CMMC ensures that DoD contractors adequately safeguard sensitive information against frequent and complex cyberattacks. Noncompliance could result in losing valuable DoD contracts and expose a contractor to cybersecurity vulnerabilities. Complying with CMMC regulations is one thing. However, maintaining compliance, year after year, is critical. That’s where CMMC automation software comes in.
The Cybersecurity Maturity Model Certification (CMMC) compliance framework is a set of standards that organizations must follow if they want to work with the US Department of Defense (DoD) or the defense industrial base (DIB). It is a US standard for determining the maturity of a company’s cybersecurity program.
The US Department of Defense established CMMC in response to significant compromises of sensitive defence information on contractors’ information systems. The CMMC framework defines five cybersecurity maturity levels that reflect a company’s cybersecurity infrastructure’s ability to safeguard sensitive government information on contractors’ information systems.
Most organizations face the challenge of the lack of internal resources required to implement a plan of action for a new and complex compliance program. Another barrier to CMMC certification for many organizations is the lack of an information security compliance program. Many companies lack the security-centric architecture and compliance management tools required for CMMC compliance. They lack the in-house expertise required to establish an effective compliance program capable of meeting CMMC standards.
12 CMMC Compliance Automation Tools
If your company wants to do business with any federal agency, CMMC software should be on your list. Wondering how to select the right tool for your organization’s needs? We have picked the best 12 CMMC compliance automation tools.
1. Scrut Automation
Scrut automation can help you achieve Cybersecurity Maturity Model Certification by providing a smarter path to compliance by eliminating time-consuming manual procedures and keeping you updated on the progress of your programs.
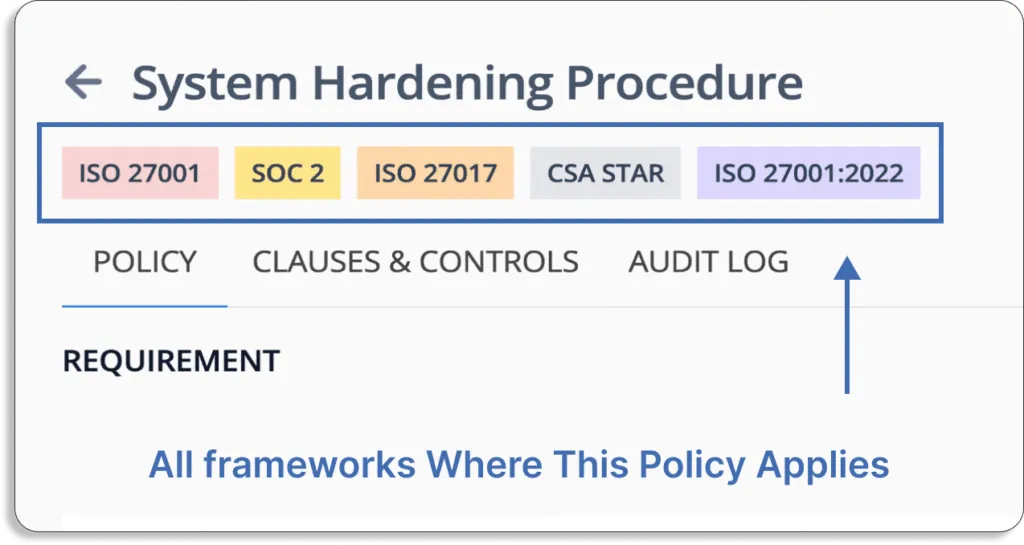
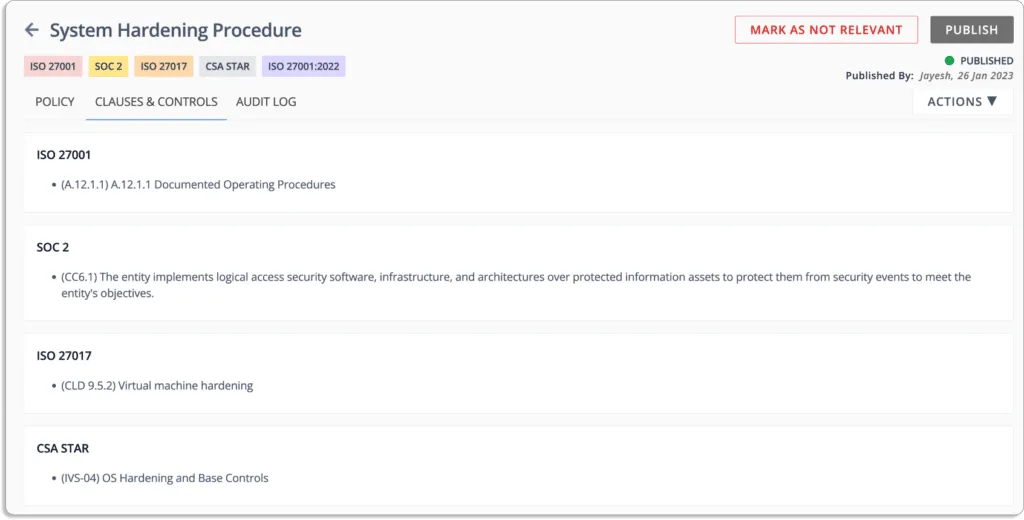
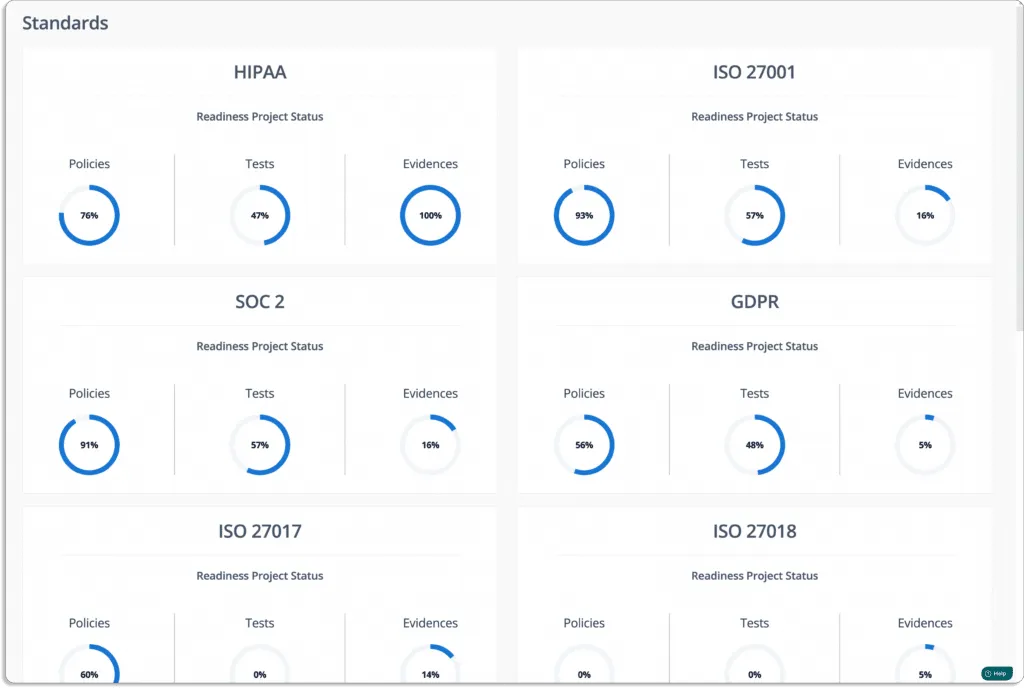
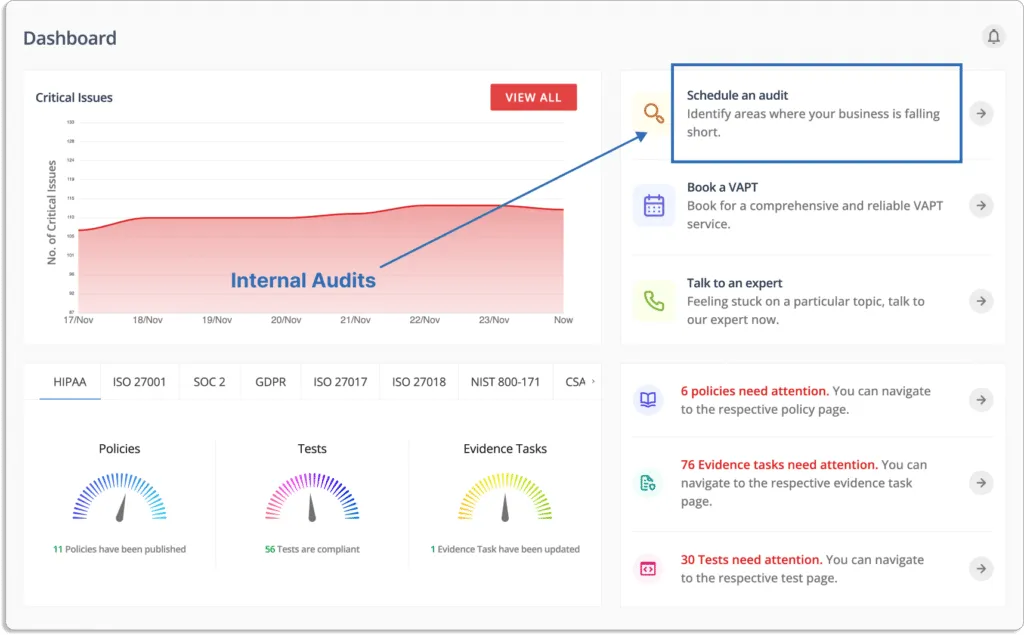
Scrut supports the following frameworks: SOC 2, SOC 3, ISO 27001, ISO 27701, ISO 27017, ISO 27018, ISO 22301, ISO 20000-1, GDPR, HIPAA, FERPA, HITRUST, FedRamp, CMMC, CCPA, PCI DSS, CSA Star, CMMI – DEV, CMMI – SVC, GLB, NIST 800 171, etc. The platform offers you prebuilt policies vetted by industry experts and aligned with popular industry frameworks, as shown in the screenshot below.
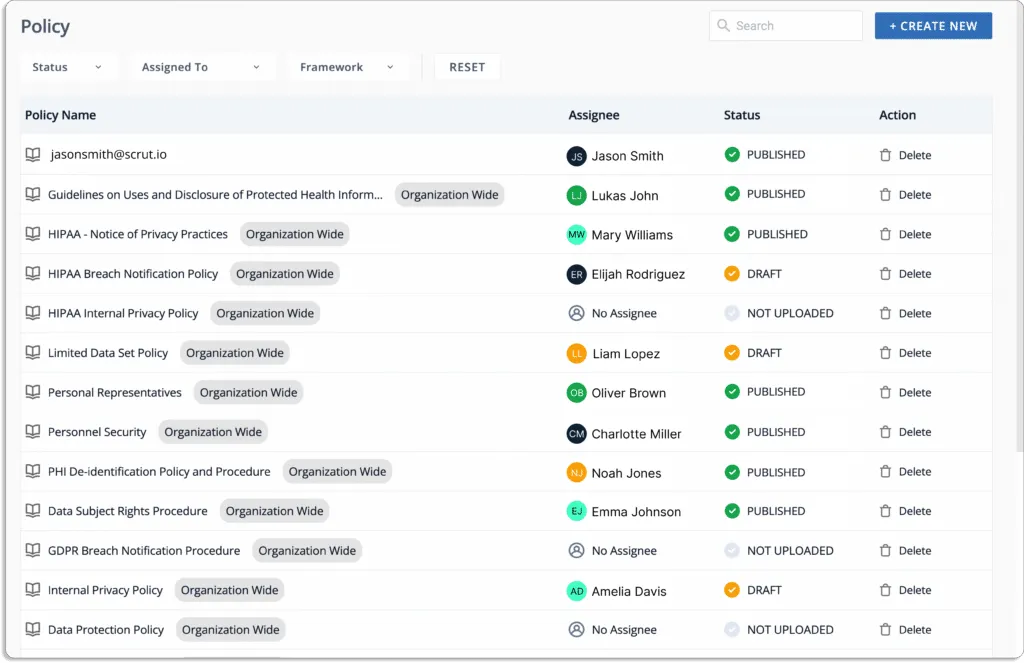
It provides you with prebuilt policies and controls that are mapped to frameworks.
The platform identifies open hazards and critical issues. It provides a single tracker to monitor what needs to be corrected and assists you in assigning and tracking activities all in one window.
Check our customer reviews below.
Pros
- Allows you to track all compliance activities in one place – With Scrut, you can track multiple compliances simultaneously. You get the visibility you need to understand the status, efficacy, and impact of your information security activities on your compliance posture with Scrut GRC. It creates a single source of truth for all information security tasks and artifacts, allowing you to close compliance gaps in real-time and remain compliant 24*7.
- Automate cloud security monitoring – Scrut is not limited to the basic controls required by popular frameworks. It automatically compares your cloud configurations to 200+ CIS benchmarks to ensure a strong information security posture.
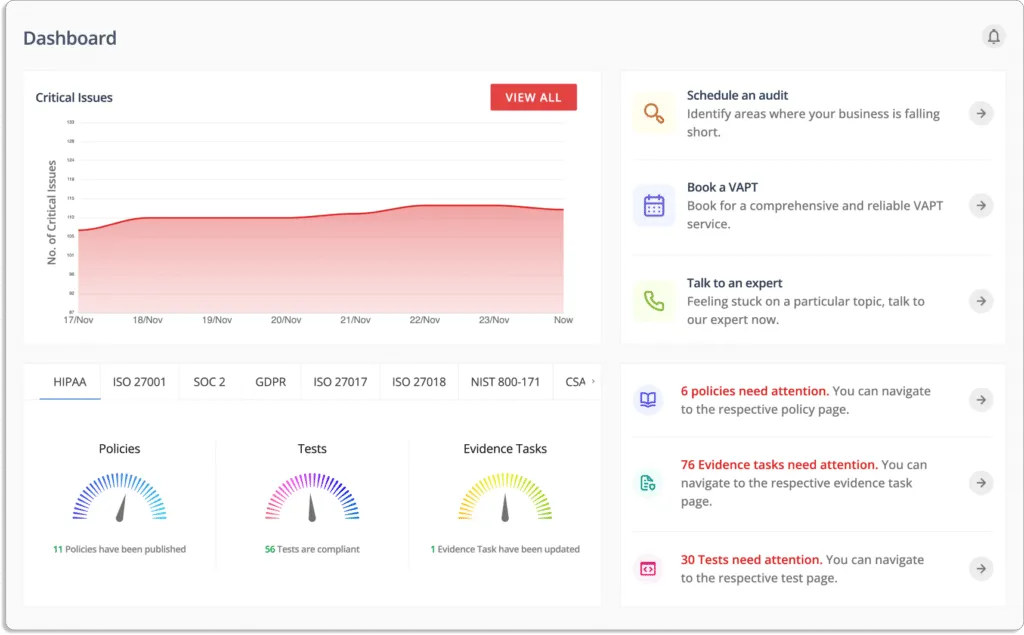
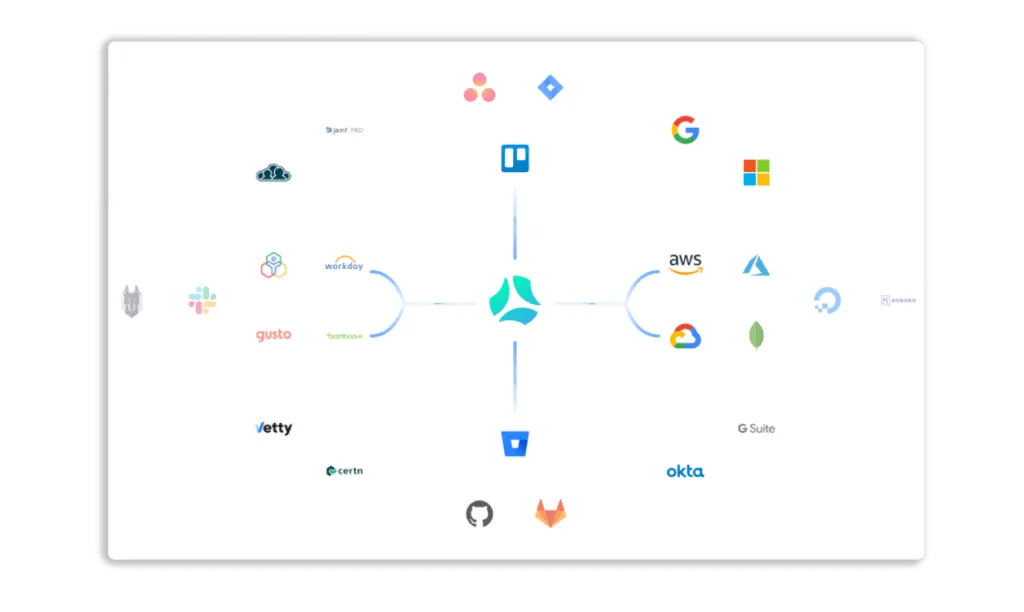
- Automated evidence collection – Evidence gathering is a time-consuming and monotonous process that no one enjoys. Scrut eliminates the need for thousands of evidence artifacts to be collected manually by automating evidence collection across 70+ integrations across mapped controls.
- Smooth audit process – Scrut automates and streamlines the time-consuming audit tasks, from planning to analysis. The platform simplifies collaboration with your auditors, increasing accountability and speeding up the fulfillment of InfoSec tasks while reducing manual work by up to 75%. You can invite auditors to the platform to manage the entire audit process in real-time, eliminating the need for a back-and-forth between email and drive folders. Scrut allows you to create audit projects and manage access with a few clicks.
Customer Rating
- G2- 5/5
2. Drata
Drata is an audit-ready security and compliance automation platform that continuously monitors and collects evidence of a company’s security controls. The platform offers custom controls to help you get compliant and continuously monitor your posture to ensure you stay compliant. It provides visibility into scoping baselines, letting you know what you’ve accomplished and what else needs to be done. Furthermore, it streamlines and automates task management by connecting to Jira, Asana, and other systems.
Pros
- Users can see a detailed overview of which compliance requires attention through Drata’s centralized visibility of personnel and assets.
- The platform automates the complex and time-consuming compliance process, removing the need for users to keep track of all the various regulations and requirements. All of that information is easily accessible and constantly updated with Drata.
Cons
- It doesn’t support the duplicative evidence upload feature. Users have to manually upload duplicate evidence.
- The tool doesn’t pick up Windows BitLocker encryption. Users have to manually upload evidence to support that feature.
Customer Rating
- G2- 4.9/5
3. Hyperproof
Hyperproof implements a security compliance program that meets DOD expectations. The platform guides you in preparing for the CMMC in a streamlined manner possible by conducting a gap analysis and identifying key actions that must be completed to satisfy CMMC requirements. It quickly collects evidence to document your CMMC compliance efforts.
Pros
- Users can create the right control set with Hyperproof frameworks to track risks and issues.
- Hyperproof’s control assessment feature enables users to design and test controls, as well as track action plans for any issues.
Cons
- Deactivated user accounts still appear in modules because of inherited security controls.
Customer Rating
- G2- 4.5/5
4. ZenGRC
ZenGRC CMMC platform provides a central repository for all audit-ready documentation. The solution offers insight into how to move to CMMC audit readiness, from self-assessment to CMMC audit by a third-party assessment organization. It eliminates the tedious manual processes and reduces the time and resource requirements to manage them.
Pros
- Users can see where they stand and what needs to be done with ZenGRC auditing functionality.
- ZenGRC provides task reminder feature so that the team members don’t have to follow up on every requirements.
Cons
- The roles available in ZenGRC are limited. For example, if a contributor is assigned a request, he or she cannot reassign the request to another contributor.
- The user’s ability to customize is limited. For example, users cannot customize when they send out notifications.
Customer Rating
- G2- 4.4/5
5. Onspring
Onspring is a GRC software that automates the process of mapping CMMC compliance requirements, gathering evidence, and providing documentation to CMMC, making your organization audit-ready. You can monitor your organization’s status for CMMC domains and capabilities in accordance with any of the five CMMC levels using Onspring. You can also assess and track subcontractors’ CMMC compliance.
Pros
- The platform increases the scalability because users can construct a workflow without knowing how to code.
- Users can easily configure all of the modules without opening change tickets.
Cons
- The platform does not automatically update the email while delegating a survey. Users have to adjust it manually.
- A major drawback is the absence of active directory integration.
Customer Rating
- G2- 4.8/5
6. Logic Manager
Logic Manager is enterprise risk management (ERM) software that enables businesses to plan for the future, protect their reputations, and improve business performance through strong governance, risk management, and compliance (GRC). The platform lets you centralize your controls and collect evidence by streamlining the audit process from beginning to end and determining your certification level.
Pros
- The platform provides templated risks library.
- The tool responds quickly to incidents when reported.
Cons
- The platform does not capture key contract details.
- Recent real-time changes are not reflected in the reporting module.
Customer Rating
- G2- 4.4/5
7. Sprinto
Sprinto is a security compliance automation platform that integrates with your cloud environment to consolidate risk, map entity-level controls, and run fully automated checks. The platform streamlines your organization’s processes and controls to achieve CMMC. It offers a real-time continuous monitoring feature.
Pros
- Sprinto provides complete transparency of the entire compliance process so that users don’t miss anything.
- The dashboard makes it easier for teams to close open loops by providing all the latest status and security checks.
Cons
- The tool doesn’t include login with the SSO provider such as Okta.
- The tool is unable to filter within those lists or sort them.
Customer Rating
- G2- 4.9/5
8. AuditBoard
AuditBoard is a cloud-based platform that transforms audit, risk, environmental, social, and compliance management. The tool simplifies CMMC assessments by combining risks, controls, policies, frameworks, and more to equip your organization to meet today’s increasing compliance requirements. It facilitates communication and collaboration with stakeholders by making it simple to deploy surveys, including pre-and post-audit surveys, and automating evidence collection.
Pros
- Users can use the tool to create custom reports to view data in Excel, allowing them to analyze trends in the data without having to create custom requests.
- Users can use filters and keyword search options to find the controls.
Cons
- Dashboard fields may not always be accessible before submitting a ticket. For instance, drop-down values in a questionnaire do not integrate well.
- The platform does not offer a Gantt chart for annual schedule audits. Users have to use Excel to monitor the audit plan’s development.
Customer Rating
- G2- 4.8/5
9. Secureframe
Secureframe is a GRC platform that assists organizations that work with the DoD in understanding compliance requirements, managing controls, streamlining workflows, and automating tasks and evidence collection to become CMMC compliant. It collects evidence and reviews processes automatically for compliance assessments.
Pros
- The software streamlines the compliance process by dividing complicated requirements into manageable tasks and corrections.
- The platform integrates with numerous technologies and assists users in comprehending what is required to reach compliance.
Cons
- Third-party auditing firms conduct the audits.
- The tool does not provide high-level priority order of events.
Customer Rating
- G2- 4.6/5
10. OneTrust
OneTrust’s readiness project survey assists you in determining your CMMC 2.0 requirements based on your business operations. The platform makes evidence collection easier by connecting your controls to the evidence tasks required to demonstrate compliance. It automatically gathers the necessary evidence to demonstrate compliance. You can obtain in-platform step-by-step guidance for your organization to help everyone understand what they need to do to support your cybersecurity practices.
Pros
- The assessment automation module enables users to collect the data required to manage data protection risks.
- The platform has numerous configuration options for business objectives.
Cons
- The tool does not provide onboarding instructions.
- Sometimes, it can be difficult to navigate and find solutions from a set of guide pages.
- When opened in duplicate tabs, the platform keeps its previous settings. For example, where assessments are filtered, it opens the same selection in a new tab.
Customer Rating
- G2- 4.3/5
11. Wabbi
Wabbi’s continuous security platform enables organizations at all CMMC levels to scale and maintains application security cost-effectively. The tool implements the practices and processes required for certification and transforming security into a strategic asset in application delivery.
12. Check Point
Check Point CloudGuard assists organizations in achieving and maintaining CMMC compliance by monitoring ongoing corporate systems compliance.
The Check Point compliance software blade compares the customer’s Check Point environment to a library of security practices, highlighting incorrect configuration settings and security flaws. Security best practices are linked to major regulations, such as CMMC, allowing complex regulatory requirements to be translated into security terms.
Pros
- The platform offers a three-tier solution that is beneficial from a strategic point of view.
- The Check Point team assists users in planning environment topologies, estimating compute resources required, and matching that with hardware.
Cons
- The lack of documentation to generate functional troubleshooting.
- It is costly, and the pricing models appear to change with each renewal.
Customer Rating
- G2- 4.6/5
CMMC automation tools are software platforms that help organizations automate cybersecurity and compliance tasks required for the Cybersecurity Maturity Model Certification (CMMC). These tools collect security evidence, map controls to requirements, and monitor systems continuously to maintain audit readiness.
Organizations use CMMC automation tools to reduce manual work, simplify compliance workflows, and maintain continuous compliance with DoD cybersecurity requirements. Automation helps teams track controls, collect evidence, and monitor security posture more efficiently.
A strong CMMC automation platform typically offers automated evidence collection, security control mapping to NIST SP 800-171, continuous monitoring, alerting for control drift, and dashboards that track compliance status. These capabilities help organizations stay audit-ready at all times.
Common CMMC automation tools include Scrut, Drata, Hyperproof, ZenGRC, Onspring, Sprinto, Secureframe, AuditBoard, OneTrust, Wabbi, and Check Point CloudGuard. These platforms automate compliance workflows, evidence collection, and risk monitoring.
Automation improves CMMC compliance by continuously monitoring security configurations, collecting compliance artifacts automatically, mapping controls to framework requirements, and identifying gaps in real time, reducing the risk of audit failures.

Susmita Joseph is a cybersecurity and compliance writer specializing in governance, risk, and regulatory content. She focuses on making complex subjects such as AI governance, cybersecurity compliance, and risk management accessible to growing and mature organizations. With a particular interest in the intersection of AI and GRC, her work explores how emerging technologies are reshaping compliance expectations and security operations.

Team Scrut is a collective of compliance, security, and risk practitioners sharing practical guidance on building audit-ready, scalable programs. We write about SOC 2, ISO 27001, continuous compliance, third-party risk, cloud security, and GRC automation, blending regulatory depth with operator experience to help fast-growing companies strengthen trust, streamline audits, and stay ahead of evolving security demands.

























