Organizations must safeguard against emerging cyber threats by proactively identifying, assessing, and addressing risks before they escalate. Many still rely on outdated methods, such as spreadsheets and email threads, to track IT risks, which consume time and increase the chances of human error.
Without real-time risk visibility, organizations remain exposed to threats. The additional burden of gathering and updating screenshots from multiple platforms compounds the inefficiency of the process.
To stay ahead, consider adopting advanced IT risk management tools like Scrut. These solutions provide real-time monitoring, identification, automation, mitigation, and assessment and seamlessly integrate into your existing security infrastructure.
Why IT Risk Management Is Critical for Modern Organizations?
Businesses face increasing cyber threats, such as hacking, data breaches, and ransomware attacks. In Q2 2024, global cyber attacks increased by 30% compared to the previous year, with an average of 1,636 attacks per organization weekly.
An IT risk management program helps identify, assess, and reduce potential threats to information systems and data. By managing these risks well, businesses can fix vulnerabilities before they cause significant disruptions or harm their reputation. It also helps companies follow industry regulations such as GDPR or HIPAA, lowering legal and financial risks.
5 Features to Look For When Choosing an IT Risk Management Platform
When choosing an IT risk management platform, you’ll want to focus on key features that ensure comprehensive risk assessment, continuous monitoring, and effective mitigation. Here are five essential features to look for:
1. Real-Time Monitoring And Threat Detection
When choosing an IT risk management platform, it’s essential to have a live, intuitive risk register with actionable workflows for managing risks.
This register should capture all risks, potential threats, and vulnerabilities, ensuring no risk is overlooked. The platform should also integrate real-time risk monitoring, threat detection, and reporting, providing continuous visibility into your IT environment.
These actionable workflows allow teams to assign and manage risks seamlessly, ensuring that nothing slips through the cracks.
2. Automation and Simplification of Quantifying Risks and Compliance Reporting
Manual risk assessments and compliance audits are time-consuming and prone to error. The platform should simplify risk quantification by automating assessments based on default and customizable criteria. Whether you need a quick evaluation using predefined scoring factors or a deeper dive with custom metrics, the system adapts to your risk analysis requirements.
In addition, the solution has to quantify your organization’s risk status, including general and third-party/vendor risks, highlight specific areas of concern and offer actionable insights for improvement. Streamlining the process reduces the potential for human error while ensuring comprehensive risk evaluation.
Furthermore, automating compliance reporting speeds up the entire process, helping you close gaps and maintain audit readiness, especially in highly regulated industries where strict compliance is critical.
3. Real-Time Risk Dashboard
IT risk management tools must have an interactive dashboard that gives you real-time insights into your organization’s cybersecurity metrics, compliance status, and vulnerabilities. You can track risks across all stages, prioritize them based on impact, and manage unresolved risks by monitoring their status.
Also, you’ll receive actionable information that empowers you to make informed decisions and streamline cybersecurity management.
4. Collaboration
IT risk management requires teamwork and collaborating with IT, security, compliance, legal, and leadership departments. Choose a platform that helps teams work together by providing communication tools, task management, and ways to handle incidents.
It should allow you to create risk mitigation tasks for each associated risk. You can have actions, like discussions and file uploads, in one place. This makes it easier to see what’s happening and ensures all steps are documented. Also, the tools must let you keep audit logs and add accountability and traceability.
Top 5 IT Risk Management Software in 2025
We have listed top IT risk management tools that offer real-time monitoring, automation, and easy scalability. They work well with your existing systems to provide complete protection and ensure smooth compliance.
1. Scrut Automation
Scrut is an IT risk management platform that helps businesses find, evaluate, and address cybersecurity and compliance risks. It provides real-time risk monitoring, automatic compliance tracking, and easy integration with existing security tools, making risk management straightforward.
Key Features of Scrut
- Reliable risk measurement: It allows you to quantify your risk profile using expert-vetted scoring methodologies. Scrut calculates inherent and residual risk scores, helping you assess the effectiveness of risk treatment plans and address critical vulnerabilities.
- Deeper customization at no extra cost: Many compliance platforms charge an additional fee for custom workflows, additional control mapping, creating new controls, and customizing controls based on security policies. With Scrut, you can customize workflows and controls at no extra cost.
- Customizable multi-approval reviews: As part of the customs workflows you can build with Scrut, you can also add a multi-approval process, for multiple stakeholders to review and approve compliance artifacts, ensuring thorough assessment.
- Map risks to compliance frameworks: Scrut pre-maps risks to security frameworks like ISO 27001 and SOC 2, helping you focus on the most relevant threats without sorting through endless risk sources.
- Automatic risk identification: The tool scans your ecosystem to automatically detect risks across your code base, infrastructure, applications, vendors, employees, access, and more. You can also use Scrut’s pre-loaded risk library or create custom risks tailored to your needs. Once risks are identified, Scrut auto populates mitigation tasks along with relevant controls
- Actionable dashboards: Dashboards help you visualize and quantify your risk posture. Scrut provides dashboards to view risk heatmaps, risk trends, treatment strategies, mitigation tasks, to help you deliver effective risk treatment strategies. Scrut also provides audit trail logs offering visibility into critical events and smallest changes made in your IT environment.
- 24/7 continuous monitoring: You can stay on top of your risk posture with Scrut’s continuous risk monitoring. With easy-to-set-up alerts and notifications integrated into your favorite messaging and mail apps, you’ll always be aware of any changes to your risk landscape.
Testimonials
Here is a review from Scrut users:
“Scrut Automation has significantly streamlined our compliance and security processes. The platform’s user-friendly interface, comprehensive dashboard, and intuitive automation features make managing frameworks like ISO 27001, SOC 2, and GDPR effortless. I particularly appreciate the automated evidence collection, which saves hours of manual work and reduces the risk of human error. The integrations with our existing tools (like AWS, Slack, and Jira) were seamless, ensuring all our data sources were covered.”
Karan A., Head of Domain Operations
“The Scrut automation platform is easy to use and learn for any individual or organization working on getting their certifications for ISO and SOC2 compliance. This tool speeds the certification process, allowing better tracking of tasks and progress made about it. The Scrut team does more than help with preps; it helps organizations tune their processes for maximum efficiency and proper post-certification practices to ensure efficient operations and strong compliance. And, the support team is responsive; this means a good user experience is practically guaranteed.”
Naresh K., IT Operation Manager
Pricing
Contact their support team for pricing plan details.
2. Drata
Drata is a security and compliance automation platform designed to help businesses manage IT risks and maintain compliance efficiently.
Its primary goal is to support organizations in meeting regulatory requirements, mitigating risks, and preparing for audits, thereby securing the trust of users, partners, and prospects.
Drata helps businesses navigate compliance for critical frameworks such as SOC 2, ISO 27001, GDPR, HIPAA, and various custom frameworks.
Key Features of Drata
- Pre-Mapped Risk Library: Access a comprehensive library of over 150 pre-mapped, threat-based risks organized by industry controls. Additionally, you can create custom risks tailored to your organization’s specific needs.
- Risk Drawer: Centralize and manage all your risk data in one place, including risk descriptions, categories, owners, supporting documents, and assessments. Treatment Plans: Drata automatically generates risk scores and treatment plans based on the severity of risks. This helps you prioritize actions and allocate resources effectively to mitigate risks.
Pricing
Drata comes with three pricing plans. You can contact their customer support to get pricing information.
3. Secureframe
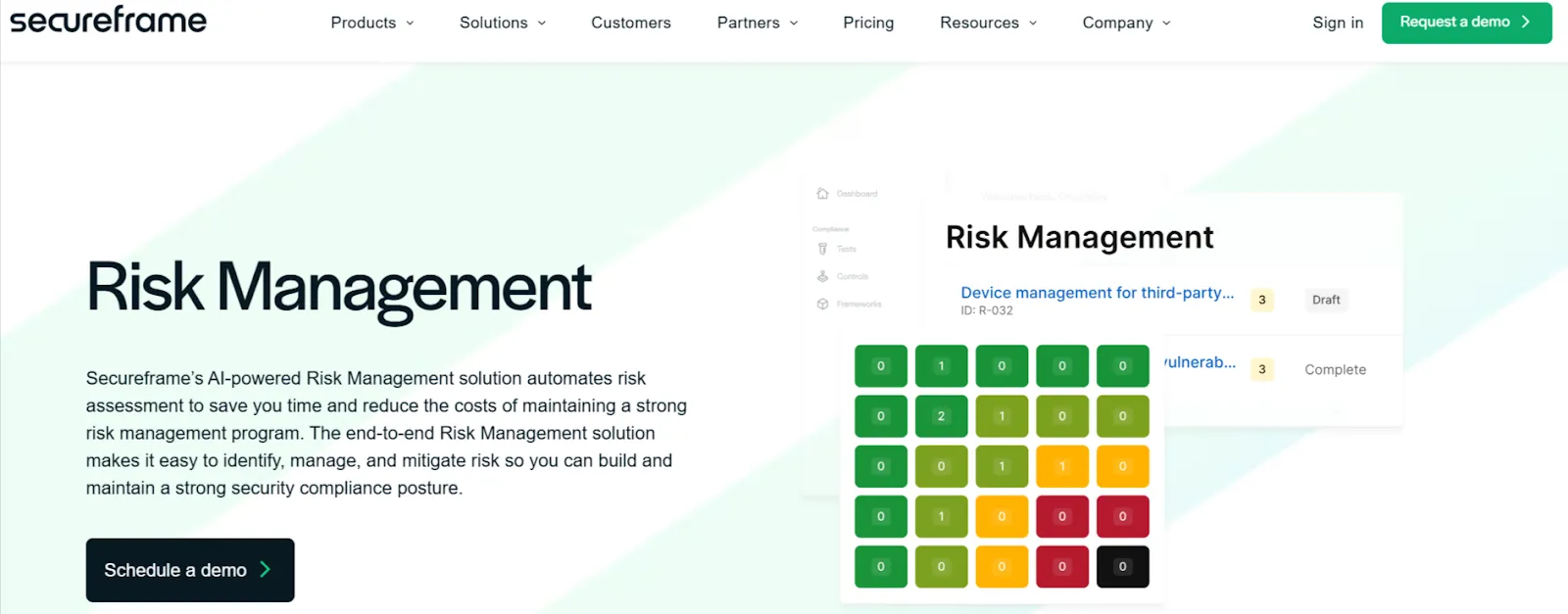
Secureframe’s AI-driven Risk management tool automates risk assessments, reducing costs and saving time. It helps you easily identify, handle, and reduce risks, allowing you to build and sustain strong security compliance.
Key Features of Secureframe
- Comprehensive Risk Management: Secureframe helps you assess and document treatment plans aligned with frameworks like SOC 2, ISO 27001, PCI, and HIPAA. Built on the ISO 27005 methodology, it ensures practical risk assessment and informed decision-making for your security compliance program.
- Easily Add Risks with the Risk Library: It offers a risk library with NIST risk scenarios across categories such as fraud, legal, finance, and IT. You can easily add these risks to your risk register, for tracking and management.
- Monitor Your Risk Management Program: Secureframe’s dashboards provide a holistic view of your organization’s risks, featuring heat maps, summary tables, and trend charts. It communicates the status of your risk management program to executives, auditors, and other stakeholders.
Pricing
You need to contact their customer support to get your customized quote.
4. Hyperproof
Hyperproof helps you identify and prioritize risks, automate and orchestrate risk workflows, align risk management with compliance activities, and reduce the time spent on risk monitoring.
Key Features of Hyperproof
- Centralized Risk Management: With Hyperproof, you can centralize all risk management activities by storing and tracking risks in the Hyperproof risk register.
- Map Controls to Risks: It integrates control health data across multiple risk registers. This enables continuous monitoring, quick issue resolution, and streamlined reporting of mitigation efforts to relevant stakeholders.
- Evaluate Risks Specific to Your Organization: The solution assesses each risk using standard fields like tolerance, actual risk, inherent risk, likelihood, and impact with customizable scales. You can also add custom fields to filter and track additional risk information directly from your dashboards and reports.
Pricing
Contact their support team to get your tailored quote.
5. LogicManager
LogicManager’s security risk management solution helps organizations manage IT and cybersecurity risks. It ensures compliance with key regulations such as SOC 2, HIPAA, ISO 27001, PCI DSS, the NIST Cybersecurity Framework, COBIT, and more.
Key Features of LogicManager
- Gap Assessment Capabilities: LogicManager performs gap assessments against major security frameworks and regulations, including SOC 2, HIPAA, ISO 27001, and more, to identify areas for improvement.
- IT Asset Management: It manages the onboarding and offboarding of IT assets while ensuring appropriate access levels across the organization for secure, organized asset control.
- Security Issue Identification and Tracking: The tool detects IT security vulnerabilities and issues and then tracks them through resolution to ensure ongoing risk mitigation and compliance.
Pricing
LogicManager offers a pricing model that matches their services to your specific needs. Contact customer support for a personalized quote.
How Scrut Enhances IT Risk Management with Automation and Real-Time Monitoring?
Scrut improves IT risk management through automation and real-time monitoring. This provides organizations with a comprehensive toolset to identify, assess, and mitigate risks. This approach streamlines risk management processes and ensures continuous compliance with various regulatory frameworks.
Here is how you can benefit from using Scrut:
- Continuous Risk Monitoring: The platform offers 24/7 risk monitoring, ensuring organizations remain aware of their risk posture. You can set up alerts and notifications that integrate with standard messaging and email applications, enabling proactive responses to emerging threats.
- Real-Time Compliance Management: Scrut automates compliance checks against 50+ frameworks, including ISO 27001 and SOC 2. This feature allows organizations to map risks to compliance controls seamlessly. This simplifies regulatory adherence while reducing the risk of non-compliance penalties.
- Automated Workflows for Risk Treatment: Scrut automates the processes involved in risk treatment, including remediation, mitigation, transference, and acceptance. You can create mitigation tasks, assign responsibilities, and track progress through automated workflows. This reduces the time and effort required for manual management.
Conclusion
With the rise of cyber threats, businesses must adopt advanced IT risk management software to identify, assess, and mitigate risks proactively. The top software solutions we explored Scrut, Drata, Secureframe, Hyperproof, and LogicManager, offer comprehensive features that ensure real-time monitoring, automation, and seamless compliance with regulatory frameworks.
Ready to take control of your IT risk management? Schedule a demo with Scrut today to explore how its features can enhance your organization’s security and compliance efforts.
Top risk management software solutions include Scrut, Secureframe, Hyperproof, LogicManager, and Drata. These tools assist in identifying, managing, and mitigating risks. They provide businesses with practical strategies to enhance their security and compliance efforts.
Risk management software is designed to help organizations manage business risks effectively. These solutions provide a structured approach to identifying, assessing, mitigating, and monitoring risks. This enables companies to make informed decisions and minimize potential negative impacts.
Compliance and risk management are typically handled separately in security strategies. However, with tools like Scrut, companies can streamline both functions into one solution, enhancing their security posture by efficiently managing compliance and mitigating risks in a unified platform.

Megha Thakkar is a technical content writer with about a decade of experience in cybersecurity and compliance. She writes extensively on SOC 2, ISO 27001, GDPR, and security operations, helping organizations translate complex requirements into clear, audit-ready decisions. Her work, tailored for CISOs and executive leaders, is frequently cited in U.S. government and NIST publications.

Team Scrut is a collective of compliance, security, and risk practitioners sharing practical guidance on building audit-ready, scalable programs. We write about SOC 2, ISO 27001, continuous compliance, third-party risk, cloud security, and GRC automation, blending regulatory depth with operator experience to help fast-growing companies strengthen trust, streamline audits, and stay ahead of evolving security demands.

























