cloud Security is more than a traditional cloud security posture management tool. It scans and monitors misconfigurations in your public cloud accounts—AWS, Azure, Google Cloud Platform, and more.
- Continuously monitor against cloud controls: Scrut Cloud Security automatically tests your cloud configurations against 200+ cloud controls to maintain a strong InfoSec posture. It then provides simple automated workflows to fix them as they occur. Furthermore, it enables you to customize your security controls by adding custom controls to scan.
At Scrut, we take a different approach to security and compliance. We believe that if you have run your groundwork for cloud security, you are better prepared to get compliant. Compliance is a byproduct of being secure.
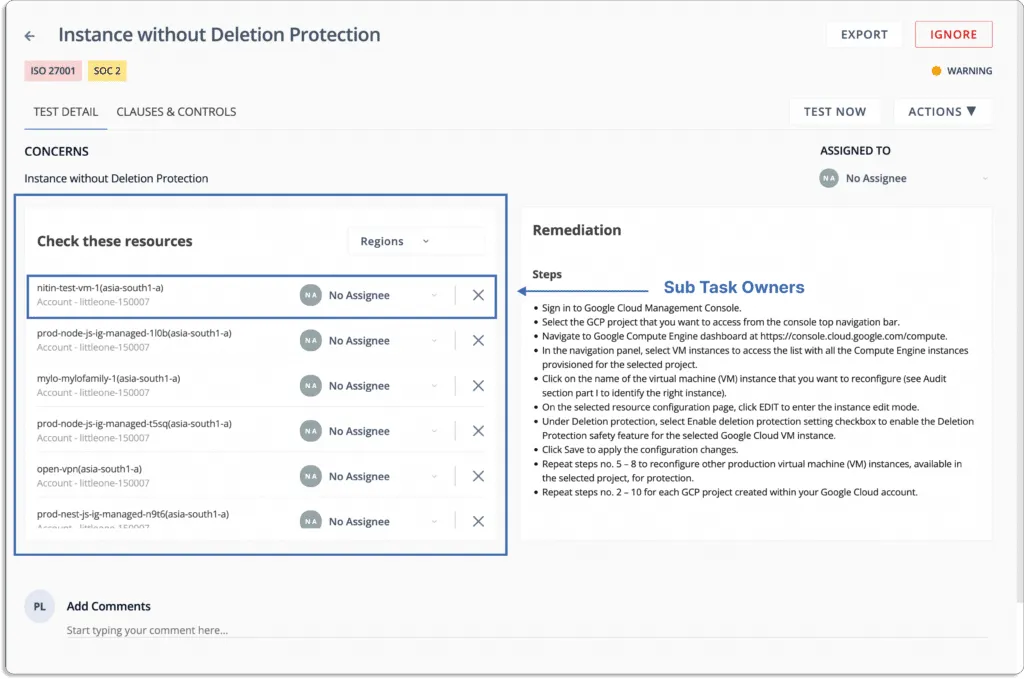
- Fix cloud misconfigurations preemptively: Scrut Cloud Security ensures that your cloud infrastructure is continuously compliant. When misconfigurations occur, Scrut gives you alerts with actionable recommendations for remediation.
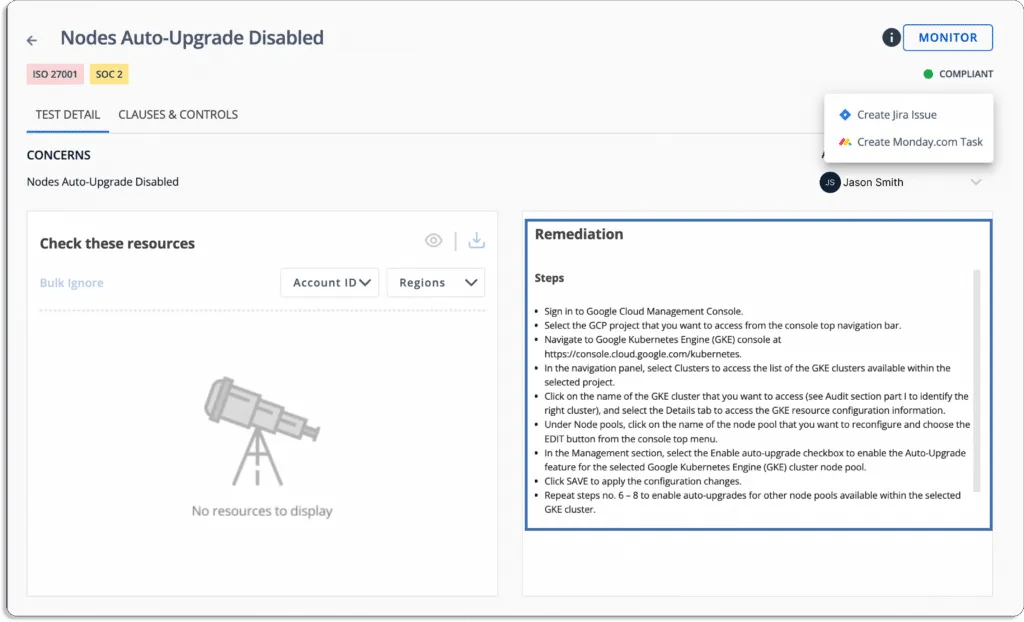
Moreover, you can delegate tasks to team members for misconfiguration fixes.
Furthermore, you get notifications directly on your existing tools, like Slack.
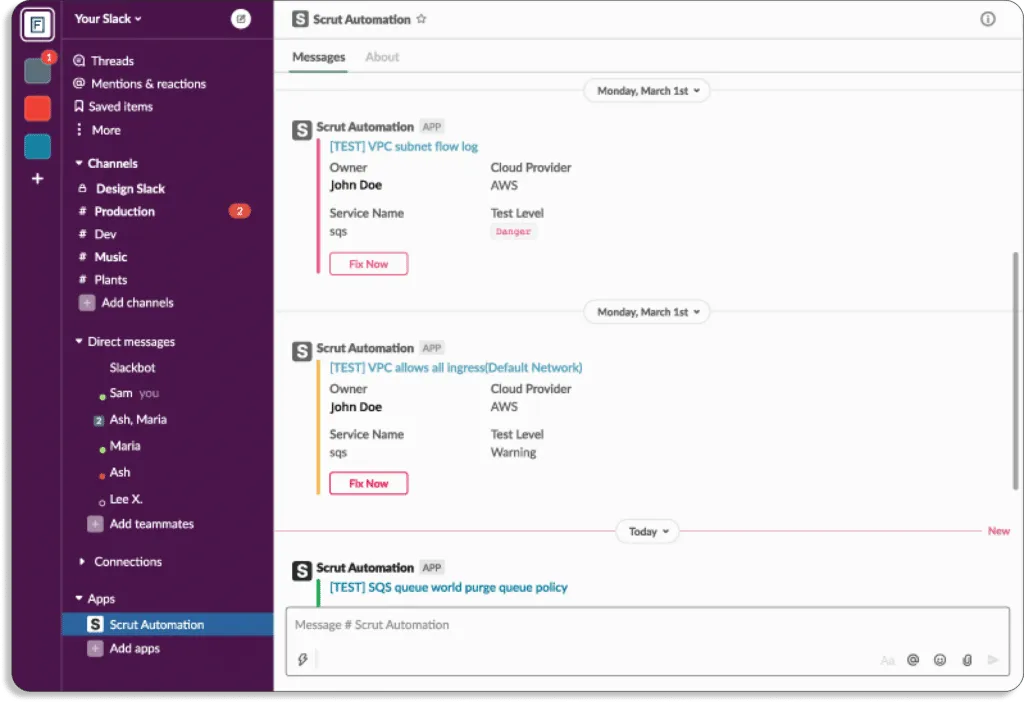
Unlike other CSPM platforms, Scrut doesn’t just bombard your security teams with alerts. During an internal research study, we found one of the key reasons customers preferred us over other CSPM platforms was our contextual and accurate alerts. So, we developed Scrut Cloud Security in such a way that it is easy to act on them.
One of our current customers was getting many false positives with their previous CSPM tool. It only wasted their security team’s time.
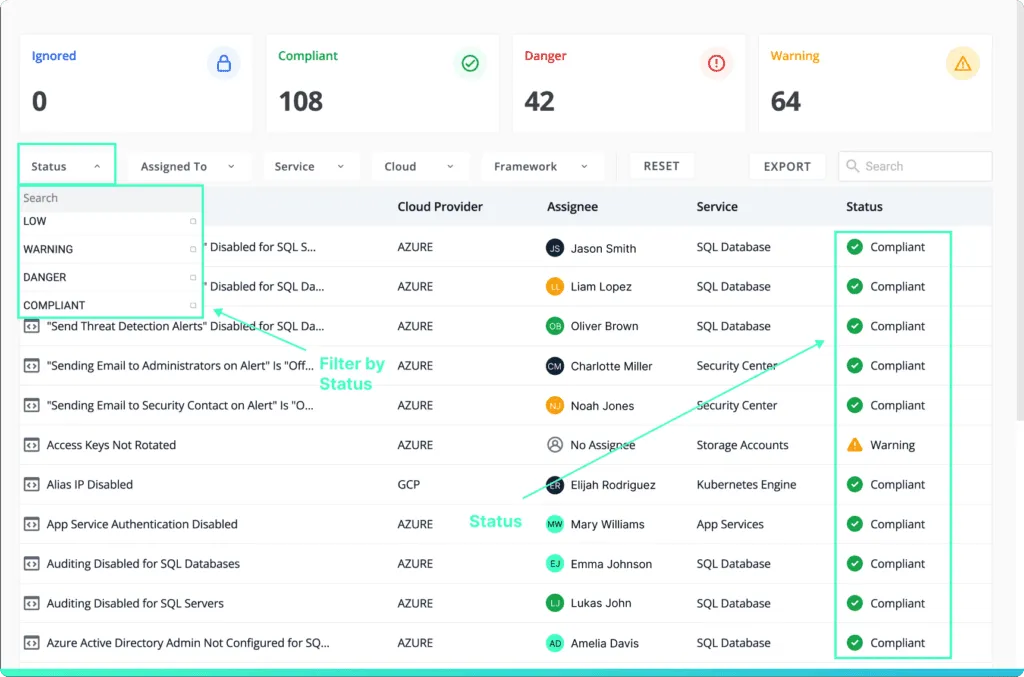
With Scrut, this issue was resolved. Through a unified dashboard for all the risks and automated classification of status, you know what to work on first.
Status
- Danger – Most critical issues. Work on these first.
- Warning – After working on the issues marked as danger, next you can work on these.
- Low – These risks are informational in nature and should be worked on last.
- Compliant – Everything is fine. Don’t need to do anything.
- Strengthen your cloud-native security: Scrut Cloud Security helps you establish full-stack security for all your cloud-native deployments, across virtual machines (VMs), containers, and serverless, by implementing best-practice security policies consistently across your hybrid and multi-cloud infrastructure.
How Scrut Cloud Security helped Typesense improve their cloud security posture and get compliant with SOC 2 Type 2 5x faster?
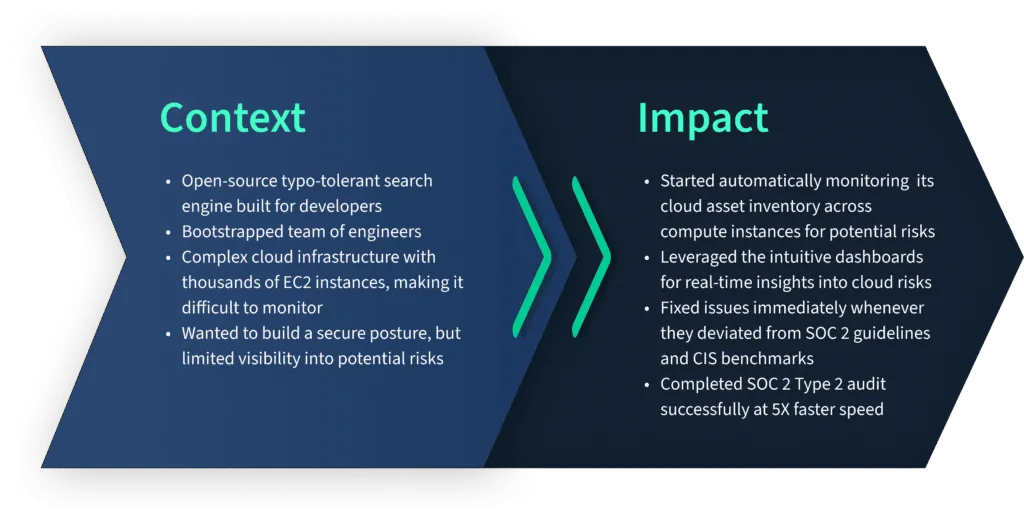
One of our clients, Typesense, wanted to build a secure cloud posture to get compliant with SOC 2 Type 2 but were limited by incomplete visibility into their cloud risks. So, they turned to Scrut Automation.
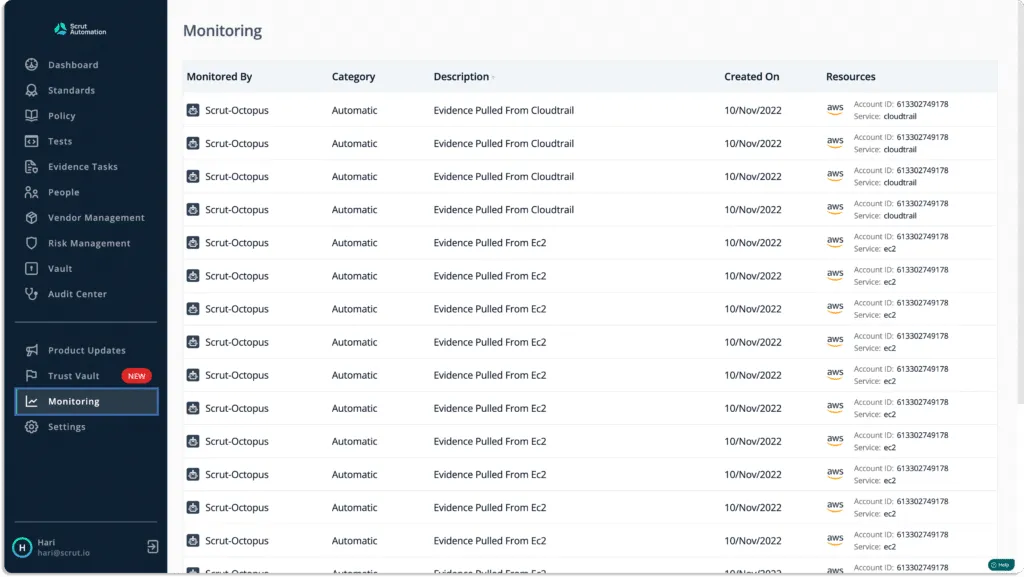
During our initial discussion with them, we found that they had thousands of EC2 instances, which were difficult to monitor. Scrut solved that issues with automated monitoring across their cloud environment.
As a result, they successfully completed their SOC 2 audit at 5x speed.
Here is what Jason Bosco, founder, and CEO of Typesense has to say about Scrut.
Getting started with Scrut is easy and quick. It is a 2 step process.

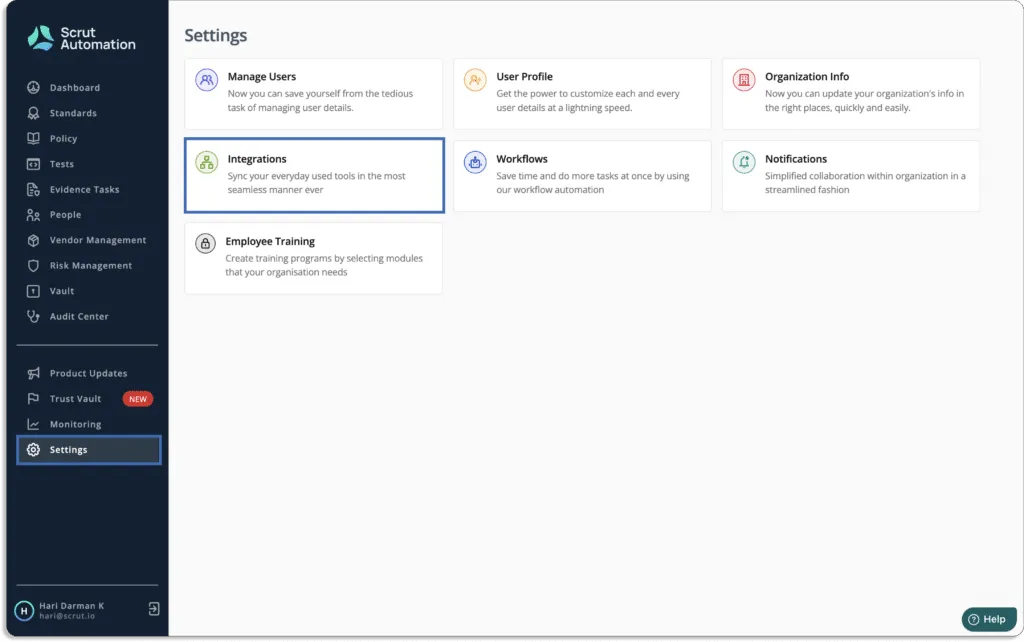
First, you need to connect your cloud infrastructure with the Scrut platform. This just takes a few minutes. Just go to Integrations under the Settings tab.
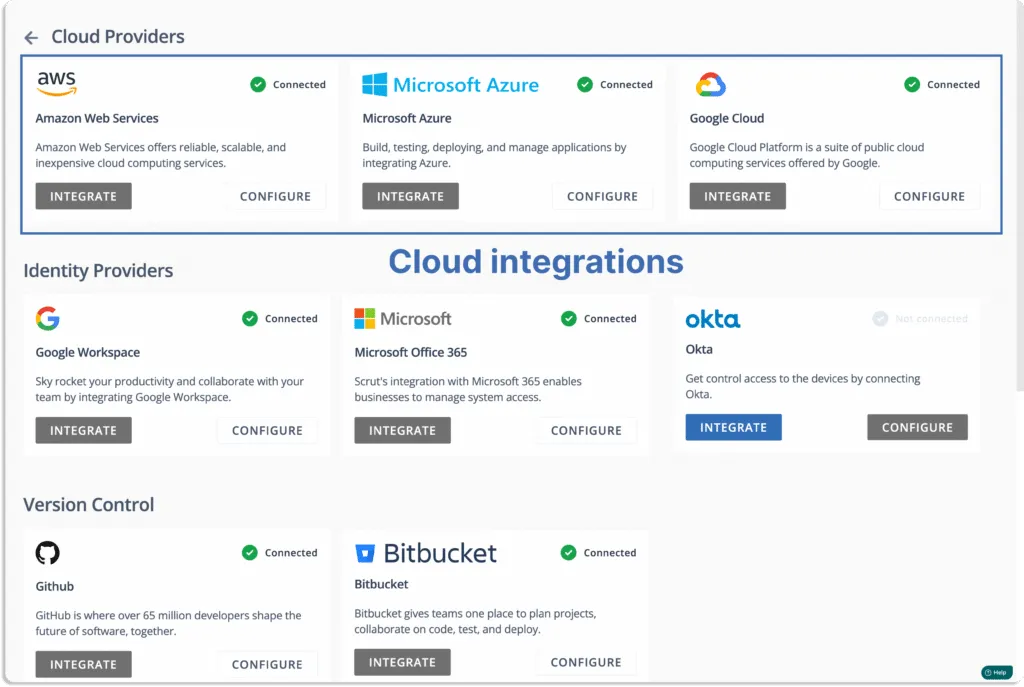
You will land on this page. Choose your cloud service providers.
Note that Scrut supports multi-cloud service providers.
Once connected, you can see the data appearing in the tests tab.
Customer Rating
- G2- 5/5

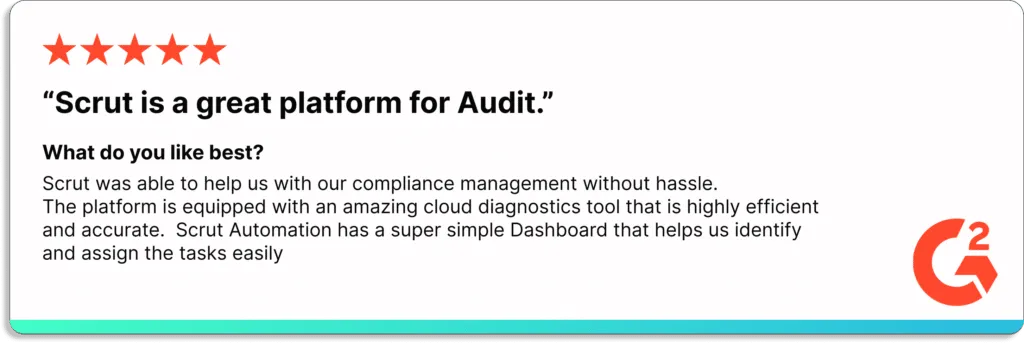
2. JupiterOne
The JupiterOne platform makes it simple for security teams to manage cloud security posture and governance requirements. It gathers information across your entire cloud and simplifies it, so that security teams can act on that data.
The platform consolidates and normalizes cyber asset data across the entire cloud environment, including identity providers, code repositories, endpoints, and ephemeral assets. It maps the relationships between each resource to provide a complete picture of the digital ecosystem.
Furthermore, the platform provides continuous monitoring of cloud environments and controls.
Pros
- Provides inventory assets and configurations using the GraphQL API.
- With the JupiterOne platform, anyone can integrate their environment and can add evidence to start assessing SOC, PCI, and HIPAA controls.
- Users can easily visualize relationships to understand what is happening in thier cloud environment.
Cons
- It can get overwhelming initially, and it takes time to get used to all the features.
Customer Rating
- G2- 5/5
3. Orca Security
Orca is a comprehensive cloud security posture management (CSPM) solution that monitors cloud environments for misconfigurations, policy violations, and compliance risks, including cloud-native services. It helps prevent risks across every layer of cloud estate, including workloads and configurations, from development to production.
The tool enables organizations to address critical cloud security issues quickly, efficiently, and affordably, allowing them to operate confidently in the cloud.
Furthermore, it provides comprehensive coverage and visibility into cloud risks.
Pros
- Provide detailed information about vulnerable cloud resources.
- The tool is simple to administer.
- Provides users with insights into their cloud environments in a short time.
Cons
- Orca’s agentless technology provides less visibility into system activity, such as applications loaded in memory.
Customer Rating
- G2- 4.7/5
4. Lacework
Lacework identifies threats and vulnerabilities across your entire environment with comprehensive cloud account security for AWS, Azure, Google Cloud, and hybrid environments. The platform reduces risk in your multi-cloud environment by detecting configuration problems and monitoring accounts for unusual activity.
It simplifies meeting compliance requirements and uses continuous analysis and historical context to reduce risk across your clouds.
Furthermore, it provides comprehensive visibility and continuous tracking to reduce risks and meet compliance requirements.
Pros
- The platform, once integrated, provides excellent visibility, alerts, and notifications.
- Users can deploy at the infrastructure level in 5 minutes. Kubernetes support is a significant benefit for businesses transitioning to modern infrastructure.
Cons
- Trouble in synchronizing solved issues in Jira because Lacework doesn’t support two-way integration.
Customer Rating
- G2- 4.5/5
5. Aquasec
Aqua Cloud Security Posture Management scans, monitors, and remediates configuration issues in public cloud accounts across AWS, Azure, Google Cloud, and Oracle Cloud according to best practices and compliance standards.
With Aquasec, users can apply consistent policies across all cloud-native deployments. The platform combines cloud workload protection for VMs, containers, and serverless with cloud infrastructure.
Pros
- Threat analysis and mitigation reports include automatic scan visualizations that ensure the information needed to prevent malicious activity.
- Provides customizable dashboards for cloud security and image scanning.
Cons
- The platform lacks a few prominent alert notification channels, such as Datadog and Webhooks.
Customer Rating
- G2- 4.5/5
6. CloudGuard Management
CloudGuard cloud security posture management, a component of the CloudGuard cloud-native security platform, automates governance across multi-cloud services and assets by visualizing and assessing security posture, detecting misconfiguration, and enforcing security best practices and compliance frameworks.
The platform manages the compliance and security posture of cloud-native environments such as Amazon Web Services, Azure, Alibaba Cloud, Google Cloud, and Kubernetes.
Pros
- Provides greater visibility on all cloud workloads and services.
- Supports all cloud areas like native services, infrastructure, serverless architecture, IAM, Kubernetes, network, etc.
Cons
- Limitation of integrating with any 3rd party systems.
- Takes a lot of time to configure and is not user-friendly.
Customer Rating
- G2- 4.5/5
7. Threat Stack
Threat Stack protects your application infrastructure across all layers of your infrastructure stack and provides the observability required for proactive and targeted remediation activity.
The platform secures highly dynamic and complex cloud-native infrastructure that requires more than traditional, fragmented approaches.
It provides integrations and critical capabilities to customers to help them overcome modern security and compliance challenges via – vulnerability assessment, file integrity monitoring, cloud management console monitoring, and host-based intrusion detection.
Pros
- A clear and concise dashboard displays server-related alerts.
- Users can apply a set of rules that are already predefined for SOC 2.
- The agents are very easy to deploy in clusters.
Cons
- Tweaking alert rules and suppressing noisy false positives takes time.
Customer Rating
- G2- 4.4/5
8. Trend Micro Cloud One Conformity
Trend Micro Cloud One Conformity provides continuous security, compliance, and governance for your cloud infrastructure.
The platform provides central visibility and real-time cloud infrastructure monitoring with a single, multi-cloud dashboard. It ensures that businesses can fully utilize the cloud with the assistance of cloud computing systems.
Pros
- Cloud accounts can be kept track of at all times. All compliance checks are alerted to you in real time.
- Provides vulnerability visibility across the infrastructure.
Cons
- Configuration can be complex sometimes.
- Deep Security has a problem updating policies. It is time-consuming to update the policy from management and distribute it to the agent on the server.
Customer Rating
- G2- 4.6/5
9. BMC Helix Cloud Security
BMC Helix cloud security posture management platform helps in remediation for public cloud services like AWS, Azure, and GCP. It integrates with ITSM tools to automate ticketing enrichment. The platform offers ready-to-use policies for CIS, PCI DSS, and GDPR, as well as support for custom policies.
Pros
- User-friendly, robust, and simple to use.
- Administrators have complete control over who and what can be remedied and where. Remediation can be performed with a single button click or by self-driving remediation.
Cons
- You cannot simply download the package and run the setup. There are 50 installs you have to perform. Each and everything must be installed in a specific order.
- It is difficult to close incidents because of status issues.
Customer Rating
- G2- 4.4/5
10. Ermetic
Ermetic manages cloud infrastructure entitlements and security posture in one multi-cloud platform. The platform enables users to address the most significant risk to cloud infrastructure by detecting, prioritizing, and remediating risky entitlements and misconfigurations at scale. It continuously discovers the entire multi-cloud asset inventory and employs full-stack analytics to accurately and contextually identify risk.
Pros
- You can set the least privilege across all the three major cloud service providers (AWS, Azure and GCP) and grant the identities precisely the permissions they need to do their jobs.
- Easy implementation with SSO for user management.
Cons
- Cannot detect misconfigurations around Kubernetes yet
- The tool needs improvement around vulnerabilities in the cloud.
Customer Rating
- G2- 4.9/5
11. Prisma Cloud
Prisma Cloud is a cloud security posture management platform that reduces the complexity of securing multi-cloud environments and simplifies compliance.
It continuously monitors and provides insights into new and existing assets, anomalous behaviors, and potential threats to security teams.
The tool analyzes and normalizes disparate data sources to provide unparalleled risk transparency.
Pros
- Easy integration with CI/CD, IaC, containers, and serverless functions.
- Container security is redefined by real-time vulnerability scanning and reporting.
Cons
- Expensive compared to many other tools
- Its UI is a bit complicated.
Customer Rating
- G2- 4.3/5
12. CrowdStrike CSPM
CrowdStrike Falcon Horizon is a cloud security posture management tool that detects and prevents cloud misconfigurations along with their remediations to resolve security risks.
CrowdStrike goes beyond ad hoc approaches by bringing everything you need for cloud security together in a single platform to provide adequate security from the host to the cloud and everywhere.
CrowdStrike Falcon Horizon enables security teams to keep applications secure and proactively monitor and remediate misconfigurations while fast-paced DevOps teams build non-stop in the cloud.
Pros
- It detects and monitors the control panel and provides security threats across clouds.
Cons
- Sometimes it shows an irrelevant vulnerability to cloud workload, which runs on other cloud platforms such as AWS and Microsoft Azure.
Customer Rating
- G2- 4.4/5
13. Datadog
Datadog cloud security posture management performs continuous configuration scans across cloud accounts, hosts, and containers. Every resource is continuously scanned, and Datadog’s executive reporting offers summaries to monitor compliance with industry benchmark standards.
Pros
- Combine all of your log management into a single, comprehensive view.
Cons
- The cost is relatively high. A modest k8s EC2 node costs more to monitor than the EC2 itself.
- Requires a lot of configuration and it is resource intensive.
Customer Rating
- G2- 4.3/5
14. Zscaler

Zscaler cloud security posture management is a unified platform that helps to identify and remediate cloud misconfigurations and vulnerabilities across all major public cloud providers.
Pros
- Due to closer Zscaler POP availability, connectivity speed is faster. You can be sure that you are sitting in a secure environment quickly.
- When the end user selects authenticate, a notification with the option to accept or deny is sent directly to their phone. If they accept, they are immediately allowed to access the computer.
Cons
- Custom app alignment is not the best because it takes some time to enter the correct data.
- Zscaler occasionally crashes and prevents any interaction after the computer has been suspended.
Customer Rating
- Capterra- 4.2/5
15. Rapid7 InsightCloudSec
Rapid InsightCloudSec secures your public cloud environment from development to production using a modern, integrated, and automated approach. It provides real-time analysis to manage cloud security posture.
The platform enforces security rules throughout the CI/CD build process to avoid misconfigurations. With Rapid7 real-time analysis and automated remediation, you can achieve continuous security and compliance.
Pros
- The best thing about the Rapid7 services is their ease of use, scalability, and deployment models.
Cons
- Sometimes fail to scan the site.
- Devices that have been discovered and examined are never removed. Manual removal is required.
Customer Rating
- G2 – 3.9/5
16. Sophos Cloud Optix
Sophos Cloud Optix is a cloud security posture management solution to identify cloud resource vulnerabilities quickly, ensure compliance, and respond to threats faster. The platform manages identities before they’re exploited. With Sophos Cloud Optix, you can prioritize and address your most critical security flaws before they are discovered and used in cyberattacks.
Cloud Optix ensures teams respond faster by identifying and risk-profiling security, compliance, and cloud spend risks and providing contextual alerts that group affected resources with detailed remediation steps.
Pros
- Users can deduce potential security risk factors, access privilege policies, and anomaly detection.
- The Sophos Cloud Optix assists in solving cloud problems, securing cloud inventories, maintaining cloud security compliance, and balancing cloud workload.
Cons
- Expensive, and the initial setup is complex.
- It is an agent-based solution.
Customer Rating
- G2 – 4.3/5

Megha Thakkar is a technical content writer with about a decade of experience in cybersecurity and compliance. She writes extensively on SOC 2, ISO 27001, GDPR, and security operations, helping organizations translate complex requirements into clear, audit-ready decisions. Her work, tailored for CISOs and executive leaders, is frequently cited in U.S. government and NIST publications.

Team Scrut is a collective of compliance, security, and risk practitioners sharing practical guidance on building audit-ready, scalable programs. We write about SOC 2, ISO 27001, continuous compliance, third-party risk, cloud security, and GRC automation, blending regulatory depth with operator experience to help fast-growing companies strengthen trust, streamline audits, and stay ahead of evolving security demands.

























